| Revision as of 15:57, 2 April 2007 view sourceComputerjoe (talk | contribs)Autopatrolled, Pending changes reviewers, Rollbackers13,763 edits Revert to revision 119741871 dated 2007-04-02 15:54:49 by Autocracy using popups← Previous edit | Latest revision as of 04:50, 22 December 2024 view source Constant314 (talk | contribs)Extended confirmed users, Pending changes reviewers, Rollbackers13,373 edits Restored revision 1260570568 by Whizz40 (talk): Use plain languageTags: Twinkle Undo | ||
| Line 1: | Line 1: | ||
| {{Short description|Global system of connected computer networks}} | |||
| {{Unreferenced|date=February 2007}} | |||
| {{About|the worldwide computer network|the global system of pages accessed through URLs via the Internet|World Wide Web|other uses}} | |||
| {{dablink|For the more general networking concept, see ], ], and ].}} | |||
| {{Redirect|The Internet|the American music group|The Internet (band)|the song Welcome To The Internet|Bo Burnham: Inside}} | |||
| <!-- The Internet and the World Wide Web are different concepts - please do not muddle them in this article --> | |||
| {{Redirect|Interweb|the song by Poppy|Interweb (song)}} | |||
| ] | |||
| {{ |
{{pp-semi-indef}} | ||
| {{pp-move}} | |||
| {{Use American English|date=August 2020}} | |||
| {{Use dmy dates|date=August 2020}} | |||
| {{Internet}} | |||
| {{Area networks}} | |||
| <!-- The Internet and the World Wide Web are different concepts – please do not muddle them in this article :) --> | |||
| The '''Internet''' |
The '''Internet''' (or '''internet'''){{efn|See ]<!-- Added per discussion currently underway on the Talk page -->}} is the ] of interconnected ]s that uses the ] (TCP/IP){{Efn|Despite the name, TCP/IP also includes UDP traffic, which is significant.<ref>{{cite web |url=https://www.cc.gatech.edu/~dovrolis/Courses/8803_F03/amogh.ppt |author=Amogh Dhamdhere |title=Internet Traffic Characterization |access-date=2022-05-06}}</ref>}} to communicate between networks and devices. It is a ] that consists of ], public, academic, business, and government networks of local to global scope, linked by a broad array of electronic, ], and ] technologies. The Internet carries a vast range of information resources and services, such as the interlinked ] documents and ] of the ] (WWW), ], ], and ]. | ||
| The origins of the Internet date back to research that enabled the ] of computer resources, the development of ] in the 1960s and the design of computer networks for ].<ref name="The Washington Post">{{Cite news|url=https://www.washingtonpost.com/sf/business/2015/05/30/net-of-insecurity-part-1/|title=A Flaw in the Design|date=30 May 2015|newspaper=The Washington Post|quote=The Internet was born of a big idea: Messages could be chopped into chunks, sent through a network in a series of transmissions, then reassembled by destination computers quickly and efficiently. Historians credit seminal insights to Welsh scientist Donald W. Davies and American engineer Paul Baran. ... The most important institutional force ... was the Pentagon's Advanced Research Projects Agency (ARPA) ... as ARPA began work on a groundbreaking computer network, the agency recruited scientists affiliated with the nation's top universities.|access-date=20 February 2020|archive-date=8 November 2020|archive-url=https://web.archive.org/web/20201108111512/https://www.washingtonpost.com/sf/business/2015/05/30/net-of-insecurity-part-1/|url-status=live}}</ref><ref name=":6">{{Cite book |last=Yates |first=David M. |url=https://books.google.com/books?id=ToMfAQAAIAAJ&q=packet+switch |title=Turing's Legacy: A History of Computing at the National Physical Laboratory 1945-1995 |date=1997 |publisher=National Museum of Science and Industry |isbn=978-0-901805-94-2 |pages=132–4 |language=en |quote=Davies's invention of packet switching and design of computer communication networks ... were a cornerstone of the development which led to the Internet}}</ref> The set of rules (]s) to enable ] on the Internet arose from research and development commissioned in the 1970s by the ] (DARPA) of the ] in collaboration with universities and researchers across the ] and in the ] and ].<ref name="Abbatep3">{{harvnb|Abbate|1999|p= "The manager of the ARPANET project, Lawrence Roberts, assembled a large team of computer scientists ... and he drew on the ideas of network experimenters in the United States and the United Kingdom. Cerf and Kahn also enlisted the help of computer scientists from England, France and the United States"}}</ref><ref>{{cite web |date=27 October 2009 |title=The Computer History Museum, SRI International, and BBN Celebrate the 40th Anniversary of First ARPANET Transmission, Precursor to Today's Internet |url=https://www.sri.com/newsroom/press-releases/computer-history-museum-sri-international-and-bbn-celebrate-40th-anniversary |archive-url=https://web.archive.org/web/20190329134941/https://www.sri.com/newsroom/press-releases/computer-history-museum-sri-international-and-bbn-celebrate-40th-anniversary |archive-date=March 29, 2019 |access-date=25 September 2017 |publisher=SRI International |quote=But the ARPANET itself had now become an island, with no links to the other networks that had sprung up. By the early 1970s, researchers in France, the UK, and the U.S. began developing ways of connecting networks to each other, a process known as internetworking.}}</ref><ref>{{cite web |author1=by Vinton Cerf, as told to Bernard Aboba |date=1993 |title=How the Internet Came to Be |url=http://elk.informatik.hs-augsburg.de/tmp/cdrom-oss/CerfHowInternetCame2B.html |archive-url=https://web.archive.org/web/20170926042220/http://elk.informatik.hs-augsburg.de/tmp/cdrom-oss/CerfHowInternetCame2B.html |archive-date=September 26, 2017 |access-date=25 September 2017 |quote=We began doing concurrent implementations at Stanford, BBN, and University College London. So effort at developing the Internet protocols was international from the beginning.}}</ref> The ] initially served as a backbone for the interconnection of regional academic and military networks in the United States to enable ]. The funding of the ] as a new backbone in the 1980s, as well as private funding for other commercial extensions, encouraged worldwide participation in the development of new networking technologies and the merger of many networks using DARPA's ].<ref>{{cite web|url=http://www.livinginternet.com/i/ii_summary.htm|title=Internet History – One Page Summary|archive-url=https://web.archive.org/web/20140702210150/http://www.livinginternet.com/i/ii_summary.htm |archive-date=2 July 2014|website=The Living Internet|first=Bill|last=Stewart|date=January 2000}}</ref> The linking of commercial networks and enterprises by the early 1990s, as well as the advent of the ],<ref>{{Cite book |title=The Desk Encyclopedia of World History |publisher=] |year=2006 |isbn=978-0-7394-7809-7 |editor-last=Wright |editor-first=Edmund |location=New York |page=312}}</ref> marked the beginning of the transition to the modern Internet,<ref>"#3 1982: the ARPANET community grows" in {{webarchive|url=https://web.archive.org/web/20170306161657/http://www.vox.com/a/internet-maps|date=6 March 2017}}, Timothy B. Lee, Vox Conversations, 2 June 2014. Retrieved 27 June 2014.</ref> and generated sustained exponential growth as generations of institutional, ], and ] ]s were connected to the internetwork. Although the Internet was widely used by ] in the 1980s, the subsequent ] in the 1990s and beyond incorporated its services and technologies into virtually every aspect of modern life. | |||
| ==Terminology: Internet vs. World Wide Web== | |||
| The Internet and the ] are not synonymous: the Internet is a collection of interconnected ''computer networks'', linked by ] wires, ] cables, ] connections, etc.; the Web is a collection of interconnected documents and other ''resources'', linked by ]s and ]. The World Wide Web is accessible via the Internet, as are many other services including ], ], and others described below. | |||
| Most traditional communication media, including ], ], ], paper mail, and newspapers, are reshaped, redefined, or even bypassed by the Internet, giving birth to new services such as ], ], ], ], digital newspapers, and ] websites. Newspapers, books, and other print publishing have adapted to ] technology or have been reshaped into ], ]s, and online ]s. The Internet has enabled and accelerated new forms of personal interaction through ], ]s, and ]s. ] has grown exponentially for major retailers, ]es, and ]s, as it enables firms to extend their "]" presence to serve a larger market or even ]. ] and ] on the Internet affect ]s across entire industries. | |||
| The best way to define and distinguish between these terms is with reference to the ]. This collection of standards and protocols is organized into layers such that each layer provides the foundation and the services required by the layer above. In this conception, the term Internet refers to computers and networks that communicate using ] (Internet protocol) and ] (Transmission Control Protocol). Once this networking structure is established, then other protocols can run “on top.” These other protocols are sometimes called services or applications. ] (HTTP) is the application layer protocol that ]s and provides access to the files, documents and other resources of the World Wide Web. | |||
| The Internet has no single centralized governance in either technological implementation or policies for access and usage; each constituent network sets its own policies.<ref>{{cite web|url=http://computer.howstuffworks.com/internet/basics/who-owns-internet.htm|archive-url=https://web.archive.org/web/20140619070159/http://computer.howstuffworks.com/internet/basics/who-owns-internet.htm |archive-date=19 June 2014|first=Jonathan|last=Strickland|title=How Stuff Works: Who owns the Internet?|date=3 March 2008|access-date=27 June 2014}}</ref> The overarching definitions of the two principal ]s on the Internet, the ] (IP address) space and the ] (DNS), are directed by a maintainer organization, the ] (ICANN). The technical underpinning and standardization of the core protocols is an activity of the ] (IETF), a non-profit organization of loosely affiliated international participants that anyone may associate with by contributing technical expertise.<ref>{{cite IETF |title=The Tao of IETF: A Novice's Guide to Internet Engineering Task Force|rfc=4677|last1=Hoffman|first1=P.|last2=Harris|first2=S.|date=September 2006|publisher=]}}</ref> In November 2006, the Internet was included on '']''{{'}}s list of the ].<ref>{{cite web |url=https://www.usatoday.com/travel/news/2006-10-26-seven-wonders-experts_x.htm |title=New Seven Wonders panel |work=USA Today |date=27 October 2006 |access-date=31 July 2010 |archive-date=15 July 2010 |archive-url=https://web.archive.org/web/20100715032114/http://www.usatoday.com/travel/news/2006-10-26-seven-wonders-experts_x.htm }}</ref> | |||
| ==Creation of the Internet== | |||
| {{TOC limit}} | |||
| {{details|History of the Internet}} | |||
| == Terminology == | |||
| The ]'s launch of ] spurred the ] to create the Advanced Research Projects Agency (ARPA, later known as the ], or DARPA) in February ] to regain a technological lead. ARPA created the ] (IPTO) to further the research of the ] (SAGE) program, which had networked country-wide ] systems together for the first time. ] was selected to head the IPTO, and saw universal networking as a potential unifying human revolution. | |||
| {{Further|Capitalization of Internet|internetworking}} | |||
| The word ''internetted'' was used as early as 1849, meaning ''interconnected'' or ''interwoven''.<ref>{{OED|Internetted}} nineteenth-century use as an adjective.</ref> The word ''Internet'' was used in 1945 by the United States War Department in a radio operator's manual,<ref>{{cite web |title=United States Army Field Manual FM 24-6 Radio Operator's Manual Army Ground Forces June 1945 |date=18 September 2023 |url=https://archive.org/details/Fm24-6/mode/2up |publisher=United States War Department }}</ref> and in 1974 as the shorthand form of Internetwork.<ref name="RFC675"/> Today, the term ''Internet'' most commonly refers to the global system of interconnected ]s, though it may also refer to any group of smaller networks.<ref name="The New York Times"/> | |||
| In ], Licklider moved from the Psycho-Acoustic Laboratory at ] to ], where he served on a committee that established ]. He worked on the SAGE project. In ] he became a Vice President at ], where he bought the first production ] computer and conducted the first public demonstration of ]. | |||
| When it came into common use, most publications treated the word ''Internet'' as a capitalized ]; this has become less common.<ref name="The New York Times" /> This reflects the tendency in English to capitalize new terms and move them to lowercase as they become familiar.<ref name="The New York Times" /><ref name="Wired" /> The word is sometimes still capitalized to distinguish the global internet from smaller networks, though many publications, including the '']'' since 2016, recommend the lowercase form in every case.<ref name="The New York Times">{{Cite news|last=Corbett|first=Philip B.|date=1 June 2016|title=It's Official: The 'Internet' Is Over|language=en-US|work=The New York Times|url=https://www.nytimes.com/2016/06/02/insider/now-it-is-official-the-internet-is-over.html|access-date=29 August 2020|issn=0362-4331|archive-date=14 October 2020|archive-url=https://web.archive.org/web/20201014142148/https://www.nytimes.com/2016/06/02/insider/now-it-is-official-the-internet-is-over.html|url-status=live}}</ref><ref name="Wired">{{Cite news|last=Herring|first=Susan C.|date=19 October 2015|title=Should You Be Capitalizing the Word 'Internet'?|magazine=Wired|url=https://www.wired.com/2015/10/should-you-be-capitalizing-the-word-internet/|access-date=29 August 2020|issn=1059-1028|archive-date=31 October 2020|archive-url=https://web.archive.org/web/20201031024342/https://www.wired.com/2015/10/should-you-be-capitalizing-the-word-internet/|url-status=live}}</ref> In 2016, the '']'' found that, based on a study of around 2.5 billion printed and online sources, "Internet" was capitalized in 54% of cases.<ref>{{Cite web|last=Coren|first=Michael J.|title=One of the internet's inventors thinks it should still be capitalized|url=https://qz.com/698175/one-of-the-internets-inventors-thinks-it-should-still-be-capitalized/|access-date=8 September 2020|website=Quartz|date=2 June 2016 |language=en|archive-date=27 September 2020|archive-url=https://web.archive.org/web/20200927102759/https://qz.com/698175/one-of-the-internets-inventors-thinks-it-should-still-be-capitalized/|url-status=live}}</ref> | |||
| Licklider recruited ] to head a project to implement a network, and Roberts based the technology on the work of ] who had written an exhaustive study for the ] that recommended ] (as opposed to ]) to make a network highly robust and survivable. After much work, the first node went live at ] on ] ] on what would be called the ], one of the "eve" networks of today's Internet. Following on from this, the ], ] and ] collaborated to create the first international packet switched network, referred to as the ] (IPSS), in ]. This network grew from Europe and the US to cover ], ] and ] by 1981. | |||
| The terms ''Internet'' and '']'' are often used interchangeably; it is common to speak of "going on the Internet" when using a ] to view ]s. However, the ], or ''the Web'', is only one of a large number of Internet services,<ref>{{cite web|date=11 March 2014|title=World Wide Web Timeline|url=http://www.pewinternet.org/2014/03/11/world-wide-web-timeline/|url-status=live|archive-url=https://web.archive.org/web/20150729162322/http://www.pewinternet.org/2014/03/11/world-wide-web-timeline/|archive-date=29 July 2015|access-date=1 August 2015|publisher=Pews Research Center}}</ref> a collection of documents (web pages) and other ]s linked by ]s and ].<ref>{{cite web|title=HTML 4.01 Specification|url=http://www.w3.org/TR/html401/struct/links.html#h-12.1|url-status=live|archive-url=https://web.archive.org/web/20081006131915/http://www.w3.org/TR/html401/struct/links.html|archive-date=6 October 2008|access-date=13 August 2008|publisher=World Wide Web Consortium|quote=he link (or hyperlink, or Web link) the basic hypertext construct. A link is a connection from one Web resource to another. Although a simple concept, the link has been one of the primary forces driving the success of the Web.}}</ref> | |||
| The first ]-wide area network was operational by ] ], when the United States' ] (NSF) constructed a ] network backbone that would later become the ]. (This date is held by some to be technically that of the birth of the Internet.) It was then followed by the opening of the network to commercial interests in 1985. Important, separate networks that offered gateways into, then later merged with, the NSFNet include ], ] and the various commercial and educational ] ] and ]. ] (later called Sprintnet) was a large privately-funded national computer network with free ] in cities throughout the U.S. that had been in operation since the 1970s. This network eventually merged with the others in the 1990s as the TCP/IP protocol became increasingly popular. The ability of TCP/IP to work over these pre-existing communication networks, especially the international X.25 IPSS network, allowed for a great ease of growth. Use of the term "Internet" to describe a single global TCP/IP network originated around this time. | |||
| == History == | |||
| The network gained a public face in the 1990s. On ] ], ], which straddles the border between ] and ], publicized the new World Wide Web project, two years after ] had begun creating ], ] and the first few Web pages at CERN. | |||
| {{Main|History of the Internet |History of the World Wide Web|Protocol Wars}} | |||
| ] | |||
| In the 1960s, ] began developing systems for ] of computer resources.<ref name="Lee1992">{{cite journal |last1=Lee |first1=J.A.N. |last2=Rosin |first2=Robert F |date=1992 |title=Time-Sharing at MIT |url=https://archive.org/details/time-sharing-at-mit |journal=IEEE Annals of the History of Computing |volume=14 |issue=1 |page=16 |doi=10.1109/85.145316 |s2cid=30976386 |access-date=October 3, 2022|issn=1058-6180 }}</ref><ref name="ctsspg">F. J. Corbató, et al., '''' (MIT Press, 1963) {{ISBN|978-0-262-03008-3}}. "To establish the context of the present work, it is informative to trace the development of time-sharing at MIT. Shortly after the first paper on time-shared computers by C. Strachey at the June 1959 UNESCO Information Processing conference, H.M. Teager and J. McCarthy delivered an unpublished paper "Time-Shared Program Testing" at the August 1959 ACM Meeting."</ref> ] proposed the idea of a universal network while working at ] and, later, leading the ] (IPTO) at the ] (ARPA) of the United States ] (DoD). Research into ], one of the fundamental Internet technologies, started in the work of ] at ] in the early 1960s and, independently, ] at the United Kingdom's ] (NPL) in 1965.<ref name="The Washington Post" /><ref name="NIHF2007">{{cite web|url=http://www.invent.org/honor/inductees/inductee-detail/?IID=316|title=Inductee Details – Paul Baran|publisher=National Inventors Hall of Fame|archive-url=https://web.archive.org/web/20170906091231/http://www.invent.org/honor/inductees/inductee-detail/?IID=316|archive-date=6 September 2017|access-date=6 September 2017|postscript=none}}; {{cite web|url=http://www.invent.org/honor/inductees/inductee-detail/?IID=328|title=Inductee Details – Donald Watts Davies|publisher=National Inventors Hall of Fame|archive-url=https://web.archive.org/web/20170906091936/http://www.invent.org/honor/inductees/inductee-detail/?IID=328|archive-date=6 September 2017|access-date=6 September 2017}}</ref> After the ] in 1967, packet switching from the proposed ] and routing concepts proposed by Baran were incorporated into the design of the ], an experimental ] network proposed by ARPA.<ref>{{Cite book |last1=Hauben |first1=Michael |url=http://www.columbia.edu/~hauben/book-pdf/CHAPTER%205.pdf |title=Netizens: On the History and Impact of Usenet and the Internet |last2=Hauben |first2=Ronda |date=1997 |publisher=Wiley |isbn=978-0-8186-7706-9 |language=en |chapter=5 The Vision of Interactive Computing And the Future |access-date=2 March 2020 |archive-url=https://web.archive.org/web/20210103184558/http://www.columbia.edu/~hauben/book-pdf/CHAPTER%205.pdf |archive-date=3 January 2021 |url-status=live}}</ref><ref>{{Cite book |last1=Zelnick |first1=Bob |url=https://books.google.com/books?id=Q10phY811tUC&pg=PA66 |title=The Illusion of Net Neutrality: Political Alarmism, Regulatory Creep and the Real Threat to Internet Freedom |last2=Zelnick |first2=Eva |publisher=Hoover Press |year=2013 |isbn=978-0-8179-1596-4 |language=en |access-date=7 May 2020 |archive-url=https://web.archive.org/web/20210110133435/https://books.google.com/books?id=Q10phY811tUC&pg=PA66 |archive-date=10 January 2021 |url-status=live}}</ref><ref>{{cite web |last=Peter |first=Ian |year=2004 |title=So, who really did invent the Internet? |url=http://www.nethistory.info/History%20of%20the%20Internet/origins.html |archive-url=https://web.archive.org/web/20110903001108/http://www.nethistory.info/History%20of%20the%20Internet/origins.html |archive-date=3 September 2011 |access-date=27 June 2014 |website=The Internet History Project}}</ref> | |||
| ARPANET development began with two network nodes which were interconnected between the ] (UCLA) and the ] (now SRI International) on 29 October 1969.<ref name="NetValley">{{cite web|url=http://www.netvalley.com/intval.html|title=Roads and Crossroads of Internet History|archive-url=https://web.archive.org/web/20160127082435/http://www.netvalley.com/intval.html|archive-date=27 January 2016|first=Gregory|last=Gromov|year=1995}}</ref> The third site was at the ], followed by the ]. In a sign of future growth, 15 sites were connected to the young ARPANET by the end of 1971.<ref>{{cite book | author-link = Katie Hafner | last = Hafner | first = Katie | title = Where Wizards Stay Up Late: The Origins of the Internet | publisher = Simon & Schuster | year = 1998 | isbn = 978-0-684-83267-8 }}</ref><ref>{{cite web|author=Hauben, Ronda |title=From the ARPANET to the Internet |year=2001 |url=http://www.columbia.edu/~rh120/other/tcpdigest_paper.txt |access-date=28 May 2009 |url-status=live |archive-url=https://web.archive.org/web/20090721093920/http://www.columbia.edu/~rh120/other/tcpdigest_paper.txt |archive-date=21 July 2009 }}</ref> These early years were documented in the 1972 film '']''.<ref>{{Cite web|title=Internet Pioneers Discuss the Future of Money, Books, and Paper in 1972|url=https://paleofuture.gizmodo.com/internet-pioneers-discuss-the-future-of-money-books-a-880551175|access-date=31 August 2020|website=Paleofuture|date=23 July 2013 |language=en-us|archive-date=17 October 2020|archive-url=https://web.archive.org/web/20201017141323/https://paleofuture.gizmodo.com/internet-pioneers-discuss-the-future-of-money-books-a-880551175|url-status=live}}</ref> Thereafter, the ARPANET gradually developed into a decentralized communications network, connecting remote centers and military bases in the United States.<ref>{{Cite journal |last=Townsend |first=Anthony |date=2001 |title=The Internet and the Rise of the New Network Cities, 1969–1999 |url=http://journals.sagepub.com/doi/10.1068/b2688 |journal=Environment and Planning B: Planning and Design |language=en |volume=28 |issue=1 |pages=39–58 |doi=10.1068/b2688 |bibcode=2001EnPlB..28...39T |issn=0265-8135 |s2cid=11574572}}</ref> Other user networks and research networks, such as the ] and ], were developed in the late 1960s and early 1970s.<ref>{{cite book |last1=Kim |first1=Byung-Keun |url=https://books.google.com/books?id=lESrw3neDokC |title=Internationalising the Internet the Co-evolution of Influence and Technology |date=2005 |publisher=Edward Elgar |isbn=978-1-84542-675-0 |pages=51–55}}</ref> | |||
| An early popular ] was '']'' based upon ]. It was eventually replaced in popularity by the ] web browser. In 1993 the ] at the ] released version 1.0 of ''Mosaic'', and by late 1994 there was growing public interest in the previously academic/technical Internet. By 1996 the word "Internet" was coming into common daily usage, frequently misused to refer to the ]. | |||
| Early international collaborations for the ARPANET were rare. Connections were made in 1973 to Norway (] and ]),<ref>{{cite web |title=NORSAR and the Internet |url=http://www.norsar.no/norsar/about-us/History/Internet/ |publisher=NORSAR |archive-url=https://web.archive.org/web/20130121220318/http://www.norsar.no/norsar/about-us/History/Internet/ |archive-date=21 January 2013 }}</ref> and to ] research group at ] (UCL), which provided a gateway to ], forming the first ] for ].<ref>{{Cite journal|last=Kirstein|first=P.T.|date=1999|title=Early experiences with the Arpanet and Internet in the United Kingdom|url=https://pdfs.semanticscholar.org/4773/f19792f9fce8eacba72e5f8c2a021414e52d.pdf|archive-url=https://web.archive.org/web/20200207092443/https://pdfs.semanticscholar.org/4773/f19792f9fce8eacba72e5f8c2a021414e52d.pdf|archive-date=2020-02-07|journal=IEEE Annals of the History of Computing|volume=21|issue=1|pages=38–44|doi=10.1109/85.759368|s2cid=1558618|issn=1934-1547}}</ref> ARPA projects, the ] and commercial initiatives led to the development of various ] and standards by which multiple separate networks could become a single network or "a network of networks".<ref>{{cite web|url=http://www.internetsociety.org/internet/what-internet/history-internet/brief-history-internet#concepts|title=Brief History of the Internet: The Initial Internetting Concepts|archive-url=https://web.archive.org/web/20160409105511/http://www.internetsociety.org/internet/what-internet/history-internet/brief-history-internet|archive-date=9 April 2016|first=Barry M.|last=Leiner|website=Internet Society|access-date=27 June 2014}}</ref> In 1974, ] at ] and ] at DARPA published a proposal for "A Protocol for Packet Network Intercommunication".<ref name="IEEE Transactions on Communications">{{Cite journal |last1=Cerf |first1=V. |last2=Kahn |first2=R. |date=1974 |title=A Protocol for Packet Network Intercommunication |url=https://www.cs.princeton.edu/courses/archive/fall06/cos561/papers/cerf74.pdf |journal=IEEE Transactions on Communications |volume=22 |issue=5 |pages=637–648 |doi=10.1109/TCOM.1974.1092259 |issn=1558-0857 |quote=The authors wish to thank a number of colleagues for helpful comments during early discussions of international network protocols, especially R. Metcalfe, R. Scantlebury, D. Walden, and H. Zimmerman; D. Davies and L. Pouzin who constructively commented on the fragmentation and accounting issues; and S. Crocker who commented on the creation and destruction of associations. |archive-url=https://web.archive.org/web/20060913213037/https://www.cs.princeton.edu/courses/archive/fall06/cos561/papers/cerf74.pdf |archive-date=13 September 2006 |url-status=live }}</ref> They used the term ''internet'' as a shorthand for ''internetwork'' in ''{{IETF RFC|675}}'',<ref name="RFC675">{{cite IETF |title=Specification of Internet Transmission Control Protocol|rfc=675|last1=Cerf|first1=Vint|last2=Dalal|first2=Yogen|first3=Carl|last3=Sunshine |date=December 1974|publisher=]}}</ref> and later ] repeated this use. Cerf and Kahn credit ] and others with important influences on the resulting ] design.<ref name="IEEE Transactions on Communications" /><ref>{{Cite news|date=30 November 2013|title=The internet's fifth man|newspaper=The Economist|url=https://www.economist.com/news/technology-quarterly/21590765-louis-pouzin-helped-create-internet-now-he-campaigning-ensure-its|access-date=22 April 2020|issn=0013-0613|quote=In the early 1970s Mr Pouzin created an innovative data network that linked locations in France, Italy and Britain. Its simplicity and efficiency pointed the way to a network that could connect not just dozens of machines, but millions of them. It captured the imagination of Dr Cerf and Dr Kahn, who included aspects of its design in the protocols that now power the internet.|archive-date=19 April 2020|archive-url=https://web.archive.org/web/20200419230318/https://www.economist.com/news/technology-quarterly/21590765-louis-pouzin-helped-create-internet-now-he-campaigning-ensure-its|url-status=live}}</ref> National ] and commercial providers developed the ] standard and deployed it on ]s.<ref>{{cite book|last=Schatt|first=Stan|title=Linking LANs: A Micro Manager's Guide|publisher=McGraw-Hill|year=1991|isbn=0-8306-3755-9|page=200}}</ref> | |||
| Meanwhile, over the course of the decade, the Internet successfully accommodated the majority of previously existing public computer networks (although some networks, such as ], have remained separate). This growth is often attributed to the lack of central administration, which allows organic growth of the network, as well as the non-proprietary open nature of the Internet protocols, which encourages vendor interoperability and prevents any one company from exerting too much control over the network. | |||
| Access to the ARPANET was expanded in 1981 when the ] (NSF) funded the ] (CSNET). In 1982, the ] (TCP/IP) was standardized, which facilitated worldwide proliferation of interconnected networks. TCP/IP network access expanded again in 1986 when the ] (NSFNet) provided access to ] sites in the United States for researchers, first at speeds of 56 kbit/s and later at 1.5 Mbit/s and 45 Mbit/s.<ref>{{cite web|url=http://www.merit.edu/about/history/pdf/NSFNET_final.pdf|archive-url=https://web.archive.org/web/20150210181738/http://www.merit.edu/about/history/pdf/NSFNET_final.pdf|archive-date=2015-02-10|title=NSFNET: A Partnership for High-Speed Networking, Final Report 1987–1995|first=Karen D.|last=Frazer|website=Merit Network, Inc.|year=1995}}</ref> The NSFNet expanded into academic and research organizations in Europe, Australia, New Zealand and Japan in 1988–89.<ref>{{cite web |author=Ben Segal |author-link=Ben Segal (computer scientist) |year=1995 |title=A Short History of Internet Protocols at CERN |url=http://www.cern.ch/ben/TCPHIST.html |url-status=dead |archive-url=https://web.archive.org/web/20230608153730/http://ben.web.cern.ch/ben/TCPHIST.html |archive-date=8 June 2023 |access-date=14 October 2011}}</ref><ref>] (RIPE)</ref><ref>{{cite web|url=http://www.apan.net/meetings/busan03/cs-history.htm|title=Internet History in Asia|work=16th APAN Meetings/Advanced Network Conference in Busan|url-status=live|archive-url=https://web.archive.org/web/20060201035514/http://apan.net/meetings/busan03/cs-history.htm|archive-date=1 February 2006|access-date=25 December 2005}}</ref><ref>{{Cite web|url=http://www.nordu.net/history/TheHistoryOfNordunet_simple.pdf|title=The History of NORDUnet|archive-url=https://web.archive.org/web/20160304031416/http://www.nordu.net/history/TheHistoryOfNordunet_simple.pdf|archive-date=4 March 2016}}</ref> Although other network protocols such as ] and PTT public data networks had global reach well before this time, this marked the beginning of the Internet as an intercontinental network. Commercial ] (ISPs) emerged in 1989 in the United States and Australia.<ref>{{cite web|url=http://www.rogerclarke.com/II/OzI04.html#CIAP|title=Origins and Nature of the Internet in Australia|last=Clarke|first=Roger|access-date=21 January 2014|archive-date=9 February 2021|archive-url=https://web.archive.org/web/20210209201253/http://www.rogerclarke.com/II/OzI04.html#CIAP|url-status=live}}</ref> The ARPANET was decommissioned in 1990.<ref>{{cite IETF |rfc=2235 |page=8 |last=Zakon |first=Robert |date=November 1997 |publisher=] |access-date=2 December 2020}}</ref> | |||
| ==Today's Internet== | |||
| ] | |||
| Aside from the complex physical connections that make up its infrastructure, the Internet is facilitated by bi- or multi-lateral commercial contracts (e.g., ]s), and by technical specifications or ]s that describe how to exchange ] over the network. Indeed, the Internet is essentially defined by its interconnections and routing policies. | |||
| ] Backbone, {{Circa|1992}}]] | |||
| As of ] ], 1.114 billion people use the Internet according to . | |||
| Steady advances in ] technology and ] created new economic opportunities for commercial involvement in the expansion of the network in its core and for delivering services to the public. In mid-1989, ] and ] established connections to the Internet, delivering email and public access products to the half million users of the Internet.<ref>{{cite web|url=https://books.google.com/books?id=wDAEAAAAMBAJ&q=compuserve%20to%20mci%20mail%20internet&pg=PT31 |title=InfoWorld|date=25 September 1989 |via=Google Books |url-status=live |archive-url=https://web.archive.org/web/20170129225422/https://books.google.com/books?id=wDAEAAAAMBAJ&pg=PT31&lpg=PT31&dq=compuserve%20to%20mci%20mail%20internet |archive-date=29 January 2017 }}</ref> Just months later, on 1 January 1990, PSInet launched an alternate Internet backbone for commercial use; one of the networks that added to the core of the commercial Internet of later years. In March 1990, the first high-speed T1 (1.5 Mbit/s) link between the NSFNET and Europe was installed between ] and ], allowing much more robust communications than were capable with satellites.<ref>{{Cite web|date=February 1990|title=INTERNET MONTHLY REPORTS|url=http://ftp.cuhk.edu.hk/pub/doc/internet/Internet.Monthly.Report/imr9002.txt|archive-url=https://wayback.archive-it.org/all/20170525080041/ftp://ftp.cuhk.edu.hk/pub/doc/internet/Internet.Monthly.Report/imr9002.txt|archive-date=25 May 2017|access-date=28 November 2020}}</ref> | |||
| ===Internet protocols=== | |||
| {{details|Internet Protocols}} | |||
| In this context, there are three layers of protocols: | |||
| * At the lowest level is ''']''' (Internet Protocol), which defines the datagrams or ]s that carry blocks of data from one node to another. The vast majority of today's Internet uses version four of the IP protocol (i.e. ]), and although ] is standardized, it exists only as "islands" of connectivity, and there are many ISPs without any IPv6 connectivity. | |||
| * Next come ''']''' (Transmission Control Protocol), ''']''' (User Datagram Protocol), and ''']''' (Internet Control Message Protocol) - the protocols by which data is transmitted. TCP makes a virtual 'connection', which gives some level of guarantee of reliability. UDP is a best-effort, connectionless transport, in which data packets that are lost in transit will not be re-sent. ICMP is connectionless, it is used for control and signaling purposes. | |||
| * On top comes the ''']'''. This defines the specific messages and data formats sent and understood by the applications running at each end of the communication. | |||
| Later in 1990, ] began writing ], the first ], after two years of lobbying CERN management. By Christmas 1990, Berners-Lee had built all the tools necessary for a working Web: the ] (HTTP) 0.9,<ref>{{cite web|url=http://www.w3.org/Protocols/HTTP/AsImplemented.html |archive-url=https://web.archive.org/web/19970605071155/http://www.w3.org/Protocols/HTTP/AsImplemented.html |archive-date=5 June 1997 |first=Tim |last=Berners-Lee |title=The Original HTTP as defined in 1991 |work=W3C.org}}</ref> the ] (HTML), the first Web browser (which was also an ] and could access ] newsgroups and ] files), the first HTTP ] (later known as ]), the first ],<ref>{{Cite web|url=http://info.cern.ch/|archive-url=https://web.archive.org/web/20100105103513/http://info.cern.ch/|title=The website of the world's first-ever web server|archive-date=5 January 2010|website=info.cern.ch}}</ref> and the first Web pages that described the project itself. In 1991 the ] was founded, allowing PSInet to communicate with the other commercial networks ] and Alternet. ] was the first ] to offer online Internet banking services to all of its members in October 1994.<ref>{{cite press release|title=Stanford Federal Credit Union Pioneers Online Financial Services.|date=21 June 1995|url=http://www.thefreelibrary.com/Stanford+Federal+Credit+Union+Pioneers+Online+Financial+Services.-a017104850|access-date=21 December 2018|archive-url=https://web.archive.org/web/20181221041632/https://www.thefreelibrary.com/Stanford+Federal+Credit+Union+Pioneers+Online+Financial+Services.-a017104850|archive-date=21 December 2018|url-status=live}}</ref> In 1996, ], also a ], became the second online bank in the world and the first in Europe.<ref>{{cite web | url=https://www.op.fi/op-financial-group/about-us/op-financial-group-in-brief/history | title=History – About us – OP Group | access-date=21 December 2018 | archive-url=https://web.archive.org/web/20181221041413/https://www.op.fi/op-financial-group/about-us/op-financial-group-in-brief/history | archive-date=21 December 2018 | url-status=live }}</ref> By 1995, the Internet was fully commercialized in the U.S. when the NSFNet was decommissioned, removing the last restrictions on use of the Internet to carry commercial traffic.<ref name="ConneXions-April1996">{{cite journal |url=http://www.merit.edu/research/nsfnet_article.php |title=Retiring the NSFNET Backbone Service: Chronicling the End of an Era |first1=Susan R. |last1=Harris |first2=Elise |last2=Gerich |journal=ConneXions |volume=10 |number=4 |date=April 1996 |archive-url=https://web.archive.org/web/20130817124939/http://merit.edu/research/nsfnet_article.php |archive-date=17 August 2013 }}</ref> | |||
| ===Internet structure=== | |||
| There have been many analyses of the Internet and its structure. For example, it has been determined that the Internet IP routing structure and hypertext links of the World Wide Web are examples of ]s. | |||
| {{Worldwide Internet users}} | |||
| Similar to the way the commercial Internet providers connect via ]s, research networks tend to interconnect into large subnetworks such as: | |||
| As technology advanced and commercial opportunities fueled reciprocal growth, the volume of ] started experiencing similar characteristics as that of the scaling of ]s, exemplified by ], doubling every 18 months. This growth, formalized as ], was catalyzed by advances in ], ] light wave systems, and ] performance.<ref name="Jindal">{{cite book |last1=Jindal |first1=R. P. |title=2009 2nd International Workshop on Electron Devices and Semiconductor Technology |chapter=From millibits to terabits per second and beyond - over 60 years of innovation |s2cid=25112828 |year=2009 |volume=49 |pages=1–6 |doi=10.1109/EDST.2009.5166093 |chapter-url=https://events.vtools.ieee.org/m/195547 |isbn=978-1-4244-3831-0 |access-date=24 August 2019 |archive-url=https://web.archive.org/web/20190823230141/https://events.vtools.ieee.org/m/195547 |archive-date=23 August 2019 }}</ref> | |||
| *] | |||
| *] | |||
| *] | |||
| *] (the UK's Joint Academic Network aka UKERNA) | |||
| Since 1995, the Internet has tremendously impacted culture and commerce, including the rise of near-instant communication by email, ], telephony (] or VoIP), ], and the World Wide Web<ref>{{cite news|url=http://news.bbc.co.uk/2/hi/science/nature/5242252.stm|title=How the web went world wide|archive-url=https://web.archive.org/web/20111121092636/http://news.bbc.co.uk/2/hi/science/nature/5242252.stm |archive-date=21 November 2011|first=Mark|last=Ward|website=Technology Correspondent|date=3 August 2006|publisher=BBC News|access-date=24 January 2011}}</ref> with its ], blogs, ]s, and ] sites. Increasing amounts of data are transmitted at higher and higher speeds over fiber optic networks operating at 1 Gbit/s, 10 Gbit/s, or more. The Internet continues to grow, driven by ever-greater amounts of online information and knowledge, commerce, entertainment and social networking services.<ref>{{cite web|url=http://clickz.com/showPage.html?page=3626274 |archive-url=https://web.archive.org/web/20081004000237/http://www.clickz.com/showPage.html?page=3626274|title=Brazil, Russia, India and China to Lead Internet Growth Through 2011 |publisher=Clickz.com |access-date=28 May 2009|archive-date=4 October 2008}}</ref> During the late 1990s, it was estimated that traffic on the public Internet grew by 100 percent per year, while the mean annual growth in the number of Internet users was thought to be between 20% and 50%.<ref>{{cite web |url=http://www.dtc.umn.edu/~odlyzko/doc/internet.size.pdf |title=The size and growth rate of the Internet |access-date=21 May 2007 |author1=Coffman, K.G |author2=Odlyzko, A.M. |author-link2=Andrew Odlyzko |publisher=AT&T Labs |date=2 October 1998 |archive-url=https://web.archive.org/web/20070614012344/http://www.dtc.umn.edu/~odlyzko/doc/internet.size.pdf |archive-date=14 June 2007 }}</ref> This growth is often attributed to the lack of central administration, which allows organic growth of the network, as well as the non-proprietary nature of the Internet protocols, which encourages vendor interoperability and prevents any one company from exerting too much control over the network.<ref>{{cite book | last = Comer | first = Douglas | title = The Internet book | publisher = Prentice Hall | page = | isbn = 978-0-13-233553-9 | year = 2006 | url-access = registration | url = https://archive.org/details/internetbookever00come_0/page/64 }}</ref> {{as of|2011|March|31}}, the estimated total number of Internet users was 2.095 billion (30% of ]).<ref name="stats1">{{cite web|url=http://www.internetworldstats.com/stats.htm|title=World Internet Users and Population Stats|date=22 June 2011|work=Internet World Stats|publisher=Miniwatts Marketing Group|archive-url=https://web.archive.org/web/20110623200007/http://www.internetworldstats.com/stats.htm|archive-date=23 June 2011|access-date=23 June 2011}}<!-- previous cite {{cite web|url=http://www.50x15.com/en-us/internet_usage.aspx |title=AMD 50x15 – World Internet Usage |publisher=50x15.com |access-date=6 November 2009 |archive-url=https://web.archive.org/web/20090831063352/http://www.50x15.com/en-us/internet_usage.aspx |archive-date=31 August 2009 |df= }} --></ref> It is estimated that in 1993 the Internet carried only 1% of the information flowing through two-way ]. By 2000 this figure had grown to 51%, and by 2007 more than 97% of all telecommunicated information was carried over the Internet.<ref>{{cite journal|title=The World's Technological Capacity to Store, Communicate, and Compute Information |first1=Martin |last1=Hilbert |first2=Priscila |last2=López |s2cid=206531385 |date=April 2011 |journal=] |volume=332 |pages=60–65 |doi=10.1126/science.1200970 |issue=6025 |bibcode=2011Sci...332...60H |pmid=21310967 |doi-access=free }}</ref> | |||
| These in turn are built around relatively smaller networks. See also the list of ] | |||
| == Governance == | |||
| In network ] diagrams, the Internet is often represented by a cloud symbol, into and out of which network communications can pass. | |||
| {{Main|Internet governance}} | |||
| ] neighborhood of ], California, United States]] | |||
| The Internet is a ] that comprises many voluntarily interconnected autonomous networks. It operates without a central governing body. The technical underpinning and standardization of the core protocols (] and ]) is an activity of the ] (IETF), a non-profit organization of loosely affiliated international participants that anyone may associate with by contributing technical expertise. To maintain interoperability, the principal ]s of the Internet are administered by the ] (ICANN). ICANN is governed by an international board of directors drawn from across the Internet technical, business, academic, and other non-commercial communities. ICANN coordinates the assignment of unique identifiers for use on the Internet, including ]s, IP addresses, application port numbers in the transport protocols, and many other parameters. Globally unified name spaces are essential for maintaining the global reach of the Internet. This role of ICANN distinguishes it as perhaps the only central coordinating body for the global Internet.<ref>{{cite web|last=Klein|first=Hans|year=2004|url=http://www.ip3.gatech.edu/research/KLEIN_ICANN%2BSovereignty.doc|title=ICANN and Non-Territorial Sovereignty: Government Without the Nation State|archive-url=https://web.archive.org/web/20130524035251/http://www.ip3.gatech.edu/research/KLEIN_ICANN%2BSovereignty.doc|archive-date=24 May 2013|website=Internet and Public Policy Project|publisher=]}}</ref> | |||
| ===ICANN=== | |||
| {{details|ICANN}} | |||
| '''The Internet Corporation for Assigned Names and Numbers (ICANN)''' is the authority that coordinates the assignment of unique identifiers on the Internet, including domain names, Internet Protocol (IP) addresses, and protocol port and parameter numbers. A globally unified namespace (i.e., a system of names in which there is one and only one holder of each name) is essential for the Internet to function. ICANN is headquartered in Marina del Rey, California, but is overseen by an international board of directors drawn from across the Internet technical, business, academic, and non-commercial communities. The US government continues to have the primary role in approving changes to the root zone file that lies at the heart of the domain name system. Because the Internet is a distributed network comprising many voluntarily interconnected networks, the Internet, as such, has no governing body. ICANN's role in coordinating the assignment of unique identifiers distinguishes it as perhaps the only central coordinating body on the global Internet, but the scope of its authority extends only to the Internet's systems of domain names, ]es, and protocol port and parameter numbers. | |||
| ] (RIRs) were established for five regions of the world. The ] (AfriNIC) for ], the ] (ARIN) for ], the ] (APNIC) for ] and the ], the ] (LACNIC) for ] and the ] region, and the ] (RIPE NCC) for ], the ], and ] were delegated to assign IP address blocks and other Internet parameters to local registries, such as ]s, from a designated pool of addresses set aside for each region. | |||
| On ] ], the World Summit on the Information Society, held in ], established the Internet Governance Forum (IGF) to discuss Internet-related issues. | |||
| The ], an agency of the ], had final approval over changes to the ] until the IANA stewardship transition on 1 October 2016.<ref>{{cite book |last= Packard |first= Ashley |title= Digital Media Law |publisher= Wiley-Blackwell |year= 2010 |isbn= 978-1-4051-8169-3 |page= 65}}</ref><ref>{{cite web|url=https://www.theregister.co.uk/2005/07/01/bush_net_policy/|title=Bush administration annexes internet|archive-url=https://web.archive.org/web/20110919130539/https://www.theregister.co.uk/2005/07/01/bush_net_policy/|archive-date=19 September 2011|first=Kieren|last=McCarthy|website=The Register|date=1 July 2005}}</ref><ref>{{cite book |last= Mueller |first= Milton L. |title= Networks and States: The Global Politics of Internet Governance |publisher= MIT Press |year= 2010 |isbn= 978-0-262-01459-5 |page= 61}}</ref><ref>{{cite web|title=ICG Applauds Transfer of IANA Stewardship|url=https://www.ianacg.org/icg-applauds-transfer-of-iana-stewardship/|website=IANA Stewardship Transition Coordination Group (ICG)|access-date=8 June 2017|archive-url=https://web.archive.org/web/20170712190131/https://www.ianacg.org/icg-applauds-transfer-of-iana-stewardship/|archive-date=12 July 2017|url-status=live}}</ref> The ] (ISOC) was founded in 1992 with a mission to ''"assure the open development, evolution and use of the Internet for the benefit of all people throughout the world"''.<ref>{{cite web |url=http://www.isoc.org/internet/history/isochistory.shtml |title=Internet Society (ISOC) All About The Internet: History of the Internet |publisher=ISOC |access-date=19 December 2013 |archive-url=https://web.archive.org/web/20111127114016/http://www.isoc.org/internet/history/isochistory.shtml |archive-date=27 November 2011 }}</ref> Its members include individuals (anyone may join) as well as corporations, ], governments, and universities. Among other activities ISOC provides an administrative home for a number of less formally organized groups that are involved in developing and managing the Internet, including: the IETF, ] (IAB), ] (IESG), ] (IRTF), and ] (IRSG). On 16 November 2005, the United Nations-sponsored ] in ] established the ] (IGF) to discuss Internet-related issues. | |||
| ===Language=== | |||
| {{details|English on the Internet}} | |||
| The prevalent language for communication on the Internet is ]. This may be a result of the Internet's origins, as well as English's role as the ]. It may also be related to the poor capability of early computers to handle characters other than those in the basic ]. {{further|]}} | |||
| == Infrastructure == | |||
| After English (30% of Web visitors) the most-requested languages on the ] are ] 14%, ] 8%, ] 8%, ] 5%, and ] 5% (from , updated January 11, 2007). | |||
| {{See also|List of countries by number of Internet users|List of countries by Internet connection speeds}} | |||
| <!-- Note that the use of these copyright statistics is dependent on "giving due credit and establishing an active link back to www.internetworldstats.com", so please do not remove the citation above --> | |||
| ] | |||
| The communications infrastructure of the Internet consists of its hardware components and a system of software layers that control various aspects of the architecture. As with any computer network, the Internet physically consists of ]s, media (such as cabling and radio links), repeaters, modems etc. However, as an example of ], many of the network nodes are not necessarily Internet equipment per se. The internet packets are carried by other full-fledged networking protocols with the Internet acting as a homogeneous networking standard, running across ] hardware, with the packets guided to their destinations by IP routers. | |||
| === Service tiers === | |||
| By continent, 36% of the world's Internet users are based in ], 29% in ], and 21% in ] ( updated January 11, 2007). | |||
| ] | |||
| <!-- Note that the use of these copyright statistics is dependent on "giving due credit and establishing an active link back to www.internetworldstats.com", so please do not remove the citation above --> | |||
| ]s (ISPs) establish the worldwide connectivity between individual networks at various levels of scope. End-users who only access the Internet when needed to perform a function or obtain information, represent the bottom of the routing hierarchy. At the top of the routing hierarchy are the ]s, large telecommunication companies that exchange traffic directly with each other via very high speed ]s and governed by ] agreements. ] and lower-level networks buy ] from other providers to reach at least some parties on the global Internet, though they may also engage in peering. An ISP may use a single upstream provider for connectivity, or implement ] to achieve redundancy and load balancing. ]s are major traffic exchanges with physical connections to multiple ISPs. Large organizations, such as academic institutions, large enterprises, and governments, may perform the same function as ISPs, engaging in peering and purchasing transit on behalf of their internal networks. Research networks tend to interconnect with large subnetworks such as ], ], ], and the UK's ], ]. | |||
| The Internet's technologies have developed enough in recent years that good facilities are available for development and communication in most widely used languages. However, some glitches such as '']'' (incorrect display of foreign language characters, also known as ''krakozyabry'') still remain. | |||
| === |
=== Access === | ||
| Common methods of ] by users include dial-up with a computer ] via telephone circuits, ] over ], ] or copper wires, ], ], and ] technology (e.g. ], ]). The Internet may often be accessed from computers in libraries and ]s. ] exist in many public places such as airport halls and coffee shops. Various terms are used, such as ''public Internet kiosk'', ''public access terminal'', and ''Web ]''. Many hotels also have public terminals that are usually fee-based. These terminals are widely accessed for various usages, such as ticket booking, bank deposit, or ]. Wi-Fi provides wireless access to the Internet via local computer networks. ] providing such access include Wi-Fi cafés, where users need to bring their own wireless devices, such as a laptop or ]. These services may be free to all, free to customers only, or fee-based. | |||
| The Internet is allowing greater flexibility in working hours and location, especially with the spread of unmetered high-speed connections and ]s. | |||
| ] efforts have led to ]s. Commercial ] services that cover large areas are available in many cities, such as ], ], ], ], ], ], ] and ], where the Internet can then be accessed from places such as a park bench.<ref>{{cite web|last=Pasternak |first=Sean B. |url=https://www.bloomberg.com/apps/news?pid=10000082&sid=aQ0ZfhMa4XGQ |title=Toronto Hydro to Install Wireless Network in Downtown Toronto |publisher=Bloomberg |date=7 March 2006 |access-date=8 August 2011 |url-status=live |archive-url=https://web.archive.org/web/20060410104717/http://www.bloomberg.com/apps/news?pid=10000082&sid=aQ0ZfhMa4XGQ |archive-date=10 April 2006 }}</ref> Experiments have also been conducted with proprietary mobile wireless networks like ], various high-speed data services over cellular networks, and fixed wireless services. Modern ]s can also access the Internet through the cellular carrier network. For Web browsing, these devices provide applications such as ], ], and ] and a wide variety of other Internet software may be installed from ]s. Internet usage by mobile and tablet devices exceeded desktop worldwide for the first time in October 2016.<ref>{{cite web|quote=StatCounter Global Stats finds that mobile and tablet devices accounted for 51.3% of Internet usage worldwide in October compared to 48.7% by desktop.|url=http://gs.statcounter.com/press/mobile-and-tablet-internet-usage-exceeds-desktop-for-first-time-worldwide|title=Mobile and Tablet Internet Usage Exceeds Desktop for First Time Worldwide|archive-url=https://web.archive.org/web/20161101170640/http://gs.statcounter.com/press/mobile-and-tablet-internet-usage-exceeds-desktop-for-first-time-worldwide|archive-date=1 November 2016|website=StatCounter: Global Stats, Press Release|date=1 November 2016}}</ref> | |||
| ===The mobile Internet=== | |||
| The Internet can now be accessed virtually anywhere by numerous means. ]s, ]s, and ]s allow users to connect to the Internet from anywhere there is a cellular network supporting that device's technology. | |||
| ====Mobile communication==== | |||
| ==Common uses of the Internet== | |||
| ] The ] (ITU) estimated that, by the end of 2017, 48% of individual users regularly connect to the Internet, up from 34% in 2012.<ref>{{cite web|url=https://www.itu.int/en/ITU-D/Statistics/Pages/publications/wtid.aspx|title=World Telecommunication/ICT Indicators Database 2020 (24th Edition/July 2020)|archive-url=https://web.archive.org/web/20190421072228/https://www.itu.int/en/ITU-D/Statistics/Pages/publications/wtid.aspx|archive-date=21 April 2019|website=International Telecommunication Union (ITU)|date=2017a|quote=Key ICT indicators for developed and developing countries and the world (totals and penetration rates). World Telecommunication/ICT Indicators database}}</ref> ] connectivity has played an important role in expanding access in recent years, especially in ] and in Africa.<ref name="UNESCO">{{Cite book|url=http://unesdoc.unesco.org/images/0026/002610/261065e.pdf|title=World Trends in Freedom of Expression and Media Development Global Report 2017/2018|publisher=UNESCO|year=2018|access-date=29 May 2018|archive-date=20 September 2018|archive-url=https://web.archive.org/web/20180920181419/http://unesdoc.unesco.org/images/0026/002610/261065e.pdf|url-status=live}}</ref> The number of unique mobile cellular subscriptions increased from 3.9 billion in 2012 to 4.8 billion in 2016, two-thirds of the world's population, with more than half of subscriptions located in Asia and the Pacific. The number of subscriptions was predicted to rise to 5.7 billion users in 2020.<ref name="GSMA The Mobile Economy 2019">{{Cite web|date=11 March 2019|title=GSMA The Mobile Economy 2019 |url=https://www.gsma.com/r/mobileeconomy/|access-date=28 November 2020|archive-url=https://web.archive.org/web/20190311062226/https://www.gsma.com/r/mobileeconomy/|archive-date=11 March 2019}}</ref> {{as of|2018}}, 80% of the world's population were covered by a ] network.<ref name="GSMA The Mobile Economy 2019" /> The limits that users face on accessing information via mobile applications coincide with a broader process of ]. Fragmentation restricts access to media content and tends to affect the poorest users the most.<ref name="UNESCO" /> | |||
| ===E-mail=== | |||
| {{details|E-mail}} | |||
| The concept of sending electronic text messages between parties in a way analogous to mailing letters or memos predates the creation of the Internet. Even today it can be important to distinguish between Internet and internal e-mail systems. Internet e-mail may travel and be stored unencrypted on many other machines and networks out of both the sender's and the recipient's control. During this time it is quite possible for the content to be read and even tampered with by third parties, if anyone considers it important enough. Purely internal or intranet mail systems, where the information never leaves the corporate or organization's network and servers, is much more secure, although in any organization there will be IT and other personnel whose job may involve monitoring, or at least occasionally accessing, the email of other employees not addressed to them. ] (webmail) between parties on the same webmail system may not actually 'go' anywhere—it merely sits on the one server and is tagged in various ways so as to appear in one person's 'sent items' list and in one or more others' 'in boxes' or other 'folders' when viewed. | |||
| ], the practice of Internet service providers allowing users free connectivity to access specific content or applications without cost, has offered opportunities to surmount economic hurdles but has also been accused by its critics as creating a two-tiered Internet. To address the issues with zero-rating, an alternative model has emerged in the concept of 'equal rating' and is being tested in experiments by ] and ] in Africa. Equal rating prevents prioritization of one type of content and zero-rates all content up to a specified data cap. In a study published by ], 15 out of 19 countries researched in Latin America had some kind of hybrid or zero-rated product offered. Some countries in the region had a handful of plans to choose from (across all mobile network operators) while others, such as ], offered as many as 30 pre-paid and 34 post-paid plans.<ref>{{Cite web|last=Galpaya|first=Helani|date=12 April 2019|title=Zero-rating in Emerging Economies|url=https://www.cigionline.org/sites/default/files/documents/GCIG%20no.47_1.pdf|url-status=live|archive-url=https://web.archive.org/web/20190412062932/https://www.cigionline.org/sites/default/files/documents/GCIG%20no.47_1.pdf|archive-date=12 April 2019|access-date=28 November 2020|website=Global Commission on Internet Governance}}</ref> | |||
| E-mail attachments have greatly increased the usefulness of e-mail in many ways. When a file is attached to an email, a text representation of the attached data (which may itself be binary data) is actually appended to the e-mail text, later to be reconstituted into a 'file' on the recipient's machine for their use. See ] (Multipurpose Internet Mail Extensions) for details of how the problems involved in doing this have been overcome. | |||
| A study of eight countries in the ] found that zero-rated data plans exist in every country, although there is a great range in the frequency with which they are offered and actually used in each.<ref>{{Cite web|url=http://a4ai.org/the-impacts-of-emerging-mobiledata-services-in-developing-countries/|title=Alliance for Affordable Internet (A4AI). 2015. Models of Mobile Data Services in Developing Countries. Research brief. The Impacts of Emerging Mobile Data Services in Developing Countries.}}{{Dead link|date=September 2024 |bot=InternetArchiveBot |fix-attempted=yes }}</ref> The study looked at the top three to five carriers by market share in Bangladesh, Colombia, Ghana, India, Kenya, Nigeria, Peru and Philippines. Across the 181 plans examined, 13 percent were offering zero-rated services. Another study, covering ], ], ] and ], found ]'s Free Basics and ] to be the most commonly zero-rated content.<ref>{{Cite web|last1= Gillwald|first1= Alison|first2=Chenai|last2=Chair|first3=Ariel |last3=Futter |first4=Kweku|last4= Koranteng |first5=Fola |last5= Odufuwa|first6= John|last6= Walubengo|date=12 September 2016|title=Much Ado About Nothing? Zero Rating in the African Context|url=https://researchictafrica.net/publications/Other_publications/2016_RIA_Zero-Rating_Policy_Paper_-_Much_ado_about_nothing.pdf|access-date=28 November 2020|website=Researchictafrica|archive-date=16 December 2020|archive-url=https://web.archive.org/web/20201216150858/https://researchictafrica.net/publications/Other_publications/2016_RIA_Zero-Rating_Policy_Paper_-_Much_ado_about_nothing.pdf|url-status=live}}</ref> | |||
| ===The World Wide Web=== | |||
| {{details|World Wide Web}}], representing some of the ]s]] | |||
| == Internet Protocol Suite == | |||
| Through ]-driven ] using ]s, like ], millions worldwide have easy, instant access to a vast and diverse amount of online information. Compared to ]s and traditional ], the World Wide Web has enabled a sudden and extreme decentralization of information and data. | |||
| {{IP stack}} | |||
| The Internet standards describe a framework known as the ] (also called ], based on the first two components.) This is a suite of protocols that are ordered into a set of four conceptional ] by the scope of their operation, originally documented in {{IETF RFC|1122}} and {{IETF RFC|1123}}. At the top is the ], where communication is described in terms of the objects or data structures most appropriate for each application. For example, a web browser operates in a ] application model and exchanges information with the ] (HTTP) and an application-germane data structure, such as the ] (HTML). | |||
| Below this top layer, the ] connects applications on different hosts with a logical channel through the network. It provides this service with a variety of possible characteristics, such as ordered, reliable delivery (TCP), and an unreliable datagram service (UDP). | |||
| Many individuals and some companies and groups have adopted the use of "Web logs" or ]s, which are largely used as easily-updatable online diaries. Some commercial organizations encourage staff to fill them with advice on their areas of specialization in the hope that visitors will be impressed by the expert knowledge and free information, and be attracted to the corporation as a result. One example of this practice is ], whose product ] publish their personal blogs in order to pique the public's interest in their work. | |||
| Underlying these layers are the networking technologies that interconnect networks at their borders and exchange traffic across them. The ] implements the ] (IP) which enables computers to identify and locate each other by ] and route their traffic via intermediate (transit) networks.<ref name=rfc791>{{Cite IETF|rfc=791|title=Internet Protocol, DARPA Internet Program Protocol Specification|editor=]|date=September 1981|publisher=]}} Updated by {{IETF RFC|1349|2474|6864}}</ref> The Internet Protocol layer code is independent of the type of network that it is physically running over. | |||
| For more information on the distinction between the World Wide Web and the Internet itself — as in everyday use the two are sometimes confused — see ] where this is discussed in more detail. | |||
| At the bottom of the architecture is the ], which connects nodes on the same physical link, and contains protocols that do not require routers for traversal to other links. The protocol suite does not explicitly specify hardware methods to transfer bits, or protocols to manage such hardware, but assumes that appropriate technology is available. Examples of that technology include ], ], and ]. | |||
| ===Remote access=== | |||
| The Internet allows computer users to connect to other computers and information stores easily, wherever they may be across the world. They may do this with or without the use of security, authentication and encryption technologies, depending on the requirements. | |||
| ] | |||
| This is encouraging new ways of working from home, collaboration and information sharing in many industries. An ] sitting at home can ] the books of a company based in another country, on a ] situated in a third country that is remotely maintained by IT specialists in a fourth. These accounts could have been created by home-working book-keepers, in other remote locations, based on information e-mailed to them from offices all over the world. Some of these things were possible before the widespread use of the Internet, but the cost of private, ]s would have made many of them infeasible in practice. | |||
| ===Internet protocol=== | |||
| An office worker away from his desk, perhaps the other side of the world on a business trip or a holiday, can open a ] session into his normal office PC using a secure ] (VPN) connection via the Internet. This gives him complete access to all his normal files and data, including e-mail and other applications, while he is away. | |||
| ] | |||
| The most prominent component of the Internet model is the Internet Protocol (IP). IP enables internetworking and, in essence, establishes the Internet itself. Two versions of the Internet Protocol exist, ] and ]. | |||
| ====IP Addresses==== | |||
| This concept is also referred to by some network security people as the Virtual Private Nightmare, because it extends the secure perimeter of a corporate network into its employees' homes; this has been the source of some notable security breaches, but also provides security for the workers. | |||
| ] | |||
| For locating individual computers on the network, the Internet provides ]es. IP addresses are used by the Internet infrastructure to direct internet packets to their destinations. They consist of fixed-length numbers, which are found within the packet. IP addresses are generally assigned to equipment either automatically via ], or are configured. | |||
| However, the network also supports other addressing systems. Users generally enter ]s (e.g. "en.wikipedia.org") instead of IP addresses because they are easier to remember; they are converted by the ] (DNS) into IP addresses which are more efficient for routing purposes. | |||
| ===Collaboration=== | |||
| {{seealso|Collaborative software}} | |||
| ====IPv4==== | |||
| The low-cost and nearly instantaneous sharing of ideas, knowledge, and skills has made ] work dramatically easier. Not only can a group cheaply communicate and test, but the wide reach of the Internet allows such groups to easily form in the first place, even among niche interests. An example of this is the ] in software development which produced ] and ] from scratch and has taken over development of ] and ] (formerly known as ] and ]). | |||
| ] (IPv4) defines an IP address as a ] number.<ref name="rfc791"/> IPv4 is the initial version used on the first generation of the Internet and is still in dominant use. It was designed in 1981 to address up to ≈4.3 billion (10<sup>9</sup>) hosts. However, the explosive growth of the Internet has led to ], which entered its final stage in 2011,<ref>{{cite web|last=Huston |first=Geoff |title=IPv4 Address Report, daily generated |url=http://www.potaroo.net/tools/ipv4/index.html |access-date=20 May 2009 |url-status=live |archive-url=https://web.archive.org/web/20090401001902/http://www.potaroo.net/tools/ipv4/index.html |archive-date=1 April 2009 }}</ref> when the global IPv4 address allocation pool was exhausted. | |||
| ====IPv6==== | |||
| Internet 'chat', whether in the form of ] 'chat rooms' or channels, or via ] systems allow colleagues to stay in touch in a very convenient way when working at their computers during the day. Messages can be sent and viewed even more quickly and conveniently than via e-mail. Extension to these systems may allow files to be exchanged, 'whiteboard' drawings to be shared as well as voice and video contact between team members. | |||
| Because of the growth of the Internet and the ], a new version of IP ], was developed in the mid-1990s, which provides vastly larger addressing capabilities and more efficient routing of Internet traffic. IPv6 uses 128 bits for the IP address and was standardized in 1998.<ref name=rfc1883>{{Cite IETF|rfc=1883|title=Internet Protocol, Version 6 (IPv6) Specification|author-link1=Steve Deering|author1=S. Deering|author2=R. Hinden|date=December 1995|publisher=Network Working Group}}</ref><ref name=rfc2460>{{Cite IETF|rfc=2460|title=Internet Protocol, Version 6 (IPv6) Specification|author-link1=Steve Deering|author1=S. Deering|author2=R. Hinden|publisher=Network Working Group|date=December 1998}}</ref><ref name=rfc8200>{{Cite IETF|rfc=8200|title=Internet Protocol, Version 6 (IPv6) Specification|author-link1=Steve Deering|author1=S. Deering|author2=R. Hinden|publisher=]|date=July 2017}}</ref> ] has been ongoing since the mid-2000s and is currently in growing deployment around the world, since Internet address registries (]) began to urge all resource managers to plan rapid adoption and conversion.<ref>{{cite web |url=https://www.arin.net/knowledge/about_resources/ceo_letter.pdf |title=Notice of Internet Protocol version 4 (IPv4) Address Depletion |access-date=7 August 2009 |archive-url=https://web.archive.org/web/20100107095025/https://www.arin.net/knowledge/about_resources/ceo_letter.pdf |archive-date=7 January 2010 }}</ref> | |||
| IPv6 is not directly interoperable by design with IPv4. In essence, it establishes a parallel version of the Internet not directly accessible with IPv4 software. Thus, translation facilities must exist for internetworking or nodes must have duplicate networking software for both networks. Essentially all modern computer operating systems support both versions of the Internet Protocol. Network infrastructure, however, has been lagging in this development. Aside from the complex array of physical connections that make up its infrastructure, the Internet is facilitated by bi- or multi-lateral commercial contracts, e.g., ]s, and by technical specifications or protocols that describe the exchange of data over the network. Indeed, the Internet is defined by its interconnections and routing policies. | |||
| ] systems allow collaborating teams to work on shared sets of documents without either accidentally overwriting each other's work or having members wait until they get 'sent' documents to be able to add their thoughts and changes. | |||
| === |
====Subnetwork==== | ||
| ] | |||
| {{details|File sharing}} | |||
| A '']'' or ''subnet'' is a logical subdivision of an ].<ref name="rfc950">{{Cite IETF|rfc=950|publisher=]|author1=Jeffrey Mogul|author2=Jon Postel|author-link2=Jon Postel|title=Internet Standard Subnetting Procedure|date=August 1985}} Updated by RFC 6918.</ref>{{rp|1,16}} The practice of dividing a network into two or more networks is called ''subnetting''. Computers that belong to a subnet are addressed with an identical ]-group in their IP addresses. This results in the logical division of an IP address into two fields, the ''network number'' or ''routing prefix'' and the ''rest field'' or ''host identifier''. The ''rest field'' is an identifier for a specific ] or network interface. | |||
| The ''routing prefix'' may be expressed in ] (CIDR) notation written as the first address of a network, followed by a slash character (''/''), and ending with the bit-length of the prefix. For example, {{IPaddr|198.51.100.0|24}} is the prefix of the ] network starting at the given address, having 24 bits allocated for the network prefix, and the remaining 8 bits reserved for host addressing. Addresses in the range {{IPaddr|198.51.100.0}} to {{IPaddr|198.51.100.255}} belong to this network. The IPv6 address specification {{IPaddr|2001:db8::|32}} is a large address block with 2<sup>96</sup> addresses, having a 32-bit routing prefix. | |||
| A ] can be ] to customers, colleagues and friends as an ]. It can be uploaded to a ] or ] server for easy download by others. It can be put into a "shared location" or onto a ] for instant use by colleagues. The load of bulk downloads to many users can be eased by the use of "]" servers or ] networks. | |||
| In any of these cases, access to the file may be controlled by user ]; the transit of the file over the Internet may be obscured by ] and money may change hands before or after access to the file is given. The price can be paid by the remote charging of funds from, for example a ] whose details are also passed - hopefully fully encrypted - across the Internet. The origin and authenticity of the file received may be checked by ]s or by ] or other message digests. | |||
| For IPv4, a network may also be characterized by its ''subnet mask'' or ''netmask'', which is the ] that when applied by a ] operation to any IP address in the network, yields the routing prefix. Subnet masks are also expressed in ] like an address. For example, {{IPaddr|255.255.255.0}} is the subnet mask for the prefix {{IPaddr|198.51.100.0|24}}. | |||
| These simple features of the Internet, over a world-wide basis, are changing the basis for the production, sale, and distribution of anything that can be reduced to a computer file for transmission. This includes all manner of office documents, publications, software products, ], photography, video, animations, graphics and the other arts. This in turn is causing seismic shifts in each of the existing industry associations, such as the ] and ] in the United States, that previously controlled the production and distribution of these products in that country. | |||
| Traffic is exchanged between subnetworks through routers when the routing prefixes of the source address and the destination address differ. A router serves as a logical or physical boundary between the subnets. | |||
| ===Streaming media=== | |||
| Many existing radio and television broadcasters provide Internet 'feeds' of their live audio and video streams (for example, the ]). They may also allow time-shift viewing or listening such as Preview, Classic Clips and Listen Again features. These providers have been joined by a range of pure Internet 'broadcasters' who never had on-air licenses. This means that an Internet-connected device, such as a computer or something more specific, can be used to access on-line media in much the same way as was previously possible only with a ] or ] receiver. The range of material is much wider, from ] to highly specialized technical Web-casts. ] is a variation on this theme, where—usually audio—material is first downloaded in full and then may be played back on a computer or shifted to a ] to be listened to on the move. These techniques using simple equipment allow anybody, with little censorship or licensing control, to broadcast audio-visual material on a worldwide basis. | |||
| The benefits of subnetting an existing network vary with each deployment scenario. In the address allocation architecture of the Internet using CIDR and in large organizations, it is necessary to allocate address space efficiently. Subnetting may also enhance routing efficiency or have advantages in network management when subnetworks are administratively controlled by different entities in a larger organization. Subnets may be arranged logically in a hierarchical architecture, partitioning an organization's network address space into a tree-like routing structure. | |||
| ]s can be seen as an even lower-budget extension of this phenomenon. While some webcams can give full frame rate video, the picture is usually either small or updates slowly. Internet users can watch animals around an African waterhole, ships in the ], the traffic at a local roundabout or their own premises, live and in real time. Video ], ], and remote controllable webcams are also popular. Many uses can be found for personal webcams in and around the home, with and without two-way sound. | |||
| === |
====Routing==== | ||
| Computers and routers use ]s in their operating system to ] to reach a node on a different subnetwork. Routing tables are maintained by manual configuration or automatically by ]s. End-nodes typically use a ] that points toward an ISP providing transit, while ISP routers use the ] to establish the most efficient routing across the complex connections of the global Internet. The ] is the ] that serves as the forwarding host (router) to other networks when no other route specification matches the destination ] of a packet.<ref>{{Cite web|url=https://www.lifewire.com/how-to-find-your-default-gateway-ip-address-2626072|title=How to Find Your Default Gateway IP Address|last=Fisher|first=Tim|website=]|access-date=25 February 2019|archive-date=25 February 2019|archive-url=https://web.archive.org/web/20190225162425/https://www.lifewire.com/how-to-find-your-default-gateway-ip-address-2626072|url-status=live}}</ref><ref>{{cite web|url=https://www.techopedia.com/definition/2184/default-gateway|title=Default Gateway|archive-url=https://web.archive.org/web/20201026160616/https://www.techopedia.com/definition/2184/default-gateway|archive-date=26 October 2020|website=techopedia.com|date=30 June 2020 }}</ref> | |||
| {{details|VoIP}} | |||
| VoIP stands for Voice over IP, where ] refers to the Internet Protocol that underlies all Internet communication. This phenomenon began as an optional two-way voice extension to some of the ] systems that took off around the year 2000. In recent years many VoIP systems have become as easy to use and as convenient as a normal telephone. The benefit is that, as the Internet carries the actual voice traffic, VoIP can be free or cost much less than a normal telephone call, especially over long distances and especially for those with always-on ] or ] Internet connections. | |||
| ===IETF=== | |||
| Thus VoIP is maturing into a viable alternative to traditional telephones. Interoperability between different providers has improved and the ability to call or receive a call from a traditional telephone is available. Simple inexpensive VoIP modems are now available that eliminate the need for a PC. | |||
| While the hardware components in the Internet infrastructure can often be used to support other software systems, it is the design and the standardization process of the software that characterizes the Internet and provides the foundation for its scalability and success. The responsibility for the architectural design of the Internet software systems has been assumed by the ] (IETF).<ref>{{cite web|url=http://www.ietf.org/ |title=IETF Home Page |publisher=Ietf.org |access-date=20 June 2009 |url-status=live |archive-url=https://web.archive.org/web/20090618032558/http://www.ietf.org/ |archive-date=18 June 2009 }}</ref> The IETF conducts standard-setting work groups, open to any individual, about the various aspects of Internet architecture. The resulting contributions and standards are published as '']'' (RFC) documents on the IETF web site. The principal methods of networking that enable the Internet are contained in specially designated RFCs that constitute the ]s. Other less rigorous documents are simply informative, experimental, or historical, or document the best current practices (BCP) when implementing Internet technologies. | |||
| == Applications and services == | |||
| Voice quality can still vary from call to call but is often equal to and can even exceed that of traditional calls. | |||
| The Internet carries many ], most prominently the World Wide Web, including ], ], ]lications, ]s, ], ], and ] services. Most ] that provide these services are today hosted in ]s, and content is often accessed through high-performance ]s. | |||
| === World Wide Web === | |||
| Remaining problems for VoIP include ] dialing and reliability. Currently a few VoIP providers provide some 911 dialing but it is not universally available. Traditional phones are line powered and operate during a power failure, VoIP does not do so without a ] for the electronics. | |||
| {{Main|World Wide Web}} | |||
| ] was used by ] at ] and became the world's first ].]] | |||
| The World Wide Web is a global collection of ], ], ], applications, and other resources, logically interrelated by ]s and referenced with ]s (URIs), which provide a global system of named references. URIs symbolically identify services, ], databases, and the documents and resources that they can provide. ] (HTTP) is the main access protocol of the World Wide Web. ]s also use HTTP for communication between software systems for information transfer, sharing and exchanging business data and logistics and is one of many languages or protocols that can be used for communication on the Internet.<ref>{{cite web|url=http://www.webopedia.com/DidYouKnow/Internet/Web_vs_Internet.asp |title=The Difference Between the Internet and the World Wide Web |work=Webopedia |publisher=QuinStreet Inc. |date=24 June 2010 |access-date=1 May 2014 |url-status=live |archive-url=https://web.archive.org/web/20140502001005/http://www.webopedia.com/DidYouKnow/Internet/Web_vs_Internet.asp |archive-date=2 May 2014 }}</ref> | |||
| Most VoIP providers offer unlimited national calling but the direction in VoIP is clearly toward global coverage with unlimited minutes for a low monthly fee. | |||
| World Wide Web browser software, such as ]'s ]/], ], ], ]'s ], and ], enable users to navigate from one web page to another via the hyperlinks embedded in the documents. These documents may also contain any combination of ], including graphics, sounds, ], ], ] and interactive content that runs while the user is interacting with the page. ] can include animations, ], ] and scientific demonstrations. Through ]-driven ] using ] like ], ] and ], users worldwide have easy, instant access to a vast and diverse amount of online information. Compared to printed media, books, encyclopedias and traditional libraries, the World Wide Web has enabled the decentralization of information on a large scale. | |||
| VoIP has also become increasingly popular within the gaming world, as a form of communication between players. Popular gaming VoIP clients include ] and ], and there are others available also. | |||
| The Web has enabled individuals and organizations to ] ideas and information to a potentially large ] online at greatly reduced expense and time delay. Publishing a web page, a blog, or building a website involves little initial ] and many cost-free services are available. However, publishing and maintaining large, professional web sites with attractive, diverse and up-to-date information is still a difficult and expensive proposition. Many individuals and some companies and groups use ''web logs'' or blogs, which are largely used as easily being able to update online diaries. Some commercial organizations encourage ] to communicate advice in their areas of specialization in the hope that visitors will be impressed by the expert knowledge and free information and be attracted to the corporation as a result. | |||
| ==Censorship== | |||
| {{details|Internet censorship}} | |||
| ] on popular web pages can be lucrative, and ], which is the sale of products and services directly via the Web, continues to grow. Online advertising is a form of ] and advertising which uses the Internet to deliver ] marketing messages to consumers. It includes email marketing, ] (SEM), social media marketing, many types of ] (including ] advertising), and ]. In 2011, Internet advertising revenues in the United States surpassed those of ] and nearly exceeded those of ].<ref name="IAB2012">{{cite web |url = http://www.iab.net/media/file/IAB_Internet_Advertising_Revenue_Report_FY_2012_rev.pdf |title = IAB Internet advertising revenue report: 2012 full year results |date = April 2013 |publisher = PricewaterhouseCoopers, Internet Advertising Bureau |access-date = 12 June 2013 |archive-url = https://web.archive.org/web/20141004001439/http://www.iab.net/media/file/IAB_Internet_Advertising_Revenue_Report_FY_2012_rev.pdf |archive-date = 4 October 2014 }}</ref>{{rp|19}} Many common online advertising practices are controversial and increasingly subject to regulation. | |||
| Some governments, such as those of ], the ] and ], restrict what people in their countries can access on the Internet, especially political and religious content. This is accomplished through software that filters domains and content so that they may not be easily accessed or obtained without elaborate circumvention. | |||
| When the Web developed in the 1990s, a typical web page was stored in completed form on a web server, formatted in ], ready for transmission to a web browser in response to a request. Over time, the process of creating and serving web pages has become dynamic, creating a flexible design, layout, and content. Websites are often created using ] software with, initially, very little content. Contributors to these systems, who may be paid staff, members of an organization or the public, fill underlying databases with content using editing pages designed for that purpose while casual visitors view and read this content in HTML form. There may or may not be editorial, approval and security systems built into the process of taking newly entered content and making it available to the target visitors. | |||
| In ], ] and ], major Internet service providers have voluntarily (possibly to avoid such an arrangement being turned into law) agreed to restrict access to sites listed by police. While this list of forbidden URLs is only supposed to contain addresses of known child pornography sites, content of the list is secret. | |||
| === Communication === | |||
| Many countries have enacted laws making the possession or distribution of certain material, such as ], illegal, but do not use filtering software. | |||
| ] is an important communications service available via the Internet. The concept of sending electronic text messages between parties, analogous to mailing letters or memos, predates the creation of the Internet.<ref>{{cite journal|first=Ron|last=Brown|title=Fax invades the mail market|url=https://books.google.com/books?id=Ry64sjvOmLkC&pg=PA218|journal=New Scientist|volume=56|issue=817|date=October 26, 1972|pages=218–221}}</ref><ref>{{cite journal|first=Herbert P.|last=Luckett|title=What's News: Electronic-mail delivery gets started|url=https://books.google.com/books?id=cKSqa8u3EIoC&pg=PA85|journal=Popular Science|volume=202|issue=3|date=March 1973|page=85}}</ref> Pictures, documents, and other files are sent as ]s. Email messages can be ] to multiple ]es. | |||
| ] is a common communications service realized with the Internet. The name of the principal internetworking protocol, the Internet Protocol, lends its name to ] (VoIP). The idea began in the early 1990s with ]-like voice applications for personal computers. VoIP systems now dominate many markets and are as easy to use and as convenient as a traditional telephone. The benefit has been substantial cost savings over traditional telephone calls, especially over long distances. ], ], and ] networks provide ] in customer premises<ref name=EBSCOhost>{{cite journal|last=Booth|first=C|title=Chapter 2: IP Phones, Software VoIP, and Integrated and Mobile VoIP|journal=Library Technology Reports|year=2010|volume=46|issue=5|pages=11–19}}</ref> and inexpensive VoIP network adapters provide the connection for traditional analog telephone sets. The voice quality of VoIP often exceeds that of traditional calls. Remaining problems for VoIP include the situation that emergency services may not be universally available and that devices rely on a local power supply, while older traditional phones are powered from the local loop, and typically operate during a power failure. | |||
| There are many free and commercially available software programs with which a user can choose to block offensive Web sites on individual computers or networks, such as to limit a child's access to pornography or violence. See '']''. | |||
| === Data transfer === | |||
| ==Internet access== | |||
| ] is an example of transferring large amounts of data across the Internet. A ] can be emailed to customers, colleagues and friends as an attachment. It can be uploaded to a website or ] (FTP) server for easy download by others. It can be put into a "shared location" or onto a ] for instant use by colleagues. The load of bulk downloads to many users can be eased by the use of "]" servers or ] networks. In any of these cases, access to the file may be controlled by user ], the transit of the file over the Internet may be obscured by ], and money may change hands for access to the file. The price can be paid by the remote charging of funds from, for example, a credit card whose details are also passed—usually fully encrypted—across the Internet. The origin and authenticity of the file received may be checked by ]s or by ] or other message digests. These simple features of the Internet, over a worldwide basis, are changing the production, sale, and distribution of anything that can be reduced to a computer file for transmission. This includes all manner of print publications, software products, news, music, film, video, photography, graphics and the other arts. This in turn has caused seismic shifts in each of the existing industries that previously controlled the production and distribution of these products. | |||
| {{details|Internet access}} | |||
| {{wikibookspar||Online linux connect}} | |||
| Common methods of home access include ], landline ] (over coaxial cable, fibre optic or copper wires), ], ] and ]. | |||
| ] is the real-time delivery of digital media for immediate consumption or enjoyment by end users. Many radio and television broadcasters provide Internet feeds of their live audio and video productions. They may also allow time-shift viewing or listening such as Preview, Classic Clips and Listen Again features. These providers have been joined by a range of pure Internet "broadcasters" who never had on-air licenses. This means that an Internet-connected device, such as a computer or something more specific, can be used to access online media in much the same way as was previously possible only with a television or radio receiver. The range of available types of content is much wider, from specialized technical ]s to on-demand popular multimedia services. ]ing is a variation on this theme, where—usually audio—material is downloaded and played back on a computer or shifted to a ] to be listened to on the move. These techniques using simple equipment allow anybody, with little censorship or licensing control, to broadcast audio-visual material worldwide. Digital media streaming increases the demand for network bandwidth. For example, standard image quality needs 1 Mbit/s link speed for SD 480p, HD 720p quality requires 2.5 Mbit/s, and the top-of-the-line HDX quality needs 4.5 Mbit/s for 1080p.<ref>{{cite web |last=Morrison |first=Geoff |url=http://www.nbcnews.com/id/40241749 |title=What to know before buying a 'connected' TV – Technology & science – Tech and gadgets – Tech Holiday Guide |publisher=NBC News |date=18 November 2010 |access-date=8 August 2011 |archive-url=https://web.archive.org/web/20200212091603/http://www.nbcnews.com/id/40241749 |archive-date=12 February 2020 |url-status=dead }}</ref> | |||
| ]s to use the Internet include libraries and ]s, where computers with Internet connections are available. There are also Internet access points in many public places such as airport halls and coffee shops, in some cases just for brief use while standing. Various terms are used, such as "public Internet kiosk", "public access terminal", and "Web ]". Many hotels now also have public terminals, though these are usually fee-based. | |||
| ]s are a low-cost extension of this phenomenon. While some webcams can give full-frame-rate video, the picture either is usually small or updates slowly. Internet users can watch animals around an African waterhole, ships in the ], traffic at a local roundabout or monitor their own premises, live and in real time. Video ] and ] are also popular with many uses being found for personal webcams, with and without two-way sound. YouTube was founded on 15 February 2005 and is now the leading website for free streaming video with more than two billion users.<ref>{{Cite web|title=Press|url=https://www.youtube.com/about/press/|access-date=19 August 2020|website=YouTube|archive-date=11 November 2017|archive-url=https://web.archive.org/web/20171111094352/https://www.youtube.com/yt/about/press/|url-status=live}}</ref> It uses an HTML5 based web player by default to stream and show video files.<ref>{{Cite news|url=https://youtube-eng.googleblog.com/2015/01/youtube-now-defaults-to-html5_27.html|title=YouTube now defaults to HTML5|work=YouTube Engineering and Developers Blog|access-date=10 September 2018|language=en-US|archive-url=https://web.archive.org/web/20180910204225/https://youtube-eng.googleblog.com/2015/01/youtube-now-defaults-to-html5_27.html|archive-date=10 September 2018|url-status=live}}</ref> Registered users may upload an unlimited amount of video and build their own personal profile. ] claims that its users watch hundreds of millions, and upload hundreds of thousands of videos daily. | |||
| Wi-Fi provides wireless access to computer networks, and therefore can do so to the Internet itself. ] providing such access include ], where a would-be user needs to bring their own wireless-enabled devices such as a ] or ]. These services may be free to all, free to customers only, or fee-based. A hotspot need not be limited to a confined location. The whole campus or park, or even the entire city can be enabled. ] efforts have led to ]s. Commercial WiFi services covering large city areas are in place in ], ], ], ], ], ] and other cities, including ] by the end of 2006. The Internet can then be accessed from such places as a park bench.<ref>. Bloomberg.com. Retrieved 19-Mar-2006.</ref> | |||
| == Social impact == | |||
| Apart from Wi-Fi, there have been experiments with proprietary mobile wireless networks like ], various high-speed data services over cellular phone networks, and fixed wireless services. | |||
| The Internet has enabled new forms of social interaction, activities, and social associations. This phenomenon has given rise to the scholarly study of the ]. The early Internet left an impact on some ]s who used ]ism to write about it, such as describing the Internet as a "means to connect individuals in a vast invisible net over all the ]."<ref>{{Cite book |last1=Carlson |first1=Kathie |title=The Book of Symbols: Reflections on Archetypal Images |last2=Flanagin |first2=Michael N. |last3=Martin |first3=Kathleen |last4=Martin |first4=Mary E. |last5=Mendelsohn |first5=John |last6=Rodgers |first6=Priscilla Young |last7=Ronnberg |first7=Ami |last8=Salman |first8=Sherry |last9=Wesley |first9=Deborah A. |publisher=] |year=2010 |isbn=978-3-8365-1448-4 |editor-last=Arm |editor-first=Karen |location=Köln |page=518 |editor-last2=Ueda |editor-first2=Kako |editor-last3=Thulin |editor-first3=Anne |editor-last4=Langerak |editor-first4=Allison |editor-last5=Kiley |editor-first5=Timothy Gus |editor-last6=Wolff |editor-first6=Mary}}</ref> | |||
| === Users === | |||
| High-end mobile phones such as smartphones generally come with Internet access through the phone network. Web browsers such as ] are available on these advanced handsets, which can also run a wide variety of other Internet software. More mobile phones have Internet access than PCs, though this is not as widely used. An internet access provider and protocol matrix differentiates the methods used to get online. | |||
| {{See also|Global Internet usage|English in computing|Languages used on the Internet}} | |||
| ]. <!-- Using image for now due to logspam generated by this graph. See https://phabricator.wikimedia.org/T277903. Graph can be restored when underlying issue fixed. -->]] | |||
| ] per capita for selected countries]] | |||
| ].</small><ref> {{webarchive|url=https://web.archive.org/web/20150528031339/http://www.itu.int/en/ITU-D/Statistics/Documents/statistics/2014/ITU_Key_2005-2014_ICT_data.xls |date=28 May 2015 }}, Key ICT indicators for developed and developing countries and the world (totals and penetration rates), International Telecommunication Union (ITU). Retrieved 25 May 2015.</ref><ref> {{webarchive|url=https://web.archive.org/web/20150517033104/http://www.itu.int/ITU-D/ict/statistics/ict/ |date=17 May 2015 }}, ICT Data and Statistics (IDS), International Telecommunication Union (ITU). Retrieved 25 May 2015.</ref>]] | |||
| Between 2000 and 2009, the number of Internet users globally rose from 390 million to 1.9 billion.<ref> {{Webarchive|url=https://web.archive.org/web/20200509175322/https://www.itu.int/en/ITU-D/Statistics/Pages/stat/default.aspx |date=9 May 2020 }}, Market Information and Statistics, International Telecommunication Union</ref> By 2010, 22% of the world's population had access to computers with 1 billion ] searches every day, 300 million Internet users reading blogs, and 2 billion videos viewed daily on ].<ref>{{cite web|url=http://www.antaranews.com/en/news/71940/google-earth-demonstrates-how-technology-benefits-ris-civil-society-govt |title=Google Earth demonstrates how technology benefits RI's civil society, govt |publisher=Antara News |date=26 May 2011 |access-date=19 November 2012 |url-status=live |archive-url=https://web.archive.org/web/20121029074528/http://www.antaranews.com/en/news/71940/google-earth-demonstrates-how-technology-benefits-ris-civil-society-govt |archive-date=29 October 2012 }}</ref> In 2014 the world's Internet users surpassed 3 billion or 44 percent of world population, but two-thirds came from the richest countries, with 78 percent of Europeans using the Internet, followed by 57 percent of the Americas.<ref>{{cite web|url=https://www.engadget.com/2014/11/25/3-billion-internet-users/ |title=There are now 3 billion Internet users, mostly in rich countries |author=Steve Dent |date=25 November 2014 |access-date=25 November 2014 |url-status=live |archive-url=https://web.archive.org/web/20141128020032/http://www.engadget.com/2014/11/25/3-billion-internet-users/ |archive-date=28 November 2014 }}</ref> However, by 2018, Asia alone accounted for 51% of all Internet users, with 2.2 billion out of the 4.3 billion Internet users in the world. China's Internet users surpassed a major milestone in 2018, when the country's Internet regulatory authority, China Internet Network Information Centre, announced that China had 802 million users.<ref>{{cite web|url=https://cnnic.com.cn/IDR/ReportDownloads/201807/P020180711391069195909.pdf|website=Cnnic.com|title=Statistical Report on Internet Development in China|date=January 2018|archive-url=https://web.archive.org/web/20190412062935/https://cnnic.com.cn/IDR/ReportDownloads/201807/P020180711391069195909.pdf|archive-date=12 April 2019|url-status=live}}</ref> China was followed by India, with some 700 million users, with the United States third with 275 million users. However, in terms of penetration, in 2022 China had a 70% penetration rate compared to India's 60% and the United States's 90%.<ref>{{cite web|url=https://www.internetworldstats.com/stats.htm|title=World Internet Users Statistics and 2019 World Population Stats|website=internetworldstats.com|access-date=17 March 2019|archive-url=https://web.archive.org/web/20171124192836/http://www.internetworldstats.com/stats.htm|archive-date=24 November 2017|url-status=live}}</ref> In 2022, 54% of the world's Internet users were based in Asia, 14% in Europe, 7% in North America, 10% in Latin America and the ], 11% in Africa, 4% in the Middle East and 1% in Oceania.<ref name=inetstats>{{cite web|url=http://www.internetworldstats.com/stats.htm|title=World Internet Usage Statistics News and Population Stats|archive-url=https://web.archive.org/web/20170319013935/http://www.internetworldstats.com/stats.htm|archive-date=19 March 2017|date=30 June 2023|access-date=14 December 2023}}</ref><!-- Note that the use of these copyright statistics is dependent on "giving due credit and establishing an active link back to www.internetworldstats.com", so please do not remove the citation above --> In 2019, Kuwait, Qatar, the Falkland Islands, Bermuda and Iceland had the highest ], with 93% or more of the population with access.<ref name=ITU-IndividualsUsingTheInternet> {{webarchive|url=https://web.archive.org/web/20140209141641/http://www.itu.int/en/ITU-D/Statistics/Documents/statistics/2013/Individuals_Internet_2000-2012.xls |date=9 February 2014 }}, International Telecommunication Union (Geneva), June 2013. Retrieved 22 June 2013.</ref> As of 2022, it was estimated that 5.4 billion people use the Internet, more than two-thirds of the world's population.<ref>{{Cite web|url=https://www.internetworldstats.com/stats.htm|title=World Internet Users Statistics and 2023 World Population Stats|website=Internet World Stats |url-status=live |archive-url=https://web.archive.org/web/20240319110853/https://www.internetworldstats.com/stats.htm |archive-date= Mar 19, 2024 }}</ref> | |||
| ==Leisure== | |||
| The Internet has been a major source of leisure since before the World Wide Web, with entertaining social experiments such as ]s and ]s being conducted on university servers, and humor-related ] groups receiving much of the main traffic. Today, many ]s have sections devoted to games and funny videos; short cartoons in the form of ] are also popular. Over 6 million people use blogs or message boards as a means of communication and for the sharing of ideas. | |||
| The prevalent language for communication via the Internet has always been English. This may be a result of the origin of the Internet, as well as the language's role as a ] and as a ]. Early computer systems were limited to the characters in the ] (ASCII), a subset of the ]. After English (27%), the most requested languages on the World Wide Web are Chinese (25%), Spanish (8%), Japanese (5%), Portuguese and German (4% each), Arabic, French and Russian (3% each), and Korean (2%).<ref name="NIUBL-IWS" /><!-- Note that the use of these copyright statistics is dependent on "giving due credit and establishing an active link back to www.internetworldstats.com", so please do not remove the citation above --> The Internet's technologies have developed enough in recent years, especially in the use of ], that good facilities are available for development and communication in the world's widely used languages. However, some glitches such as '']'' (incorrect display of some languages' characters) still remain. | |||
| The pornography and ] industries have both taken full advantage of the World Wide Web, and often provide a significant source of advertising revenue for other Web sites. Although many governments have attempted to put restrictions on both industries' use of the Internet, this has generally failed to stop their widespread popularity. A song in the ] show '']'' is titled "]" and refers to the popularity of this aspect of the internet. | |||
| In a US study in 2005, the percentage of men using the Internet was very slightly ahead of the percentage of women, although this difference reversed in those under 30. Men logged on more often, spent more time online, and were more likely to be broadband users, whereas women tended to make more use of opportunities to communicate (such as email). Men were more likely to use the Internet to pay bills, participate in auctions, and for recreation such as downloading music and videos. Men and women were equally likely to use the Internet for shopping and banking.<ref>{{Cite web |last=Fallows |first=Deborah |date=2005-12-28 |title=How Women and Men Use the Internet |url=https://www.pewresearch.org/internet/2005/12/28/how-women-and-men-use-the-internet/ |website=Pew Research Center |language=en-US |url-status=live |archive-url= https://web.archive.org/web/20230608191432/https://www.pewresearch.org/internet/2005/12/28/how-women-and-men-use-the-internet/ |archive-date= Jun 8, 2023 }}</ref> In 2008, women significantly outnumbered men on most social networking services, such as Facebook and Myspace, although the ratios varied with age.<ref>{{cite web |url=http://business.rapleaf.com/company_press_2008_07_29.html |archive-url=https://web.archive.org/web/20090320211742/http://business.rapleaf.com/company_press_2008_07_29.html|archive-date=20 March 2009 |title=Rapleaf Study Reveals Gender and Age Data of Social Network Users |website=Rapleaf |date=July 29, 2008 }}</ref> Women watched more streaming content, whereas men downloaded more.<ref>{{cite web|url=http://www.entrepreneur.com/tradejournals/article/178175272.html |title=Women Ahead of Men in Online Tv, Dvr, Games, And Social Media. |publisher=Entrepreneur |date=1 May 2008 |access-date=8 August 2011 |archive-url=https://web.archive.org/web/20080916094836/http://www.entrepreneur.com/tradejournals/article/178175272.html |archive-date=16 September 2008 }}</ref> Men were more likely to blog. Among those who blog, men were more likely to have a professional blog, whereas women were more likely to have a personal blog.<ref>{{cite web |url=http://technorati.com/blogging/state-of-the-blogosphere/ |title= State of the Blogosphere |publisher=Technorati |access-date=8 August 2011 |archive-url=https://web.archive.org/web/20091002101707/http://technorati.com/blogging/state-of-the-blogosphere/ |archive-date=2 October 2009 }}</ref> | |||
| One main area of leisure on the Internet is ]. This form of leisure creates communities, bringing people of all ages and origins to enjoy the fast-paced world of multiplayer games. These range from ] to ]s, from ] to ]. This has revolutionized the way many people interact and spend their free time on the Internet. | |||
| Several neologisms exist that refer to Internet users: ] (as in "citizen of the net")<ref>{{cite book|last1=Seese|first1=Michael|isbn=978-1-60005-132-6|page=130|url=https://books.google.com/books?id=3noNR3IfSpgC&q=citizen+of+the+net&pg=PA130|title=Scrappy Information Security|access-date=5 June 2015|url-status=live|archive-url=https://web.archive.org/web/20170905151414/https://books.google.com/books?id=3noNR3IfSpgC&pg=PA130&lpg=PA130&dq=citizen+of+the+net|archive-date=5 September 2017|year=2009|publisher=Happy About }}</ref> refers to those ] in improving ], the Internet in general or surrounding political affairs and rights such as ],<ref>"", Dictionary.com. {{webarchive|url=https://web.archive.org/web/20120421223939/http://dictionary.reference.com/browse/netizen |date=21 April 2012 }}.</ref><ref name=Hauben>{{cite web|url=http://www.columbia.edu/~rh120/ch106.x01|title=The Net and Netizens|first=Michael|last=Hauben |date=June 5, 1996 |archive-url=https://web.archive.org/web/20110604214312/http://www.columbia.edu/~rh120/ch106.x01|archive-date=4 June 2011|publisher=Columbia University}}</ref> ] refers to operators or technically highly capable users of the Internet,<ref>{{cite web|url=http://www.isoc.org/internet/history/brief.shtml|title=A Brief History of the Internet |date=10 Dec 2003 |first1=B M. |last1=Leiner |first2=V G. |last2=Cerf |first3=D D. |last3=Clark |first4=R E. |last4=Kahn |first5=L |last5=Kleinrock |first6=D C. |last6=Lynch |first7=J |last7=Postel |first8=L G. |last8=Roberts |first9=S |last9=Wolff |archive-url=https://web.archive.org/web/20070604153304/http://www.isoc.org/internet/history/brief.shtml|archive-date=4 June 2007|website=the Internet Society}}</ref><ref>{{cite web|title= internaut |url=https://www.oxforddictionaries.com/definition/english/internaut |website=Oxford Dictionaries |access-date=6 June 2015 |archive-url=https://web.archive.org/web/20150613002443/https://www.oxforddictionaries.com/definition/english/internaut |archive-date=13 June 2015 }}</ref> ] refers to a person using the Internet in order to engage in society, politics, and government participation.<ref>{{cite book|first1=Karen|last1=Mossberger|title=Digital Citizenship – The Internet, Society and Participation|first2=Caroline J.|last2=Tolbert|first3=Ramona S.|last3=McNeal|year=2011|publisher=SPIE Press |isbn=978-0-8194-5606-9}}</ref> | |||
| While online gaming has been around since the 1970s, modern modes of online gaming began with services such as ] and ], which players of games would typically subscribe to. Non-subscribers were limited to certain types of gameplay or certain games. | |||
| <gallery mode="packed" heights="300px"> | |||
| Many use the Internet to access and download music, movies and other works for their enjoyment and relaxation. As discussed above, there are paid and unpaid sources for all of these, using centralized servers and distributed peer-to-peer technologies. Discretion is needed as some of these sources take more care over the original artists' rights and over copyright laws than others. | |||
| InternetUsersByLanguagePieChart.svg|<div style="text-align: center">''']'''<ref name=NIUBL-IWS>{{cite web|url=http://www.internetworldstats.com/stats7.htm|title=Top Ten Internet Languages |archive-url=https://web.archive.org/web/20120426122721/http://www.internetworldstats.com/stats7.htm|archive-date=26 April 2012|website=Internet World Stats, Miniwatts Marketing Group|date=18 March 2012 |access-date=22 April 2012}}</ref></div> | |||
| WebsitesByLanguagePieChart.svg|<div style="text-align: center">''']'''<ref name=UofCLBWApril2013>{{cite web|title=Usage of content languages for websites|url=http://w3techs.com/technologies/overview/content_language/all|work=W3Techs|access-date=26 April 2013|archive-url=https://archive.today/20120717235405/http://w3techs.com/technologies/overview/content_language/all|archive-date=17 July 2012|url-status=live}}</ref></div> | |||
| </gallery> | |||
| === Usage === | |||
| Many use the World Wide Web to access news, weather and sports reports, to plan and book holidays and to find out more about their random ideas and casual interests. | |||
| ]'''</div>Source: ].]] | |||
| {{Main|Global digital divide|Digital divide}} | |||
| ]<br />as a percentage of a country's population'''</div>Source: ].<ref name="FixedBroadbandITUDynamic2012"> {{Webarchive|url=https://web.archive.org/web/20190726064920/http://www.itu.int/ITU-D/ICTEYE/Reporting/DynamicReportWizard.aspx |date=26 July 2019 }}, Dynamic Report, ITU ITC EYE, ]. Retrieved 29 June 2013.</ref>]] | |||
| People use ], ] and email to make and stay in touch with friends worldwide, sometimes in the same way as some previously had ]s. Social networking Web sites like ] and many others like them also put and keep people in contact for their enjoyment. | |||
| ]<br />as a percentage of a country's population'''</div>Source: ].<ref name="MobleBroadbandITUDynamic2012"> {{Webarchive|url=https://web.archive.org/web/20190726064920/http://www.itu.int/ITU-D/ICTEYE/Reporting/DynamicReportWizard.aspx |date=26 July 2019 }}, Dynamic Report, ITU ITC EYE, ]. Retrieved 29 June 2013.</ref>]] | |||
| The Internet has seen a growing amount of ], where users can access their files, folders, and settings via the Internet. An example of an ] webos is ]. | |||
| The Internet allows greater flexibility in working hours and location, especially with the spread of unmetered high-speed connections. The Internet can be accessed almost anywhere by numerous means, including through ]s. Mobile phones, ]s, ]s and ]s allow users to connect to the Internet ]ly. Within the limitations imposed by small screens and other limited facilities of such pocket-sized devices, the services of the Internet, including email and the web, may be available. Service providers may restrict the services offered and mobile data charges may be significantly higher than other access methods. | |||
| Educational material at all levels from pre-school to post-doctoral is available from websites. Examples range from ], through school and high-school revision guides and ], to access to top-end scholarly literature through the likes of ]. For ], help with ] and other assignments, self-guided learning, whiling away spare time or just looking up more detail on an interesting fact, it has never been easier for people to access educational information at any level from anywhere. The Internet in general and the World Wide Web in particular are important enablers of both ] and ]. Further, the Internet allows researchers (especially those from the social and behavioral sciences) to conduct research remotely via virtual laboratories, with profound changes in reach and generalizability of findings as well as in communication between scientists and in the publication of results.<ref>{{cite book|last=Reips|first=U.-D.|year=2008|chapter=How Internet-mediated research changes science|url=http://www.cambridge.org/us/academic/subjects/psychology/social-psychology/psychological-aspects-cyberspace-theory-research-applications|title=Psychological aspects of cyberspace: Theory, research, applications|archive-url=https://web.archive.org/web/20140809235408/http://www.cambridge.org/us/academic/subjects/psychology/social-psychology/psychological-aspects-cyberspace-theory-research-applications|archive-date=9 August 2014|pages=268–294|location=Cambridge|publisher=Cambridge University Press|isbn=978-0-521-69464-3}}</ref> | |||
| ] has become a serious drain on corporate resources; the average UK employee spends 57 minutes a day surfing the Web at work, according to a study by ] . | |||
| The low cost and nearly instantaneous sharing of ideas, knowledge, and skills have made ] work dramatically easier, with the help of ]. Not only can a group cheaply communicate and share ideas but the wide reach of the Internet allows such groups more easily to form. An example of this is the ], which has produced, among other things, ], ], and ] (later forked into ]). Internet chat, whether using an ] chat room, an ] system, or a social networking service, allows colleagues to stay in touch in a very convenient way while working at their computers during the day. Messages can be exchanged even more quickly and conveniently than via email. These systems may allow files to be exchanged, drawings and images to be shared, or voice and video contact between team members. | |||
| ==Complex architecture == | |||
| Many computer scientists see the Internet as a "prime example of a large-scale, highly engineered, yet highly ]".<ref>Walter Willinger, Ramesh Govindan, Sugih Jamin, Vern Paxson, and Scott Shenker (2002). . In ''Proceedings of the National Academy of Sciences, 99'', suppl. 1, 2573 – 2580.</ref> The Internet is extremely heterogeneous. (For instance, data transfer rates and physical characteristics of connections vary widely.) The Internet exhibits ] that depend on its large-scale organization. For example, data transfer rates exhibit temporal self-similarity. Further adding to the complexity of the Internet is the ability of more than one computer to use the Internet through only one node, thus creating the possibility for a very deep and hierarchal based sub-network that can theoretically be extended infinitely (disregarding the programmatic limitations of the IPv4 protocol). | |||
| ] systems allow collaborating teams to work on shared sets of documents simultaneously without accidentally destroying each other's work. Business and project teams can share calendars as well as documents and other information. Such collaboration occurs in a wide variety of areas including scientific research, software development, conference planning, political activism and creative writing. Social and political collaboration is also becoming more widespread as both Internet access and ] spread. | |||
| {{section-stub}} | |||
| The Internet allows computer users to remotely access other computers and information stores easily from any access point. Access may be with ]; i.e., authentication and encryption technologies, depending on the requirements. This is encouraging new ways of ], collaboration and information sharing in many industries. An accountant sitting at home can ] the books of a company based in another country, on a server situated in a third country that is remotely maintained by IT specialists in a fourth. These accounts could have been created by home-working bookkeepers, in other remote locations, based on information emailed to them from offices all over the world. Some of these things were possible before the widespread use of the Internet, but the cost of private ]s would have made many of them infeasible in practice. An office worker away from their desk, perhaps on the other side of the world on a business trip or a holiday, can access their emails, access their data using ], or open a ] session into their office PC using a secure ] (VPN) connection on the Internet. This can give the worker complete access to all of their normal files and data, including email and other applications, while away from the office. It has been referred to among ]s as the Virtual Private Nightmare,<ref>{{cite web|title=The Virtual Private Nightmare: VPN |url=http://librenix.com/?inode=5013 |publisher=Librenix |access-date=21 July 2010 |date=4 August 2004 |url-status=live |archive-url=https://web.archive.org/web/20110515152637/http://librenix.com/?inode=5013 |archive-date=15 May 2011 }}</ref> because it extends the secure perimeter of a corporate network into remote locations and its employees' homes. By the late 2010s the Internet had been described as "the main source of scientific information "for the majority of the global North population".<ref>{{cite book|author1=Dariusz Jemielniak|url=https://books.google.com/books?id=yLDMDwAAQBAJ|title=Collaborative Society|author2=Aleksandra Przegalinska|year= 2020|publisher=MIT Press|isbn=978-0-262-35645-9|access-date=26 November 2020|archive-date=23 November 2020|archive-url=https://web.archive.org/web/20201123045652/https://books.google.com/books?id=yLDMDwAAQBAJ|url-status=live}}</ref>{{Rp|111}} | |||
| ==Marketing== | |||
| The Internet has also become a large market for companies; some of the biggest companies today have grown by taking advantage of the efficient nature of low-cost ] and ] through the Internet; also known as ]. It is the fastest way to spread information to a vast amount of people simultaneously. The Internet has also subsequently revolutionized ]—for example; a person can order a ] online and receive it in the ] within a couple of days, or ] it directly in some cases. The Internet has also greatly facilitated ] which allows a company to market a product to a specific person or a specific group of people more so than any other advertising medium. | |||
| === Social networking and entertainment === | |||
| Examples of personalized marketing include online communities such as ], ], ], and others which thousands of Internet users join to advertise themselves and make friends online. Many of these users are young teens and adolescents ranging from 13 to 25 years old. In turn, when they advertise themselves they advertise interests and hobbies, which online marketing companies can use as information as to what those users will purchase online, and advertise their own companies' products to those users. | |||
| {{See also|Social networking service#Social impact}} | |||
| Many people use the World Wide Web to access news, weather and sports reports, to plan and book vacations and to pursue their personal interests. People use ], messaging and email to make and stay in touch with friends worldwide, sometimes in the same way as some previously had ]s. Social networking services such as ] have created new ways to socialize and interact. Users of these sites are able to add a wide variety of information to pages, pursue common interests, and connect with others. It is also possible to find existing acquaintances, to allow communication among existing groups of people. Sites like ] foster commercial and business connections. YouTube and ] specialize in users' videos and photographs. Social networking services are also widely used by businesses and other organizations to promote their brands, to market to their customers and to encourage posts to "]". "Black hat" social media techniques are also employed by some organizations, such as ] accounts and ]. | |||
| A risk for both individuals' and organizations' writing posts (especially public posts) on social networking services is that especially foolish or controversial posts occasionally lead to an unexpected and possibly large-scale backlash on social media from other Internet users. This is also a risk in relation to controversial ''offline'' behavior, if it is widely made known. The nature of this backlash can range widely from counter-arguments and public mockery, through insults and ], to, in extreme cases, rape and death ]. The ] describes the tendency of many individuals to behave more stridently or offensively online than they would in person. A significant number of ] women have been the target of various forms of ] in response to posts they have made on social media, and Twitter in particular has been criticized in the past for not doing enough to aid victims of online abuse.<ref>{{Cite news|url=https://www.bbc.co.uk/news/technology-23477130 |title=Twitter 'report abuse' button calls after rape threats |last=Moore |first=Keith |date=27 July 2013 |work=] |access-date=7 December 2014 |url-status=live |archive-url=https://web.archive.org/web/20140904014545/http://www.bbc.co.uk/news/technology-23477130 |archive-date=4 September 2014 }}</ref> | |||
| A very ineffective way of advertising on the Internet is through ] an email with advertisements.{{or}} This is ineffective because, now, most email providers offer protection against email spam. Most spam messages are sent automatically to everybody in the email database of the company/person that is spamming. This way of advertising is almost like using ]. | |||
| For organizations, such a backlash can cause overall ], especially if reported by the media. However, this is not always the case, as any brand damage in the eyes of people with an opposing opinion to that presented by the organization could sometimes be outweighed by strengthening the brand in the eyes of others. Furthermore, if an organization or individual gives in to demands that others perceive as wrong-headed, that can then provoke a counter-backlash. | |||
| Adware is another ineffective way of advertising because most people simply close a popup window when it shows up, not bothering to read it.{{or}} | |||
| Some websites, such as ], have rules forbidding the posting of ] of individuals (also known as ]), due to concerns about such postings leading to mobs of large numbers of Internet users directing harassment at the specific individuals thereby identified. In particular, the Reddit rule forbidding the posting of personal information is widely understood to imply that all identifying photos and names must be ] in Facebook ] posted to Reddit. However, the interpretation of this rule in relation to public Twitter posts is less clear, and in any case, like-minded people online have many other ways they can use to direct each other's attention to public social media posts they disagree with. | |||
| {{further|] and ]}} | |||
| Children also face dangers online such as ] and ], who sometimes pose as children themselves. Children may also encounter material that they may find upsetting, or material that their parents consider to be not age-appropriate. Due to naivety, they may also post personal information about themselves online, which could put them or their families at risk unless warned not to do so. Many parents choose to enable ] or supervise their children's online activities in an attempt to protect their children from inappropriate material on the Internet. The most popular social networking services, such as Facebook and Twitter, commonly forbid users under the age of 13. However, these policies are typically trivial to circumvent by registering an account with a false birth date, and a significant number of children aged under 13 join such sites anyway. Social networking services for younger children, which claim to provide better levels of protection for children, also exist.<ref>{{cite web|url=http://mashable.com/2010/10/11/social-networks-children/ |title=5 Fun and Safe Social Networks for Children |date=11 October 2010 |access-date=7 December 2014 |website=] |last=Kessler |first=Sarah |url-status=live |archive-url=https://web.archive.org/web/20141220082237/http://mashable.com/2010/10/11/social-networks-children/ |archive-date=20 December 2014 }}</ref> | |||
| ==The name Internet== | |||
| {{details|Internet capitalization conventions}} | |||
| {{Wiktionarypar2|Internet|internet}} | |||
| ''Internet'' is traditionally written with a ] first letter, as it is a ]. The ], the ], the ], the ], and several other Internet-related organizations use this convention in their publications. | |||
| The Internet has been a major outlet for leisure activity since its inception, with entertaining ]s such as ]s and ]s being conducted on university servers, and humor-related ] groups receiving much traffic.<ref name="StudFiles">{{Cite web |title=Communication in our life |url=https://studfile.net/preview/2987063/ |access-date=2023-05-16 |website=StudFiles |language=ru}}</ref> Many ] have sections devoted to games and funny videos.<ref name="StudFiles" /> The ] and ] industries have taken advantage of the World Wide Web. Although many governments have attempted to restrict both industries' use of the Internet, in general, this has failed to stop their widespread popularity.<ref>{{cite web|url=https://abcnews.go.com/Business/SmallBiz/story?id=4151592|title=Do It Yourself! Amateur Porn Stars Make Bank|archive-url=https://web.archive.org/web/20111230075056/https://abcnews.go.com/Business/SmallBiz/story?id=4151592 |archive-date=30 December 2011|first=Russell|last=Goldman|website=ABC News|date=22 January 2008}}</ref> | |||
| Many newspapers, newswires, periodicals, and technical journals capitalize the term (''Internet''). Examples include '']'', the '']'', '']'', '']'', '']'', and '']''. | |||
| Another area of leisure activity on the Internet is ].<ref>{{cite web|url=http://internetgames.about.com/od/gamingnews/a/trendsdecade.htm|title=Top Online Game Trends of the Decade|archive-url=https://web.archive.org/web/20110929074221/http://internetgames.about.com/od/gamingnews/a/trendsdecade.htm |archive-date=29 September 2011|first=Dave|last=Spohn|website=About.com|date=15 December 2009}}</ref> This form of recreation creates communities, where people of all ages and origins enjoy the fast-paced world of multiplayer games. These range from ] to ]s, from ]s to ]. While online gaming has been around since the 1970s, modern modes of online gaming began with subscription services such as ] and ].<ref>{{cite web|url=http://internetgames.about.com/od/gamingnews/a/timeline.htm|title=Internet Game Timeline: 1963–2004|archive-url=https://web.archive.org/web/20060425091409/http://internetgames.about.com/od/gamingnews/a/timeline.htm|archive-date=25 April 2006|first=Dave|last=Spohn|website=About.com|date=2 June 2011}}</ref> Non-subscribers were limited to certain types of game play or certain games. Many people use the Internet to access and download music, movies and other works for their enjoyment and relaxation. Free and fee-based services exist for all of these activities, using centralized servers and distributed peer-to-peer technologies. Some of these sources exercise more care with respect to the original artists' copyrights than others. | |||
| Others assert that the first letter should be written in ] (''internet''). A significant number of publications use this form, including '']'', the ], the '']'', '']'', '']'', and '']''. As of 2005, many publications using ''internet'' appear to be located outside of ]—although one U.S. news source, '']'', has adopted the lower-case spelling. | |||
| Internet usage has been correlated to users' loneliness.<ref>{{cite web|author1=Carole Hughes |author2=Boston College |url=https://www2.bc.edu/~hughesc/abstract.html |archive-url=https://web.archive.org/web/20151107031736/https://www2.bc.edu/~hughesc/abstract.html |archive-date=7 November 2015 |title=The Relationship Between Internet Use and Loneliness Among College Students |publisher=Boston College |access-date=11 August 2011}}</ref> Lonely people tend to use the Internet as an outlet for their feelings and to share their stories with others, such as in the "]" thread. A 2017 book claimed that the Internet consolidates most aspects of human endeavor into singular arenas of which all of humanity are potential members and competitors, with fundamentally negative ] as a result. While successes in each field of activity are pervasively visible and trumpeted, they are reserved for an extremely thin sliver of the world's most exceptional, leaving everyone else behind. Whereas, before the Internet, expectations of success in any field were supported by reasonable probabilities of achievement at the village, suburb, city or even state level, the same expectations in the Internet world are virtually certain to bring disappointment today: there is always someone else, somewhere on the planet, who can do better and take the now one-and-only top spot.<ref>{{cite book|last=Barker|first=Eric|title=Barking Up the Wrong Tree|publisher=HarperCollins|date=2017|isbn=978-0-06-241604-9|pages=235–236}}</ref> | |||
| Historically, ''Internet'' and ''internet'' have had different meanings, with ''internet'' being a contraction of ''internetwork'' or ''internetworking'' and ''Internet'' referring to a matrix of networks using TCP/IP (Transmission Control Protocol/Internet Protocol) according to the book Where wizards stay up late. Under this distinction, the Internet is a particular internet, but the reverse does not apply. The distinction was evident in many RFCs, books, and articles from the 1980s and early 1990s (some of which, such as RFC 1918, refer to "internets" in the plural), but has recently fallen into disuse.{{Fact|date=February 2007}} Instead, the term ] is generally used for private networks. See also: ]. | |||
| ] is a new organizational form that involves, "highly dispersed small groups of practitioners that may remain largely anonymous within the larger social context and operate in relative secrecy, while still linked remotely to a larger network of believers who share a set of practices and texts, and often a common devotion to a particular leader. Overseas supporters provide funding and support; domestic practitioners distribute tracts, participate in acts of resistance, and share information on the internal situation with outsiders. Collectively, members and practitioners of such sects construct viable virtual communities of faith, exchanging personal testimonies and engaging in the collective study via email, online chat rooms, and web-based message boards."<ref>{{cite book|first=Patricia M.|last=Thornton|chapter=The New Cybersects: Resistance and Repression in the Reform era|editor1-first=Elizabeth |editor1-last=Perry|editor2-first=Mark|editor2-last=Selden|title=Chinese Society: Change, Conflict and Resistance|edition=2|location=London and New York|publisher=Routledge|year=2003|pages=149–150|isbn=978-0-415-56074-0}}</ref> In particular, the British government has raised concerns about the prospect of young British Muslims being indoctrinated into Islamic extremism by material on the Internet, being persuaded to join ] groups such as the so-called "]", and then potentially committing acts of terrorism on returning to Britain after fighting in Syria or Iraq. | |||
| Some people use the lower-case term as a medium (like radio or newspaper, e.g. ''I've found it in internet''), and capitalised (or first letter capitalised) as the global network. | |||
| ] can become a drain on corporate resources; the average UK employee spent 57 minutes a day surfing the Web while at work, according to a 2003 study by Peninsula Business Services.<ref>{{cite news|url=http://www.scotsman.com/news/net-abuse-hits-small-city-firms-1-892163 |title=Net abuse hits small city firms |work=The Scotsman |date=11 September 2003 |access-date=7 August 2009 |location=Edinburgh |url-status=live |archive-url=https://web.archive.org/web/20121020041820/http://www.scotsman.com/news/net-abuse-hits-small-city-firms-1-892163 |archive-date=20 October 2012 }}</ref> ] is excessive computer use that interferes with daily life. ] believes that Internet use has other ], for instance improving skills of scan-reading and ] with the deep thinking that leads to true creativity.<ref>{{cite book|url=https://archive.org/details/shallowswhatinte0000carr/page/276|title=The Shallows: What the Internet Is Doing to Our Brains|first=Nicholas G.|last=Carr|author-link=Nicholas G. Carr|publisher=W.W. Norton|year=2010|page=|isbn=978-0-393-07222-8}}</ref> | |||
| ==Significant Internet events== | |||
| ===Malfunctions and attacks=== | |||
| *] — ] ] | |||
| *Predicted ] - ] ] | |||
| *UUNet/Worldcom backbone difficulties — ] ] | |||
| *] — ] ] | |||
| *] — ] ] | |||
| *] | |||
| === Electronic business === | |||
| ==See also== | |||
| ] (''e-business'') encompasses business processes spanning the entire ]: purchasing, ], ], ], ] service, and business relationship. ] seeks to add revenue streams using the Internet to build and enhance relationships with clients and partners. According to ], the size of worldwide e-commerce, when global business-to-business and -consumer transactions are combined, equate to $16 trillion for 2013. A report by Oxford Economics added those two together to estimate the total size of the ] at $20.4 trillion, equivalent to roughly 13.8% of global sales.<ref>{{cite web|url=http://www.myclouddoor.com/web/documents/The%20New%20Digital%20Economy.pdf|title=The New Digital Economy: How it will transform business|archive-url=https://web.archive.org/web/20140706101452/http://www.myclouddoor.com/web/documents/The%20New%20Digital%20Economy.pdf |archive-date=6 July 2014|website=Oxford Economics|date=2 July 2011}}</ref> | |||
| {{sisterlinks|Internet}} | |||
| :''Main lists: ] and ]'' | |||
| While much has been written of the economic advantages of ], there is also evidence that some aspects of the Internet such as maps and location-aware services may serve to reinforce ] and the ].<ref>{{cite web |title=How the Internet Reinforces Inequality in the Real World |work=The Atlantic |author=Badger, Emily |date=6 February 2013 |access-date=13 February 2013 |url=http://www.theatlanticcities.com/technology/2013/02/how-internet-reinforces-inequality-real-world/4602/ |archive-url=https://web.archive.org/web/20130211095334/http://www.theatlanticcities.com/technology/2013/02/how-internet-reinforces-inequality-real-world/4602/ |archive-date=11 February 2013 }}</ref> Electronic commerce may be responsible for ] and the decline of ], ] businesses resulting in increases in ].<ref>{{cite web|url=https://www.zdnet.com/article/e-commerce-will-make-the-shopping-mall-a-retail-wasteland/|title=E-commerce will make the shopping mall a retail wasteland|archive-url=https://web.archive.org/web/20130219011301/http://www.zdnet.com/e-commerce-will-make-the-shopping-mall-a-retail-wasteland-7000009960/|archive-date=19 February 2013|website=ZDNet|url-status=live|date=17 January 2013}}</ref><ref>{{cite web|url=http://www.comscore.com/Insights/Press_Releases/2012/12/Free_Shipping_Day_Promotion_Spurs_Late-Season_Online_Spending_Surge|title='Free Shipping Day' Promotion Spurs Late-Season Online Spending Surge, Improving Season-to-Date Growth Rate to 16 Percent vs. Year Ago|archive-url=https://web.archive.org/web/20130128191411/http://www.comscore.com/Insights/Press_Releases/2012/12/Free_Shipping_Day_Promotion_Spurs_Late-Season_Online_Spending_Surge |archive-date=28 January 2013|website=Comscore|date=23 December 2012}}</ref><ref>{{cite web|url=http://www.theatlanticcities.com/jobs-and-economy/2012/12/death-american-shopping-mall/4252/|title=The Death of the American Shopping Mall|archive-url=https://web.archive.org/web/20130215044619/http://www.theatlanticcities.com/jobs-and-economy/2012/12/death-american-shopping-mall/4252/ |archive-date=15 February 2013|website=The Atlantic – Cities|date=26 December 2012}}</ref> | |||
| ===Major aspects and issues=== | |||
| *] | |||
| *] | |||
| *] | |||
| *] | |||
| Author ], a long-time critic of the social transformations caused by the Internet, has focused on the economic effects of consolidation from Internet businesses. Keen cites a 2013 ] report saying brick-and-mortar retailers employ 47 people for every $10 million in sales while Amazon employs only 14. Similarly, the 700-employee room rental start-up ] was valued at $10 billion in 2014, about half as much as ], which employs 152,000 people. At that time, ] employed 1,000 full-time employees and was valued at $18.2 billion, about the same valuation as ] and ] combined, which together employed almost 60,000 people.<ref>{{cite news| last1=Harris |first1=Michael |title=Book review: 'The Internet Is Not the Answer' by Andrew Keen |url=https://www.washingtonpost.com/opinions/book-review-the-internet-is-not-the-answer-by-andrew-keen/2015/01/02/8627999a-7973-11e4-9a27-6fdbc612bff8_story.html |access-date=25 January 2015 |newspaper=The Washington Post|date=2 January 2015 |url-status=live |archive-url=https://web.archive.org/web/20150120000258/https://www.washingtonpost.com/opinions/book-review-the-internet-is-not-the-answer-by-andrew-keen/2015/01/02/8627999a-7973-11e4-9a27-6fdbc612bff8_story.html |archive-date=20 January 2015 }}</ref> | |||
| ===Functions=== | |||
| *] | |||
| *] | |||
| *] | |||
| *] | |||
| *] | |||
| *] | |||
| === |
===Remote work=== | ||
| ] is facilitated by tools such as ], ], ], ], and VoIP so that work may be performed from any location, most conveniently the worker's home. It can be efficient and useful for companies as it allows workers to communicate over long distances, saving significant amounts of travel time and cost. More workers have adequate bandwidth at home to use these tools to link their home to their corporate ] and internal communication networks. | |||
| *] (HTTP) | |||
| *] (ISP) | |||
| *] | |||
| === Collaborative publishing === | |||
| ===Regulatory bodies=== | |||
| ]s have also been used in the academic community for sharing and dissemination of information across institutional and international boundaries.<ref>{{Cite book|url=http://portal.acm.org/citation.cfm?id=1142215.1142259|title=New Interfaces For Musical Expression|isbn=978-2-84426-314-8|author1=MM Wanderley |author2=D Birnbaum |author3=J Malloch |year=2006|publisher=IRCAM – Centre Pompidou|page=180}}</ref> In those settings, they have been found useful for collaboration on ], ], departmental documentation, and committee work.<ref>{{Cite journal|title=Putting Wikis to Work in Libraries|author=Nancy T. Lombardo|s2cid=11552140|volume=27|issue=2|date=June 2008|journal=Medical Reference Services Quarterly|pages=129–145|doi=10.1080/02763860802114223|pmid=18844087}}</ref> The ] uses a wiki to allow the public to collaborate on finding ] relevant to examination of pending patent applications. ], New York has used a wiki to allow citizens to collaborate on the design and planning of a local park.<ref name="Noveck">{{cite journal|title=Misplaced Pages and the Future of Legal Education |author=Noveck, Beth Simone |journal=Journal of Legal Education |volume=57 |issue=1 |url=http://heinonline.org/HOL/LandingPage?collection=journals&handle=hein.journals/jled57&div=8&id=&page= |date=March 2007 |url-status=live |archive-url=https://web.archive.org/web/20140703005842/http://heinonline.org/HOL/LandingPage?collection=journals&handle=hein.journals%2Fjled57&div=8&id=&page= |archive-date=3 July 2014 }}{{subscription required}}</ref> The ] has the largest user base among wikis on the World Wide Web<ref>{{Cite web|url=http://s23.org/wikistats/largest_html.php?sort=users_desc&th=8000&lines=500 |title=WikiStats by S23 |access-date=7 April 2007 |publisher=S23Wiki |date=3 April 2008 |archive-url=https://web.archive.org/web/20140825164715/http://s23.org/wikistats/largest_html.php?sort=users_desc&th=8000&lines=500 |archive-date=25 August 2014}}</ref> and ranks in the top 10 among all sites in terms of traffic.<ref>{{Cite web |url=http://www.alexa.com/topsites |title=Alexa Web Search – Top 500 |access-date=2 March 2015 |publisher=] |url-status=live |archive-url=https://web.archive.org/web/20150302173920/http://www.alexa.com/topsites |archive-date=2 March 2015 }}</ref> | |||
| *] (IANA) | |||
| *] (]) | |||
| === Politics and political revolutions === | |||
| ==References== | |||
| {{See also|Internet censorship|Mass surveillance|Social media use in politics}} | |||
| ===Citations and notes=== | |||
| ] during the ], informing the ] public that 'like' or 'share' activities on social media could result in imprisonment (observed 30 June 2014)]] | |||
| <!--This article uses the Cite.php citation mechanism. If you would like more information on how to add references to this article, please see http://meta.wikimedia.org/Cite/Cite.php --> | |||
| The Internet has achieved new relevance as a political tool. The presidential campaign of ] in 2004 in the United States was notable for its success in soliciting donation via the Internet. Many political groups use the Internet to achieve a new method of organizing for carrying out their mission, having given rise to ].<ref name=cascading>{{cite web|url=http://www.miller-mccune.com/politics/the-cascading-effects-of-the-arab-spring-28575/ |archive-url=https://web.archive.org/web/20110227051329/http://www.miller-mccune.com/politics/the-cascading-effects-of-the-arab-spring-28575/ |archive-date=27 February 2011 |title=The Arab Uprising's Cascading Effects |publisher=Miller-mccune.com |date=23 February 2011 |access-date=27 February 2011}}</ref><ref>{{cite web|url=http://www.etd.ceu.hu/2011/chokoshvili_davit.pdf|title=The Role of the Internet in Democratic Transition: Case Study of the Arab Spring|archive-url=https://web.archive.org/web/20120705155248/http://www.etd.ceu.hu/2011/chokoshvili_davit.pdf|archive-date=2012-07-05|date=5 July 2012 }}, Davit Chokoshvili, Master's Thesis, June 2011</ref> '']'' suggested that ] websites, such as Facebook and Twitter, helped people organize the political revolutions in Egypt, by helping activists organize protests, communicate grievances, and disseminate information.<ref>{{cite news|url=https://www.nytimes.com/2011/02/10/world/middleeast/10youth.html |work=The New York Times |first=David D. |last=Kirkpatrick |title=Wired and Shrewd, Young Egyptians Guide Revolt |date=9 February 2011 |url-status=live |archive-url=https://web.archive.org/web/20170129225903/http://www.nytimes.com/2011/02/10/world/middleeast/10youth.html |archive-date=29 January 2017 }}</ref> | |||
| Many have understood the Internet as an extension of the ] notion of the '']'', observing how network communication technologies provide something like a global civic forum. However, incidents of politically motivated ] have now been recorded in many countries, including western democracies.<ref name="DeibertPalfreyRohozinski2008">{{cite book | author1 = Ronald Deibert | author2 = John Palfrey | author3 = Rafal Rohozinski | author4 = Jonathan Zittrain |year=2008 | title = Access Denied: The Practice and Policy of Global Internet Filtering | publisher = MIT Press | pages = | isbn = 978-0-262-29072-2 | url = https://books.google.com/books?id=l6ry0NeJ1N8C}}</ref><ref name="DiamondPlattner2012">{{cite book | author1 = Larry Diamond | author2 = Marc F. Plattner | year= 2012 | title = Liberation Technology: Social Media and the Struggle for Democracy | publisher = JHU Press | pages = | isbn = 978-1-4214-0568-1 | url = https://books.google.com/books?id=xhwFEF9HD2sC}}</ref> | |||
| ] is the use of ] devices, such as the Internet, to provide ]s to citizens and other persons in a country or region. E-government offers opportunities for more direct and convenient citizen access to government<ref>{{Cite journal |last1=Manoharan |first1=Aroon P. |last2=Melitski |first2=James |last3=Holzer |first3=Marc |date=2022-01-20 |title=Digital Governance: An Assessment of Performance and Best Practices |journal=Public Organization Review |volume=23 |issue=1 |pages=265–283 |language=en |doi=10.1007/s11115-021-00584-8 |issn=1573-7098 |pmc=8769785}}</ref> and for government provision of services directly to citizens.<ref>{{Cite book|title=Encyclopedia of the City|last=Caves|first=R. W.|publisher=Routledge|year=2004|page=180}}</ref> | |||
| === Philanthropy === | |||
| The spread of low-cost Internet access in developing countries has opened up new possibilities for ] charities, which allow individuals to contribute small amounts to charitable projects for other individuals. Websites, such as ] and ], allow small-scale donors to direct funds to individual projects of their choice. A popular twist on Internet-based philanthropy is the use of ] for charitable purposes. ] pioneered this concept in 2005, offering the first web-based service to publish individual loan profiles for funding. Kiva raises funds for local intermediary ] organizations that post stories and updates on behalf of the borrowers. Lenders can contribute as little as $25 to loans of their choice and receive their money back as borrowers repay. Kiva falls short of being a pure peer-to-peer charity, in that loans are disbursed before being funded by lenders and borrowers do not communicate with lenders themselves.<ref>{{cite web|url=http://blogs.cgdev.org/open_book/2009/10/kiva-is-not-quite-what-it-seems.php|title=Kiva Is Not Quite What It Seems|archive-url=https://web.archive.org/web/20100210045011/http://blogs.cgdev.org/open_book/2009/10/kiva-is-not-quite-what-it-seems.php|archive-date=10 February 2010|first=David|last=Roodman|website=Center for Global Development|date=2 October 2009|access-date=16 January 2010}}</ref><ref>{{cite news|last=Strom |first=Stephanie |title=Confusion on Where Money Lent via Kiva Goes |work=The New York Times |page=6 |date=9 November 2009 |url=https://www.nytimes.com/2009/11/09/business/global/09kiva.html |url-status=live |archive-url=https://web.archive.org/web/20170129225155/http://www.nytimes.com/2009/11/09/business/global/09kiva.html |archive-date=29 January 2017 }}</ref> | |||
| == Security == | |||
| {{Main|Internet security}} | |||
| Internet resources, hardware, and software components are the target of criminal or malicious attempts to gain unauthorized control to cause interruptions, commit fraud, engage in blackmail or access private information.<ref>{{cite book|last=Gralla|first=Preston|title=How the Internet Works|year=2007|publisher=Que Pub|location=Indianapolis|isbn=978-0-7897-2132-7|url-access=registration|url=https://archive.org/details/howinternetworks00gral}}</ref> | |||
| ===Malware=== | |||
| ] is malicious software used and distributed via the Internet. It includes ]es which are copied with the help of humans, ]s which copy themselves automatically, software for ]s, ], ]s, and ] that reports on the activity and typing of users. Usually, these activities constitute ]. Defense theorists have also speculated about the possibilities of ] using ] using similar methods on a large scale.<ref>{{Cite web|last=Andriole|first=Steve|title=Cyberwarfare Will Explode In 2020 (Because It's Cheap, Easy And Effective)|url=https://www.forbes.com/sites/steveandriole/2020/01/14/cyberwarfare-will-explode-in-2020-because-its-cheap-easy--effective/|access-date=2021-05-18|website=Forbes|language=en}}</ref> | |||
| Malware poses serious problems to individuals and businesses on the Internet.<ref>{{Cite journal |last1=Kim |first1=Jin-Young |last2=Bu |first2=Seok-Jun |last3=Cho |first3=Sung-Bae |date=2018-09-01 |title=Zero-day malware detection using transferred generative adversarial networks based on deep autoencoders |url=https://www.sciencedirect.com/science/article/pii/S0020025518303475 |journal=Information Sciences |language=en |volume=460–461 |pages=83–102 |doi=10.1016/j.ins.2018.04.092 |issn=0020-0255 |s2cid=51882216 |access-date=2 December 2021}}</ref><ref>{{Cite journal |last1=Razak |first1=Mohd Faizal Ab |last2=Anuar |first2=Nor Badrul |last3=Salleh |first3=Rosli |last4=Firdaus |first4=Ahmad |date=2016-11-01 |title=The rise of "malware": Bibliometric analysis of malware study |url=https://linkinghub.elsevier.com/retrieve/pii/S1084804516301904 |journal=Journal of Network and Computer Applications |language=en |volume=75 |pages=58–76 |doi=10.1016/j.jnca.2016.08.022 |access-date=30 April 2022}}</ref> According to ]'s 2018 Internet Security Threat Report (ISTR), malware variants number has increased to 669,947,865 in 2017, which is twice as many malware variants as in 2016.<ref>{{Cite journal |last1=Xiao |first1=Fei |last2=Sun |first2=Yi |last3=Du |first3=Donggao |last4=Li |first4=Xuelei |last5=Luo |first5=Min |date=2020-03-21 |title=A Novel Malware Classification Method Based on Crucial Behavior |journal=Mathematical Problems in Engineering |volume=2020 |pages=1–12 |doi=10.1155/2020/6804290 |issn=1024-123X |doi-access=free}}</ref> ], which includes malware attacks as well as other crimes committed by computer, was predicted to cost the world economy US$6 trillion in 2021, and is increasing at a rate of 15% per year.<ref name="Morgan">{{cite web |last=Morgan |first=Steve |date=13 November 2020 |title=Cybercrime To Cost The World $10.5 Trillion Annually By 2025 |url=https://cybersecurityventures.com/hackerpocalypse-cybercrime-report-2016/ |url-status=live |archive-url=https://web.archive.org/web/20220305072352/https://cybersecurityventures.com/hackerpocalypse-cybercrime-report-2016/ |archive-date=5 March 2022 |access-date=5 March 2022 |work=Cybercrime magazine website |publisher=Cybersecurity ventures |format= |doi=}}</ref> Since 2021, malware has been designed to target computer systems that run critical infrastructure such as the ].<ref>{{Cite journal |last1=Eder-Neuhauser |first1=Peter |last2=Zseby |first2=Tanja |last3=Fabini |first3=Joachim |date=2019-06-01 |title=Malware propagation in smart grid networks: metrics, simulation and comparison of three malware types |journal=Journal of Computer Virology and Hacking Techniques |language=en |volume=15 |issue=2 |pages=109–125 |doi=10.1007/s11416-018-0325-y |issn=2263-8733 |s2cid=255164530 |doi-access=free}}</ref><ref>{{Cite journal |last1=Razak |first1=Mohd Faizal Ab |last2=Anuar |first2=Nor Badrul |last3=Salleh |first3=Rosli |last4=Firdaus |first4=Ahmad |date=2016-11-01 |title=The rise of "malware": Bibliometric analysis of malware study |url=https://www.sciencedirect.com/science/article/pii/S1084804516301904 |journal=Journal of Network and Computer Applications |volume=75 |pages=58–76 |doi=10.1016/j.jnca.2016.08.022 |issn=1084-8045}}</ref> Malware can be designed to evade antivirus software detection algorithms.<ref>{{Cite web |last=Spring |first=Tom |date=2023-06-12 |title=Obfuscation tool 'BatCloak' can evade 80% of AV engines |url=https://www.scmagazine.com/news/obfuscation-batcloak-80-percent-av-engines |access-date=2023-12-21 |website=SC Media |language=en}}</ref><ref>{{Cite web |last=Nam |first=Nguyen |date=2023-01-10 |title=Kiểm tra ip |url=http://kiemtraip.vn |access-date=2023-12-21 |language=en-US}}</ref><ref>{{Cite web |last=Amos |first=Zac |title=How Ransomware Can Evade Antivirus Software |url=https://gca.isa.org/blog/how-ransomware-can-evade-antivirus-software |access-date=2023-12-21 |website=gca.isa.org |language=en}}</ref> | |||
| === Surveillance === | |||
| {{Main|Computer and network surveillance}} | |||
| {{See also|Signals intelligence|Mass surveillance}} | |||
| The vast majority of computer surveillance involves the monitoring of ] and ] on the Internet.<ref name="sciam-internet">{{cite news|url=http://www.sciam.com/article.cfm?id=internet-eavesdropping|title=Internet Eavesdropping: A Brave New World of Wiretapping|last=Diffie|first=Whitfield|author2=Susan Landau|date=August 2008|work=Scientific American|access-date=13 March 2009|archive-url=https://web.archive.org/web/20081113212137/http://www.sciam.com/article.cfm?id=internet-eavesdropping|archive-date=13 November 2008|url-status=live}}</ref> In the United States for example, under the ], all phone calls and broadband Internet traffic (emails, web traffic, instant messaging, etc.) are required to be available for unimpeded real-time monitoring by Federal law enforcement agencies.<ref name="eff-calea-archive">{{cite web|url=http://w2.eff.org/Privacy/Surveillance/CALEA/?f=archive.html |archive-url=https://web.archive.org/web/20081025074518/http://w2.eff.org/Privacy/Surveillance/CALEA/?f=archive.html |archive-date=25 October 2008 |title=CALEA Archive|work=Electronic Frontier Foundation (website) |access-date=14 March 2009 }}</ref><ref name="eff-calea-summary">{{cite web|url=https://www.eff.org/issues/calea |title=CALEA: The Perils of Wiretapping the Internet |work=Electronic Frontier Foundation (website) |access-date=14 March 2009 |url-status=live |archive-url=https://web.archive.org/web/20090316041313/http://www.eff.org/issues/calea |archive-date=16 March 2009 }}</ref><ref name="eff-calea-faq">{{cite web|url=https://www.eff.org/pages/calea-faq |title=CALEA: Frequently Asked Questions |work=Electronic Frontier Foundation (website) |access-date=14 March 2009 |url-status=live |archive-url=https://web.archive.org/web/20090501072553/http://www.eff.org/pages/calea-faq |archive-date=1 May 2009 |date=20 September 2007 }}</ref> ] is the monitoring of data traffic on a ]. Computers communicate over the Internet by breaking up messages (emails, images, videos, web pages, files, etc.) into small chunks called "packets", which are routed through a network of computers, until they reach their destination, where they are assembled back into a complete "message" again. ] intercepts these packets as they are traveling through the network, in order to examine their contents using other programs. A packet capture is an information ''gathering'' tool, but not an ''analysis'' tool. That is it gathers "messages" but it does not analyze them and figure out what they mean. Other programs are needed to perform ] and sift through intercepted data looking for important/useful information. Under the ] all U.S. telecommunications providers are required to install packet sniffing technology to allow Federal law enforcement and intelligence agencies to intercept all of their customers' ] and VoIP traffic.<ref>{{cite web|url=http://www.baller.com/pdfs/ACE.pdf|archive-url=https://web.archive.org/web/20120907032500/http://www.baller.com/pdfs/ACE.pdf|title=American Council on Education vs. FCC, Decision, United States Court of Appeals for the District of Columbia Circuit|date=9 June 2006|access-date=8 September 2013|archive-date=7 September 2012}}</ref> | |||
| The large amount of data gathered from packet capture requires surveillance software that filters and reports relevant information, such as the use of certain words or phrases, the access to certain types of web sites, or communicating via email or chat with certain parties.<ref name="usatoday-chatroom">{{cite news|url=https://www.usatoday.com/tech/news/surveillance/2004-10-11-chatroom-surv_x.htm|title=Government funds chat room surveillance research|last=Hill|first=Michael|date=11 October 2004|agency=Associated Press|newspaper=USA Today|access-date=19 March 2009|url-status=live|archive-url=https://web.archive.org/web/20100511220550/http://www.usatoday.com/tech/news/surveillance/2004-10-11-chatroom-surv_x.htm|archive-date=11 May 2010}}</ref> Agencies, such as the ], ], ] and the ], spend billions of dollars per year to develop, purchase, implement, and operate systems for interception and analysis of data.<ref name="zdnet-fbi">{{cite news|url=http://news.zdnet.com/2100-9595_22-151059.html|archive-url=https://web.archive.org/web/20100407040227/http://news.zdnet.com/2100-9595_22-151059.html|title=FBI turns to broad new wiretap method|last=McCullagh|first=Declan|date=30 January 2007|work=ZDNet News|access-date=13 March 2009|archive-date=7 April 2010}}</ref> Similar systems are operated by ] to identify and suppress dissidents. The required hardware and software were allegedly installed by German ] and Finnish ].<ref>{{cite web|url=http://www.debka.com/article/3509/|title=First round in Internet war goes to Iranian intelligence|website=]|date=28 June 2009|url-access=subscription|archive-url=https://web.archive.org/web/20131221173608/http://www.debka.com/article/3509/ |archive-date=21 December 2013}}</ref> | |||
| === Censorship === | |||
| {{Main|Internet censorship |Internet freedom}} | |||
| {{See also|Culture of fear|Great Firewall}} | |||
| ] (2018)'''<ref name=FOTN-2018>{{cite web |title=Freedom on the Net 2018 |url=https://freedomhouse.org/sites/default/files/FOTN_2018_Final%20Booklet_11_1_2018.pdf |website=Freedom House |date=November 2018 |access-date=1 November 2018 |archive-url=https://web.archive.org/web/20181101192951/https://freedomhouse.org/sites/default/files/FOTN_2018_Final%20Booklet_11_1_2018.pdf |archive-date=1 November 2018 }}</ref><ref name=ONISS-Nov2011>OpenNet Initiative {{webarchive|url=https://web.archive.org/web/20120110211146/http://opennet.net/research/data |date=10 January 2012 }}, 8 November 2011 and {{webarchive|url=https://web.archive.org/web/20110826003215/http://opennet.net/research/profiles |date=26 August 2011 }}, the OpenNet Initiative is a collaborative partnership of the Citizen Lab at the Munk School of Global Affairs, University of Toronto; the Berkman Center for Internet & Society at Harvard University; and the SecDev Group, Ottawa</ref>{{efn|name=ONIChildPornLegal|Due to legal concerns the ] does not check for filtering of ] and because their classifications focus on technical filtering, they do not include other types of censorship.}}<ref name=RWBEnemies2014>{{cite web|url=http://12mars.rsf.org/2014-en/#slide2|archive-url=https://web.archive.org/web/20140312120731/http://12mars.rsf.org/2014-en/#slide2|archive-date=2014-03-12|title=Enemies of the Internet 2014: Entities at the heart of censorship and surveillance|website=Reporters Without Borders|location=Paris|date=11 March 2014}}</ref><ref name=RWBEnemies>{{cite web|url=https://12mars.rsf.org/wp-content/uploads/EN_RAPPORT_INTERNET_BD.pdf|archive-url=https://web.archive.org/web/20170703221044/https://12mars.rsf.org/wp-content/uploads/EN_RAPPORT_INTERNET_BD.pdf|archive-date=2017-07-03|title=Internet Enemies|website=Reporters Without Borders|location=Paris|date=12 March 2012}}</ref></div> | |||
| <blockquote> | |||
| {{Col-begin}} | |||
| {{Col-1-of-2}} | |||
| {{legend|#F9D|Pervasive}} | |||
| {{legend|#FDD|Substantial}} | |||
| {{Col-2-of-2}} | |||
| {{legend|#FFD|Selective}} | |||
| {{legend|#98FB98|Little or none}} | |||
| {{Col-end}} | |||
| <div style="text-align: center">{{legend|#e0e0e0|Unclassified / No data}}</div> | |||
| </blockquote> | |||
| ]] | |||
| Some governments, such as those of ], ], ], ], ] and the ], restrict access to content on the Internet within their territories, especially to political and religious content, with domain name and keyword filters.<ref>{{cite book|url=http://mitpress.mit.edu/catalog/item/default.asp?ttype=2&tid=12187|title=Access Controlled: The Shaping of Power, Rights, and Rule in Cyberspace|archive-url=https://web.archive.org/web/20110604102753/http://mitpress.mit.edu/catalog/item/default.asp?ttype=2&tid=12187 |archive-date=4 June 2011|first1=Ronald J.|last1=Deibert|first2=John G.|last2=Palfrey|first3=Rafal|last3=Rohozinski|first4=Jonathan|last4=Zittrain|publisher=MIT Press|year=2010|isbn=978-0-262-51435-4}}</ref> | |||
| In Norway, Denmark, Finland, and Sweden, major Internet service providers have voluntarily agreed to restrict access to sites listed by authorities. While this list of forbidden resources is supposed to contain only known child pornography sites, the content of the list is secret.<ref name="The Register">{{cite web|title=Finland censors anti-censorship site |work=] |url=https://www.theregister.co.uk/2008/02/18/finnish_policy_censor_activist/ |date=18 February 2008 |access-date=19 February 2008 |url-status=live |archive-url=https://web.archive.org/web/20080220075300/https://www.theregister.co.uk/2008/02/18/finnish_policy_censor_activist/ |archive-date=20 February 2008 }}</ref> Many countries, including the United States, have enacted laws against the possession or distribution of certain material, such as ], via the Internet but do not mandate filter software. Many free or commercially available software programs, called ] are available to users to block offensive websites on individual computers or networks in order to limit access by children to pornographic material or depiction of violence. | |||
| == Performance == | |||
| As the Internet is a heterogeneous network, its physical characteristics, including, for example the ] of connections, vary widely. It exhibits ] that depend on its large-scale organization.<ref>{{cite journal |last1=Albert |first1=Réka |last2=Jeong |first2=Hawoong |last3=Barabási |first3=Albert-László |s2cid=4419938 |title=Diameter of the World-Wide Web |journal=Nature |date=9 September 1999 |volume=401 |issue=6749 |pages=130–131 |doi=10.1038/43601|arxiv=cond-mat/9907038 |bibcode=1999Natur.401..130A }}</ref> | |||
| ===Traffic volume=== | |||
| {{Latest Global Internet traffic}} | |||
| The volume of ] is difficult to measure because no single point of measurement exists in the multi-tiered, non-hierarchical topology. Traffic data may be estimated from the aggregate volume through the peering points of the ] providers, but traffic that stays local in large provider networks may not be accounted for. | |||
| === Outages === | |||
| An ] or outage can be caused by local signaling interruptions. Disruptions of ]s may cause blackouts or slowdowns to large areas, such as in the ]. Less-developed countries are more vulnerable due to the small number of high-capacity links. Land cables are also vulnerable, as in 2011 when a woman digging for scrap metal severed most connectivity for the nation of Armenia.<ref>{{cite news|work=The Guardian |url=https://www.theguardian.com/world/2011/apr/06/georgian-woman-cuts-web-access |title=Georgian woman cuts off web access to whole of Armenia |date=6 April 2011 |access-date=11 April 2012 |url-status=live |archive-url=https://web.archive.org/web/20130825075603/http://www.theguardian.com/world/2011/apr/06/georgian-woman-cuts-web-access |archive-date=25 August 2013 }}</ref> Internet blackouts affecting almost entire countries can be achieved by governments as a form of ], as in the blockage of the ], whereby approximately 93%<ref name="renesys1">{{cite web| last =Cowie| first =James| title =Egypt Leaves the Internet| publisher =Renesys| url =http://www.renesys.com/blog/2011/01/egypt-leaves-the-internet.shtml| access-date =28 January 2011| archive-url =https://web.archive.org/web/20110128080518/http://www.renesys.com/blog/2011/01/egypt-leaves-the-internet.shtml| archive-date =28 January 2011}}</ref> of networks were without access in 2011 in an attempt to stop mobilization for ].<ref>{{cite news|url=https://www.bbc.co.uk/news/technology-12306041 |work=BBC News |title=Egypt severs internet connection amid growing unrest |date=28 January 2011 |url-status=live |archive-url=https://web.archive.org/web/20120123164134/http://www.bbc.co.uk/news/technology-12306041 |archive-date=23 January 2012 }}</ref> | |||
| === Energy use === | |||
| Estimates of the Internet's ] have been the subject of controversy, according to a 2014 peer-reviewed research paper that found claims differing by a factor of 20,000 published in the literature during the preceding decade, ranging from 0.0064 ]s per gigabyte transferred (kWh/GB) to 136 kWh/GB.<ref name="Environmental Impact Assessment Review">{{Cite journal|last1=Coroama|first1=Vlad C.|last2=Hilty|first2=Lorenz M.|date=February 2014|title=Assessing Internet energy intensity: A review of methods and results|url=http://publicationslist.org/data/lorenz.hilty/ref-218/2014_Coroama_Hilty_Assessing_Internet_Energy_Intensity_AAM.pdf|journal=Environmental Impact Assessment Review|language=en|volume=45|pages=63–68|doi=10.1016/j.eiar.2013.12.004|bibcode=2014EIARv..45...63C |access-date=9 March 2020|archive-date=23 September 2020|archive-url=https://web.archive.org/web/20200923042203/http://publicationslist.org/data/lorenz.hilty/ref-218/2014_Coroama_Hilty_Assessing_Internet_Energy_Intensity_AAM.pdf|url-status=live}}</ref> The researchers attributed these discrepancies mainly to the year of reference (i.e. whether efficiency gains over time had been taken into account) and to whether "end devices such as ]s and servers are included" in the analysis.<ref name="Environmental Impact Assessment Review" /> | |||
| In 2011, academic researchers estimated the overall ]d by the Internet to be between 170 and 307 ], less than two percent of the energy used by humanity. This estimate included the energy needed to build, operate, and periodically replace the estimated 750 million ]s, a billion ]s and 100 million servers worldwide as well as the energy that routers, ]s, ]es, ] transmitters and ] devices use when transmitting ].<ref>{{cite web|first=Jim|last=Giles|title=Internet responsible for 2 per cent of global energy usage|website=New Scientist|date=26 October 2011|url=http://www.newscientist.com/blogs/onepercent/2011/10/307-gw-the-maximum-energy-the.html |archive-date=1 October 2014 |archive-url=https://web.archive.org/web/20141001113334/http://www.newscientist.com/blogs/onepercent/2011/10/307-gw-the-maximum-energy-the.html}},</ref><ref>{{cite book|chapter-url=http://conferences.sigcomm.org/hotnets/2011/papers/hotnetsX-final56.pdf|archive-url=https://web.archive.org/web/20140810075940/http://conferences.sigcomm.org/hotnets/2011/papers/hotnetsX-final56.pdf |archive-date=10 August 2014|first1=Barath|last1=Raghavan|first2=Justin|last2=Ma|title=Proceedings of the 10th ACM Workshop on Hot Topics in Networks |chapter=The energy and emergy of the internet |date=14 November 2011|pages=1–6|location=Cambridge, MA.|publisher=ACM SIGCOMM|doi=10.1145/2070562.2070571|isbn=978-1-4503-1059-8|s2cid=6125953}}</ref> According to a non-peer-reviewed study published in 2018 by ] (a French think tank funded by corporate sponsors), nearly 4% of global ] could be attributed to global ] and the necessary infrastructure.<ref>{{cite web|url=https://www.dw.com/en/is-netflix-bad-for-the-environment-how-streaming-video-contributes-to-climate-change/a-49556716|title=Is Netflix bad for the environment? How streaming video contributes to climate change {{!}} DW {{!}} 11.07.2019|last=Cwienk|first=Jeannette|date=11 July 2019|publisher=Deutsche Welle|language=en-GB|access-date=19 July 2019|archive-date=12 July 2019|archive-url=https://web.archive.org/web/20190712203905/https://www.dw.com/en/is-netflix-bad-for-the-environment-how-streaming-video-contributes-to-climate-change/a-49556716|url-status=live}}</ref> The study also said that ] alone accounted for 60% of this data transfer and therefore contributed to over 300 million tons of CO<sub>2</sub> emission per year, and argued for new "digital sobriety" regulations restricting the use and size of video files.<ref>{{cite web|url=https://theshiftproject.org/en/article/unsustainable-use-online-video/|title="Climate crisis: The Unsustainable Use of Online Video": Our new report|date=10 July 2019|website=The Shift Project|language=en-GB|access-date=19 July 2019|archive-url=https://web.archive.org/web/20190721144259/https://theshiftproject.org/en/article/unsustainable-use-online-video/|archive-date=21 July 2019|url-status=live}}</ref> | |||
| {{Clear}} | |||
| == See also == | |||
| {{portal|Internet|World}} | |||
| {{div col|colwidth=20em}} | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * "]" | |||
| * ] | |||
| {{div col end}} | |||
| == Notes == | |||
| {{notelist}} | |||
| == References == | |||
| {{reflist}} | {{reflist}} | ||
| == |
== Sources == | ||
| * {{Free-content attribution | |||
| * — Internet history and related information, including information from many creators of the Internet | |||
| | title = World Trends in Freedom of Expression and Media Development Global Report 2017/2018 | |||
| * peer-reviewed journal on the Internet | |||
| | publisher = UNESCO | |||
| | page numbers = 202 | |||
| | source = | |||
| | documentURL = http://unesdoc.unesco.org/images/0026/002610/261065e.pdf | |||
| | license statement url = http://www.unesco.org/ulis/cgi-bin/ulis.pl?catno=261065&set=005B0D29C5_0_12&gp=1&lin=1&ll=1 | |||
| | license = | |||
| }} | |||
| *{{cite book |last1=Abbate |first1=Janet |title=Inventing the Internet |location=Cambridge, Massachusetts |author-link=Janet Abbate |publisher=MIT Press |year=1999 |isbn=978-0-262-01172-3 |url-access=registration |url=https://archive.org/details/inventinginterne00abba}} | |||
| == Further reading == | |||
| ==External links== | |||
| * , a peer-reviewed journal on the Internet by the University Library of the ], {{ISSN|1396-0466}} | |||
| {{wikibooks|The Information Age}} | |||
| * , Vincent Zegna & Mike Pepper, Sonet Digital, November 2005, pp. 1–7. | |||
| ===General=== | |||
| * {{Cite book|last=Castells|first=Manuel|title=The Rise of the Network Society|publisher=]|year=2010|isbn=978-1-4051-9686-4}} | |||
| * | |||
| * {{citation |last=Yeo |first=ShinJoung |date=2023 |title=Behind the Search Box: Google and the Global Internet Industry |publisher=U of Illinois Press |jstor=10.5406/jj.4116455 |isbn=978-0-252-04499-1 }} | |||
| * | |||
| * | |||
| * from Keynote | |||
| * | |||
| == External links == | |||
| ===Articles=== | |||
| {{Sister project links|Internet|voy=no}} | |||
| * | |||
| * | |||
| * | |||
| * , Internet history and related information, including information from many creators of the Internet | |||
| * | |||
| * Seven part article explaining the origins to the present and a summary of predictions for the future of the Internet. | |||
| * | |||
| * | |||
| * An article summarizing the core Internet technologies, written for non-experts | |||
| {{Media culture}} | |||
| ===History=== | |||
| {{Semantic Web}} | |||
| *The Dream Machine: J.C.R. Licklider and the Revolution That Made Computing Personal M. Mitchell Waldrop | |||
| {{Cloud computing}} | |||
| * | |||
| {{Telecommunications}} | |||
| * | |||
| {{Authority control}} | |||
| * | |||
| * | |||
| * | |||
| * | |||
| * | |||
| * | |||
| * - A searchable database of old cached versions of Web sites dating back to 1996 | |||
| * | |||
| * | |||
| * A list of lectures, some of which relate to the Internet, from the ] is available . Of particular interest is lecture #3 ''The Next Big Thing: Video Internet'' which is delivered in ] format. The lecture gives a brief history of networking; discusses convergence between the Internet/telephone/television networks; the expansion of broadband access; makes predictions about the future of delivery of video over the Internet. | |||
| a list of different themes from the www | |||
| ] | |||
| ] | ] | ||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | ] | ||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | ] | ||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
Latest revision as of 04:50, 22 December 2024
Global system of connected computer networks This article is about the worldwide computer network. For the global system of pages accessed through URLs via the Internet, see World Wide Web. For other uses, see Internet (disambiguation). "The Internet" redirects here. For the American music group, see The Internet (band). For the song Welcome To The Internet, see Bo Burnham: Inside. "Interweb" redirects here. For the song by Poppy, see Interweb (song).
| Internet |
|---|
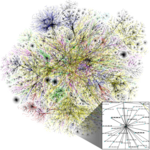 An Opte Project visualization of routing paths through a portion of the Internet An Opte Project visualization of routing paths through a portion of the Internet |
| General |
| Governance |
| Information infrastructure |
| Services |
| History |
| Guides |
|
|
| Computer network types by scale |
|---|
 |
The Internet (or internet) is the global system of interconnected computer networks that uses the Internet protocol suite (TCP/IP) to communicate between networks and devices. It is a network of networks that consists of private, public, academic, business, and government networks of local to global scope, linked by a broad array of electronic, wireless, and optical networking technologies. The Internet carries a vast range of information resources and services, such as the interlinked hypertext documents and applications of the World Wide Web (WWW), electronic mail, internet telephony, and file sharing.
The origins of the Internet date back to research that enabled the time-sharing of computer resources, the development of packet switching in the 1960s and the design of computer networks for data communication. The set of rules (communication protocols) to enable internetworking on the Internet arose from research and development commissioned in the 1970s by the Defense Advanced Research Projects Agency (DARPA) of the United States Department of Defense in collaboration with universities and researchers across the United States and in the United Kingdom and France. The ARPANET initially served as a backbone for the interconnection of regional academic and military networks in the United States to enable resource sharing. The funding of the National Science Foundation Network as a new backbone in the 1980s, as well as private funding for other commercial extensions, encouraged worldwide participation in the development of new networking technologies and the merger of many networks using DARPA's Internet protocol suite. The linking of commercial networks and enterprises by the early 1990s, as well as the advent of the World Wide Web, marked the beginning of the transition to the modern Internet, and generated sustained exponential growth as generations of institutional, personal, and mobile computers were connected to the internetwork. Although the Internet was widely used by academia in the 1980s, the subsequent commercialization of the Internet in the 1990s and beyond incorporated its services and technologies into virtually every aspect of modern life.
Most traditional communication media, including telephone, radio, television, paper mail, and newspapers, are reshaped, redefined, or even bypassed by the Internet, giving birth to new services such as email, Internet telephone, Internet television, online music, digital newspapers, and video streaming websites. Newspapers, books, and other print publishing have adapted to website technology or have been reshaped into blogging, web feeds, and online news aggregators. The Internet has enabled and accelerated new forms of personal interaction through instant messaging, Internet forums, and social networking services. Online shopping has grown exponentially for major retailers, small businesses, and entrepreneurs, as it enables firms to extend their "brick and mortar" presence to serve a larger market or even sell goods and services entirely online. Business-to-business and financial services on the Internet affect supply chains across entire industries.
The Internet has no single centralized governance in either technological implementation or policies for access and usage; each constituent network sets its own policies. The overarching definitions of the two principal name spaces on the Internet, the Internet Protocol address (IP address) space and the Domain Name System (DNS), are directed by a maintainer organization, the Internet Corporation for Assigned Names and Numbers (ICANN). The technical underpinning and standardization of the core protocols is an activity of the Internet Engineering Task Force (IETF), a non-profit organization of loosely affiliated international participants that anyone may associate with by contributing technical expertise. In November 2006, the Internet was included on USA Today's list of the New Seven Wonders.
Terminology
Further information: Capitalization of Internet and internetworkingThe word internetted was used as early as 1849, meaning interconnected or interwoven. The word Internet was used in 1945 by the United States War Department in a radio operator's manual, and in 1974 as the shorthand form of Internetwork. Today, the term Internet most commonly refers to the global system of interconnected computer networks, though it may also refer to any group of smaller networks.
When it came into common use, most publications treated the word Internet as a capitalized proper noun; this has become less common. This reflects the tendency in English to capitalize new terms and move them to lowercase as they become familiar. The word is sometimes still capitalized to distinguish the global internet from smaller networks, though many publications, including the AP Stylebook since 2016, recommend the lowercase form in every case. In 2016, the Oxford English Dictionary found that, based on a study of around 2.5 billion printed and online sources, "Internet" was capitalized in 54% of cases.
The terms Internet and World Wide Web are often used interchangeably; it is common to speak of "going on the Internet" when using a web browser to view web pages. However, the World Wide Web, or the Web, is only one of a large number of Internet services, a collection of documents (web pages) and other web resources linked by hyperlinks and URLs.
History
Main articles: History of the Internet, History of the World Wide Web, and Protocol Wars
In the 1960s, computer scientists began developing systems for time-sharing of computer resources. J. C. R. Licklider proposed the idea of a universal network while working at Bolt Beranek & Newman and, later, leading the Information Processing Techniques Office (IPTO) at the Advanced Research Projects Agency (ARPA) of the United States Department of Defense (DoD). Research into packet switching, one of the fundamental Internet technologies, started in the work of Paul Baran at RAND in the early 1960s and, independently, Donald Davies at the United Kingdom's National Physical Laboratory (NPL) in 1965. After the Symposium on Operating Systems Principles in 1967, packet switching from the proposed NPL network and routing concepts proposed by Baran were incorporated into the design of the ARPANET, an experimental resource sharing network proposed by ARPA.
ARPANET development began with two network nodes which were interconnected between the University of California, Los Angeles (UCLA) and the Stanford Research Institute (now SRI International) on 29 October 1969. The third site was at the University of California, Santa Barbara, followed by the University of Utah. In a sign of future growth, 15 sites were connected to the young ARPANET by the end of 1971. These early years were documented in the 1972 film Computer Networks: The Heralds of Resource Sharing. Thereafter, the ARPANET gradually developed into a decentralized communications network, connecting remote centers and military bases in the United States. Other user networks and research networks, such as the Merit Network and CYCLADES, were developed in the late 1960s and early 1970s.
Early international collaborations for the ARPANET were rare. Connections were made in 1973 to Norway (NORSAR and NDRE), and to Peter Kirstein's research group at University College London (UCL), which provided a gateway to British academic networks, forming the first internetwork for resource sharing. ARPA projects, the International Network Working Group and commercial initiatives led to the development of various protocols and standards by which multiple separate networks could become a single network or "a network of networks". In 1974, Vint Cerf at Stanford University and Bob Kahn at DARPA published a proposal for "A Protocol for Packet Network Intercommunication". They used the term internet as a shorthand for internetwork in RFC 675, and later RFCs repeated this use. Cerf and Kahn credit Louis Pouzin and others with important influences on the resulting TCP/IP design. National PTTs and commercial providers developed the X.25 standard and deployed it on public data networks.
Access to the ARPANET was expanded in 1981 when the National Science Foundation (NSF) funded the Computer Science Network (CSNET). In 1982, the Internet Protocol Suite (TCP/IP) was standardized, which facilitated worldwide proliferation of interconnected networks. TCP/IP network access expanded again in 1986 when the National Science Foundation Network (NSFNet) provided access to supercomputer sites in the United States for researchers, first at speeds of 56 kbit/s and later at 1.5 Mbit/s and 45 Mbit/s. The NSFNet expanded into academic and research organizations in Europe, Australia, New Zealand and Japan in 1988–89. Although other network protocols such as UUCP and PTT public data networks had global reach well before this time, this marked the beginning of the Internet as an intercontinental network. Commercial Internet service providers (ISPs) emerged in 1989 in the United States and Australia. The ARPANET was decommissioned in 1990.

Steady advances in semiconductor technology and optical networking created new economic opportunities for commercial involvement in the expansion of the network in its core and for delivering services to the public. In mid-1989, MCI Mail and Compuserve established connections to the Internet, delivering email and public access products to the half million users of the Internet. Just months later, on 1 January 1990, PSInet launched an alternate Internet backbone for commercial use; one of the networks that added to the core of the commercial Internet of later years. In March 1990, the first high-speed T1 (1.5 Mbit/s) link between the NSFNET and Europe was installed between Cornell University and CERN, allowing much more robust communications than were capable with satellites.
Later in 1990, Tim Berners-Lee began writing WorldWideWeb, the first web browser, after two years of lobbying CERN management. By Christmas 1990, Berners-Lee had built all the tools necessary for a working Web: the HyperText Transfer Protocol (HTTP) 0.9, the HyperText Markup Language (HTML), the first Web browser (which was also an HTML editor and could access Usenet newsgroups and FTP files), the first HTTP server software (later known as CERN httpd), the first web server, and the first Web pages that described the project itself. In 1991 the Commercial Internet eXchange was founded, allowing PSInet to communicate with the other commercial networks CERFnet and Alternet. Stanford Federal Credit Union was the first financial institution to offer online Internet banking services to all of its members in October 1994. In 1996, OP Financial Group, also a cooperative bank, became the second online bank in the world and the first in Europe. By 1995, the Internet was fully commercialized in the U.S. when the NSFNet was decommissioned, removing the last restrictions on use of the Internet to carry commercial traffic.
| 2005 | 2010 | 2017 | 2023 | |
|---|---|---|---|---|
| World population (billions) | 6.5 | 6.9 | 7.4 | 8.0 |
| Worldwide | 16% | 30% | 48% | 67% |
| In developing world | 8% | 21% | 41.3% | 60% |
| In developed world | 51% | 67% | 81% | 93% |
As technology advanced and commercial opportunities fueled reciprocal growth, the volume of Internet traffic started experiencing similar characteristics as that of the scaling of MOS transistors, exemplified by Moore's law, doubling every 18 months. This growth, formalized as Edholm's law, was catalyzed by advances in MOS technology, laser light wave systems, and noise performance.
Since 1995, the Internet has tremendously impacted culture and commerce, including the rise of near-instant communication by email, instant messaging, telephony (Voice over Internet Protocol or VoIP), two-way interactive video calls, and the World Wide Web with its discussion forums, blogs, social networking services, and online shopping sites. Increasing amounts of data are transmitted at higher and higher speeds over fiber optic networks operating at 1 Gbit/s, 10 Gbit/s, or more. The Internet continues to grow, driven by ever-greater amounts of online information and knowledge, commerce, entertainment and social networking services. During the late 1990s, it was estimated that traffic on the public Internet grew by 100 percent per year, while the mean annual growth in the number of Internet users was thought to be between 20% and 50%. This growth is often attributed to the lack of central administration, which allows organic growth of the network, as well as the non-proprietary nature of the Internet protocols, which encourages vendor interoperability and prevents any one company from exerting too much control over the network. As of 31 March 2011, the estimated total number of Internet users was 2.095 billion (30% of world population). It is estimated that in 1993 the Internet carried only 1% of the information flowing through two-way telecommunication. By 2000 this figure had grown to 51%, and by 2007 more than 97% of all telecommunicated information was carried over the Internet.
Governance
Main article: Internet governance
The Internet is a global network that comprises many voluntarily interconnected autonomous networks. It operates without a central governing body. The technical underpinning and standardization of the core protocols (IPv4 and IPv6) is an activity of the Internet Engineering Task Force (IETF), a non-profit organization of loosely affiliated international participants that anyone may associate with by contributing technical expertise. To maintain interoperability, the principal name spaces of the Internet are administered by the Internet Corporation for Assigned Names and Numbers (ICANN). ICANN is governed by an international board of directors drawn from across the Internet technical, business, academic, and other non-commercial communities. ICANN coordinates the assignment of unique identifiers for use on the Internet, including domain names, IP addresses, application port numbers in the transport protocols, and many other parameters. Globally unified name spaces are essential for maintaining the global reach of the Internet. This role of ICANN distinguishes it as perhaps the only central coordinating body for the global Internet.
Regional Internet registries (RIRs) were established for five regions of the world. The African Network Information Center (AfriNIC) for Africa, the American Registry for Internet Numbers (ARIN) for North America, the Asia–Pacific Network Information Centre (APNIC) for Asia and the Pacific region, the Latin American and Caribbean Internet Addresses Registry (LACNIC) for Latin America and the Caribbean region, and the Réseaux IP Européens – Network Coordination Centre (RIPE NCC) for Europe, the Middle East, and Central Asia were delegated to assign IP address blocks and other Internet parameters to local registries, such as Internet service providers, from a designated pool of addresses set aside for each region.
The National Telecommunications and Information Administration, an agency of the United States Department of Commerce, had final approval over changes to the DNS root zone until the IANA stewardship transition on 1 October 2016. The Internet Society (ISOC) was founded in 1992 with a mission to "assure the open development, evolution and use of the Internet for the benefit of all people throughout the world". Its members include individuals (anyone may join) as well as corporations, organizations, governments, and universities. Among other activities ISOC provides an administrative home for a number of less formally organized groups that are involved in developing and managing the Internet, including: the IETF, Internet Architecture Board (IAB), Internet Engineering Steering Group (IESG), Internet Research Task Force (IRTF), and Internet Research Steering Group (IRSG). On 16 November 2005, the United Nations-sponsored World Summit on the Information Society in Tunis established the Internet Governance Forum (IGF) to discuss Internet-related issues.
Infrastructure
See also: List of countries by number of Internet users and List of countries by Internet connection speeds
The communications infrastructure of the Internet consists of its hardware components and a system of software layers that control various aspects of the architecture. As with any computer network, the Internet physically consists of routers, media (such as cabling and radio links), repeaters, modems etc. However, as an example of internetworking, many of the network nodes are not necessarily Internet equipment per se. The internet packets are carried by other full-fledged networking protocols with the Internet acting as a homogeneous networking standard, running across heterogeneous hardware, with the packets guided to their destinations by IP routers.
Service tiers
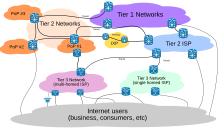
Internet service providers (ISPs) establish the worldwide connectivity between individual networks at various levels of scope. End-users who only access the Internet when needed to perform a function or obtain information, represent the bottom of the routing hierarchy. At the top of the routing hierarchy are the tier 1 networks, large telecommunication companies that exchange traffic directly with each other via very high speed fiber-optic cables and governed by peering agreements. Tier 2 and lower-level networks buy Internet transit from other providers to reach at least some parties on the global Internet, though they may also engage in peering. An ISP may use a single upstream provider for connectivity, or implement multihoming to achieve redundancy and load balancing. Internet exchange points are major traffic exchanges with physical connections to multiple ISPs. Large organizations, such as academic institutions, large enterprises, and governments, may perform the same function as ISPs, engaging in peering and purchasing transit on behalf of their internal networks. Research networks tend to interconnect with large subnetworks such as GEANT, GLORIAD, Internet2, and the UK's national research and education network, JANET.
Access
Common methods of Internet access by users include dial-up with a computer modem via telephone circuits, broadband over coaxial cable, fiber optics or copper wires, Wi-Fi, satellite, and cellular telephone technology (e.g. 3G, 4G). The Internet may often be accessed from computers in libraries and Internet cafés. Internet access points exist in many public places such as airport halls and coffee shops. Various terms are used, such as public Internet kiosk, public access terminal, and Web payphone. Many hotels also have public terminals that are usually fee-based. These terminals are widely accessed for various usages, such as ticket booking, bank deposit, or online payment. Wi-Fi provides wireless access to the Internet via local computer networks. Hotspots providing such access include Wi-Fi cafés, where users need to bring their own wireless devices, such as a laptop or PDA. These services may be free to all, free to customers only, or fee-based.
Grassroots efforts have led to wireless community networks. Commercial Wi-Fi services that cover large areas are available in many cities, such as New York, London, Vienna, Toronto, San Francisco, Philadelphia, Chicago and Pittsburgh, where the Internet can then be accessed from places such as a park bench. Experiments have also been conducted with proprietary mobile wireless networks like Ricochet, various high-speed data services over cellular networks, and fixed wireless services. Modern smartphones can also access the Internet through the cellular carrier network. For Web browsing, these devices provide applications such as Google Chrome, Safari, and Firefox and a wide variety of other Internet software may be installed from app stores. Internet usage by mobile and tablet devices exceeded desktop worldwide for the first time in October 2016.
Mobile communication

The International Telecommunication Union (ITU) estimated that, by the end of 2017, 48% of individual users regularly connect to the Internet, up from 34% in 2012. Mobile Internet connectivity has played an important role in expanding access in recent years, especially in Asia and the Pacific and in Africa. The number of unique mobile cellular subscriptions increased from 3.9 billion in 2012 to 4.8 billion in 2016, two-thirds of the world's population, with more than half of subscriptions located in Asia and the Pacific. The number of subscriptions was predicted to rise to 5.7 billion users in 2020. As of 2018, 80% of the world's population were covered by a 4G network. The limits that users face on accessing information via mobile applications coincide with a broader process of fragmentation of the Internet. Fragmentation restricts access to media content and tends to affect the poorest users the most.
Zero-rating, the practice of Internet service providers allowing users free connectivity to access specific content or applications without cost, has offered opportunities to surmount economic hurdles but has also been accused by its critics as creating a two-tiered Internet. To address the issues with zero-rating, an alternative model has emerged in the concept of 'equal rating' and is being tested in experiments by Mozilla and Orange in Africa. Equal rating prevents prioritization of one type of content and zero-rates all content up to a specified data cap. In a study published by Chatham House, 15 out of 19 countries researched in Latin America had some kind of hybrid or zero-rated product offered. Some countries in the region had a handful of plans to choose from (across all mobile network operators) while others, such as Colombia, offered as many as 30 pre-paid and 34 post-paid plans.
A study of eight countries in the Global South found that zero-rated data plans exist in every country, although there is a great range in the frequency with which they are offered and actually used in each. The study looked at the top three to five carriers by market share in Bangladesh, Colombia, Ghana, India, Kenya, Nigeria, Peru and Philippines. Across the 181 plans examined, 13 percent were offering zero-rated services. Another study, covering Ghana, Kenya, Nigeria and South Africa, found Facebook's Free Basics and Misplaced Pages Zero to be the most commonly zero-rated content.
Internet Protocol Suite
| Internet protocol suite |
|---|
| Application layer |
| Transport layer |
| Internet layer |
| Link layer |
The Internet standards describe a framework known as the Internet protocol suite (also called TCP/IP, based on the first two components.) This is a suite of protocols that are ordered into a set of four conceptional layers by the scope of their operation, originally documented in RFC 1122 and RFC 1123. At the top is the application layer, where communication is described in terms of the objects or data structures most appropriate for each application. For example, a web browser operates in a client–server application model and exchanges information with the HyperText Transfer Protocol (HTTP) and an application-germane data structure, such as the HyperText Markup Language (HTML).
Below this top layer, the transport layer connects applications on different hosts with a logical channel through the network. It provides this service with a variety of possible characteristics, such as ordered, reliable delivery (TCP), and an unreliable datagram service (UDP).
Underlying these layers are the networking technologies that interconnect networks at their borders and exchange traffic across them. The Internet layer implements the Internet Protocol (IP) which enables computers to identify and locate each other by IP address and route their traffic via intermediate (transit) networks. The Internet Protocol layer code is independent of the type of network that it is physically running over.
At the bottom of the architecture is the link layer, which connects nodes on the same physical link, and contains protocols that do not require routers for traversal to other links. The protocol suite does not explicitly specify hardware methods to transfer bits, or protocols to manage such hardware, but assumes that appropriate technology is available. Examples of that technology include Wi-Fi, Ethernet, and DSL.

Internet protocol

The most prominent component of the Internet model is the Internet Protocol (IP). IP enables internetworking and, in essence, establishes the Internet itself. Two versions of the Internet Protocol exist, IPv4 and IPv6.
IP Addresses

For locating individual computers on the network, the Internet provides IP addresses. IP addresses are used by the Internet infrastructure to direct internet packets to their destinations. They consist of fixed-length numbers, which are found within the packet. IP addresses are generally assigned to equipment either automatically via DHCP, or are configured.
However, the network also supports other addressing systems. Users generally enter domain names (e.g. "en.wikipedia.org") instead of IP addresses because they are easier to remember; they are converted by the Domain Name System (DNS) into IP addresses which are more efficient for routing purposes.
IPv4
Internet Protocol version 4 (IPv4) defines an IP address as a 32-bit number. IPv4 is the initial version used on the first generation of the Internet and is still in dominant use. It was designed in 1981 to address up to ≈4.3 billion (10) hosts. However, the explosive growth of the Internet has led to IPv4 address exhaustion, which entered its final stage in 2011, when the global IPv4 address allocation pool was exhausted.
IPv6
Because of the growth of the Internet and the depletion of available IPv4 addresses, a new version of IP IPv6, was developed in the mid-1990s, which provides vastly larger addressing capabilities and more efficient routing of Internet traffic. IPv6 uses 128 bits for the IP address and was standardized in 1998. IPv6 deployment has been ongoing since the mid-2000s and is currently in growing deployment around the world, since Internet address registries (RIRs) began to urge all resource managers to plan rapid adoption and conversion.
IPv6 is not directly interoperable by design with IPv4. In essence, it establishes a parallel version of the Internet not directly accessible with IPv4 software. Thus, translation facilities must exist for internetworking or nodes must have duplicate networking software for both networks. Essentially all modern computer operating systems support both versions of the Internet Protocol. Network infrastructure, however, has been lagging in this development. Aside from the complex array of physical connections that make up its infrastructure, the Internet is facilitated by bi- or multi-lateral commercial contracts, e.g., peering agreements, and by technical specifications or protocols that describe the exchange of data over the network. Indeed, the Internet is defined by its interconnections and routing policies.
Subnetwork

A subnetwork or subnet is a logical subdivision of an IP network. The practice of dividing a network into two or more networks is called subnetting. Computers that belong to a subnet are addressed with an identical most-significant bit-group in their IP addresses. This results in the logical division of an IP address into two fields, the network number or routing prefix and the rest field or host identifier. The rest field is an identifier for a specific host or network interface.
The routing prefix may be expressed in Classless Inter-Domain Routing (CIDR) notation written as the first address of a network, followed by a slash character (/), and ending with the bit-length of the prefix. For example, 198.51.100.0/24 is the prefix of the Internet Protocol version 4 network starting at the given address, having 24 bits allocated for the network prefix, and the remaining 8 bits reserved for host addressing. Addresses in the range 198.51.100.0 to 198.51.100.255 belong to this network. The IPv6 address specification 2001:db8::/32 is a large address block with 2 addresses, having a 32-bit routing prefix.
For IPv4, a network may also be characterized by its subnet mask or netmask, which is the bitmask that when applied by a bitwise AND operation to any IP address in the network, yields the routing prefix. Subnet masks are also expressed in dot-decimal notation like an address. For example, 255.255.255.0 is the subnet mask for the prefix 198.51.100.0/24.
Traffic is exchanged between subnetworks through routers when the routing prefixes of the source address and the destination address differ. A router serves as a logical or physical boundary between the subnets.
The benefits of subnetting an existing network vary with each deployment scenario. In the address allocation architecture of the Internet using CIDR and in large organizations, it is necessary to allocate address space efficiently. Subnetting may also enhance routing efficiency or have advantages in network management when subnetworks are administratively controlled by different entities in a larger organization. Subnets may be arranged logically in a hierarchical architecture, partitioning an organization's network address space into a tree-like routing structure.
Routing
Computers and routers use routing tables in their operating system to direct IP packets to reach a node on a different subnetwork. Routing tables are maintained by manual configuration or automatically by routing protocols. End-nodes typically use a default route that points toward an ISP providing transit, while ISP routers use the Border Gateway Protocol to establish the most efficient routing across the complex connections of the global Internet. The default gateway is the node that serves as the forwarding host (router) to other networks when no other route specification matches the destination IP address of a packet.
IETF
While the hardware components in the Internet infrastructure can often be used to support other software systems, it is the design and the standardization process of the software that characterizes the Internet and provides the foundation for its scalability and success. The responsibility for the architectural design of the Internet software systems has been assumed by the Internet Engineering Task Force (IETF). The IETF conducts standard-setting work groups, open to any individual, about the various aspects of Internet architecture. The resulting contributions and standards are published as Request for Comments (RFC) documents on the IETF web site. The principal methods of networking that enable the Internet are contained in specially designated RFCs that constitute the Internet Standards. Other less rigorous documents are simply informative, experimental, or historical, or document the best current practices (BCP) when implementing Internet technologies.
Applications and services
The Internet carries many applications and services, most prominently the World Wide Web, including social media, electronic mail, mobile applications, multiplayer online games, Internet telephony, file sharing, and streaming media services. Most servers that provide these services are today hosted in data centers, and content is often accessed through high-performance content delivery networks.
World Wide Web
Main article: World Wide Web
The World Wide Web is a global collection of documents, images, multimedia, applications, and other resources, logically interrelated by hyperlinks and referenced with Uniform Resource Identifiers (URIs), which provide a global system of named references. URIs symbolically identify services, web servers, databases, and the documents and resources that they can provide. HyperText Transfer Protocol (HTTP) is the main access protocol of the World Wide Web. Web services also use HTTP for communication between software systems for information transfer, sharing and exchanging business data and logistics and is one of many languages or protocols that can be used for communication on the Internet.
World Wide Web browser software, such as Microsoft's Internet Explorer/Edge, Mozilla Firefox, Opera, Apple's Safari, and Google Chrome, enable users to navigate from one web page to another via the hyperlinks embedded in the documents. These documents may also contain any combination of computer data, including graphics, sounds, text, video, multimedia and interactive content that runs while the user is interacting with the page. Client-side software can include animations, games, office applications and scientific demonstrations. Through keyword-driven Internet research using search engines like Yahoo!, Bing and Google, users worldwide have easy, instant access to a vast and diverse amount of online information. Compared to printed media, books, encyclopedias and traditional libraries, the World Wide Web has enabled the decentralization of information on a large scale.
The Web has enabled individuals and organizations to publish ideas and information to a potentially large audience online at greatly reduced expense and time delay. Publishing a web page, a blog, or building a website involves little initial cost and many cost-free services are available. However, publishing and maintaining large, professional web sites with attractive, diverse and up-to-date information is still a difficult and expensive proposition. Many individuals and some companies and groups use web logs or blogs, which are largely used as easily being able to update online diaries. Some commercial organizations encourage staff to communicate advice in their areas of specialization in the hope that visitors will be impressed by the expert knowledge and free information and be attracted to the corporation as a result.
Advertising on popular web pages can be lucrative, and e-commerce, which is the sale of products and services directly via the Web, continues to grow. Online advertising is a form of marketing and advertising which uses the Internet to deliver promotional marketing messages to consumers. It includes email marketing, search engine marketing (SEM), social media marketing, many types of display advertising (including web banner advertising), and mobile advertising. In 2011, Internet advertising revenues in the United States surpassed those of cable television and nearly exceeded those of broadcast television. Many common online advertising practices are controversial and increasingly subject to regulation.
When the Web developed in the 1990s, a typical web page was stored in completed form on a web server, formatted in HTML, ready for transmission to a web browser in response to a request. Over time, the process of creating and serving web pages has become dynamic, creating a flexible design, layout, and content. Websites are often created using content management software with, initially, very little content. Contributors to these systems, who may be paid staff, members of an organization or the public, fill underlying databases with content using editing pages designed for that purpose while casual visitors view and read this content in HTML form. There may or may not be editorial, approval and security systems built into the process of taking newly entered content and making it available to the target visitors.
Communication
Email is an important communications service available via the Internet. The concept of sending electronic text messages between parties, analogous to mailing letters or memos, predates the creation of the Internet. Pictures, documents, and other files are sent as email attachments. Email messages can be cc-ed to multiple email addresses.
Internet telephony is a common communications service realized with the Internet. The name of the principal internetworking protocol, the Internet Protocol, lends its name to voice over Internet Protocol (VoIP). The idea began in the early 1990s with walkie-talkie-like voice applications for personal computers. VoIP systems now dominate many markets and are as easy to use and as convenient as a traditional telephone. The benefit has been substantial cost savings over traditional telephone calls, especially over long distances. Cable, ADSL, and mobile data networks provide Internet access in customer premises and inexpensive VoIP network adapters provide the connection for traditional analog telephone sets. The voice quality of VoIP often exceeds that of traditional calls. Remaining problems for VoIP include the situation that emergency services may not be universally available and that devices rely on a local power supply, while older traditional phones are powered from the local loop, and typically operate during a power failure.
Data transfer
File sharing is an example of transferring large amounts of data across the Internet. A computer file can be emailed to customers, colleagues and friends as an attachment. It can be uploaded to a website or File Transfer Protocol (FTP) server for easy download by others. It can be put into a "shared location" or onto a file server for instant use by colleagues. The load of bulk downloads to many users can be eased by the use of "mirror" servers or peer-to-peer networks. In any of these cases, access to the file may be controlled by user authentication, the transit of the file over the Internet may be obscured by encryption, and money may change hands for access to the file. The price can be paid by the remote charging of funds from, for example, a credit card whose details are also passed—usually fully encrypted—across the Internet. The origin and authenticity of the file received may be checked by digital signatures or by MD5 or other message digests. These simple features of the Internet, over a worldwide basis, are changing the production, sale, and distribution of anything that can be reduced to a computer file for transmission. This includes all manner of print publications, software products, news, music, film, video, photography, graphics and the other arts. This in turn has caused seismic shifts in each of the existing industries that previously controlled the production and distribution of these products.
Streaming media is the real-time delivery of digital media for immediate consumption or enjoyment by end users. Many radio and television broadcasters provide Internet feeds of their live audio and video productions. They may also allow time-shift viewing or listening such as Preview, Classic Clips and Listen Again features. These providers have been joined by a range of pure Internet "broadcasters" who never had on-air licenses. This means that an Internet-connected device, such as a computer or something more specific, can be used to access online media in much the same way as was previously possible only with a television or radio receiver. The range of available types of content is much wider, from specialized technical webcasts to on-demand popular multimedia services. Podcasting is a variation on this theme, where—usually audio—material is downloaded and played back on a computer or shifted to a portable media player to be listened to on the move. These techniques using simple equipment allow anybody, with little censorship or licensing control, to broadcast audio-visual material worldwide. Digital media streaming increases the demand for network bandwidth. For example, standard image quality needs 1 Mbit/s link speed for SD 480p, HD 720p quality requires 2.5 Mbit/s, and the top-of-the-line HDX quality needs 4.5 Mbit/s for 1080p.
Webcams are a low-cost extension of this phenomenon. While some webcams can give full-frame-rate video, the picture either is usually small or updates slowly. Internet users can watch animals around an African waterhole, ships in the Panama Canal, traffic at a local roundabout or monitor their own premises, live and in real time. Video chat rooms and video conferencing are also popular with many uses being found for personal webcams, with and without two-way sound. YouTube was founded on 15 February 2005 and is now the leading website for free streaming video with more than two billion users. It uses an HTML5 based web player by default to stream and show video files. Registered users may upload an unlimited amount of video and build their own personal profile. YouTube claims that its users watch hundreds of millions, and upload hundreds of thousands of videos daily.
Social impact
The Internet has enabled new forms of social interaction, activities, and social associations. This phenomenon has given rise to the scholarly study of the sociology of the Internet. The early Internet left an impact on some writers who used symbolism to write about it, such as describing the Internet as a "means to connect individuals in a vast invisible net over all the earth."
Users
See also: Global Internet usage, English in computing, and Languages used on the Internet


Between 2000 and 2009, the number of Internet users globally rose from 390 million to 1.9 billion. By 2010, 22% of the world's population had access to computers with 1 billion Google searches every day, 300 million Internet users reading blogs, and 2 billion videos viewed daily on YouTube. In 2014 the world's Internet users surpassed 3 billion or 44 percent of world population, but two-thirds came from the richest countries, with 78 percent of Europeans using the Internet, followed by 57 percent of the Americas. However, by 2018, Asia alone accounted for 51% of all Internet users, with 2.2 billion out of the 4.3 billion Internet users in the world. China's Internet users surpassed a major milestone in 2018, when the country's Internet regulatory authority, China Internet Network Information Centre, announced that China had 802 million users. China was followed by India, with some 700 million users, with the United States third with 275 million users. However, in terms of penetration, in 2022 China had a 70% penetration rate compared to India's 60% and the United States's 90%. In 2022, 54% of the world's Internet users were based in Asia, 14% in Europe, 7% in North America, 10% in Latin America and the Caribbean, 11% in Africa, 4% in the Middle East and 1% in Oceania. In 2019, Kuwait, Qatar, the Falkland Islands, Bermuda and Iceland had the highest Internet penetration by the number of users, with 93% or more of the population with access. As of 2022, it was estimated that 5.4 billion people use the Internet, more than two-thirds of the world's population.
The prevalent language for communication via the Internet has always been English. This may be a result of the origin of the Internet, as well as the language's role as a lingua franca and as a world language. Early computer systems were limited to the characters in the American Standard Code for Information Interchange (ASCII), a subset of the Latin alphabet. After English (27%), the most requested languages on the World Wide Web are Chinese (25%), Spanish (8%), Japanese (5%), Portuguese and German (4% each), Arabic, French and Russian (3% each), and Korean (2%). The Internet's technologies have developed enough in recent years, especially in the use of Unicode, that good facilities are available for development and communication in the world's widely used languages. However, some glitches such as mojibake (incorrect display of some languages' characters) still remain.
In a US study in 2005, the percentage of men using the Internet was very slightly ahead of the percentage of women, although this difference reversed in those under 30. Men logged on more often, spent more time online, and were more likely to be broadband users, whereas women tended to make more use of opportunities to communicate (such as email). Men were more likely to use the Internet to pay bills, participate in auctions, and for recreation such as downloading music and videos. Men and women were equally likely to use the Internet for shopping and banking. In 2008, women significantly outnumbered men on most social networking services, such as Facebook and Myspace, although the ratios varied with age. Women watched more streaming content, whereas men downloaded more. Men were more likely to blog. Among those who blog, men were more likely to have a professional blog, whereas women were more likely to have a personal blog.
Several neologisms exist that refer to Internet users: Netizen (as in "citizen of the net") refers to those actively involved in improving online communities, the Internet in general or surrounding political affairs and rights such as free speech, Internaut refers to operators or technically highly capable users of the Internet, digital citizen refers to a person using the Internet in order to engage in society, politics, and government participation.
Usage

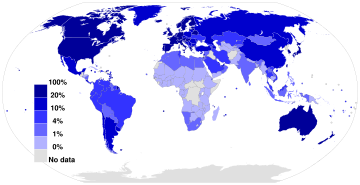
as a percentage of a country's populationSource: International Telecommunication Union.
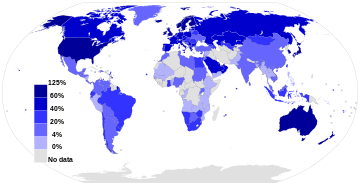
as a percentage of a country's populationSource: International Telecommunication Union.
The Internet allows greater flexibility in working hours and location, especially with the spread of unmetered high-speed connections. The Internet can be accessed almost anywhere by numerous means, including through mobile Internet devices. Mobile phones, datacards, handheld game consoles and cellular routers allow users to connect to the Internet wirelessly. Within the limitations imposed by small screens and other limited facilities of such pocket-sized devices, the services of the Internet, including email and the web, may be available. Service providers may restrict the services offered and mobile data charges may be significantly higher than other access methods.
Educational material at all levels from pre-school to post-doctoral is available from websites. Examples range from CBeebies, through school and high-school revision guides and virtual universities, to access to top-end scholarly literature through the likes of Google Scholar. For distance education, help with homework and other assignments, self-guided learning, whiling away spare time or just looking up more detail on an interesting fact, it has never been easier for people to access educational information at any level from anywhere. The Internet in general and the World Wide Web in particular are important enablers of both formal and informal education. Further, the Internet allows researchers (especially those from the social and behavioral sciences) to conduct research remotely via virtual laboratories, with profound changes in reach and generalizability of findings as well as in communication between scientists and in the publication of results.
The low cost and nearly instantaneous sharing of ideas, knowledge, and skills have made collaborative work dramatically easier, with the help of collaborative software. Not only can a group cheaply communicate and share ideas but the wide reach of the Internet allows such groups more easily to form. An example of this is the free software movement, which has produced, among other things, Linux, Mozilla Firefox, and OpenOffice.org (later forked into LibreOffice). Internet chat, whether using an IRC chat room, an instant messaging system, or a social networking service, allows colleagues to stay in touch in a very convenient way while working at their computers during the day. Messages can be exchanged even more quickly and conveniently than via email. These systems may allow files to be exchanged, drawings and images to be shared, or voice and video contact between team members.
Content management systems allow collaborating teams to work on shared sets of documents simultaneously without accidentally destroying each other's work. Business and project teams can share calendars as well as documents and other information. Such collaboration occurs in a wide variety of areas including scientific research, software development, conference planning, political activism and creative writing. Social and political collaboration is also becoming more widespread as both Internet access and computer literacy spread.
The Internet allows computer users to remotely access other computers and information stores easily from any access point. Access may be with computer security; i.e., authentication and encryption technologies, depending on the requirements. This is encouraging new ways of remote work, collaboration and information sharing in many industries. An accountant sitting at home can audit the books of a company based in another country, on a server situated in a third country that is remotely maintained by IT specialists in a fourth. These accounts could have been created by home-working bookkeepers, in other remote locations, based on information emailed to them from offices all over the world. Some of these things were possible before the widespread use of the Internet, but the cost of private leased lines would have made many of them infeasible in practice. An office worker away from their desk, perhaps on the other side of the world on a business trip or a holiday, can access their emails, access their data using cloud computing, or open a remote desktop session into their office PC using a secure virtual private network (VPN) connection on the Internet. This can give the worker complete access to all of their normal files and data, including email and other applications, while away from the office. It has been referred to among system administrators as the Virtual Private Nightmare, because it extends the secure perimeter of a corporate network into remote locations and its employees' homes. By the late 2010s the Internet had been described as "the main source of scientific information "for the majority of the global North population".
Social networking and entertainment
See also: Social networking service § Social impactMany people use the World Wide Web to access news, weather and sports reports, to plan and book vacations and to pursue their personal interests. People use chat, messaging and email to make and stay in touch with friends worldwide, sometimes in the same way as some previously had pen pals. Social networking services such as Facebook have created new ways to socialize and interact. Users of these sites are able to add a wide variety of information to pages, pursue common interests, and connect with others. It is also possible to find existing acquaintances, to allow communication among existing groups of people. Sites like LinkedIn foster commercial and business connections. YouTube and Flickr specialize in users' videos and photographs. Social networking services are also widely used by businesses and other organizations to promote their brands, to market to their customers and to encourage posts to "go viral". "Black hat" social media techniques are also employed by some organizations, such as spam accounts and astroturfing.
A risk for both individuals' and organizations' writing posts (especially public posts) on social networking services is that especially foolish or controversial posts occasionally lead to an unexpected and possibly large-scale backlash on social media from other Internet users. This is also a risk in relation to controversial offline behavior, if it is widely made known. The nature of this backlash can range widely from counter-arguments and public mockery, through insults and hate speech, to, in extreme cases, rape and death threats. The online disinhibition effect describes the tendency of many individuals to behave more stridently or offensively online than they would in person. A significant number of feminist women have been the target of various forms of harassment in response to posts they have made on social media, and Twitter in particular has been criticized in the past for not doing enough to aid victims of online abuse.
For organizations, such a backlash can cause overall brand damage, especially if reported by the media. However, this is not always the case, as any brand damage in the eyes of people with an opposing opinion to that presented by the organization could sometimes be outweighed by strengthening the brand in the eyes of others. Furthermore, if an organization or individual gives in to demands that others perceive as wrong-headed, that can then provoke a counter-backlash.
Some websites, such as Reddit, have rules forbidding the posting of personal information of individuals (also known as doxxing), due to concerns about such postings leading to mobs of large numbers of Internet users directing harassment at the specific individuals thereby identified. In particular, the Reddit rule forbidding the posting of personal information is widely understood to imply that all identifying photos and names must be censored in Facebook screenshots posted to Reddit. However, the interpretation of this rule in relation to public Twitter posts is less clear, and in any case, like-minded people online have many other ways they can use to direct each other's attention to public social media posts they disagree with.
Children also face dangers online such as cyberbullying and approaches by sexual predators, who sometimes pose as children themselves. Children may also encounter material that they may find upsetting, or material that their parents consider to be not age-appropriate. Due to naivety, they may also post personal information about themselves online, which could put them or their families at risk unless warned not to do so. Many parents choose to enable Internet filtering or supervise their children's online activities in an attempt to protect their children from inappropriate material on the Internet. The most popular social networking services, such as Facebook and Twitter, commonly forbid users under the age of 13. However, these policies are typically trivial to circumvent by registering an account with a false birth date, and a significant number of children aged under 13 join such sites anyway. Social networking services for younger children, which claim to provide better levels of protection for children, also exist.
The Internet has been a major outlet for leisure activity since its inception, with entertaining social experiments such as MUDs and MOOs being conducted on university servers, and humor-related Usenet groups receiving much traffic. Many Internet forums have sections devoted to games and funny videos. The Internet pornography and online gambling industries have taken advantage of the World Wide Web. Although many governments have attempted to restrict both industries' use of the Internet, in general, this has failed to stop their widespread popularity.
Another area of leisure activity on the Internet is multiplayer gaming. This form of recreation creates communities, where people of all ages and origins enjoy the fast-paced world of multiplayer games. These range from MMORPG to first-person shooters, from role-playing video games to online gambling. While online gaming has been around since the 1970s, modern modes of online gaming began with subscription services such as GameSpy and MPlayer. Non-subscribers were limited to certain types of game play or certain games. Many people use the Internet to access and download music, movies and other works for their enjoyment and relaxation. Free and fee-based services exist for all of these activities, using centralized servers and distributed peer-to-peer technologies. Some of these sources exercise more care with respect to the original artists' copyrights than others.
Internet usage has been correlated to users' loneliness. Lonely people tend to use the Internet as an outlet for their feelings and to share their stories with others, such as in the "I am lonely will anyone speak to me" thread. A 2017 book claimed that the Internet consolidates most aspects of human endeavor into singular arenas of which all of humanity are potential members and competitors, with fundamentally negative impacts on mental health as a result. While successes in each field of activity are pervasively visible and trumpeted, they are reserved for an extremely thin sliver of the world's most exceptional, leaving everyone else behind. Whereas, before the Internet, expectations of success in any field were supported by reasonable probabilities of achievement at the village, suburb, city or even state level, the same expectations in the Internet world are virtually certain to bring disappointment today: there is always someone else, somewhere on the planet, who can do better and take the now one-and-only top spot.
Cybersectarianism is a new organizational form that involves, "highly dispersed small groups of practitioners that may remain largely anonymous within the larger social context and operate in relative secrecy, while still linked remotely to a larger network of believers who share a set of practices and texts, and often a common devotion to a particular leader. Overseas supporters provide funding and support; domestic practitioners distribute tracts, participate in acts of resistance, and share information on the internal situation with outsiders. Collectively, members and practitioners of such sects construct viable virtual communities of faith, exchanging personal testimonies and engaging in the collective study via email, online chat rooms, and web-based message boards." In particular, the British government has raised concerns about the prospect of young British Muslims being indoctrinated into Islamic extremism by material on the Internet, being persuaded to join terrorist groups such as the so-called "Islamic State", and then potentially committing acts of terrorism on returning to Britain after fighting in Syria or Iraq.
Cyberslacking can become a drain on corporate resources; the average UK employee spent 57 minutes a day surfing the Web while at work, according to a 2003 study by Peninsula Business Services. Internet addiction disorder is excessive computer use that interferes with daily life. Nicholas G. Carr believes that Internet use has other effects on individuals, for instance improving skills of scan-reading and interfering with the deep thinking that leads to true creativity.
Electronic business
Electronic business (e-business) encompasses business processes spanning the entire value chain: purchasing, supply chain management, marketing, sales, customer service, and business relationship. E-commerce seeks to add revenue streams using the Internet to build and enhance relationships with clients and partners. According to International Data Corporation, the size of worldwide e-commerce, when global business-to-business and -consumer transactions are combined, equate to $16 trillion for 2013. A report by Oxford Economics added those two together to estimate the total size of the digital economy at $20.4 trillion, equivalent to roughly 13.8% of global sales.
While much has been written of the economic advantages of Internet-enabled commerce, there is also evidence that some aspects of the Internet such as maps and location-aware services may serve to reinforce economic inequality and the digital divide. Electronic commerce may be responsible for consolidation and the decline of mom-and-pop, brick and mortar businesses resulting in increases in income inequality.
Author Andrew Keen, a long-time critic of the social transformations caused by the Internet, has focused on the economic effects of consolidation from Internet businesses. Keen cites a 2013 Institute for Local Self-Reliance report saying brick-and-mortar retailers employ 47 people for every $10 million in sales while Amazon employs only 14. Similarly, the 700-employee room rental start-up Airbnb was valued at $10 billion in 2014, about half as much as Hilton Worldwide, which employs 152,000 people. At that time, Uber employed 1,000 full-time employees and was valued at $18.2 billion, about the same valuation as Avis Rent a Car and The Hertz Corporation combined, which together employed almost 60,000 people.
Remote work
Remote work is facilitated by tools such as groupware, virtual private networks, conference calling, videotelephony, and VoIP so that work may be performed from any location, most conveniently the worker's home. It can be efficient and useful for companies as it allows workers to communicate over long distances, saving significant amounts of travel time and cost. More workers have adequate bandwidth at home to use these tools to link their home to their corporate intranet and internal communication networks.
Collaborative publishing
Wikis have also been used in the academic community for sharing and dissemination of information across institutional and international boundaries. In those settings, they have been found useful for collaboration on grant writing, strategic planning, departmental documentation, and committee work. The United States Patent and Trademark Office uses a wiki to allow the public to collaborate on finding prior art relevant to examination of pending patent applications. Queens, New York has used a wiki to allow citizens to collaborate on the design and planning of a local park. The English Misplaced Pages has the largest user base among wikis on the World Wide Web and ranks in the top 10 among all sites in terms of traffic.
Politics and political revolutions
See also: Internet censorship, Mass surveillance, and Social media use in politics
The Internet has achieved new relevance as a political tool. The presidential campaign of Howard Dean in 2004 in the United States was notable for its success in soliciting donation via the Internet. Many political groups use the Internet to achieve a new method of organizing for carrying out their mission, having given rise to Internet activism. The New York Times suggested that social media websites, such as Facebook and Twitter, helped people organize the political revolutions in Egypt, by helping activists organize protests, communicate grievances, and disseminate information.
Many have understood the Internet as an extension of the Habermasian notion of the public sphere, observing how network communication technologies provide something like a global civic forum. However, incidents of politically motivated Internet censorship have now been recorded in many countries, including western democracies.
E-government is the use of technological communications devices, such as the Internet, to provide public services to citizens and other persons in a country or region. E-government offers opportunities for more direct and convenient citizen access to government and for government provision of services directly to citizens.
Philanthropy
The spread of low-cost Internet access in developing countries has opened up new possibilities for peer-to-peer charities, which allow individuals to contribute small amounts to charitable projects for other individuals. Websites, such as DonorsChoose and GlobalGiving, allow small-scale donors to direct funds to individual projects of their choice. A popular twist on Internet-based philanthropy is the use of peer-to-peer lending for charitable purposes. Kiva pioneered this concept in 2005, offering the first web-based service to publish individual loan profiles for funding. Kiva raises funds for local intermediary microfinance organizations that post stories and updates on behalf of the borrowers. Lenders can contribute as little as $25 to loans of their choice and receive their money back as borrowers repay. Kiva falls short of being a pure peer-to-peer charity, in that loans are disbursed before being funded by lenders and borrowers do not communicate with lenders themselves.
Security
Main article: Internet securityInternet resources, hardware, and software components are the target of criminal or malicious attempts to gain unauthorized control to cause interruptions, commit fraud, engage in blackmail or access private information.
Malware
Malware is malicious software used and distributed via the Internet. It includes computer viruses which are copied with the help of humans, computer worms which copy themselves automatically, software for denial of service attacks, ransomware, botnets, and spyware that reports on the activity and typing of users. Usually, these activities constitute cybercrime. Defense theorists have also speculated about the possibilities of hackers using cyber warfare using similar methods on a large scale.
Malware poses serious problems to individuals and businesses on the Internet. According to Symantec's 2018 Internet Security Threat Report (ISTR), malware variants number has increased to 669,947,865 in 2017, which is twice as many malware variants as in 2016. Cybercrime, which includes malware attacks as well as other crimes committed by computer, was predicted to cost the world economy US$6 trillion in 2021, and is increasing at a rate of 15% per year. Since 2021, malware has been designed to target computer systems that run critical infrastructure such as the electricity distribution network. Malware can be designed to evade antivirus software detection algorithms.
Surveillance
Main article: Computer and network surveillance See also: Signals intelligence and Mass surveillanceThe vast majority of computer surveillance involves the monitoring of data and traffic on the Internet. In the United States for example, under the Communications Assistance For Law Enforcement Act, all phone calls and broadband Internet traffic (emails, web traffic, instant messaging, etc.) are required to be available for unimpeded real-time monitoring by Federal law enforcement agencies. Packet capture is the monitoring of data traffic on a computer network. Computers communicate over the Internet by breaking up messages (emails, images, videos, web pages, files, etc.) into small chunks called "packets", which are routed through a network of computers, until they reach their destination, where they are assembled back into a complete "message" again. Packet Capture Appliance intercepts these packets as they are traveling through the network, in order to examine their contents using other programs. A packet capture is an information gathering tool, but not an analysis tool. That is it gathers "messages" but it does not analyze them and figure out what they mean. Other programs are needed to perform traffic analysis and sift through intercepted data looking for important/useful information. Under the Communications Assistance For Law Enforcement Act all U.S. telecommunications providers are required to install packet sniffing technology to allow Federal law enforcement and intelligence agencies to intercept all of their customers' broadband Internet and VoIP traffic.
The large amount of data gathered from packet capture requires surveillance software that filters and reports relevant information, such as the use of certain words or phrases, the access to certain types of web sites, or communicating via email or chat with certain parties. Agencies, such as the Information Awareness Office, NSA, GCHQ and the FBI, spend billions of dollars per year to develop, purchase, implement, and operate systems for interception and analysis of data. Similar systems are operated by Iranian secret police to identify and suppress dissidents. The required hardware and software were allegedly installed by German Siemens AG and Finnish Nokia.
Censorship
Main articles: Internet censorship and Internet freedom See also: Culture of fear and Great Firewall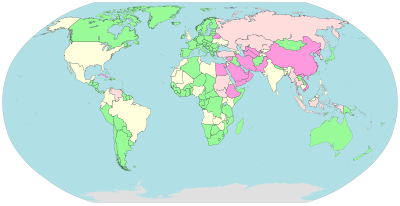
Unclassified / No data
Pervasive Substantial Selective Little or none
Some governments, such as those of Burma, Iran, North Korea, Mainland China, Saudi Arabia and the United Arab Emirates, restrict access to content on the Internet within their territories, especially to political and religious content, with domain name and keyword filters.
In Norway, Denmark, Finland, and Sweden, major Internet service providers have voluntarily agreed to restrict access to sites listed by authorities. While this list of forbidden resources is supposed to contain only known child pornography sites, the content of the list is secret. Many countries, including the United States, have enacted laws against the possession or distribution of certain material, such as child pornography, via the Internet but do not mandate filter software. Many free or commercially available software programs, called content-control software are available to users to block offensive websites on individual computers or networks in order to limit access by children to pornographic material or depiction of violence.
Performance
As the Internet is a heterogeneous network, its physical characteristics, including, for example the data transfer rates of connections, vary widely. It exhibits emergent phenomena that depend on its large-scale organization.
Traffic volume
| Graphs are unavailable due to technical issues. Updates on reimplementing the Graph extension, which will be known as the Chart extension, can be found on Phabricator and on MediaWiki.org. |
The volume of Internet traffic is difficult to measure because no single point of measurement exists in the multi-tiered, non-hierarchical topology. Traffic data may be estimated from the aggregate volume through the peering points of the Tier 1 network providers, but traffic that stays local in large provider networks may not be accounted for.
Outages
An Internet blackout or outage can be caused by local signaling interruptions. Disruptions of submarine communications cables may cause blackouts or slowdowns to large areas, such as in the 2008 submarine cable disruption. Less-developed countries are more vulnerable due to the small number of high-capacity links. Land cables are also vulnerable, as in 2011 when a woman digging for scrap metal severed most connectivity for the nation of Armenia. Internet blackouts affecting almost entire countries can be achieved by governments as a form of Internet censorship, as in the blockage of the Internet in Egypt, whereby approximately 93% of networks were without access in 2011 in an attempt to stop mobilization for anti-government protests.
Energy use
Estimates of the Internet's electricity usage have been the subject of controversy, according to a 2014 peer-reviewed research paper that found claims differing by a factor of 20,000 published in the literature during the preceding decade, ranging from 0.0064 kilowatt hours per gigabyte transferred (kWh/GB) to 136 kWh/GB. The researchers attributed these discrepancies mainly to the year of reference (i.e. whether efficiency gains over time had been taken into account) and to whether "end devices such as personal computers and servers are included" in the analysis.
In 2011, academic researchers estimated the overall energy used by the Internet to be between 170 and 307 GW, less than two percent of the energy used by humanity. This estimate included the energy needed to build, operate, and periodically replace the estimated 750 million laptops, a billion smart phones and 100 million servers worldwide as well as the energy that routers, cell towers, optical switches, Wi-Fi transmitters and cloud storage devices use when transmitting Internet traffic. According to a non-peer-reviewed study published in 2018 by The Shift Project (a French think tank funded by corporate sponsors), nearly 4% of global CO2 emissions could be attributed to global data transfer and the necessary infrastructure. The study also said that online video streaming alone accounted for 60% of this data transfer and therefore contributed to over 300 million tons of CO2 emission per year, and argued for new "digital sobriety" regulations restricting the use and size of video files.
See also
- Crowdfunding
- Crowdsourcing
- Cyberspace
- Darknet
- Deep web
- Hyphanet
- Internet industry jargon
- Index of Internet-related articles
- Internet metaphors
- Internet video
- "Internets"
- Outline of the Internet
Notes
- See Capitalization of Internet
- Despite the name, TCP/IP also includes UDP traffic, which is significant.
- Due to legal concerns the OpenNet Initiative does not check for filtering of child pornography and because their classifications focus on technical filtering, they do not include other types of censorship.
References
- Amogh Dhamdhere. "Internet Traffic Characterization". Retrieved 6 May 2022.
- ^ "A Flaw in the Design". The Washington Post. 30 May 2015. Archived from the original on 8 November 2020. Retrieved 20 February 2020.
The Internet was born of a big idea: Messages could be chopped into chunks, sent through a network in a series of transmissions, then reassembled by destination computers quickly and efficiently. Historians credit seminal insights to Welsh scientist Donald W. Davies and American engineer Paul Baran. ... The most important institutional force ... was the Pentagon's Advanced Research Projects Agency (ARPA) ... as ARPA began work on a groundbreaking computer network, the agency recruited scientists affiliated with the nation's top universities.
- Yates, David M. (1997). Turing's Legacy: A History of Computing at the National Physical Laboratory 1945-1995. National Museum of Science and Industry. pp. 132–4. ISBN 978-0-901805-94-2.
Davies's invention of packet switching and design of computer communication networks ... were a cornerstone of the development which led to the Internet
- Abbate 1999, p. 3 "The manager of the ARPANET project, Lawrence Roberts, assembled a large team of computer scientists ... and he drew on the ideas of network experimenters in the United States and the United Kingdom. Cerf and Kahn also enlisted the help of computer scientists from England, France and the United States"
- "The Computer History Museum, SRI International, and BBN Celebrate the 40th Anniversary of First ARPANET Transmission, Precursor to Today's Internet". SRI International. 27 October 2009. Archived from the original on 29 March 2019. Retrieved 25 September 2017.
But the ARPANET itself had now become an island, with no links to the other networks that had sprung up. By the early 1970s, researchers in France, the UK, and the U.S. began developing ways of connecting networks to each other, a process known as internetworking.
- by Vinton Cerf, as told to Bernard Aboba (1993). "How the Internet Came to Be". Archived from the original on 26 September 2017. Retrieved 25 September 2017.
We began doing concurrent implementations at Stanford, BBN, and University College London. So effort at developing the Internet protocols was international from the beginning.
- Stewart, Bill (January 2000). "Internet History – One Page Summary". The Living Internet. Archived from the original on 2 July 2014.
- Wright, Edmund, ed. (2006). The Desk Encyclopedia of World History. New York: Oxford University Press. p. 312. ISBN 978-0-7394-7809-7.
- "#3 1982: the ARPANET community grows" in 40 maps that explain the internet Archived 6 March 2017 at the Wayback Machine, Timothy B. Lee, Vox Conversations, 2 June 2014. Retrieved 27 June 2014.
- Strickland, Jonathan (3 March 2008). "How Stuff Works: Who owns the Internet?". Archived from the original on 19 June 2014. Retrieved 27 June 2014.
- Hoffman, P.; Harris, S. (September 2006). The Tao of IETF: A Novice's Guide to Internet Engineering Task Force. IETF. doi:10.17487/RFC4677. RFC 4677.
- "New Seven Wonders panel". USA Today. 27 October 2006. Archived from the original on 15 July 2010. Retrieved 31 July 2010.
- "Internetted". Oxford English Dictionary (Online ed.). Oxford University Press. (Subscription or participating institution membership required.) nineteenth-century use as an adjective.
- "United States Army Field Manual FM 24-6 Radio Operator's Manual Army Ground Forces June 1945". United States War Department. 18 September 2023.
- ^ Cerf, Vint; Dalal, Yogen; Sunshine, Carl (December 1974). Specification of Internet Transmission Control Protocol. IETF. doi:10.17487/RFC0675. RFC 675.
- ^ Corbett, Philip B. (1 June 2016). "It's Official: The 'Internet' Is Over". The New York Times. ISSN 0362-4331. Archived from the original on 14 October 2020. Retrieved 29 August 2020.
- ^ Herring, Susan C. (19 October 2015). "Should You Be Capitalizing the Word 'Internet'?". Wired. ISSN 1059-1028. Archived from the original on 31 October 2020. Retrieved 29 August 2020.
- Coren, Michael J. (2 June 2016). "One of the internet's inventors thinks it should still be capitalized". Quartz. Archived from the original on 27 September 2020. Retrieved 8 September 2020.
- "World Wide Web Timeline". Pews Research Center. 11 March 2014. Archived from the original on 29 July 2015. Retrieved 1 August 2015.
- "HTML 4.01 Specification". World Wide Web Consortium. Archived from the original on 6 October 2008. Retrieved 13 August 2008.
he link (or hyperlink, or Web link) the basic hypertext construct. A link is a connection from one Web resource to another. Although a simple concept, the link has been one of the primary forces driving the success of the Web.
- Waldrop, Mitch (2015). "DARPA and the Internet Revolution" (PDF). darpa.mil. Retrieved 16 May 2024.
- Lee, J.A.N.; Rosin, Robert F (1992). "Time-Sharing at MIT". IEEE Annals of the History of Computing. 14 (1): 16. doi:10.1109/85.145316. ISSN 1058-6180. S2CID 30976386. Retrieved 3 October 2022.
- F. J. Corbató, et al., The Compatible Time-Sharing System A Programmer's Guide (MIT Press, 1963) ISBN 978-0-262-03008-3. "To establish the context of the present work, it is informative to trace the development of time-sharing at MIT. Shortly after the first paper on time-shared computers by C. Strachey at the June 1959 UNESCO Information Processing conference, H.M. Teager and J. McCarthy delivered an unpublished paper "Time-Shared Program Testing" at the August 1959 ACM Meeting."
- "Inductee Details – Paul Baran". National Inventors Hall of Fame. Archived from the original on 6 September 2017. Retrieved 6 September 2017; "Inductee Details – Donald Watts Davies". National Inventors Hall of Fame. Archived from the original on 6 September 2017. Retrieved 6 September 2017.
- