| Revision as of 09:29, 6 February 2019 edit124.123.49.244 (talk) Not rightTags: Mobile edit Mobile web edit← Previous edit | Latest revision as of 17:21, 5 August 2024 edit undoRobbieIanMorrison (talk | contribs)Extended confirmed users18,443 edits →Etymology: added "" to a quote to allow it to read smoothly | ||
| (44 intermediate revisions by 36 users not shown) | |||
| Line 1: | Line 1: | ||
| {{Short description|Electronic software copy protection device}} | |||
| {{Multiple issues| | |||
| {{ |
{{more citations needed|date=March 2008}} | ||
| {{cleanup|date=July 2009}} | |||
| }} | |||
| A '''software protection dongle''' (commonly known as a '''dongle''' or '''key''') is an electronic ] and content protection device |
A '''software protection dongle''' (commonly known as a '''dongle''' or '''key''') is an electronic ] and content protection device. When connected to a computer or other electronics, they unlock software functionality or decode ].<ref>{{cite book |last1=Amos |first1=S. W. |last2=Amos |first2=Roger S. |title=Newnes Dictionary of Electronics |url=https://archive.org/details/newnesdictionary0000amos_o3q0 |url-access=registration |accessdate=4 July 2013 |year=2002 |edition=4th |publisher=] |isbn=0750643315 |oclc=144646016 |page=}}</ref> The hardware key is programmed with a ] or other cryptographic protection mechanism and functions via an electrical connector to an ] of the computer or appliance.<ref>{{cite book |last=Stobbs |first=Gregory A. |title=Software Patents |edition=Third |url=https://books.google.com/books?id=Rn1vZWqSuNYC&pg=SA2-PA90 |accessdate=4 July 2013 |year=2012 |publisher=] |isbn=9781454811978 |oclc=802867781 |pages=2–90}}</ref> | ||
| In software protection, dongles are two-interface security tokens with transient data flow with a pull{{clarify|date=January 2021}} communication that reads security data from the dongle. In the absence of these dongles, certain software may run only in a restricted mode, or not at all. In addition to software protection, dongles can enable functions in electronic devices, such as receiving and processing encoded video streams on television sets. | |||
| ] | |||
| == |
==Etymology== | ||
| The Merriam-Webster dictionary states that the "First known use of ]" was in 1981 and that the etymology was "perhaps alteration of dangle."<ref>{{cite web |title=Dongle |url=https://www.merriam-webster.com/dictionary/dongle |publisher=Merriam-Webster |accessdate=11 June 2019}}</ref> | |||
| ] | |||
| ] | |||
| ] | ] | ||
| Line 18: | Line 14: | ||
| ] | ] | ||
| ⚫ | Dongles rapidly evolved into active devices that contained a serial transceiver (]) and even a ] to handle transactions with the host. Later versions adopted the ] interface, which became the preferred choice over the ] or parallel interface.{{Citation needed|date=June 2021}} | ||
| ⚫ | A 1992 advertisement for ] claimed the word dongle was derived from the name "Don Gall". Though untrue, this has given rise to an ].<ref>, ''Byte'' Magazine, p. 148</ref> | ||
| ⚫ | == Usage == | ||
| In late 1970s/early 1980s, Wordcraft became the earliest ] to use a software protection dongle.<ref>https://qustuff.com/early_days.htm</ref> The dongle was passive using a 74LS165 8-bit shift register connected to one of the two ] ports on the ] microcomputer. The tape cassette port supplied both power and bi-directional data I/O. | |||
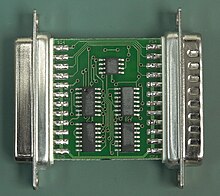
| ⚫ | ] parallel port copy protection dongles.]] | ||
| ⚫ | Efforts to introduce dongle copy-protection in the mainstream software market have met stiff resistance from users. Such copy-protection is more typically used with very expensive packages and ] software such as ]/] software, ], ] hospitality and special retail software, ] applications, and some ] packages. | ||
| ⚫ | In cases such as prepress and printing software, the dongle is encoded with a specific, per-user license key, which enables particular features in the target application. This is a form of tightly controlled licensing, which allows the vendor to engage in vendor lock-in and charge more than it would otherwise for the product. An example is the way ] licenses ] to customers: When a ] output device is sold to a customer, Prinergy's own license cost is provided separately to the customer, and the base price contains little more than the required licenses to output work to the device. | ||
