| Revision as of 13:32, 25 October 2006 edit83.26.140.21 (talk) →References← Previous edit | Latest revision as of 23:36, 1 December 2024 edit undoRemsense (talk | contribs)Extended confirmed users, Page movers, New page reviewers, Template editors60,107 editsm Reverted 1 edit by Marginataen (talk) to last revision by MrOllieTags: Twinkle Undo | ||
| Line 1: | Line 1: | ||
| {{short description|Type of decentralized and distributed network architecture}} | |||
| :''P2P redirects here. For other uses, see ] or ].'' | |||
| {{Other uses|Peer-to-peer (disambiguation)|Point-to-point (disambiguation)|P2P (disambiguation)}} | |||
| {{More citations needed|date=August 2024}} | |||
| ] | |||
| '''Peer-to-peer''' ('''P2P''') computing or networking is a ] architecture that partitions tasks or workloads between peers. Peers are equally privileged, ] participants in the network, forming a peer-to-peer network of ].<ref>{{Cite web|last=Cope|first=James|date=2002-04-08|title=What's a Peer-to-Peer (P2P) Network?|url=https://www.computerworld.com/article/2588287/networking-peer-to-peer-network.html|access-date=2021-12-21|website=Computerworld|language=en}}</ref> In addition, a ] (PAN) is also in nature a type of ] peer-to-peer network typically between two devices.<ref>{{cite web|title=Why personal area networks are the best thing to happen to hotel Wi-Fi|url=https://www.techradar.com/news/why-personal-area-networks-are-the-best-thing-to-happen-to-hotel-wi-fi|date=12 July 2016|author=Desire Athow}}</ref> | |||
| A '''peer-to-peer''' (or '''P2P''') computer network is a ] that relies primarily on the computing power and ] of the participants in the network rather than concentrating it in a relatively low number of ]s. P2P networks are typically used for connecting nodes via largely '']'' connections. Such networks are useful for many purposes. Sharing content files (see ]) containing audio, video, data or anything in digital format is very common, and realtime data, such as ] traffic, is also passed using P2P technology. | |||
| ]''', where individual ] request services and resources from centralized ]]]Peers make a portion of their resources, such as processing power, disk storage, or ], directly available to other network participants, without the need for central coordination by servers or stable hosts.<ref>Rüdiger Schollmeier, ''A Definition of Peer-to-Peer Networking for the Classification of Peer-to-Peer Architectures and Applications'', Proceedings of the First International Conference on Peer-to-Peer Computing, IEEE (2002).</ref> Peers are both suppliers and consumers of resources, in contrast to the traditional ] in which the consumption and supply of resources are divided.<ref name=CP2P>{{cite journal|last=Bandara|first=H. M. N. D|author2=A. P. Jayasumana|title=Collaborative Applications over Peer-to-Peer Systems – Challenges and Solutions|journal=Peer-to-Peer Networking and Applications|volume=6|issue=3|pages=257–276|year=2012|doi=10.1007/s12083-012-0157-3|arxiv=1207.0790|bibcode=2012arXiv1207.0790D|s2cid=14008541}}</ref> | |||
| A pure peer-to-peer network does not have the notion of clients or servers, but only equal ''peer'' ]s that simultaneously function as both "clients" and "servers" to the other nodes on the network. This model of network arrangement differs from the ] model where communication is usually to and from a central server. A typical example for a non peer-to-peer file transfer is an ] server where the client and server programs are quite distinct, and the clients initiate the download/uploads and the servers react to and satisfy these requests. | |||
| While P2P systems had previously been used in many ]s,<ref name="D. Barkai, 2002">{{Cite book|title=Peer-to-peer computing : technologies for sharing and collaborating on the net|last=Barkai|first=David|date=2001|publisher=Intel Press|isbn=978-0970284679|location=Hillsboro, OR|oclc=49354877|url=https://archive.org/details/ixp1200programmi00john}}</ref> the architecture was popularized by the ] file sharing system ], originally released in 1999.<ref>{{Cite journal|last1=Saroiu|first1=Stefan|last2=Gummadi|first2=Krishna P.|last3=Gribble|first3=Steven D.|date=2003-08-01|title=Measuring and analyzing the characteristics of Napster and Gnutella hosts|url=https://doi.org/10.1007/s00530-003-0088-1|journal=Multimedia Systems|language=en|volume=9|issue=2|pages=170–184|doi=10.1007/s00530-003-0088-1|s2cid=15963045|issn=1432-1882}}</ref> P2P is used in many protocols such as ] file sharing over the Internet<ref>{{Cite web |date=2023-04-19 |title=What Is BitTorrent and Is It Safe? |url=https://www.kaspersky.com/resource-center/definitions/bittorrent |access-date=2023-10-24 |website=www.kaspersky.com |language=en}}</ref> and in ] like ] displaying and ] radio.<ref>{{Cite web |title=האוניברסיטה הפתוחה |url=https://www.openu.ac.il/ErrorMessages/400iv.html |access-date=2024-07-15 |website=www.openu.ac.il}}</ref> The concept has inspired new structures and philosophies in many areas of human interaction. In such social contexts, ] refers to the ] ]ing that has emerged throughout society, enabled by ] technologies in general. | |||
| The earliest peer-to-peer network in widespread use was the ] ] system, in which peers communicated with one another in order to propagate ] articles over the entire Usenet network. Particularly in the earlier days of Usenet, ] was used to extend even beyond the ]. However, the news server system also acted in a client-server form when individual users accessed a local news server in order to read and post articles. | |||
| ==Development== | |||
| Some networks and channels, such as ], ], or ] ], use a client-server structure for some tasks (e.g., searching) and a peer-to-peer structure for others. Networks such as ] or ] use a peer-to-peer structure for all purposes, and are sometimes referred to as true peer-to-peer networks, although Gnutella is greatly facilitated by directory servers that inform peers of the network addresses of other peers. | |||
| ] was established in 1999.]] | |||
| While P2P systems had previously been used in many application domains,<ref name="D. Barkai, 2002"/> the concept was popularized by ] systems such as the music-sharing application ]. The peer-to-peer movement allowed millions of Internet users to connect "directly, forming groups and collaborating to become user-created search engines, virtual supercomputers, and filesystems".<ref name="Oram, A. 2001">{{Cite book|title=Peer-to-peer: harnessing the benefits of disruptive technology |date=2001|publisher=O'Reilly|isbn=9780596001100|editor-last=Oram|editor-first=Andrew|location=]|language=en|oclc=123103147|url=https://archive.org/details/peertopeerharnes00oram_0}}</ref> The basic concept of peer-to-peer computing was envisioned in earlier software systems and networking discussions, reaching back to principles stated in the first ], RFC 1.<ref>RFC 1, ''Host Software'', S. Crocker, IETF Working Group (April 7, 1969)</ref> | |||
| ]'s vision for the ] was close to a P2P network in that it assumed each user of the web would be an active editor and contributor, creating and linking content to form an interlinked "web" of links. The early Internet was more open than the present day, where two machines connected to the Internet could send packets to each other without firewalls and other security measures.<ref>{{Cite journal |title=Internet security enters the Middle Ages |date=1995 |url=https://ieeexplore.ieee.org/document/467613 |access-date=2023-12-14 |doi=10.1109/2.467613 |last1=Oppliger |first1=R. |journal=Computer |volume=28 |issue=10 |pages=100–101 }}</ref><ref name="Oram, A. 2001" />{{Page needed|date=March 2018}} This contrasts with the ]-like structure of the web as it has developed over the years.<ref>{{cite web |url=http://www.w3.org/People/Berners-Lee/1996/ppf.html |title=The World Wide Web: Past, Present and Future |first=Tim |last=Berners-Lee |date=August 1996 |access-date=5 November 2011}}</ref><ref>{{cite book |last1=Sandhu |first1=R. |last2=Zhang |first2=X. |title=Proceedings of the tenth ACM symposium on Access control models and technologies |chapter=Peer-to-peer access control architecture using trusted computing technology |date=2005 |chapter-url=https://doi.org/10.1145/1063979.1064005 |pages=147–158 | doi=10.1145/1063979.1064005|isbn=1595930450 |s2cid=1478064 }}</ref><ref name="Steinmetz, R. 2005 pp. 9-16" /> As a precursor to the Internet, ] was a successful peer-to-peer network where "every participating node could request and serve content". However, ARPANET was not self-organized, and it could not "provide any means for context or content-based routing beyond 'simple' address-based routing."<ref name="Steinmetz, R. 2005 pp. 9-16">{{Cite book|title=Peer-to-Peer Systems and Applications|last1=Steinmetz|first1=Ralf|last2=Wehrle|first2=Klaus|date=2005|publisher=Springer, Berlin, Heidelberg|isbn=9783540291923|series=Lecture Notes in Computer Science|pages=9–16|language=en|chapter=2. What Is This "Peer-to-Peer" About?|doi=10.1007/11530657_2}}</ref> | |||
| Peer-to-peer architecture embodies one of the key technical concepts of the internet, described in the first internet ], "], Host Software" dated ] ]. More recently, the concept has achieved recognition in the general public in the context of the absence of central indexing ]s in architectures used for exchanging multimedia files. | |||
| Therefore, ], a distributed messaging system that is often described as an early peer-to-peer architecture, was established. It was developed in 1979 as a system that enforces a ] of control.<ref>Horton, Mark, and Rick Adams. "Standard for interchange of USENET messages." (1987): 1. https://www.hjp.at/doc/rfc/rfc1036.html {{Webarchive|url=https://web.archive.org/web/20210612114622/https://hjp.at/doc/rfc/rfc1036.html |date=2021-06-12 }}</ref> The basic model is a ] model from the user or client perspective that offers a self-organizing approach to newsgroup servers. However, ]s communicate with one another as peers to propagate Usenet news articles over the entire group of network servers. The same consideration applies to ] email in the sense that the core email-relaying network of ]s has a peer-to-peer character, while the periphery of ]s and their direct connections is strictly a client-server relationship.<ref>{{Cite web |last=Sharma |first=M. K. |title=CLIENT SERVER TECHNOLOGY |url=https://dde-ac.in/Books/C132.pdf |publisher=SWAMI VIVEKANAND SUBHARTI UNIVERSITY}}</ref> | |||
| The concept of peer to peer is increasingly evolving to an expanded usage as the relational dynamic active in distributed networks, i.e. not just computer to computer, but human to human. ] has developed the notion of commons-based peer production to denote collaborative projects such as free software. Associated with peer production are the concept of peer governance (referring to the manner in which peer production projects are managed) and peer property (referring to the new type of licenses which recognize individual authorship but not exclusive property rights, such as the ] and the ] License). | |||
| In May 1999, with millions more people on the Internet, ] introduced the music and file-sharing application called Napster.<ref name="Steinmetz, R. 2005 pp. 9-16"/> Napster was the beginning of peer-to-peer networks, as we know them today, where "participating users establish a virtual network, entirely independent from the physical network, without having to obey any administrative authorities or restrictions".<ref name="Steinmetz, R. 2005 pp. 9-16" /> | |||
| ==Operation of peer-to-peer networks== | |||
| One possible classification of peer-to-peer networks is according to their degree of centralisation: | |||
| ==Architecture== | |||
| Pure peer-to-peer: | |||
| A peer-to-peer network is designed around the notion of equal '']'' nodes simultaneously functioning as both "clients" and "servers" to the other nodes on the network.<ref>{{Cite web |title=Practical Applications of Peer-to-Peer Networks in File Sharing and Content Distribution {{!}} SimpleSwap |url=https://simpleswap.io/blog/practical-applications-of-peer-to-peer-networks-in-file-sharing-and-content-distribution |access-date=2024-08-21 |website=SimpleSwap {{!}} Cryptocurrency exchange blog |language=en}}</ref> This model of network arrangement differs from the ] model where communication is usually to and from a central server. A typical example of a file transfer that uses the client-server model is the ] (FTP) service in which the client and server programs are distinct: the clients initiate the transfer, and the servers satisfy these requests. | |||
| * Peers act as equals, merging the roles of clients and server | |||
| * There is no central server managing the network | |||
| * There is no central router | |||
| ===Routing and resource discovery=== | |||
| Hybrid peer-to-peer: | |||
| Peer-to-peer networks generally implement some form of virtual ] on top of the physical network topology, where the nodes in the overlay form a ] of the nodes in the physical network.<ref>{{Cite web |title=Overlay Network - an overview {{!}} ScienceDirect Topics |url=https://www.sciencedirect.com/topics/computer-science/overlay-network |access-date=2024-08-21 |website=www.sciencedirect.com}}</ref> Data is still exchanged directly over the underlying ] network, but at the ] peers can communicate with each other directly, via the logical overlay links (each of which corresponds to a path through the underlying physical network). Overlays are used for indexing and peer discovery, and make the P2P system independent from the physical network topology. Based on how the nodes are linked to each other within the overlay network, and how resources are indexed and located, we can classify networks as ''unstructured'' or ''structured'' (or as a hybrid between the two).<ref>{{cite book |editor-last=Ahson |editor-first=Syed A. |editor2-last=Ilyas |editor2-first=Mohammad |title=SIP Handbook: Services, Technologies, and Security of Session Initiation Protocol |publisher=Taylor & Francis |year=2008 |isbn=9781420066043 |page=204 |url=https://books.google.com/books?id=CKzPq3-wVdcC&pg=PA204}}</ref><ref>{{cite book |editor-last=Zhu |editor-first=Ce |title=Streaming Media Architectures: Techniques and Applications: Recent Advances |publisher=IGI Global |year=2010 |isbn=9781616928339 |page=265 |url=https://books.google.com/books?id=Cb4dWYVJ_8AC&pg=PA265 |display-editors=etal}}</ref><ref>{{cite book |last=Kamel |first=Mina |chapter=Optimal Topology Design for Overlay Networks |editor-last=Akyildiz |editor-first=Ian F. |title=Networking 2007: Ad Hoc and Sensor Networks, Wireless Networks, Next Generation Internet: 6th International IFIP-TC6 Networking Conference, Atlanta, GA, USA, May 14-18, 2007 Proceedings|publisher=Springer |year=2007 |isbn=9783540726050 |page=714 |chapter-url=https://books.google.com/books?id=r4V2G7yPLIAC&pg=PA714 |display-authors=etal}}</ref> | |||
| * Has a central server that keeps information on peers and responds to requests for that information. | |||
| * Peers are responsible for hosting available resources (as the central server does not have them), for letting the central server know what resources they want to share, and for making its shareable resources available to peers that request it. | |||
| * Route terminals are used addresses, which are referenced by a set of indices to obtain an absolute address. | |||
| ====Unstructured networks==== | |||
| Some examples of "pure" peer-to-peer ] networks designed for ] are ] and ]. | |||
| ] | |||
| ''Unstructured peer-to-peer networks'' do not impose a particular structure on the overlay network by design, but rather are formed by nodes that randomly form connections to each other.<ref>{{cite book |last=Filali |first=Imen |chapter=A Survey of Structured P2P Systems for RDF Data Storage and Retrieval |editor-last=Hameurlain |editor-first=Abdelkader |title=Transactions on Large-Scale Data- and Knowledge-Centered Systems III: Special Issue on Data and Knowledge Management in Grid and PSP Systems |publisher=Springer |year=2011 |isbn=9783642230738|page=21 |chapter-url=https://books.google.com/books?id=pjQr7BHtbCoC&pg=PA21 |display-authors=etal|display-editors=etal}}</ref> (], ], and ] are examples of unstructured P2P protocols).<ref name=":0">{{cite book |last=Zulhasnine |first=Mohammed |chapter=P2P Streaming Over Cellular Networks: Issues, Challenges, and Opportunities |editor=Pathan |title=Building Next-Generation Converged Networks: Theory and Practice |publisher=CRC Press |year=2013 |isbn=9781466507616 |page=99 |chapter-url=https://books.google.com/books?id=tr5PGJk-swIC&pg=PA99 |display-authors=etal|display-editors=etal}}</ref> | |||
| Because there is no structure globally imposed upon them, unstructured networks are easy to build and allow for localized optimizations to different regions of the overlay.<ref>{{cite book |last1=Chervenak |first1=Ann |last2=Bharathi |first2=Shishir |chapter=Peer-to-peer Approaches to Grid Resource Discovery |editor-last=Danelutto |editor-first=Marco |title=Making Grids Work: Proceedings of the CoreGRID Workshop on Programming Models Grid and P2P System Architecture Grid Systems, Tools and Environments 12-13 June 2007, Heraklion, Crete, Greece|publisher=Springer |year=2008 |isbn=9780387784489 |page=67 |chapter-url=https://books.google.com/books?id=adN0pm_BBuYC&pg=PA67 |display-editors=etal}}</ref> Also, because the role of all peers in the network is the same, unstructured networks are highly robust in the face of high rates of "churn"—that is, when large numbers of peers are frequently joining and leaving the network.<ref name="Jin-Unstructured-2010">{{cite book |last1=Jin |first1=Xing |last2=Chan |first2=S.-H. Gary |chapter=Unstructured Peer-to-Peer Network Architectures |editor=Shen |title=Handbook of Peer-to-Peer Networking |publisher=Springer |year=2010 |isbn=978-0-387-09750-3 |page=119 |display-editors=etal}}</ref><ref name="lv-2002">{{cite book |last=Lv |first=Qin |chapter=Can Heterogeneity Make Gnutella Stable? |editor-last=Druschel |editor-first=Peter |title=Peer-to-Peer Systems: First International Workshop, IPTPS 2002, Cambridge, MA, USA, March 7-8, 2002, Revised Papers |publisher=Springer |year=2002 |isbn=9783540441793 |page= |chapter-url=https://books.google.com/books?id=f57AwpUIctcC&pg=PA94 |display-authors=etal |display-editors=etal |url=https://archive.org/details/peertopeersystem0000iptp/page/94 }}</ref> | |||
| ==Advantages of peer-to-peer networks== | |||
| An important goal in peer-to-peer networks is that all clients provide resources, including ], storage space, and computing power. Thus, as nodes arrive and demand on the system increases, the total capacity of the system also increases. This is not true of a client-server architecture with a fixed set of servers, in which adding more clients could mean slower data transfer for all users. | |||
| However, the primary limitations of unstructured networks also arise from this lack of structure. In particular, when a peer wants to find a desired piece of data in the network, the search query must be flooded through the network to find as many peers as possible that share the data. Flooding causes a very high amount of signaling traffic in the network, uses more ]/memory (by requiring every peer to process all search queries), and does not ensure that search queries will always be resolved. Furthermore, since there is no correlation between a peer and the content managed by it, there is no guarantee that flooding will find a peer that has the desired data. Popular content is likely to be available at several peers and any peer searching for it is likely to find the same thing. But if a peer is looking for rare data shared by only a few other peers, then it is highly unlikely that the search will be successful.<ref>{{cite book |last1=Shen |first1=Xuemin |last2=Yu |first2=Heather |last3=Buford |first3=John |last4=Akon |first4=Mursalin |title=Handbook of Peer-to-Peer Networking |publisher=Springer|edition=1st |year=2009 |location=New York |page=118 |isbn=978-0-387-09750-3}}</ref> | |||
| The distributed nature of peer-to-peer networks also increases robustness in case of failures by replicating data over multiple peers, and -- in pure P2P systems -- by enabling peers to find the data without relying on a centralized index server. In the latter case, there is no ] in the system. | |||
| ====Structured networks==== | |||
| When the term peer-to-peer was used to describe the ] network, it implied that the peer ] was important, but, in reality, the great achievement of Napster was the empowerment of the peers (i.e., the fringes of the network) in association with a central index, which made it fast and efficient to locate available content. The peer protocol was just a common way to achieve this. | |||
| ] (DHT) to identify and locate nodes/resources]] | |||
| In ''structured peer-to-peer networks'' the overlay is organized into a specific topology, and the protocol ensures that any node can efficiently<ref>{{Cite web |last1=Dhara |first1=Krishna |last2=Kolberg |first2=Mario |date=January 2010 |title=Overview of Structured Peer-to-Peer Overlay Algorithms |url=https://www.researchgate.net/publication/226809025 }}</ref> search the network for a file/resource, even if the resource is extremely rare.<ref name=":0" /> | |||
| ==Unstructured and structured P2P networks== | |||
| The P2P ] consists of all the participating peers as network nodes. There are links between any two nodes that know each other: i.e. if a participating peer knows the location of another peer in the P2P network, then there is a directed edge from the former node to the latter in the overlay network. Based on how the nodes in the overlay network are linked to each other, we can classify the P2P networks as unstructured or structured. | |||
| The most common type of structured P2P networks implement a ] (DHT),<ref name="CP2P" /><ref>R. Ranjan, A. Harwood, and R. Buyya, "Peer-to-peer based resource discovery in global grids: a tutorial," ''IEEE Commun. Surv.'', vol. 10, no. 2. and P. Trunfio, "Peer-to-Peer resource discovery in Grids: Models and systems," ''Future Generation Computer Systems'' archive, vol. 23, no. 7, Aug. 2007.</ref> in which a variant of ] is used to assign ownership of each file to a particular peer.<ref>{{cite book |last1=Kelaskar |first1=M. |last2=Matossian |first2=V. |last3=Mehra |first3=P. |last4=Paul |first4=D. |last5=Parashar |first5=M. |year=2002 |url=http://portal.acm.org/citation.cfm?id=873218 |title=A Study of Discovery Mechanisms for Peer-to-Peer Application |pages=444– |publisher=IEEE Computer Society |isbn=9780769515823 }}</ref><ref name="P2P_API">{{cite book |last1=Dabek |first1=Frank |first2=Ben |last2=Zhao |first3=Peter |last3=Druschel |first4=John |last4=Kubiatowicz |first5=Ion |last5=Stoica |title=Peer-to-Peer Systems II |chapter=Towards a Common API for Structured Peer-to-Peer Overlays |year=2003 |volume=2735 |series=Lecture Notes in Computer Science |pages=33–44 |doi=10.1007/978-3-540-45172-3_3 |isbn=978-3-540-40724-9 |citeseerx=10.1.1.12.5548 }}</ref> This enables peers to search for resources on the network using a ]: that is, (''key'', ''value'') pairs are stored in the DHT, and any participating node can efficiently retrieve the value associated with a given key.<ref>Moni Naor and Udi Wieder. {{Webarchive|url=https://web.archive.org/web/20191209032152/http://www.wisdom.weizmann.ac.il/~naor/PAPERS/dh.pdf |date=2019-12-09 }}. Proc. SPAA, 2003.</ref><ref>Gurmeet Singh Manku. {{webarchive|url=https://web.archive.org/web/20040910154927/http://www-db.stanford.edu/~manku/phd/index.html |date=2004-09-10 }}. Ph. D. Thesis (Stanford University), August 2004.</ref> | |||
| An unstructured P2P network is formed when the overlay links are established arbitrarily. Such networks can be easily constructed as a new peer that wants to join the network can copy existing links of another node and then form its own links over time. In an unstructured P2P network, if a peer wants to find a desired piece of data in the network, the query has to be flooded through the network in order to find as many peers as possible that share the data. The main disadvantage with such networks is that the queries may not always be resolved. A popular content is likely to be available at several peers and any peer searching for it is likely to find the same, but, if a peer is looking for a rare or not-so-popular data shared by only a few other peers, then it is highly unlikely that search be successful. Since there is no correlation between a peer and the content managed by it, there is no guarantee that flooding will find a peer that has the desired data. Flooding also causes a high amount of signalling traffic in the network and hence such networks typically have a very poor search efficiency. Most of the popular P2P networks such as ], ] and ] are unstructured. | |||
| ] | |||
| However, in order to route traffic efficiently through the network, nodes in a structured overlay must maintain lists of neighbors<ref>{{Cite web|url=https://sites.cs.ucsb.edu/~ravenben/publications/pdf/impact-iptps.pdf|title=Impact of Neighbor Selection on Performance and Resilience of Structured P2P Networks|author=Byung-Gon Chun, Ben Y. Zhao, John D. Kubiatowicz|date=2005-02-24|access-date=2019-08-24}}</ref> that satisfy specific criteria. This makes them less robust in networks with a high rate of ''churn'' (i.e. with large numbers of nodes frequently joining and leaving the network).<ref name="lv-2002" /><ref>{{cite book|last=Li |first=Deng |title=An Efficient, Scalable, and Robust P2P Overlay for Autonomic Communication |editor-last=Vasilakos |editor-first=A.V. |publisher=Springer |year=2009 |isbn=978-0-387-09752-7 |page=329 |url=https://books.google.com/books?id=c02mTcXW_U4C&pg=PA329 |display-authors=etal|display-editors=etal}}</ref> More recent evaluation of P2P resource discovery solutions under real workloads have pointed out several issues in DHT-based solutions such as high cost of advertising/discovering resources and static and dynamic load imbalance.<ref>{{cite journal |last1=Bandara |first1=H. M. N. Dilum |first2=Anura P. |last2=Jayasumana |title=Evaluation of P2P Resource Discovery Architectures Using Real-Life Multi-Attribute Resource and Query Characteristics |journal=IEEE Consumer Communications and Networking Conf. (CCNC '12) |date=January 2012}}</ref> | |||
| Structured P2P networks overcome the limitations of unstructured networks by maintaining a ] (DHT) and by allowing each peer to be responsible for a specific part of the content in the network. These networks use ] and assign values to every content and every peer in the network and then follow a global protocol in determining which peer is responsible for which content. This way, whenever a peer wants to search for some data, it uses the global protocol to determine the peer(s) responsible for the data and then directs the search towards the responsible peer(s). Some well known structured P2P networks are: | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| Notable distributed networks that use DHTs include ], an alternative to ] distributed tracker, the ], the ], and the ]. Some prominent research projects include the ], ], ], ], a self-organized and emerging overlay network, and ].<ref>{{cite book | last1=Korzun | first1=Dmitry| last2=Gurtov| first2 = Andrei| title= Structured P2P Systems: Fundamentals of Hierarchical Organization, Routing, Scaling, and Security|publisher=Springer | isbn = 978-1-4614-5482-3 |date= November 2012 | url=https://www.springer.com/gp/book/9781461454823}}</ref> DHT-based networks have also been widely utilized for accomplishing efficient resource discovery<ref>{{cite web |last1=Ranjan |first1=Rajiv |last2=Harwood |first2=Aaron |last3=Buyya |first3=Rajkumar |date=1 December 2006 |url=http://www.cs.mu.oz.au/%7Erranjan/pgrid.pdf |title=A Study on Peer-to-Peer Based Discovery of Grid Resource Information |access-date=25 August 2008 |archive-date=14 May 2011 |archive-url=https://web.archive.org/web/20110514055004/http://www.cs.mu.oz.au/%7Erranjan/pgrid.pdf |url-status=dead }}</ref><ref>{{cite web |url=http://gridbus.org/papers/DecentralisedDiscoveryGridFed-eScience2007.pdf |first1=Rajiv |last1=Ranjan |first2=Lipo |last2=Chan |first3=Aaron |last3=Harwood |first4=Shanika |last4=Karunasekera |first5=Rajkumar |last5=Buyya |title=Decentralised Resource Discovery Service for Large Scale Federated Grids |url-status=dead |archive-url=https://web.archive.org/web/20080910170417/http://gridbus.org/papers/DecentralisedDiscoveryGridFed-eScience2007.pdf |archive-date=2008-09-10 }}</ref> for ] systems, as it aids in resource management and scheduling of applications. | |||
| ==Legal controversy== | |||
| {{See|EU Copyright Directive}} | |||
| Under US law "the Betamax decision" (]), case holds that copying "technologies" are not ''inherently'' illegal, if substantial non-infringing use can be made of them. This decision, predating the widespread use of the ] applies to most data networks, including peer-to-peer networks, since distribution of correctly licensed files can be performed. These non-infringing uses include sending open source software, public domain files and out of copyright works. Other jurisdictions tend to view the situation in somewhat similar ways. | |||
| ====Hybrid models==== | |||
| In practice, many, often most, of the files shared on peer-to-peer networks are copies of copyrighted popular music and movies. Sharing of these copies among strangers is illegal in most jurisdictions. This has led many observers, including most media companies and some peer-to-peer critics, to conclude that the networks themselves pose grave threats to the established distribution model. The research that attempts to measure actual monetary loss has been somewhat equivocal. Whilst on paper the existence of these networks results in large losses, the actual income does not seem to have changed much since these networks started up. Whether the threat is real or not, both the ] and the ] now spend large amounts of money attempting to lobby lawmakers for the creation of new laws, and some copyright owners pay companies to help legally challenge users engaging in illegal sharing of their material. | |||
| Hybrid models are a combination of peer-to-peer and client–server models.<ref>{{cite book |last=Darlagiannis |first=Vasilios |chapter=Hybrid Peer-to-Peer Systems|editor-last1=Steinmetz |editor-first1=Ralf |editor-last2=Wehrle |editor-first2=Klaus |title=Peer-to-Peer Systems and Applications |publisher=Springer |year=2005 |isbn=9783540291923 |chapter-url=https://books.google.com/books?id=A8CLZ1FB4qoC&pg=PA353 }}</ref> A common hybrid model is to have a central server that helps peers find each other. ] was an example of a hybrid model .{{citation needed|date=June 2023}} There are a variety of hybrid models, all of which make trade-offs between the centralized functionality provided by a structured server/client network and the node equality afforded by the pure peer-to-peer unstructured networks. Currently, hybrid models have better performance than either pure unstructured networks or pure structured networks because certain functions, such as searching, do require a centralized functionality but benefit from the decentralized aggregation of nodes provided by unstructured networks.<ref>{{cite journal |last1=Yang |first1=Beverly |last2=Garcia-Molina |first2=Hector |year=2001 |title=Comparing Hybrid Peer-to-Peer Systems |journal=Very Large Data Bases |url=http://infolab.stanford.edu/~byang/pubs/hybridp2p_long.pdf |access-date=8 October 2013}}</ref> | |||
| ====CoopNet content distribution system==== | |||
| In spite of the Betamax decision, peer-to-peer networks themselves have been targeted by the representatives of those artists and organizations who license their creative works, including industry trade organizations such as the RIAA and MPAA as a potential threat. The Napster service was shut down by an RIAA lawsuit. In this case, Napster had been deliberately marketed as a way to distribute audio files without permission from the copyright owners. However, Napster's use of a central server distinguishes it, on its facts, from the next generation peer-to-peer technology, in which the communication of files is truly "peer to peer". | |||
| '''CoopNet (Cooperative Networking)''' was a proposed system for off-loading serving to peers who have recently ]ed content, proposed by computer scientists Venkata N. Padmanabhan and Kunwadee Sripanidkulchai, working at ] and ].<ref>{{Cite book| last1 = Padmanabhan| first1 = Venkata N.| last2 = Sripanidkulchai| first2 = Kunwadee| publication-date = March 2002| year = 2002| title = The Case for Cooperative Networking (PostScript with addendum)| volume = Proceedings of the First International Workshop on Peer-to-Peer Systems| series = Lecture Notes in Computer Science| location = Cambridge, MA| publisher = Springer| pages = | isbn = 978-3-540-44179-3| doi = 10.1007/3-540-45748-8_17| url = https://archive.org/details/peertopeersystem0000iptp/page/178}} {{Webarchive|url=https://web.archive.org/web/20070417140616/http://research.microsoft.com/projects/CoopNet/papers/iptps02-with-addendum.pdf |date=2007-04-17 }} {{Webarchive|url=https://web.archive.org/web/20230101095443/https://link.springer.com/chapter/10.1007/3-540-45748-8_17 |date=2023-01-01 }}</ref><ref>{{Cite web|url=http://research.microsoft.com/projects/CoopNet/|title=CoopNet: Cooperative Networking|publisher=Microsoft Research}} Project home page.</ref> When a ] experiences an increase in load it redirects incoming peers to other peers who have agreed to ] the content, thus off-loading balance from the server. All of the information is retained at the server. This system makes use of the fact that the bottleneck is most likely in the outgoing bandwidth than the ], hence its server-centric design. It assigns peers to other peers who are 'close in ]' to its neighbors in an attempt to use locality. If multiple peers are found with the same ] it designates that the node choose the fastest of its neighbors. ] is transmitted by having clients ] the previous stream, and then transmit it piece-wise to new nodes. | |||
| ===Security and trust=== | |||
| In '']'', the U.S. Supreme Court reversed a decision of the Ninth Circuit Court of Appeals which had granted a summary judgment of dismissal, and held that were factual issues concerning whether the defendant p2p software providers had, or had not, encouraged their users to infringe copyrights. If they had done so, they could be held liable for secondary copyright infringement. | |||
| Peer-to-peer systems pose unique challenges from a ] perspective. Like any other form of ], P2P applications can contain ]. What makes this particularly dangerous for P2P software, however, is that peer-to-peer applications act as servers as well as clients, meaning that they can be more vulnerable to ].<ref name="vu-p2p-principles-p8">{{cite book |last=Vu |first=Quang H. |title=Peer-to-Peer Computing: Principles and Applications |publisher=Springer |year=2010 |isbn=978-3-642-03513-5 |page=8 |display-authors=etal}}</ref> | |||
| ====Routing attacks==== | |||
| A little over a year later, the RIAA initiated the first major post-Grokster case, '''', in Manhattan federal court. Lime Wire has counterclaimed in that suit, charging the major record companies with antitrust violations and other misconduct. | |||
| Since each node plays a role in routing traffic through the network, malicious users can perform a variety of "routing attacks", or ] attacks. Examples of common routing attacks include "incorrect lookup routing" whereby malicious nodes deliberately forward requests incorrectly or return false results, "incorrect routing updates" where malicious nodes corrupt the routing tables of neighboring nodes by sending them false information, and "incorrect routing network partition" where when new nodes are joining they bootstrap via a malicious node, which places the new node in a partition of the network that is populated by other malicious nodes.<ref name="vu-p2p-principles-p8" /> | |||
| ====Corrupted data and malware==== | |||
| Shortly thereafter, the lower court judge in <i>Grokster</i> found one of the defendants, Streamcast, the maker of Morpheus, to be liable under the standards enunciated by the Supreme Court. | |||
| {{See also|Data validation|Malware}} | |||
| The prevalence of ] varies between different peer-to-peer protocols.<ref>{{Cite web |title=Malware Propagation Modelling in Peer-to-Peer Networks: A Review |url=https://bradscholars.brad.ac.uk/bitstream/handle/10454/16651/Malware%20Propagation%20Modelling%20in%20Peer%20to%20Peer%20Networks.pdf?sequence=4&isAllowed=y}}</ref> Studies analyzing the spread of malware on P2P networks found, for example, that 63% of the answered download requests on the ] network contained some form of malware, whereas only 3% of the content on ] contained malware. In both cases, the top three most common types of malware accounted for the large majority of cases (99% in gnutella, and 65% in OpenFT). Another study analyzing traffic on the ] network found that 15% of the 500,000 file sample taken were infected by one or more of the 365 different ] that were tested for.<ref>{{cite book |last=Goebel |first=Jan |chapter=Measurement and Analysis of Autonomous Spreading Malware in a University Environment |editor-last=Hämmerli |editor-first=Bernhard Markus |editor2-last=Sommer |editor2-first=Robin |title=Detection of Intrusions and Malware, and Vulnerability Assessment: 4th International Conference, DIMVA 2007 Lucerne, Switzerland, July 12-13, 2007 Proceedings |publisher=Springer |year=2007 |isbn=9783540736134 |page=112 |chapter-url=https://books.google.com/books?id=M0PfEaVa9QIC&pg=PA112 |display-authors=etal}}</ref> | |||
| Corrupted data can also be distributed on P2P networks by modifying files that are already being shared on the network. For example, on the ] network, the ] managed to introduce faked chunks into downloads and downloaded files (mostly ] files). Files infected with the RIAA virus were unusable afterwards and contained malicious code. The RIAA is also known to have uploaded fake music and movies to P2P networks in order to deter illegal file sharing.<ref>{{cite news |url=https://www.nytimes.com/2003/05/04/business/04MUSI.html |title=Software Bullet Is Sought to Kill Musical Piracy |last=Sorkin |first=Andrew Ross |date=4 May 2003 |newspaper=New York Times |access-date=5 November 2011}}</ref> Consequently, the P2P networks of today have seen an enormous increase of their security and file verification mechanisms. Modern ], ] and different encryption methods have made most networks resistant to almost any type of attack, even when major parts of the respective network have been replaced by faked or nonfunctional hosts.<ref>{{cite tech report |first=Vivek |last=Singh |first2=Himani |last2=Gupta |title= Anonymous File Sharing in Peer to Peer System by Random Walks |number=123456789/9306 |institution=SRM University |year=2012 }}</ref> | |||
| As actions to defend copyright infringement by media companies expand, the networks have quickly adapted and constantly become both technologically and legally more difficult to dismantle. This has caused the users that are actually breaking the law to become targets, because whilst the underlying technology may be legal, the abuse of it by individuals redistributing content in a copyright infringing way is clearly not. | |||
| ===Resilient and scalable computer networks=== | |||
| ] networks allow for distribution of material - legal or not - with little or no legal accountability across a wide variety of jurisdictions. Many profess that this will lead to greater or easier trading of illegal material and even (as some suggest) facilitate ], and call for its regulation on those grounds . Others counter that the potential for illegal uses should not prevent the technology from being used for legal purposes, that the presumption of innocence must apply, and that non peer-to-peer technologies like ], which also possess anonymizing services, have similar capabilities. | |||
| {{See also|Wireless mesh network|Distributed computing}} | |||
| The decentralized nature of P2P networks increases robustness because it removes the ] that can be inherent in a client–server based system.<ref name="ms-overlay-survey">{{cite web |url=http://academic.research.microsoft.com/Publication/2633870/a-survey-and-comparison-of-peer-to-peer-overlay-network-schemes |title=A survey and comparison of peer-to-peer overlay network schemes |last1=Lua |first1=Eng Keong |last2=Crowcroft |first2=Jon |last3=Pias |first3=Marcelo |last4=Sharma |first4=Ravi |last5=Lim |first5=Steven |year=2005 |url-status=dead |archive-url=https://web.archive.org/web/20120724222234/http://academic.research.microsoft.com/Publication/2633870/a-survey-and-comparison-of-peer-to-peer-overlay-network-schemes |archive-date=2012-07-24 }}</ref> As nodes arrive and demand on the system increases, the total capacity of the system also increases, and the likelihood of failure decreases. If one peer on the network fails to function properly, the whole network is not compromised or damaged. In contrast, in a typical client–server architecture, clients share only their demands with the system, but not their resources. In this case, as more clients join the system, fewer resources are available to serve each client, and if the central server fails, the entire network is taken down. | |||
| ===Distributed storage and search=== | |||
| In the ] (EU), the 2001 ], which implemented the 1996 ] ("World Intellectual Property Organization Copyright Treaty"), prohibits peer-to-peer, claiming it is a violation of the directive. However, not all European member states have implemented the directive in national legislation. Notably, on December 22, 2005, after discussing the EU directive, the French parliament passed two amendments legalizing the exchange of copies on the internet for private use. In a later proceeding, the French government withdrew the article in question and made illegal any p2p client obviously aimed at sharing copyrighted material. The term "obviously" was not defined. The project of law (called ]) has still to be discussed by the French senate and, if the decision differs too much from the Parliament's, it will be debated on second lecture back at the Parliament (]). | |||
| ]" using ], a free ] that runs on a peer-to-peer network instead of making requests to centralized index servers]] | |||
| There are both advantages and disadvantages in P2P networks related to the topic of data ], recovery, and availability. In a centralized network, the system administrators are the only forces controlling the availability of files being shared. If the administrators decide to no longer distribute a file, they simply have to remove it from their servers, and it will no longer be available to users. Along with leaving the users powerless in deciding what is distributed throughout the community, this makes the entire system vulnerable to threats and requests from the government and other large forces. | |||
| For example, ] has been pressured by the ], ], and entertainment industry to filter out copyrighted content. Although server-client networks are able to monitor and manage content availability, they can have more stability in the availability of the content they choose to host. A client should not have trouble accessing obscure content that is being shared on a stable centralized network. P2P networks, however, are more unreliable in sharing unpopular files because sharing files in a P2P network requires that at least one node in the network has the requested data, and that node must be able to connect to the node requesting the data. This requirement is occasionally hard to meet because users may delete or stop sharing data at any point.<ref>{{cite journal |year=2003 |title=Looking up data in P2P systems |journal=Communications of the ACM |volume=46 |issue=2 |pages=43–48 |doi=10.1145/606272.606299 |url=http://www.nms.lcs.mit.edu/papers/p43-balakrishnan.pdf |access-date=8 October 2013|last1=Balakrishnan |first1=Hari |last2=Kaashoek |first2=M. Frans |last3=Karger |first3=David |last4=Morris |first4=Robert |last5=Stoica |first5=Ion |citeseerx=10.1.1.5.3597 |s2cid=2731647 }}</ref> | |||
| Interestingly, Canada stands out by authorizing, at least until the projected copyright reform, downloads on peer-to-peer networks under the "private copying" exception. | |||
| In a P2P network, the community of users is entirely responsible for deciding which content is available. Unpopular files eventually disappear and become unavailable as fewer people share them. Popular files, however, are highly and easily distributed. Popular files on a P2P network are more stable and available than files on central networks. In a centralized network, a simple loss of connection between the server and clients can cause a failure, but in P2P networks, the connections between every node must be lost to cause a data-sharing failure. In a centralized system, the administrators are responsible for all data recovery and backups, while in P2P systems, each node requires its backup system. Because of the lack of central authority in P2P networks, forces such as the recording industry, ], ], and the government are unable to delete or stop the sharing of content on P2P systems.<ref>{{cite web |url=http://www.p2pnews.net/2012/06/14/art-thou-a-peer/ |title=Art thou a Peer? |author=<!--Staff writer(s); no by-line.--> |date=14 June 2012 |website=www.p2pnews.net |access-date=10 October 2013 |url-status=dead |archive-url=https://web.archive.org/web/20131006022409/http://www.p2pnews.net/2012/06/14/art-thou-a-peer/ |archive-date=6 October 2013 }}</ref> | |||
| ===Important Cases=== | |||
| ==Applications== | |||
| * US law | |||
| **] (The Betamax decision) | |||
| ** ] | |||
| ===Content delivery=== | |||
| ==Computer science perspective== | |||
| In P2P networks, clients both provide and use resources. This means that unlike client–server systems, the content-serving capacity of peer-to-peer networks can actually ''increase'' as more users begin to access the content (especially with protocols such as ] that require users to share, refer a performance measurement study<ref>{{cite book | chapter-url=https://ieeexplore.ieee.org/document/6488040 | doi=10.1109/NCC.2013.6488040 | chapter=Performance analysis of BitTorrent protocol | title=2013 National Conference on Communications (NCC) | date=2013 | last1=Sharma | first1=Parul | last2=Bhakuni | first2=Anuja | last3=Kaushal | first3=Rishabh | pages=1–5 | isbn=978-1-4673-5952-8 }}</ref>). This property is one of the major advantages of using P2P networks because it makes the setup and running costs very small for the original content distributor.<ref>{{cite journal |last=Li |first=Jin |title=On peer-to-peer (P2P) content delivery |journal=Peer-to-Peer Networking and Applications |volume=1 |issue=1 |doi=10.1007/s12083-007-0003-1 |pages=45–63 ≤≥|url=http://www.land.ufrj.br/~classes/coppe-redes-2008/biblio/P2P-content-delivery.pdf |year=2008 |s2cid=16438304 }}</ref><ref>{{cite book |last=Stutzbach |first=Daniel |chapter=The scalability of swarming peer-to-peer content delivery |editor-last=Boutaba |editor-first=Raouf |title=NETWORKING 2005 -- Networking Technologies, Services, and Protocols; Performance of Computer and Communication Networks; Mobile and Wireless Communications Systems |publisher=Springer |year=2005 |isbn=978-3-540-25809-4 |pages=15–26 |chapter-url=http://ix.cs.uoregon.edu/~reza/PUB/networking05.pdf |display-authors=etal|display-editors=etal}}</ref> | |||
| Technically, a completely pure peer-to-peer application must implement only peering protocols that do not recognize the concepts of "server" and "client". Such ''pure'' peer applications and networks are rare. Most networks and applications described as peer-to-peer actually contain or rely on some non-peer elements, such as ]. Also, real world applications often use multiple protocols and act as client, server, and peer simultaneously, or over time. Completely decentralized networks of peers have been in use for many years: two examples are ] (]) and ] (]). | |||
| ===File-sharing networks=== | |||
| Many P2P systems use stronger peers (super-peers, super-nodes) as servers and client-peers are connected in a star-like fashion to a single super-peer. | |||
| ] networks such as ], ], and the ] have been useful in popularizing peer-to-peer technologies. These advancements have paved the way for ] and services, including distributed caching systems like Correli Caches to enhance performance.<ref>Gareth Tyson, Andreas Mauthe, Sebastian Kaune, Mu Mu and Thomas Plagemann. Corelli: A Dynamic Replication Service for Supporting Latency-Dependent Content in Community Networks. In Proc. 16th ACM/SPIE Multimedia Computing and Networking Conference (MMCN), San Jose, CA (2009).{{cite web |title=Archived copy |url=http://www.dcs.kcl.ac.uk/staff/tysong/files/MMCN09.pdf |url-status=dead |archive-url=https://web.archive.org/web/20110429181811/http://www.dcs.kcl.ac.uk/staff/tysong/files/MMCN09.pdf |archive-date=2011-04-29 |access-date=2011-03-12}}</ref> Furthermore, peer-to-peer networks have made possible the software publication and distribution, enabling efficient sharing of ] and various games though ] networks. | |||
| ====Copyright infringements==== | |||
| Sun added classes to the Java technology to speed the development of peer-to-peer applications quickly in the late ] so that developers could build decentralized real time chat applets and applications before Instant Messaging networks were popular. This effort is now being continued with the ] project. | |||
| Peer-to-peer networking involves data transfer from one user to another without using an intermediate server. Companies developing P2P applications have been involved in numerous legal cases, primarily in the United States, over conflicts with ] law.<ref name="Springer">{{cite book |last=Glorioso |first=Andrea |chapter=The Social Impact of P2P Systems |editor=Shen |title=Handbook of Peer-to-Peer Networking|publisher=Springer |year=2010 |isbn=978-0-387-09750-3 |page=48 |display-authors=etal|display-editors=etal}}</ref> Two major cases are ''] vs RIAA'' and '']''.<ref name="news.cnet.com">{{cite web |author=John Borland |title=Judge: File-Swapping Tools are Legal |url=http://news.cnet.com/Judge-File-swapping-tools-are-legal/2100-1027_3-998363.html/ |date=April 25, 2003 |archive-url=https://web.archive.org/web/20120310165410/http://news.cnet.com/Judge-File-swapping-tools-are-legal/2100-1027_3-998363.html |archive-date=2012-03-10 |website=news.cnet.com |url-status=dead}}</ref> In the last case, the Court unanimously held that defendant peer-to-peer file sharing companies Grokster and Streamcast could be sued for inducing copyright infringement. | |||
| ===Multimedia=== | |||
| Peer-to-peer systems and applications have attracted a great deal of attention from computer science research; some prominent research projects include the ], the ], the ], a self-organized and emerging overlay network and the ] (see below for external links related to these projects). | |||
| The ] and ] protocols are used in various peer-to-peer applications. Some ] multimedia applications leverage a peer-to-peer network in conjunction with streaming servers to stream audio and video to their clients. ] is employed for multicasting streams. Additionally, a project called ], undertaken by ], MIT, and ], aims to facilitate file sharing among educational institutions globally. Another notable program, ], enables users to create anonymous and autonomous web portals that are distributed via a peer-to-peer network. | |||
| ===Other P2P applications=== | |||
| ==Use of peer-to-peer networks in bioinformatics== | |||
| ] connect peers]]] is a distributed version-controlled publishing platform. ], is an ] used to browse the Internet ]. Unlike the related I2P, the ] is not itself peer-to-peer{{Dubious|date=December 2022}}; however, it can enable peer-to-peer applications to be built on top of it via ]. The ] (IPFS) is a ] and network designed to create a ], peer-to-peer method of storing and sharing ] distribution protocol, with nodes in the IPFS network forming a ]. ] is a peer-to-peer chat and ] app. ] is a peer-to-peer protocol designed for the ]. ] is a ] designed to be independent from the Internet. ] is a connection-sharing application that shares Internet access with other devices using Wi-Fi or Bluetooth. | |||
| Peer-to-peer networks have also begun to attract attention from scientists in other disciplines, especially those that deal with large datasets such as ]. P2P networks can be used to run large programs designed to carry out tests to identify drug candidates. The first such program was begun in 2001 the Centre for Computational Drug Discovery at ] in cooperation with the National Foundation for Cancer Research. There are now several similar programs running under the auspices of the ]. On a smaller scale, a self-administered program for computational biologists to run and compare various bioinformatics software is available from . Academic institutions have also begun experimenting with file sharing: one of the most interesting projects is ]. | |||
| ] is a directory-syncing app. Research includes projects such as the ], the ], the ], and the ]. ] is a peer-to-peer ] capable of supporting many different types of applications, primarily ]. ] is also a directory-syncing app. ] l and ] applications are designed to power real-time marketplaces. The ] is conducting research on P2P networks as part of its modern network warfare strategy.<ref>{{cite news |last=Walker |first=Leslie |date=2001-11-08 |title=Uncle Sam Wants Napster! |url=https://www.washingtonpost.com/ac2/wp-dyn?pagename=article&node=washtech/techthursday/columns/dotcom&contentId=A59099-2001Nov7 |access-date=2010-05-22 |newspaper=The Washington Post}}</ref> In May 2003, ], then director of ], testified that the United States military uses P2P networks. ] is a P2P ] ] in ] for use in ]s, as well as in the ] standalone version that bridges WebTorrent and ] serverless networks. ], in ], uses a proprietary peer-to-peer technology called "Delivery Optimization" to deploy operating system updates using end-users' PCs either on the local network or other PCs. According to Microsoft's Channel 9, this led to a 30%-50% reduction in Internet bandwidth usage.<ref>Hammerksjold Andreas; Engler, Narkis, {{Webarchive|url=https://web.archive.org/web/20190204231107/https://channel9.msdn.com/Events/Ignite/Microsoft-Ignite-Orlando-2017/BRK2048|date=2019-02-04}}, '']'', 11 October 2017, Retrieved on 4 February 2019.</ref> Artisoft's ] was built as a peer-to-peer operating system where machines can function as both servers and workstations simultaneously. ] Hotline Client was built with decentralized servers and tracker software dedicated to any type of files and continues to operate today. ] are peer-to-peer-based ] that use ]s | |||
| ==Attacks on peer-to-peer networks== | |||
| * ] | |||
| Many peer-to-peer networks are under constant attack by people with a variety of motives. | |||
| * ] | |||
| ==Social implications== | |||
| Examples include: | |||
| * poisoning attacks (e.g. providing files whose contents are different from the description) | |||
| * polluting attacks (e.g. inserting "bad" chunks/packets into an otherwise valid file on the network) | |||
| * defection attacks (users or software that make use of the network without contributing resources to it) | |||
| * insertion of viruses to carried data (e.g. downloaded or carried files may be infected with viruses or other malware) | |||
| * ] in the peer-to-peer network software itself (e.g. distributed software may contain spyware) | |||
| * ] attacks (attacks that may make the network run very slowly or break completely) | |||
| * filtering (network operators may attempt to prevent peer-to-peer network data from being carried) | |||
| * identity attacks (e.g. tracking down the users of the network and harassing or legally attacking them) | |||
| * ] (e.g. sending unsolicited information across the network- not necessarily as a denial of service attack) | |||
| ===Incentivizing resource sharing and cooperation=== | |||
| Most attacks can be defeated or controlled by careful design of the peer-to-peer network and through the use of encryption. P2P network defense is in fact closely related to the "]". However, almost any network will fail when the majority of the peers are trying to damage it, and many protocols may be rendered impotent by far fewer numbers. | |||
| ] protocol''': In this animation, the colored bars beneath all of the 7 clients in the upper region above represent the file being shared, with each color representing an individual piece of the file. After the initial pieces transfer from the ] (large system at the bottom), the pieces are individually transferred from client to client. The original seeder only needs to send out one copy of the file for all the clients to receive a copy.]] | |||
| Cooperation among a community of participants is key to the continued success of P2P systems aimed at casual human users; these reach their full potential only when large numbers of nodes contribute resources. But in current practice, P2P networks often contain large numbers of users who utilize resources shared by other nodes, but who do not share anything themselves (often referred to as the "freeloader problem"). | |||
| Freeloading can have a profound impact on the network and in some cases can cause the community to collapse.<ref>Krishnan, R., Smith, M. D., Tang, Z., & Telang, R. (2004, January). The impact of free-riding on peer-to-peer networks. In System Sciences, 2004. Proceedings of the 37th Annual Hawaii International Conference on (pp. 10-pp). IEEE.</ref> In these types of networks "users have natural disincentives to cooperate because cooperation consumes their own resources and may degrade their own performance".<ref name="Feldman, M. 2004, pp. 102-111">Feldman, M., Lai, K., Stoica, I., & Chuang, J. (2004, May). Robust incentive techniques for peer-to-peer networks. In Proceedings of the 5th ACM conference on Electronic commerce (pp. 102-111). ACM.</ref> Studying the social attributes of P2P networks is challenging due to large populations of turnover, asymmetry of interest and zero-cost identity.<ref name="Feldman, M. 2004, pp. 102-111" /> A variety of incentive mechanisms have been implemented to encourage or even force nodes to contribute resources.<ref>{{cite book |last=Vu |first=Quang H. |title=Peer-to-Peer Computing: Principles and Applications |publisher=Springer |year=2010 |isbn=978-3-642-03513-5 |page=172 |display-authors=etal}}</ref><ref name="vu-p2p-principles-p8" /> | |||
| ==Networks, protocols and applications== | |||
| <!-- | |||
| Some researchers have explored the benefits of enabling virtual communities to self-organize and introduce incentives for resource sharing and cooperation, arguing that the social aspect missing from today's P2P systems should be seen both as a goal and a means for self-organized virtual communities to be built and fostered.<ref>P. Antoniadis and B. Le Grand, "Incentives for resource sharing in self-organized communities: From economics to social psychology," Digital Information Management (ICDIM '07), 2007</ref> Ongoing research efforts for designing effective incentive mechanisms in P2P systems, based on principles from game theory, are beginning to take on a more psychological and information-processing direction. | |||
| Please don't forget to add new multiple network applications also to the list below for that. | |||
| ====Privacy and anonymity==== | |||
| Please use the Format: | |||
| Some peer-to-peer networks (e.g. ]) place a heavy emphasis on ] and ]—that is, ensuring that the contents of communications are hidden from eavesdroppers, and that the identities/locations of the participants are concealed. ] can be used to provide ], ], authorization, and authentication for data/messages. ] and other ] protocols (e.g. Tarzan) can be used to provide anonymity.<ref>{{cite book |last=Vu |first=Quang H. |title=Peer-to-Peer Computing: Principles and Applications |publisher=Springer |year=2010 |isbn=978-3-642-03513-5 |pages=179–181 |display-authors=etal}}</ref> | |||
| * <network/protocol>: <list of applications using that network> | |||
| Perpetrators of ] and other ] have used peer-to-peer platforms to carry out activities with anonymity.<ref>{{cite web|url=https://news.un.org/en/story/2020/03/1058501|title=No country is free from child sexual abuse, exploitation, UN's top rights forum hears|date=March 3, 2020|website=UN News}}</ref> | |||
| Note that all networks and protocols are in alphabetical order except very similar applications which are listed in one entry with the most important one first, determining the place of this very similar applications in the list. | |||
| ==Political implications== | |||
| Adding external links to entries in this list is inappropriate. Links for a given client should be in that client's article. | |||
| ===Intellectual property law and illegal sharing=== | |||
| --> | |||
| Although peer-to-peer networks can be used for legitimate purposes, rights holders have targeted peer-to-peer over the involvement with sharing copyrighted material. Peer-to-peer networking involves data transfer from one user to another without using an intermediate server. Companies developing P2P applications have been involved in numerous legal cases, primarily in the United States, primarily over issues surrounding ] law.<ref name="Springer"/> Two major cases are ''] vs RIAA'' and '']''<ref name="news.cnet.com"/> In both of the cases the file sharing technology was ruled to be legal as long as the developers had no ability to prevent the sharing of the copyrighted material. | |||
| * ]: ], ] | |||
| * ]: ], ]], ], ], ], ], ], ], ], ], ], ], ], ], ], ], , ] | |||
| * ]: a peer-to-peer based communications system | |||
| * ] network: ], ], ], ] | |||
| * ] | |||
| * ]: ], ], ], ], ], ], ], ], ] | |||
| * ]: ], ], ] (and its variants stripped of ] including ]), ] (and its variants stripped of adware such as ]), ], ], ], ], ] | |||
| * ]: ] (on its own network), Freenet | |||
| * ]: GNUnet, (GNUnet-gtk) | |||
| * ]: ], ], ], ], ], ], ], ], ], ], ], ], ], ], ], ], ], ] | |||
| * ]: ], ], ], ], ], ], ], ], ], ] | |||
| * ] (using ] protocol): ], ], ] | |||
| * ]/MP2P: ], ] | |||
| * MFPnet: ] | |||
| * ]: ], ], ] | |||
| * ] type networks: ], ], ], ] | |||
| * ] type networks: ], ], ] | |||
| * ] | |||
| * ]: ] | |||
| <!-- | |||
| To establish criminal liability for the copyright infringement on peer-to-peer systems, the government must prove that the defendant infringed a copyright willingly for the purpose of personal financial gain or commercial advantage.<ref>Majoras, D. B. (2005). Peer-to-peer file-sharing technology consumer protection and competition issues. Federal Trade Commission, Retrieved from http://www.ftc.gov/reports/p2p05/050623p2prpt.pdf {{Webarchive|url=https://web.archive.org/web/20121101120121/http://ftc.gov/reports/p2p05/050623p2prpt.pdf |date=2012-11-01 }}</ref> ] exceptions allow limited use of copyrighted material to be downloaded without acquiring permission from the rights holders. These documents are usually news reporting or under the lines of research and scholarly work. Controversies have developed over the concern of illegitimate use of peer-to-peer networks regarding public safety and national security. When a file is downloaded through a peer-to-peer network, it is impossible to know who created the file or what users are connected to the network at a given time. Trustworthiness of sources is a potential security threat that can be seen with peer-to-peer systems.<ref>The Government of the Hong Kong Special Administrative Region, (2008). Peer-to-peer network. Retrieved from website: http://www.infosec.gov.hk/english/technical/files/peer.pdf {{Webarchive|url=https://web.archive.org/web/20191209032145/https://www.infosec.gov.hk/english/technical/files/peer.pdf |date=2019-12-09 }}</ref> | |||
| Note: "other networks" is not appropriate for external links. Adding them will result in them being promptly deleted. If you feel your external link is relevant, add it to the appropriate section (External Links). | |||
| A study ordered by the ] found that illegal downloading ''may'' lead to an increase in overall video game sales because newer games charge for extra features or levels. The paper concluded that piracy had a negative financial impact on movies, music, and literature. The study relied on self-reported data about game purchases and use of illegal download sites. Pains were taken to remove effects of false and misremembered responses.<ref>{{Cite news|url=http://www.newsweek.com/secret-piracy-study-european-union-669436|title=Illegal downloads may not actually harm sales, but the European Union doesn't want you to know that|last=Sanders|first=Linley|date=2017-09-22|work=Newsweek|access-date=2018-03-29|language=en}}</ref><ref>{{Cite news|url=http://bigthink.com/david-ryan-polgar/video-game-piracy-may-actually-result-in-more-sales|title=Does Video Game Piracy Actually Result in More Sales?|last=Polgar|first=David Ryan|date=October 15, 2017|work=Big Think|access-date=2018-03-29}}</ref><ref>{{Cite news|url=https://arstechnica.com/gaming/2017/09/eu-study-finds-piracy-doesnt-hurt-game-sales-may-actually-help/|title=EU study finds piracy doesn't hurt game sales, may actually help|last=Orland|first=Kyle|date=September 26, 2017|work=Ars Technica|access-date=2018-03-29|language=en-us}}</ref> | |||
| --> | |||
| * other networks: ], ], ], ], ], ], ], ], ], ], ], ], ], ], ], ], ], ], ], ], ], ], ], ], ], ], ], ], ], ], ], ], ], ], ], ] | |||
| ===Network neutrality=== | |||
| An earlier generation of peer-to-peer systems were called "metacomputing" or were classed as "middleware". These include: ], ] | |||
| Peer-to-peer applications present one of the core issues in the ] controversy. Internet service providers (]) have been known to throttle P2P file-sharing traffic due to its high-] usage.<ref name="newteevee.com">{{Cite web |date=2022-07-01 |title=What is bandwidth throttling? How to stop it {{!}} NordVPN |url=https://nordvpn.com/blog/what-is-bandwidth-throttling/ |access-date=2024-08-21 |website=nordvpn.com |language=en}}</ref> Compared to Web browsing, e-mail or many other uses of the internet, where data is only transferred in short intervals and relative small quantities, P2P file-sharing often consists of relatively heavy bandwidth usage due to ongoing file transfers and swarm/network coordination packets. In October 2007, ], one of the largest broadband Internet providers in the United States, started blocking P2P applications such as ]. Their rationale was that P2P is mostly used to share illegal content, and their infrastructure is not designed for continuous, high-bandwidth traffic. | |||
| Critics point out that P2P networking has legitimate legal uses, and that this is another way that large providers are trying to control use and content on the Internet, and direct people towards a ]-based application architecture. The client–server model provides financial barriers-to-entry to small publishers and individuals, and can be less efficient for sharing large files. As a reaction to this ], several P2P applications started implementing protocol obfuscation, such as the ]. Techniques for achieving "protocol obfuscation" involves removing otherwise easily identifiable properties of protocols, such as deterministic byte sequences and packet sizes, by making the data look as if it were random.<ref name="breaking">{{cite journal |url=http://www.iis.se/docs/hjelmvik_breaking.pdf |title=Breaking and Improving Protocol Obfuscation |last1=Hjelmvik |first1=Erik |last2=John |first2=Wolfgang |journal=Technical Report |date=2010-07-27 |issn=1652-926X }}</ref> The ISP's solution to the high bandwidth is ], where an ISP stores the part of files most accessed by P2P clients in order to save access to the Internet. | |||
| ===Multi-network applications=== | |||
| <!-- | |||
| ==Current research== | |||
| <Format>: <application> (networks/protocols) (operating systems) (open source?) | |||
| Researchers have used computer simulations to aid in understanding and evaluating the complex behaviors of individuals within the network. "Networking research often relies on simulation in order to test and evaluate new ideas. An important requirement of this process is that results must be reproducible so that other researchers can replicate, validate, and extend existing work."<ref name="Basu, A. 2013">Basu, A., Fleming, S., Stanier, J., Naicken, S., Wakeman, I., & Gurbani, V. K. (2013). The state of peer-to-peer network simulators. ACM Computing Surveys, 45(4), 46.</ref> If the research cannot be reproduced, then the opportunity for further research is hindered. "Even though new simulators continue to be released, the research community tends towards only a handful of open-source simulators. The demand for features in simulators, as shown by our criteria and survey, is high. Therefore, the community should work together to get these features in open-source software. This would reduce the need for custom simulators, and hence increase repeatability and reputability of experiments."<ref name="Basu, A. 2013"/> | |||
| Popular simulators that were widely used in the past are NS2, OMNeT++, SimPy, NetLogo, PlanetLab, ProtoPeer, QTM, PeerSim, ONE, P2PStrmSim, PlanetSim, GNUSim, and Bharambe.<ref>{{Cite journal |last1=Ihle |first1=Cornelius |last2=Trautwein |first2=Dennis |last3=Schubotz |first3=Moritz |last4=Meuschke |first4=Norman |last5=Gipp |first5=Bela |date=2023-01-24 |title=Incentive Mechanisms in Peer-to-Peer Networks — A Systematic Literature Review |journal=ACM Computing Surveys |volume=55 |issue=14s |pages=1–69 |doi=10.1145/3578581 |issn=0360-0300 |s2cid=256106264 |doi-access=free}}</ref> | |||
| Note they *are* in alphabetical order... | |||
| Besides all the above stated facts, there has also been work done on ns-2 open source network simulators. One research issue related to free rider detection and punishment has been explored using ns-2 simulator here.<ref>A Bhakuni, P Sharma, R Kaushal , International Advanced Computing Conference, 2014. {{doi|10.1109/IAdCC.2014.6779311}}</ref> | |||
| --> | |||
| * ] (], ]) (], ], ], ], ], ] and ]) (open source) | |||
| * ] (], ]) (Windows) (open source) | |||
| * ] (], ], ], ]) (crossplatform) (open source) | |||
| * ] (own ] protocol, and with plugins - FastTrack, eDonkey and Gnutella) (open source) | |||
| * ] (Gnutella, ]) (Windows) (open source) | |||
| * ] (Fasttrack, ], Gnutella, Gnutella2) (Microsoft Windows) (closed source) | |||
| * ] (Ares, FastTrack (plugin required), Gnutella, OpenFT) (open source) | |||
| * ] (Gnutella, Gnutella2) (Windows) (closed source) | |||
| * ] (BitTorrent, ], FastTrack, Gnutella, Gnutella2, Kademlia) (Windows, Linux, Mac OS X) (open source) | |||
| * ] (NEO Network, Gnutella, Gnutella2, BitTorrent) (Windows) (closed source) | |||
| * ] (], Key Network) (Linux, Windows) (open source) | |||
| * ] (BitTorrent, eDonkey, Gnutella, Gnutella2) (Windows) (open source) | |||
| * ] (Windows) (mxpie.com) (Currently shut down) | |||
| * ] (Gnutella, ZEPP) (Windows) (closed source) | |||
| ==See also== | ==See also== | ||
| {{Portal bar|Internet}} | |||
| *] | |||
| {{cmn| | |||
| *] | |||
| * ] | |||
| *] | |||
| * ] | |||
| *] | |||
| * ] (CHAT) | |||
| *] | |||
| * ] | |||
| *] | |||
| *] | * ] | ||
| * ] | |||
| *] | |||
| *] | * ] | ||
| *] |
* ] | ||
| * ] | |||
| *] | |||
| *] | * ] | ||
| *] | * ] | ||
| *] | * ] | ||
| * ] | |||
| *] | |||
| }} | |||
| *] | |||
| * p2p news, apps, Linux P2P, beginners' guide, p2p statistics and much more :) | |||
| ==External links== | |||
| {{Commonscat|P2P}} | |||
| * A review of the current and potential uses of peer-to-peer networks in scientific research | |||
| * Annual | |||
| * on peer-to-peer computing | |||
| * | |||
| * | |||
| * List of file sharing software for GNU/Linux | |||
| * p2p news, apps, Linux P2P, beginners' guide, p2p statistics and much more :) | |||
| * | |||
| * peer-to-peer development resources | |||
| * peer-to-peer networking & the entertainment industry. A free-to-distribute white paper by Scott Jensen | |||
| * peer-to-peer web servers on mobile devices | |||
| * Wiki-based site with discussion of the philosophy behind peer-to-peer networks | |||
| * - article by ]. | |||
| ==References== | ==References== | ||
| {{Reflist|30em}} | |||
| ==External links== | |||
| * Ross J. Anderson. . In ''Pragocrypt 1996'', 1996. | |||
| {{Commons category|Peer-to-peer}} | |||
| {{refbegin|2}} | |||
| * Ghosh Debjani, Rajan Payas, Pandey Mayank {{Webarchive|url=https://web.archive.org/web/20170219011236/http://link.springer.com/chapter/10.1007/978-3-319-07350-7_19 |date=2017-02-19 }} Springer Proceedings, June 2014 | |||
| * of P2P terminology | |||
| * , Special Issue, Elsevier Journal of Computer Communication, (Ed) Javed I. Khan and Adam Wierzbicki, Volume 31, Issue 2, February 2008 | |||
| * {{cite journal | last1 = Anderson | first1 = Ross J. | title = The eternity service | url = http://www.cl.cam.ac.uk/users/rja14/eternity/eternity.html| journal = Pragocrypt | volume = 1996 }} | |||
| * Marling Engle & J. I. Khan. {{Webarchive|url=https://web.archive.org/web/20070615192323/http://www.medianet.kent.edu/techreports/TR2006-11-01-p2pvuln-EK.pdf |date=2007-06-15 }}, May 2006 | |||
| * Stephanos Androutsellis-Theotokis and Diomidis Spinellis. {{Webarchive|url=https://web.archive.org/web/20201109023714/http://www.spinellis.gr/pubs/jrnl/2004-ACMCS-p2p/html/AS04.html |date=2020-11-09 }}. ACM Computing Surveys, 36(4):335–371, December 2004. | |||
| * Biddle, Peter, Paul England, Marcus Peinado, and Bryan Willman, {{Webarchive|url=https://web.archive.org/web/20110727174231/http://crypto.stanford.edu/DRM2002/darknet5.doc |date=2011-07-27 }}. In ''2002 ACM Workshop on Digital Rights Management'', November 2002. | |||
| * John F. Buford, Heather Yu, Eng Keong Lua . {{ISBN|0123742145}}, Morgan Kaufmann, December 2008 | |||
| * Djamal-Eddine Meddour, Mubashar Mushtaq, and Toufik Ahmed, " {{Webarchive|url=https://web.archive.org/web/20110822171602/http://multicomm.polito.it/proc_multicomm06_8.pdf |date=2011-08-22 }}", in the proceedings of the 1st Multimedia Communications Workshop MULTICOMM 2006 held in conjunction with IEEE ICC 2006 pp 43–48, June 2006, Istanbul, Turkey. | |||
| * Detlef Schoder and Kai Fischbach, " {{Webarchive|url=https://web.archive.org/web/20110915100115/http://www.econbiz.de/archiv1/2008/42151_concepts_peer-to-peer_networking.pdf |date=2011-09-15 }}". In: Subramanian, R.; Goodman, B. (eds.): ''P2P Computing: The Evolution of a Disruptive Technology'', Idea Group Inc, Hershey. 2005 | |||
| * Ramesh Subramanian and Brian Goodman (eds), '''', {{ISBN|1-59140-429-0}}, Idea Group Inc., Hershey, PA, United States, 2005. | |||
| * ]. {{Webarchive|url=https://web.archive.org/web/20121013004555/http://dspace.mit.edu/handle/1721.1/8438 |date=2012-10-13 }}. ], 2002. | |||
| * Silverthorne, Sean. '' {{Webarchive|url=https://web.archive.org/web/20060630024153/http://hbswk.hbs.edu/item.jhtml?id=4206&t=innovation |date=2006-06-30 }}''. ], 2004. | |||
| * {{Webarchive|url=https://web.archive.org/web/20141005000618/http://broadband.mpi-sws.org/transparency/bttest.php |date=2014-10-05 }} test P2P ] (]) | |||
| {{refend}} | |||
| {{Bitcoin}} | |||
| {{Tor hidden services}} | |||
| {{Cryptographic software}} | |||
| {{File sharing}} | |||
| {{Authority control}} | |||
| {{DEFAULTSORT:Peer-To-Peer}} | |||
| * Marling Engle. , May 2006 | |||
| ] | |||
| * Stephanos Androutsellis-Theotokis and Diomidis Spinellis. . ACM Computing Surveys, 36(4):335–371, December 2004. . | |||
| ] | |||
| * Biddle, Peter, Paul England, Marcus Peinado, and Bryan Willman, . In ''2002 ACM Workshop on Digital Rights Management'', ] ]. | |||
| * Antony Rowstron and Peter Druschel, Pastry: Scalable, Decentralized Object Location, and Routing for Large-Scale Peer-to-Peer Systems. In proceedings ''Middleware 2001 : IFIP/ACM International Conference on Distributed Systems Platforms''. Heidelberg, Germany, ]-16, 2001. Lecture Notes in Computer Science, Volume 2218, Jan 2001, Page 329. | |||
| * Andy Oram et al., Peer-to-Peer:Harnessing the Power of Disruptive Technologies, Oreilly 2001 | |||
| * Detlef Schoder and Kai Fischbach, . In: Subramanian, R.; Goodman, B. (eds.): P2P Computing: The Evolution of a Disruptive Technology, Idea Group Inc, Hershey. | |||
| * I. Stoica, R. Morris, D. Karger, M. F. Kaashoek, and H. Balakrishnan. Chord: A scalable peer-to-peer lookup service for internet applications. In ''Proceedings of SIGCOMM 2001'', August 2001. | |||
| * Ralf Steinmetz, Klaus Wehrle (Eds). . ISBN 3-540-29192-X, Lecture Notes in Computer Science, Volume 3485, Sep 2005 | |||
| *] ''. ], 2002. | |||
| * Silverthorne, Sean. ''''. ], 2004. | |||
| * Kronschnabl, A & Rawlings T. Marion Boyars, 2004. | |||
| ] | ] | ||
| ] | ] | ||
| ] | ] | ||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
Latest revision as of 23:36, 1 December 2024
Type of decentralized and distributed network architecture For other uses, see Peer-to-peer (disambiguation), Point-to-point (disambiguation), and P2P (disambiguation).| This article needs additional citations for verification. Please help improve this article by adding citations to reliable sources. Unsourced material may be challenged and removed. Find sources: "Peer-to-peer" – news · newspapers · books · scholar · JSTOR (August 2024) (Learn how and when to remove this message) |

Peer-to-peer (P2P) computing or networking is a distributed application architecture that partitions tasks or workloads between peers. Peers are equally privileged, equipotent participants in the network, forming a peer-to-peer network of nodes. In addition, a personal area network (PAN) is also in nature a type of decentralized peer-to-peer network typically between two devices.

Peers make a portion of their resources, such as processing power, disk storage, or network bandwidth, directly available to other network participants, without the need for central coordination by servers or stable hosts. Peers are both suppliers and consumers of resources, in contrast to the traditional client–server model in which the consumption and supply of resources are divided.
While P2P systems had previously been used in many application domains, the architecture was popularized by the Internet file sharing system Napster, originally released in 1999. P2P is used in many protocols such as BitTorrent file sharing over the Internet and in personal networks like Miracast displaying and Bluetooth radio. The concept has inspired new structures and philosophies in many areas of human interaction. In such social contexts, peer-to-peer as a meme refers to the egalitarian social networking that has emerged throughout society, enabled by Internet technologies in general.
Development

While P2P systems had previously been used in many application domains, the concept was popularized by file sharing systems such as the music-sharing application Napster. The peer-to-peer movement allowed millions of Internet users to connect "directly, forming groups and collaborating to become user-created search engines, virtual supercomputers, and filesystems". The basic concept of peer-to-peer computing was envisioned in earlier software systems and networking discussions, reaching back to principles stated in the first Request for Comments, RFC 1.
Tim Berners-Lee's vision for the World Wide Web was close to a P2P network in that it assumed each user of the web would be an active editor and contributor, creating and linking content to form an interlinked "web" of links. The early Internet was more open than the present day, where two machines connected to the Internet could send packets to each other without firewalls and other security measures. This contrasts with the broadcasting-like structure of the web as it has developed over the years. As a precursor to the Internet, ARPANET was a successful peer-to-peer network where "every participating node could request and serve content". However, ARPANET was not self-organized, and it could not "provide any means for context or content-based routing beyond 'simple' address-based routing."
Therefore, Usenet, a distributed messaging system that is often described as an early peer-to-peer architecture, was established. It was developed in 1979 as a system that enforces a decentralized model of control. The basic model is a client–server model from the user or client perspective that offers a self-organizing approach to newsgroup servers. However, news servers communicate with one another as peers to propagate Usenet news articles over the entire group of network servers. The same consideration applies to SMTP email in the sense that the core email-relaying network of mail transfer agents has a peer-to-peer character, while the periphery of Email clients and their direct connections is strictly a client-server relationship.
In May 1999, with millions more people on the Internet, Shawn Fanning introduced the music and file-sharing application called Napster. Napster was the beginning of peer-to-peer networks, as we know them today, where "participating users establish a virtual network, entirely independent from the physical network, without having to obey any administrative authorities or restrictions".
Architecture
A peer-to-peer network is designed around the notion of equal peer nodes simultaneously functioning as both "clients" and "servers" to the other nodes on the network. This model of network arrangement differs from the client–server model where communication is usually to and from a central server. A typical example of a file transfer that uses the client-server model is the File Transfer Protocol (FTP) service in which the client and server programs are distinct: the clients initiate the transfer, and the servers satisfy these requests.
Routing and resource discovery
Peer-to-peer networks generally implement some form of virtual overlay network on top of the physical network topology, where the nodes in the overlay form a subset of the nodes in the physical network. Data is still exchanged directly over the underlying TCP/IP network, but at the application layer peers can communicate with each other directly, via the logical overlay links (each of which corresponds to a path through the underlying physical network). Overlays are used for indexing and peer discovery, and make the P2P system independent from the physical network topology. Based on how the nodes are linked to each other within the overlay network, and how resources are indexed and located, we can classify networks as unstructured or structured (or as a hybrid between the two).
Unstructured networks

Unstructured peer-to-peer networks do not impose a particular structure on the overlay network by design, but rather are formed by nodes that randomly form connections to each other. (Gnutella, Gossip, and Kazaa are examples of unstructured P2P protocols).
Because there is no structure globally imposed upon them, unstructured networks are easy to build and allow for localized optimizations to different regions of the overlay. Also, because the role of all peers in the network is the same, unstructured networks are highly robust in the face of high rates of "churn"—that is, when large numbers of peers are frequently joining and leaving the network.
However, the primary limitations of unstructured networks also arise from this lack of structure. In particular, when a peer wants to find a desired piece of data in the network, the search query must be flooded through the network to find as many peers as possible that share the data. Flooding causes a very high amount of signaling traffic in the network, uses more CPU/memory (by requiring every peer to process all search queries), and does not ensure that search queries will always be resolved. Furthermore, since there is no correlation between a peer and the content managed by it, there is no guarantee that flooding will find a peer that has the desired data. Popular content is likely to be available at several peers and any peer searching for it is likely to find the same thing. But if a peer is looking for rare data shared by only a few other peers, then it is highly unlikely that the search will be successful.
Structured networks
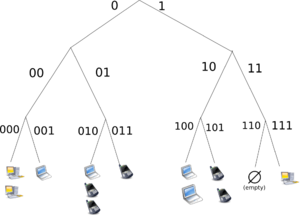
In structured peer-to-peer networks the overlay is organized into a specific topology, and the protocol ensures that any node can efficiently search the network for a file/resource, even if the resource is extremely rare.
The most common type of structured P2P networks implement a distributed hash table (DHT), in which a variant of consistent hashing is used to assign ownership of each file to a particular peer. This enables peers to search for resources on the network using a hash table: that is, (key, value) pairs are stored in the DHT, and any participating node can efficiently retrieve the value associated with a given key.

However, in order to route traffic efficiently through the network, nodes in a structured overlay must maintain lists of neighbors that satisfy specific criteria. This makes them less robust in networks with a high rate of churn (i.e. with large numbers of nodes frequently joining and leaving the network). More recent evaluation of P2P resource discovery solutions under real workloads have pointed out several issues in DHT-based solutions such as high cost of advertising/discovering resources and static and dynamic load imbalance.
Notable distributed networks that use DHTs include Tixati, an alternative to BitTorrent's distributed tracker, the Kad network, the Storm botnet, and the YaCy. Some prominent research projects include the Chord project, Kademlia, PAST storage utility, P-Grid, a self-organized and emerging overlay network, and CoopNet content distribution system. DHT-based networks have also been widely utilized for accomplishing efficient resource discovery for grid computing systems, as it aids in resource management and scheduling of applications.
Hybrid models
Hybrid models are a combination of peer-to-peer and client–server models. A common hybrid model is to have a central server that helps peers find each other. Spotify was an example of a hybrid model . There are a variety of hybrid models, all of which make trade-offs between the centralized functionality provided by a structured server/client network and the node equality afforded by the pure peer-to-peer unstructured networks. Currently, hybrid models have better performance than either pure unstructured networks or pure structured networks because certain functions, such as searching, do require a centralized functionality but benefit from the decentralized aggregation of nodes provided by unstructured networks.
CoopNet content distribution system
CoopNet (Cooperative Networking) was a proposed system for off-loading serving to peers who have recently downloaded content, proposed by computer scientists Venkata N. Padmanabhan and Kunwadee Sripanidkulchai, working at Microsoft Research and Carnegie Mellon University. When a server experiences an increase in load it redirects incoming peers to other peers who have agreed to mirror the content, thus off-loading balance from the server. All of the information is retained at the server. This system makes use of the fact that the bottleneck is most likely in the outgoing bandwidth than the CPU, hence its server-centric design. It assigns peers to other peers who are 'close in IP' to its neighbors in an attempt to use locality. If multiple peers are found with the same file it designates that the node choose the fastest of its neighbors. Streaming media is transmitted by having clients cache the previous stream, and then transmit it piece-wise to new nodes.
Security and trust
Peer-to-peer systems pose unique challenges from a computer security perspective. Like any other form of software, P2P applications can contain vulnerabilities. What makes this particularly dangerous for P2P software, however, is that peer-to-peer applications act as servers as well as clients, meaning that they can be more vulnerable to remote exploits.
Routing attacks
Since each node plays a role in routing traffic through the network, malicious users can perform a variety of "routing attacks", or denial of service attacks. Examples of common routing attacks include "incorrect lookup routing" whereby malicious nodes deliberately forward requests incorrectly or return false results, "incorrect routing updates" where malicious nodes corrupt the routing tables of neighboring nodes by sending them false information, and "incorrect routing network partition" where when new nodes are joining they bootstrap via a malicious node, which places the new node in a partition of the network that is populated by other malicious nodes.
Corrupted data and malware
See also: Data validation and MalwareThe prevalence of malware varies between different peer-to-peer protocols. Studies analyzing the spread of malware on P2P networks found, for example, that 63% of the answered download requests on the gnutella network contained some form of malware, whereas only 3% of the content on OpenFT contained malware. In both cases, the top three most common types of malware accounted for the large majority of cases (99% in gnutella, and 65% in OpenFT). Another study analyzing traffic on the Kazaa network found that 15% of the 500,000 file sample taken were infected by one or more of the 365 different computer viruses that were tested for.
Corrupted data can also be distributed on P2P networks by modifying files that are already being shared on the network. For example, on the FastTrack network, the RIAA managed to introduce faked chunks into downloads and downloaded files (mostly MP3 files). Files infected with the RIAA virus were unusable afterwards and contained malicious code. The RIAA is also known to have uploaded fake music and movies to P2P networks in order to deter illegal file sharing. Consequently, the P2P networks of today have seen an enormous increase of their security and file verification mechanisms. Modern hashing, chunk verification and different encryption methods have made most networks resistant to almost any type of attack, even when major parts of the respective network have been replaced by faked or nonfunctional hosts.
Resilient and scalable computer networks
See also: Wireless mesh network and Distributed computingThe decentralized nature of P2P networks increases robustness because it removes the single point of failure that can be inherent in a client–server based system. As nodes arrive and demand on the system increases, the total capacity of the system also increases, and the likelihood of failure decreases. If one peer on the network fails to function properly, the whole network is not compromised or damaged. In contrast, in a typical client–server architecture, clients share only their demands with the system, but not their resources. In this case, as more clients join the system, fewer resources are available to serve each client, and if the central server fails, the entire network is taken down.
Distributed storage and search

There are both advantages and disadvantages in P2P networks related to the topic of data backup, recovery, and availability. In a centralized network, the system administrators are the only forces controlling the availability of files being shared. If the administrators decide to no longer distribute a file, they simply have to remove it from their servers, and it will no longer be available to users. Along with leaving the users powerless in deciding what is distributed throughout the community, this makes the entire system vulnerable to threats and requests from the government and other large forces.
For example, YouTube has been pressured by the RIAA, MPAA, and entertainment industry to filter out copyrighted content. Although server-client networks are able to monitor and manage content availability, they can have more stability in the availability of the content they choose to host. A client should not have trouble accessing obscure content that is being shared on a stable centralized network. P2P networks, however, are more unreliable in sharing unpopular files because sharing files in a P2P network requires that at least one node in the network has the requested data, and that node must be able to connect to the node requesting the data. This requirement is occasionally hard to meet because users may delete or stop sharing data at any point.
In a P2P network, the community of users is entirely responsible for deciding which content is available. Unpopular files eventually disappear and become unavailable as fewer people share them. Popular files, however, are highly and easily distributed. Popular files on a P2P network are more stable and available than files on central networks. In a centralized network, a simple loss of connection between the server and clients can cause a failure, but in P2P networks, the connections between every node must be lost to cause a data-sharing failure. In a centralized system, the administrators are responsible for all data recovery and backups, while in P2P systems, each node requires its backup system. Because of the lack of central authority in P2P networks, forces such as the recording industry, RIAA, MPAA, and the government are unable to delete or stop the sharing of content on P2P systems.
Applications
Content delivery
In P2P networks, clients both provide and use resources. This means that unlike client–server systems, the content-serving capacity of peer-to-peer networks can actually increase as more users begin to access the content (especially with protocols such as Bittorrent that require users to share, refer a performance measurement study). This property is one of the major advantages of using P2P networks because it makes the setup and running costs very small for the original content distributor.
File-sharing networks
Peer-to-peer file sharing networks such as Gnutella, G2, and the eDonkey network have been useful in popularizing peer-to-peer technologies. These advancements have paved the way for Peer-to-peer content delivery networks and services, including distributed caching systems like Correli Caches to enhance performance. Furthermore, peer-to-peer networks have made possible the software publication and distribution, enabling efficient sharing of Linux distribution and various games though file sharing networks.
Copyright infringements
Peer-to-peer networking involves data transfer from one user to another without using an intermediate server. Companies developing P2P applications have been involved in numerous legal cases, primarily in the United States, over conflicts with copyright law. Two major cases are Grokster vs RIAA and MGM Studios, Inc. v. Grokster, Ltd.. In the last case, the Court unanimously held that defendant peer-to-peer file sharing companies Grokster and Streamcast could be sued for inducing copyright infringement.
Multimedia
The P2PTV and PDTP protocols are used in various peer-to-peer applications. Some proprietary multimedia applications leverage a peer-to-peer network in conjunction with streaming servers to stream audio and video to their clients. Peercasting is employed for multicasting streams. Additionally, a project called LionShare, undertaken by Pennsylvania State University, MIT, and Simon Fraser University, aims to facilitate file sharing among educational institutions globally. Another notable program, Osiris, enables users to create anonymous and autonomous web portals that are distributed via a peer-to-peer network.
Other P2P applications

Dat is a distributed version-controlled publishing platform. I2P, is an overlay network used to browse the Internet anonymously. Unlike the related I2P, the Tor network is not itself peer-to-peer; however, it can enable peer-to-peer applications to be built on top of it via onion services. The InterPlanetary File System (IPFS) is a protocol and network designed to create a content-addressable, peer-to-peer method of storing and sharing hypermedia distribution protocol, with nodes in the IPFS network forming a distributed file system. Jami is a peer-to-peer chat and SIP app. JXTA is a peer-to-peer protocol designed for the Java platform. Netsukuku is a Wireless community network designed to be independent from the Internet. Open Garden is a connection-sharing application that shares Internet access with other devices using Wi-Fi or Bluetooth.
Resilio Sync is a directory-syncing app. Research includes projects such as the Chord project, the PAST storage utility, the P-Grid, and the CoopNet content distribution system. Secure Scuttlebutt is a peer-to-peer gossip protocol capable of supporting many different types of applications, primarily social networking. Syncthing is also a directory-syncing app. Tradepal l and M-commerce applications are designed to power real-time marketplaces. The U.S. Department of Defense is conducting research on P2P networks as part of its modern network warfare strategy. In May 2003, Anthony Tether, then director of DARPA, testified that the United States military uses P2P networks. WebTorrent is a P2P streaming torrent client in JavaScript for use in web browsers, as well as in the WebTorrent Desktop standalone version that bridges WebTorrent and BitTorrent serverless networks. Microsoft, in Windows 10, uses a proprietary peer-to-peer technology called "Delivery Optimization" to deploy operating system updates using end-users' PCs either on the local network or other PCs. According to Microsoft's Channel 9, this led to a 30%-50% reduction in Internet bandwidth usage. Artisoft's LANtastic was built as a peer-to-peer operating system where machines can function as both servers and workstations simultaneously. Hotline Communications Hotline Client was built with decentralized servers and tracker software dedicated to any type of files and continues to operate today. Cryptocurrencies are peer-to-peer-based digital currencies that use blockchains
Social implications
Incentivizing resource sharing and cooperation

Cooperation among a community of participants is key to the continued success of P2P systems aimed at casual human users; these reach their full potential only when large numbers of nodes contribute resources. But in current practice, P2P networks often contain large numbers of users who utilize resources shared by other nodes, but who do not share anything themselves (often referred to as the "freeloader problem").
Freeloading can have a profound impact on the network and in some cases can cause the community to collapse. In these types of networks "users have natural disincentives to cooperate because cooperation consumes their own resources and may degrade their own performance". Studying the social attributes of P2P networks is challenging due to large populations of turnover, asymmetry of interest and zero-cost identity. A variety of incentive mechanisms have been implemented to encourage or even force nodes to contribute resources.
Some researchers have explored the benefits of enabling virtual communities to self-organize and introduce incentives for resource sharing and cooperation, arguing that the social aspect missing from today's P2P systems should be seen both as a goal and a means for self-organized virtual communities to be built and fostered. Ongoing research efforts for designing effective incentive mechanisms in P2P systems, based on principles from game theory, are beginning to take on a more psychological and information-processing direction.
Privacy and anonymity
Some peer-to-peer networks (e.g. Freenet) place a heavy emphasis on privacy and anonymity—that is, ensuring that the contents of communications are hidden from eavesdroppers, and that the identities/locations of the participants are concealed. Public key cryptography can be used to provide encryption, data validation, authorization, and authentication for data/messages. Onion routing and other mix network protocols (e.g. Tarzan) can be used to provide anonymity.
Perpetrators of live streaming sexual abuse and other cybercrimes have used peer-to-peer platforms to carry out activities with anonymity.
Political implications
Intellectual property law and illegal sharing
Although peer-to-peer networks can be used for legitimate purposes, rights holders have targeted peer-to-peer over the involvement with sharing copyrighted material. Peer-to-peer networking involves data transfer from one user to another without using an intermediate server. Companies developing P2P applications have been involved in numerous legal cases, primarily in the United States, primarily over issues surrounding copyright law. Two major cases are Grokster vs RIAA and MGM Studios, Inc. v. Grokster, Ltd. In both of the cases the file sharing technology was ruled to be legal as long as the developers had no ability to prevent the sharing of the copyrighted material.
To establish criminal liability for the copyright infringement on peer-to-peer systems, the government must prove that the defendant infringed a copyright willingly for the purpose of personal financial gain or commercial advantage. Fair use exceptions allow limited use of copyrighted material to be downloaded without acquiring permission from the rights holders. These documents are usually news reporting or under the lines of research and scholarly work. Controversies have developed over the concern of illegitimate use of peer-to-peer networks regarding public safety and national security. When a file is downloaded through a peer-to-peer network, it is impossible to know who created the file or what users are connected to the network at a given time. Trustworthiness of sources is a potential security threat that can be seen with peer-to-peer systems.
A study ordered by the European Union found that illegal downloading may lead to an increase in overall video game sales because newer games charge for extra features or levels. The paper concluded that piracy had a negative financial impact on movies, music, and literature. The study relied on self-reported data about game purchases and use of illegal download sites. Pains were taken to remove effects of false and misremembered responses.
Network neutrality
Peer-to-peer applications present one of the core issues in the network neutrality controversy. Internet service providers (ISPs) have been known to throttle P2P file-sharing traffic due to its high-bandwidth usage. Compared to Web browsing, e-mail or many other uses of the internet, where data is only transferred in short intervals and relative small quantities, P2P file-sharing often consists of relatively heavy bandwidth usage due to ongoing file transfers and swarm/network coordination packets. In October 2007, Comcast, one of the largest broadband Internet providers in the United States, started blocking P2P applications such as BitTorrent. Their rationale was that P2P is mostly used to share illegal content, and their infrastructure is not designed for continuous, high-bandwidth traffic.
Critics point out that P2P networking has legitimate legal uses, and that this is another way that large providers are trying to control use and content on the Internet, and direct people towards a client–server-based application architecture. The client–server model provides financial barriers-to-entry to small publishers and individuals, and can be less efficient for sharing large files. As a reaction to this bandwidth throttling, several P2P applications started implementing protocol obfuscation, such as the BitTorrent protocol encryption. Techniques for achieving "protocol obfuscation" involves removing otherwise easily identifiable properties of protocols, such as deterministic byte sequences and packet sizes, by making the data look as if it were random. The ISP's solution to the high bandwidth is P2P caching, where an ISP stores the part of files most accessed by P2P clients in order to save access to the Internet.
Current research
Researchers have used computer simulations to aid in understanding and evaluating the complex behaviors of individuals within the network. "Networking research often relies on simulation in order to test and evaluate new ideas. An important requirement of this process is that results must be reproducible so that other researchers can replicate, validate, and extend existing work." If the research cannot be reproduced, then the opportunity for further research is hindered. "Even though new simulators continue to be released, the research community tends towards only a handful of open-source simulators. The demand for features in simulators, as shown by our criteria and survey, is high. Therefore, the community should work together to get these features in open-source software. This would reduce the need for custom simulators, and hence increase repeatability and reputability of experiments."
Popular simulators that were widely used in the past are NS2, OMNeT++, SimPy, NetLogo, PlanetLab, ProtoPeer, QTM, PeerSim, ONE, P2PStrmSim, PlanetSim, GNUSim, and Bharambe.
Besides all the above stated facts, there has also been work done on ns-2 open source network simulators. One research issue related to free rider detection and punishment has been explored using ns-2 simulator here.
See also
Portal:- Client-to-client protocol
- Client–queue–client
- Cultural-historical activity theory (CHAT)
- Distributed Data Management Architecture
- End-to-end principle
- Friend-to-friend
- List of P2P protocols
- Peer-to-peer energy trading
- Semantic P2P networks
- Sharing economy
- SponsorChange
- USB dead drop
- Wireless ad hoc network
References
- Cope, James (2002-04-08). "What's a Peer-to-Peer (P2P) Network?". Computerworld. Retrieved 2021-12-21.
- Desire Athow (12 July 2016). "Why personal area networks are the best thing to happen to hotel Wi-Fi".
- Rüdiger Schollmeier, A Definition of Peer-to-Peer Networking for the Classification of Peer-to-Peer Architectures and Applications, Proceedings of the First International Conference on Peer-to-Peer Computing, IEEE (2002).
- ^ Bandara, H. M. N. D; A. P. Jayasumana (2012). "Collaborative Applications over Peer-to-Peer Systems – Challenges and Solutions". Peer-to-Peer Networking and Applications. 6 (3): 257–276. arXiv:1207.0790. Bibcode:2012arXiv1207.0790D. doi:10.1007/s12083-012-0157-3. S2CID 14008541.
- ^ Barkai, David (2001). Peer-to-peer computing : technologies for sharing and collaborating on the net. Hillsboro, OR: Intel Press. ISBN 978-0970284679. OCLC 49354877.
- Saroiu, Stefan; Gummadi, Krishna P.; Gribble, Steven D. (2003-08-01). "Measuring and analyzing the characteristics of Napster and Gnutella hosts". Multimedia Systems. 9 (2): 170–184. doi:10.1007/s00530-003-0088-1. ISSN 1432-1882. S2CID 15963045.
- "What Is BitTorrent and Is It Safe?". www.kaspersky.com. 2023-04-19. Retrieved 2023-10-24.
- "האוניברסיטה הפתוחה". www.openu.ac.il. Retrieved 2024-07-15.
- ^ Oram, Andrew, ed. (2001). Peer-to-peer: harnessing the benefits of disruptive technology. Sebastopol, California: O'Reilly. ISBN 9780596001100. OCLC 123103147.
- RFC 1, Host Software, S. Crocker, IETF Working Group (April 7, 1969)
- Oppliger, R. (1995). "Internet security enters the Middle Ages". Computer. 28 (10): 100–101. doi:10.1109/2.467613. Retrieved 2023-12-14.
- Berners-Lee, Tim (August 1996). "The World Wide Web: Past, Present and Future". Retrieved 5 November 2011.
- Sandhu, R.; Zhang, X. (2005). "Peer-to-peer access control architecture using trusted computing technology". Proceedings of the tenth ACM symposium on Access control models and technologies. pp. 147–158. doi:10.1145/1063979.1064005. ISBN 1595930450. S2CID 1478064.
- ^ Steinmetz, Ralf; Wehrle, Klaus (2005). "2. What Is This "Peer-to-Peer" About?". Peer-to-Peer Systems and Applications. Lecture Notes in Computer Science. Springer, Berlin, Heidelberg. pp. 9–16. doi:10.1007/11530657_2. ISBN 9783540291923.
- Horton, Mark, and Rick Adams. "Standard for interchange of USENET messages." (1987): 1. https://www.hjp.at/doc/rfc/rfc1036.html Archived 2021-06-12 at the Wayback Machine
- Sharma, M. K. "CLIENT SERVER TECHNOLOGY" (PDF). SWAMI VIVEKANAND SUBHARTI UNIVERSITY.
- "Practical Applications of Peer-to-Peer Networks in File Sharing and Content Distribution | SimpleSwap". SimpleSwap | Cryptocurrency exchange blog. Retrieved 2024-08-21.
- "Overlay Network - an overview | ScienceDirect Topics". www.sciencedirect.com. Retrieved 2024-08-21.
- Ahson, Syed A.; Ilyas, Mohammad, eds. (2008). SIP Handbook: Services, Technologies, and Security of Session Initiation Protocol. Taylor & Francis. p. 204. ISBN 9781420066043.
- Zhu, Ce; et al., eds. (2010). Streaming Media Architectures: Techniques and Applications: Recent Advances. IGI Global. p. 265. ISBN 9781616928339.
- Kamel, Mina; et al. (2007). "Optimal Topology Design for Overlay Networks". In Akyildiz, Ian F. (ed.). Networking 2007: Ad Hoc and Sensor Networks, Wireless Networks, Next Generation Internet: 6th International IFIP-TC6 Networking Conference, Atlanta, GA, USA, May 14-18, 2007 Proceedings. Springer. p. 714. ISBN 9783540726050.
- Filali, Imen; et al. (2011). "A Survey of Structured P2P Systems for RDF Data Storage and Retrieval". In Hameurlain, Abdelkader; et al. (eds.). Transactions on Large-Scale Data- and Knowledge-Centered Systems III: Special Issue on Data and Knowledge Management in Grid and PSP Systems. Springer. p. 21. ISBN 9783642230738.
- ^ Zulhasnine, Mohammed; et al. (2013). "P2P Streaming Over Cellular Networks: Issues, Challenges, and Opportunities". In Pathan; et al. (eds.). Building Next-Generation Converged Networks: Theory and Practice. CRC Press. p. 99. ISBN 9781466507616.
- Chervenak, Ann; Bharathi, Shishir (2008). "Peer-to-peer Approaches to Grid Resource Discovery". In Danelutto, Marco; et al. (eds.). Making Grids Work: Proceedings of the CoreGRID Workshop on Programming Models Grid and P2P System Architecture Grid Systems, Tools and Environments 12-13 June 2007, Heraklion, Crete, Greece. Springer. p. 67. ISBN 9780387784489.
- Jin, Xing; Chan, S.-H. Gary (2010). "Unstructured Peer-to-Peer Network Architectures". In Shen; et al. (eds.). Handbook of Peer-to-Peer Networking. Springer. p. 119. ISBN 978-0-387-09750-3.
- ^ Lv, Qin; et al. (2002). "Can Heterogeneity Make Gnutella Stable?". In Druschel, Peter; et al. (eds.). Peer-to-Peer Systems: First International Workshop, IPTPS 2002, Cambridge, MA, USA, March 7-8, 2002, Revised Papers. Springer. p. 94. ISBN 9783540441793.
- Shen, Xuemin; Yu, Heather; Buford, John; Akon, Mursalin (2009). Handbook of Peer-to-Peer Networking (1st ed.). New York: Springer. p. 118. ISBN 978-0-387-09750-3.
- Dhara, Krishna; Kolberg, Mario (January 2010). "Overview of Structured Peer-to-Peer Overlay Algorithms".
- R. Ranjan, A. Harwood, and R. Buyya, "Peer-to-peer based resource discovery in global grids: a tutorial," IEEE Commun. Surv., vol. 10, no. 2. and P. Trunfio, "Peer-to-Peer resource discovery in Grids: Models and systems," Future Generation Computer Systems archive, vol. 23, no. 7, Aug. 2007.
- Kelaskar, M.; Matossian, V.; Mehra, P.; Paul, D.; Parashar, M. (2002). A Study of Discovery Mechanisms for Peer-to-Peer Application. IEEE Computer Society. pp. 444–. ISBN 9780769515823.
- Dabek, Frank; Zhao, Ben; Druschel, Peter; Kubiatowicz, John; Stoica, Ion (2003). "Towards a Common API for Structured Peer-to-Peer Overlays". Peer-to-Peer Systems II. Lecture Notes in Computer Science. Vol. 2735. pp. 33–44. CiteSeerX 10.1.1.12.5548. doi:10.1007/978-3-540-45172-3_3. ISBN 978-3-540-40724-9.
- Moni Naor and Udi Wieder. Novel Architectures for P2P Applications: the Continuous-Discrete Approach Archived 2019-12-09 at the Wayback Machine. Proc. SPAA, 2003.
- Gurmeet Singh Manku. Dipsea: A Modular Distributed Hash Table Archived 2004-09-10 at the Wayback Machine. Ph. D. Thesis (Stanford University), August 2004.
- Byung-Gon Chun, Ben Y. Zhao, John D. Kubiatowicz (2005-02-24). "Impact of Neighbor Selection on Performance and Resilience of Structured P2P Networks" (PDF). Retrieved 2019-08-24.
{{cite web}}: CS1 maint: multiple names: authors list (link) - Li, Deng; et al. (2009). Vasilakos, A.V.; et al. (eds.). An Efficient, Scalable, and Robust P2P Overlay for Autonomic Communication. Springer. p. 329. ISBN 978-0-387-09752-7.
- Bandara, H. M. N. Dilum; Jayasumana, Anura P. (January 2012). "Evaluation of P2P Resource Discovery Architectures Using Real-Life Multi-Attribute Resource and Query Characteristics". IEEE Consumer Communications and Networking Conf. (CCNC '12).
- Korzun, Dmitry; Gurtov, Andrei (November 2012). Structured P2P Systems: Fundamentals of Hierarchical Organization, Routing, Scaling, and Security. Springer. ISBN 978-1-4614-5482-3.
- Ranjan, Rajiv; Harwood, Aaron; Buyya, Rajkumar (1 December 2006). "A Study on Peer-to-Peer Based Discovery of Grid Resource Information" (PDF). Archived from the original (PDF) on 14 May 2011. Retrieved 25 August 2008.
- Ranjan, Rajiv; Chan, Lipo; Harwood, Aaron; Karunasekera, Shanika; Buyya, Rajkumar. "Decentralised Resource Discovery Service for Large Scale Federated Grids" (PDF). Archived from the original (PDF) on 2008-09-10.
- Darlagiannis, Vasilios (2005). "Hybrid Peer-to-Peer Systems". In Steinmetz, Ralf; Wehrle, Klaus (eds.). Peer-to-Peer Systems and Applications. Springer. ISBN 9783540291923.
- Yang, Beverly; Garcia-Molina, Hector (2001). "Comparing Hybrid Peer-to-Peer Systems" (PDF). Very Large Data Bases. Retrieved 8 October 2013.
- Padmanabhan, Venkata N.; Sripanidkulchai, Kunwadee (2002). The Case for Cooperative Networking (PostScript with addendum). Lecture Notes in Computer Science. Vol. Proceedings of the First International Workshop on Peer-to-Peer Systems. Cambridge, MA: Springer (published March 2002). pp. 178. doi:10.1007/3-540-45748-8_17. ISBN 978-3-540-44179-3. PDF (Microsoft, with addendum) Archived 2007-04-17 at the Wayback Machine PDF (Springer, original, fee may be required) Archived 2023-01-01 at the Wayback Machine
- "CoopNet: Cooperative Networking". Microsoft Research. Project home page.
- ^ Vu, Quang H.; et al. (2010). Peer-to-Peer Computing: Principles and Applications. Springer. p. 8. ISBN 978-3-642-03513-5.
- "Malware Propagation Modelling in Peer-to-Peer Networks: A Review" (PDF).
- Goebel, Jan; et al. (2007). "Measurement and Analysis of Autonomous Spreading Malware in a University Environment". In Hämmerli, Bernhard Markus; Sommer, Robin (eds.). Detection of Intrusions and Malware, and Vulnerability Assessment: 4th International Conference, DIMVA 2007 Lucerne, Switzerland, July 12-13, 2007 Proceedings. Springer. p. 112. ISBN 9783540736134.
- Sorkin, Andrew Ross (4 May 2003). "Software Bullet Is Sought to Kill Musical Piracy". New York Times. Retrieved 5 November 2011.
- Singh, Vivek; Gupta, Himani (2012). Anonymous File Sharing in Peer to Peer System by Random Walks (Technical report). SRM University. 123456789/9306.
- Lua, Eng Keong; Crowcroft, Jon; Pias, Marcelo; Sharma, Ravi; Lim, Steven (2005). "A survey and comparison of peer-to-peer overlay network schemes". Archived from the original on 2012-07-24.
- Balakrishnan, Hari; Kaashoek, M. Frans; Karger, David; Morris, Robert; Stoica, Ion (2003). "Looking up data in P2P systems" (PDF). Communications of the ACM. 46 (2): 43–48. CiteSeerX 10.1.1.5.3597. doi:10.1145/606272.606299. S2CID 2731647. Retrieved 8 October 2013.
- "Art thou a Peer?". www.p2pnews.net. 14 June 2012. Archived from the original on 6 October 2013. Retrieved 10 October 2013.
- Sharma, Parul; Bhakuni, Anuja; Kaushal, Rishabh (2013). "Performance analysis of BitTorrent protocol". 2013 National Conference on Communications (NCC). pp. 1–5. doi:10.1109/NCC.2013.6488040. ISBN 978-1-4673-5952-8.
- Li, Jin (2008). "On peer-to-peer (P2P) content delivery" (PDF). Peer-to-Peer Networking and Applications. 1 (1): 45–63 ≤≥. doi:10.1007/s12083-007-0003-1. S2CID 16438304.
- Stutzbach, Daniel; et al. (2005). "The scalability of swarming peer-to-peer content delivery" (PDF). In Boutaba, Raouf; et al. (eds.). NETWORKING 2005 -- Networking Technologies, Services, and Protocols; Performance of Computer and Communication Networks; Mobile and Wireless Communications Systems. Springer. pp. 15–26. ISBN 978-3-540-25809-4.
- Gareth Tyson, Andreas Mauthe, Sebastian Kaune, Mu Mu and Thomas Plagemann. Corelli: A Dynamic Replication Service for Supporting Latency-Dependent Content in Community Networks. In Proc. 16th ACM/SPIE Multimedia Computing and Networking Conference (MMCN), San Jose, CA (2009)."Archived copy" (PDF). Archived from the original (PDF) on 2011-04-29. Retrieved 2011-03-12.
{{cite web}}: CS1 maint: archived copy as title (link) - ^ Glorioso, Andrea; et al. (2010). "The Social Impact of P2P Systems". In Shen; et al. (eds.). Handbook of Peer-to-Peer Networking. Springer. p. 48. ISBN 978-0-387-09750-3.
- ^ John Borland (April 25, 2003). "Judge: File-Swapping Tools are Legal". news.cnet.com. Archived from the original on 2012-03-10.
- Walker, Leslie (2001-11-08). "Uncle Sam Wants Napster!". The Washington Post. Retrieved 2010-05-22.
- Hammerksjold Andreas; Engler, Narkis, "Delivery Optimization - a deep dive" Archived 2019-02-04 at the Wayback Machine, Channel 9, 11 October 2017, Retrieved on 4 February 2019.
- Krishnan, R., Smith, M. D., Tang, Z., & Telang, R. (2004, January). The impact of free-riding on peer-to-peer networks. In System Sciences, 2004. Proceedings of the 37th Annual Hawaii International Conference on (pp. 10-pp). IEEE.
- ^ Feldman, M., Lai, K., Stoica, I., & Chuang, J. (2004, May). Robust incentive techniques for peer-to-peer networks. In Proceedings of the 5th ACM conference on Electronic commerce (pp. 102-111). ACM.
- Vu, Quang H.; et al. (2010). Peer-to-Peer Computing: Principles and Applications. Springer. p. 172. ISBN 978-3-642-03513-5.
- P. Antoniadis and B. Le Grand, "Incentives for resource sharing in self-organized communities: From economics to social psychology," Digital Information Management (ICDIM '07), 2007
- Vu, Quang H.; et al. (2010). Peer-to-Peer Computing: Principles and Applications. Springer. pp. 179–181. ISBN 978-3-642-03513-5.
- "No country is free from child sexual abuse, exploitation, UN's top rights forum hears". UN News. March 3, 2020.
- Majoras, D. B. (2005). Peer-to-peer file-sharing technology consumer protection and competition issues. Federal Trade Commission, Retrieved from http://www.ftc.gov/reports/p2p05/050623p2prpt.pdf Archived 2012-11-01 at the Wayback Machine
- The Government of the Hong Kong Special Administrative Region, (2008). Peer-to-peer network. Retrieved from website: http://www.infosec.gov.hk/english/technical/files/peer.pdf Archived 2019-12-09 at the Wayback Machine
- Sanders, Linley (2017-09-22). "Illegal downloads may not actually harm sales, but the European Union doesn't want you to know that". Newsweek. Retrieved 2018-03-29.
- Polgar, David Ryan (October 15, 2017). "Does Video Game Piracy Actually Result in More Sales?". Big Think. Retrieved 2018-03-29.
- Orland, Kyle (September 26, 2017). "EU study finds piracy doesn't hurt game sales, may actually help". Ars Technica. Retrieved 2018-03-29.
- "What is bandwidth throttling? How to stop it | NordVPN". nordvpn.com. 2022-07-01. Retrieved 2024-08-21.
- Hjelmvik, Erik; John, Wolfgang (2010-07-27). "Breaking and Improving Protocol Obfuscation" (PDF). Technical Report. ISSN 1652-926X.
- ^ Basu, A., Fleming, S., Stanier, J., Naicken, S., Wakeman, I., & Gurbani, V. K. (2013). The state of peer-to-peer network simulators. ACM Computing Surveys, 45(4), 46.
- Ihle, Cornelius; Trautwein, Dennis; Schubotz, Moritz; Meuschke, Norman; Gipp, Bela (2023-01-24). "Incentive Mechanisms in Peer-to-Peer Networks — A Systematic Literature Review". ACM Computing Surveys. 55 (14s): 1–69. doi:10.1145/3578581. ISSN 0360-0300. S2CID 256106264.
- A Bhakuni, P Sharma, R Kaushal "Free-rider detection and punishment in BitTorrent based P2P networks", International Advanced Computing Conference, 2014. doi:10.1109/IAdCC.2014.6779311
External links
- Ghosh Debjani, Rajan Payas, Pandey Mayank P2P-VoD Streaming: Design Issues & User Experience Challenges Archived 2017-02-19 at the Wayback Machine Springer Proceedings, June 2014
- Glossary of P2P terminology
- Foundation of Peer-to-Peer Computing, Special Issue, Elsevier Journal of Computer Communication, (Ed) Javed I. Khan and Adam Wierzbicki, Volume 31, Issue 2, February 2008
- Anderson, Ross J. "The eternity service". Pragocrypt. 1996.
- Marling Engle & J. I. Khan. Vulnerabilities of P2P systems and a critical look at their solutions Archived 2007-06-15 at the Wayback Machine, May 2006
- Stephanos Androutsellis-Theotokis and Diomidis Spinellis. A survey of peer-to-peer content distribution technologies Archived 2020-11-09 at the Wayback Machine. ACM Computing Surveys, 36(4):335–371, December 2004.
- Biddle, Peter, Paul England, Marcus Peinado, and Bryan Willman, The Darknet and the Future of Content Distribution Archived 2011-07-27 at the Wayback Machine. In 2002 ACM Workshop on Digital Rights Management, November 2002.
- John F. Buford, Heather Yu, Eng Keong Lua P2P Networking and Applications. ISBN 0123742145, Morgan Kaufmann, December 2008
- Djamal-Eddine Meddour, Mubashar Mushtaq, and Toufik Ahmed, "Open Issues in P2P Multimedia Streaming Archived 2011-08-22 at the Wayback Machine", in the proceedings of the 1st Multimedia Communications Workshop MULTICOMM 2006 held in conjunction with IEEE ICC 2006 pp 43–48, June 2006, Istanbul, Turkey.
- Detlef Schoder and Kai Fischbach, "Core Concepts in Peer-to-Peer (P2P) Networking Archived 2011-09-15 at the Wayback Machine". In: Subramanian, R.; Goodman, B. (eds.): P2P Computing: The Evolution of a Disruptive Technology, Idea Group Inc, Hershey. 2005
- Ramesh Subramanian and Brian Goodman (eds), Peer-to-Peer Computing: Evolution of a Disruptive Technology, ISBN 1-59140-429-0, Idea Group Inc., Hershey, PA, United States, 2005.
- Shuman Ghosemajumder. Advanced Peer-Based Technology Business Models Archived 2012-10-13 at the Wayback Machine. MIT Sloan School of Management, 2002.
- Silverthorne, Sean. Music Downloads: Pirates- or Customers? Archived 2006-06-30 at the Wayback Machine. Harvard Business School Working Knowledge, 2004.
- Glasnost Archived 2014-10-05 at the Wayback Machine test P2P traffic shaping (Max Planck Institute for Software Systems)
| Bitcoin | |||||
|---|---|---|---|---|---|
| People | |||||
| Lists | |||||
| Technologies | |||||
| Forks |
| ||||
| History | |||||
| Movies |
| ||||
| Legal entities (not exchanges) | |||||
| Bitcoin in El Salvador | |||||
| Tor onion services | |
|---|---|
| Search engines | |
| News | |
| File storage and peer-to-peer file sharing | |
| Email and instant messaging | |
| Social media and forums | |
| Financial | |
| Darknet markets | |
| Document archives | |
| Nonprofit organizations | |
| Operating systems | |
| Government | |
| Whistleblowing | |
| Pornography | |
| Other | |
Sites in italics are now offline or discontinued (not counting ambiguously forked sites).
| |
| Cryptographic software | |||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Email clients | |||||||||||||||
| Secure communication |
| ||||||||||||||
| Disk encryption (Comparison) | |||||||||||||||
| Anonymity | |||||||||||||||
| File systems (List) | |||||||||||||||
| Security-focused operating system | |||||||||||||||
| Service providers | |||||||||||||||
| Educational | |||||||||||||||
| Anti–computer forensics | |||||||||||||||
| Related topics | |||||||||||||||
| Peer-to-peer file sharing | |||||||
|---|---|---|---|---|---|---|---|
| Networks, protocols |
| ||||||
| Comparisons of clients | |||||||
| Hyperlinks | |||||||
| Uses | |||||||
| Concepts |
| ||||||
| Internal technologies | |||||||