| The requirements for security were identified by the author of the Wordcraft word processor, Pete Dowson, and his colleague Mike Lake. Through the network of PET users in the UK they made contact with Graham Heggie in Coventry and Graham's knowledge of electronics meant that they quickly arrived at the idea of a 74LS165 shift register connected to the tape cassette port which provided 5V power and lines to shift the bits into the software. The shift register contained only 8 bits but with lines tied to ground or 5V at random it could provide a random number between 0 and 255 which was sufficient security for the software. The prototype was on ] which dangled from the tape port edge connector on wires - so "dangle" became "dongle". Pete Dowson wrote special self-modifying 6502 machine code to drive the port directly and to obfuscate the code when not in use. | |||
| ⚫ | USB dongles are also a big part of ]'s audio production and editing systems, such as ], WaveLab, Hypersonic, ], and others. The dongle used by Steinberg's products is also known as a Steinberg Key. The Steinberg Key can be purchased separately from its counterpart applications and generally comes bundled with the "Syncrosoft License Control Center" application, which is cross-platform compatible with both Mac OS X and Windows. | ||
| The first device used a commercial potting box with black or blue epoxy resin. Wordcraft's distributor at the time, Dataview Ltd., then based in ], UK, went on to produce dongles for other software developers. When Wordcraft International was formed in ], UK, responsibility for manufacture was transferred to Brian Edmundson who also produced the plastic moulding for the enclosure. One of the greatest regrets of Graham, Pete and Mike was that they did not patent the idea when they came up with it.<ref>https://qustuff.com/early_days.htm</ref> | |||
| ⚫ | Some software developers use traditional USB flash drives as software license dongles that contain hardware serial numbers in conjunction with the stored device ID strings, which are generally not easily changed by an end-user. A developer can also use the dongle to store user settings or even a complete "portable" version of the application. Not all flash drives are suitable for this use, as not all manufacturers install unique serial numbers into their devices. | ||
| Versions of the Wordcraft dongle were later produced for IBM 25 pin parallel ports, 25 pin serial ports and 9 pin serial ports. Among the computers supported, before the arrival of the IBM PC, were ]'s ] Victor 9000, the ACT ] and the DEC ]. | |||
| Although such medium security may deter a casual hacker, the lack of a processor core in the dongle to authenticate data, perform encryption/decryption, and execute inaccessible binary code makes such a passive dongle inappropriate for all but the lowest-priced software. A simpler and even less secure option is to use unpartitioned or unallocated storage in the dongle to store license data. Common USB flash drives are relatively inexpensive compared to dedicated security dongle devices, but reading and storing data in a flash drive are easy to intercept, alter, and bypass. | |||
| An early example of the term was in 1984, when early production ]s were shipped with part of the QL firmware held on an external 16 KB ROM cartridge (infamously known as the "]" or "dongle"), until the QL was redesigned to increase the internal ROM capacity from 32 to 48 KB.<ref name="sunrise">{{Cite web|url=http://www.nvg.ntnu.no/sinclair/computers/ql/ql_sst.htm|title=The Quantum Leap – to where?|work=Sinclair and the 'Sunrise' Technology|author=Ian Adamson|author2=Richard Kennedy |accessdate=2006-12-15}}</ref><ref name="dickinson-ql">{{Cite web | |||
| |url=https://www.flickr.com/photos/9574086@N02/sets/72157600854938578/ | |||
| |title=QL and Beyond | |||
| |work=Flickr | |||
| |author=Rick Dickinson | |||
| |date=2007-07-16 | |||
| |accessdate=2008-04-21}}</ref> | |||
| ⚫ | Dongles rapidly evolved into active devices that contained a serial transceiver (]) and even a ] to handle transactions with the host. Later versions adopted the ] interface |
||
| ⚫ | A 1992 advertisement for ] claimed the word dongle was derived from the name "Don Gall". Though untrue, this has given rise to an ].<ref>, ''Byte'' Magazine, p. |
||
| ⚫ | == |
||
| ⚫ | ] parallel port copy protection dongles.]] | ||
| ⚫ | Efforts to introduce dongle copy-protection in the mainstream software market have met stiff resistance from users. Such copy-protection is more typically used with very expensive packages and ] software such as ]/] software, ] hospitality and special retail software, ] applications, and some ] packages. | ||
| ⚫ | In cases such as prepress and printing software, the dongle is encoded with a specific, per-user license key, which enables particular features in the target application. This is a form of tightly controlled licensing, which allows the vendor to engage in vendor lock-in and charge more than it would otherwise for the product. An example is the way ] licenses ] to customers: When a computer-to-plate output device is sold to a customer, Prinergy's own license cost is provided separately to the customer, and the base price contains little more than the required licenses to output work to the device. | ||
| ⚫ | USB dongles are also a big part of ]'s audio production and editing systems, such as ], WaveLab, |
||
| ⚫ | Some software developers use traditional USB flash drives as software license dongles that contain hardware serial numbers in conjunction with the stored device ID strings, which are generally not easily changed by an end-user. A developer can also use the dongle to store user settings or even a complete "portable" version of the application. Not all flash drives are suitable for this use, as not all manufacturers install unique serial numbers into their devices |
||
| ===Issues=== | ===Issues=== | ||
| There are potential weaknesses in the implementation of the protocol between the dongle and the copy-controlled software |
There are potential weaknesses in the implementation of the protocol between the dongle and the copy-controlled software. For example, a simple implementation might define a ] to check for the dongle's presence, returning "true" or "false" accordingly, but the dongle requirement can be easily circumvented by modifying the software to always answer "true". | ||
| Modern dongles include built-in strong encryption and use fabrication techniques designed to thwart ]. Typical dongles also now contain ] — essential parts of the software may actually be stored and executed on the dongle. Thus dongles have become ]s that execute program instructions that may be input to the cryptoprocessor only in encrypted form. The original secure cryptoprocessor was designed for copy protection of personal computer software (see US Patent 4,168,396, Sept 18, 1979)<ref></ref> to provide more security than dongles could then provide. See also ]. | Modern dongles include built-in strong encryption and use fabrication techniques designed to thwart ]. Typical dongles also now contain ] — essential parts of the software may actually be stored and executed on the dongle. Thus dongles have become ]s that execute program instructions that may be input to the cryptoprocessor only in encrypted form. The original secure cryptoprocessor was designed for copy protection of personal computer software (see US Patent 4,168,396, Sept 18, 1979)<ref></ref> to provide more security than dongles could then provide. See also ]. | ||
| Hardware cloning, where the dongle is emulated by a device driver, is also a threat to traditional dongles. To thwart this, some dongle vendors adopted smart card product, which is widely used in extremely rigid security requirement environments such as military and banking, in their dongle products. | Hardware cloning, where the dongle is emulated by a device driver, is also a threat to traditional dongles. To thwart this, some dongle vendors adopted ], which is widely used in extremely rigid security requirement environments such as military and banking, in their dongle products. | ||
| A more innovative modern dongle is designed with a ] process which transfers encrypted parts of the software vendor's program code or license enforcement into a secure hardware environment (such as in a smart card OS, mentioned above). An ] can port thousands of lines of important ] code into the dongle.{{citation needed|date=December 2012}} | A more innovative modern dongle is designed with a ] process which transfers encrypted parts of the software vendor's program code or license enforcement into a secure hardware environment (such as in a smart card OS, mentioned above). An ] can port thousands of lines of important ] code into the dongle.{{citation needed|date=December 2012}} | ||
| In addition, dongles have been criticized because as they are ], they are easily lost and prone to damage, potentially increasing operational costs such as device cost and delivery cost. | |||
| ==Game consoles== | ==Game consoles== | ||
| Some unlicensed titles for ]s (such as '']'' or '']'') used dongles to connect to officially licensed ]s, in order to circumvent the authentication chip embedded in the console.{{citation needed|date=March 2012}} | Some unlicensed titles for ]s (such as '']'' or '']'') used dongles to connect to officially licensed ]s, in order to circumvent the authentication chip embedded in the console.{{citation needed|date=March 2012}} | ||
| Some ] devices, such as the ] and ] use a dongle. Typically it attaches to the memory card slot of the system, with the disc based software refusing to work if the dongle is not detected. The dongle is also used for holding settings and storage of new codes, added either by the user or through official updates, because the disc, being read only, cannot store them. Some dongles will also double as normal memory cards. | Some ] devices, such as the ] and ] use a dongle. Typically it attaches to the memory card slot of the system, with the disc based software refusing to work if the dongle is not detected. The dongle is also used for holding settings and storage of new codes, added either by the user or through official updates, because the disc, being read only, cannot store them. Some dongles will also double as normal memory cards.{{citation needed|date=March 2012}} | ||
| ==See also== | ==See also== | ||
| * ] | * ] | ||
| * ] | |||
| * ] | * ] | ||
| * ] | * ] | ||
| Line 80: | Line 62: | ||
| {{Software distribution}} | {{Software distribution}} | ||
| {{Authority control}} | |||
| {{DEFAULTSORT:Dongle, software protection}} | {{DEFAULTSORT:Dongle, software protection}} | ||
| Line 86: | Line 69: | ||
| ] | ] | ||
| ] | ] | ||
| ] | ] | ||
| ] | ] | ||
Latest revision as of 17:21, 5 August 2024
Electronic software copy protection device| This article needs additional citations for verification. Please help improve this article by adding citations to reliable sources. Unsourced material may be challenged and removed. Find sources: "Software protection dongle" – news · newspapers · books · scholar · JSTOR (March 2008) (Learn how and when to remove this message) |
A software protection dongle (commonly known as a dongle or key) is an electronic copy protection and content protection device. When connected to a computer or other electronics, they unlock software functionality or decode content. The hardware key is programmed with a product key or other cryptographic protection mechanism and functions via an electrical connector to an external bus of the computer or appliance.
In software protection, dongles are two-interface security tokens with transient data flow with a pull communication that reads security data from the dongle. In the absence of these dongles, certain software may run only in a restricted mode, or not at all. In addition to software protection, dongles can enable functions in electronic devices, such as receiving and processing encoded video streams on television sets.

Etymology
The Merriam-Webster dictionary states that the "First known use of dongle" was in 1981 and that the etymology was "perhaps alteration of dangle."

Dongles rapidly evolved into active devices that contained a serial transceiver (UART) and even a microprocessor to handle transactions with the host. Later versions adopted the USB interface, which became the preferred choice over the serial or parallel interface.
A 1992 advertisement for Rainbow Technologies claimed the word dongle was derived from the name "Don Gall". Though untrue, this has given rise to an urban myth.
Usage

Efforts to introduce dongle copy-protection in the mainstream software market have met stiff resistance from users. Such copy-protection is more typically used with very expensive packages and vertical market software such as CAD/CAM software, cellphone flasher/JTAG debugger software, MICROS Systems hospitality and special retail software, digital audio workstation applications, and some translation memory packages.
In cases such as prepress and printing software, the dongle is encoded with a specific, per-user license key, which enables particular features in the target application. This is a form of tightly controlled licensing, which allows the vendor to engage in vendor lock-in and charge more than it would otherwise for the product. An example is the way Kodak licenses Prinergy to customers: When a computer-to-plate output device is sold to a customer, Prinergy's own license cost is provided separately to the customer, and the base price contains little more than the required licenses to output work to the device.
USB dongles are also a big part of Steinberg's audio production and editing systems, such as Cubase, WaveLab, Hypersonic, HALion, and others. The dongle used by Steinberg's products is also known as a Steinberg Key. The Steinberg Key can be purchased separately from its counterpart applications and generally comes bundled with the "Syncrosoft License Control Center" application, which is cross-platform compatible with both Mac OS X and Windows.
Some software developers use traditional USB flash drives as software license dongles that contain hardware serial numbers in conjunction with the stored device ID strings, which are generally not easily changed by an end-user. A developer can also use the dongle to store user settings or even a complete "portable" version of the application. Not all flash drives are suitable for this use, as not all manufacturers install unique serial numbers into their devices.
Although such medium security may deter a casual hacker, the lack of a processor core in the dongle to authenticate data, perform encryption/decryption, and execute inaccessible binary code makes such a passive dongle inappropriate for all but the lowest-priced software. A simpler and even less secure option is to use unpartitioned or unallocated storage in the dongle to store license data. Common USB flash drives are relatively inexpensive compared to dedicated security dongle devices, but reading and storing data in a flash drive are easy to intercept, alter, and bypass.
Issues
There are potential weaknesses in the implementation of the protocol between the dongle and the copy-controlled software. For example, a simple implementation might define a function to check for the dongle's presence, returning "true" or "false" accordingly, but the dongle requirement can be easily circumvented by modifying the software to always answer "true".
Modern dongles include built-in strong encryption and use fabrication techniques designed to thwart reverse engineering. Typical dongles also now contain non-volatile memory — essential parts of the software may actually be stored and executed on the dongle. Thus dongles have become secure cryptoprocessors that execute program instructions that may be input to the cryptoprocessor only in encrypted form. The original secure cryptoprocessor was designed for copy protection of personal computer software (see US Patent 4,168,396, Sept 18, 1979) to provide more security than dongles could then provide. See also bus encryption.
Hardware cloning, where the dongle is emulated by a device driver, is also a threat to traditional dongles. To thwart this, some dongle vendors adopted smart card product, which is widely used in extremely rigid security requirement environments such as military and banking, in their dongle products.
A more innovative modern dongle is designed with a code porting process which transfers encrypted parts of the software vendor's program code or license enforcement into a secure hardware environment (such as in a smart card OS, mentioned above). An ISV can port thousands of lines of important computer program code into the dongle.
In addition, dongles have been criticized because as they are hardware, they are easily lost and prone to damage, potentially increasing operational costs such as device cost and delivery cost.
Game consoles
Some unlicensed titles for game consoles (such as Super 3D Noah's Ark or Little Red Hood) used dongles to connect to officially licensed ROM cartridges, in order to circumvent the authentication chip embedded in the console.
Some cheat code devices, such as the GameShark and Action Replay use a dongle. Typically it attaches to the memory card slot of the system, with the disc based software refusing to work if the dongle is not detected. The dongle is also used for holding settings and storage of new codes, added either by the user or through official updates, because the disc, being read only, cannot store them. Some dongles will also double as normal memory cards.
See also
- Digital rights management
- License manager
- Lock-out chip
- Product activation
- Security token
- Trusted client
- Software monetization
References
- Amos, S. W.; Amos, Roger S. (2002). Newnes Dictionary of Electronics (4th ed.). Newnes Press. p. 152. ISBN 0750643315. OCLC 144646016. Retrieved 4 July 2013.
- Stobbs, Gregory A. (2012). Software Patents (Third ed.). Wolters Kluwer. pp. 2–90. ISBN 9781454811978. OCLC 802867781. Retrieved 4 July 2013.
- "Dongle". Merriam-Webster. Retrieved 11 June 2019.
- Sentinel advert, Byte Magazine, p. 148
- US Patent 4,168,396
External links
| Software distribution | |
|---|---|
| Licenses | |
| Compensation models | |
| Delivery methods | |
| Deceptive and/or illicit | |
| Software release life cycle | |
| Copy protection | |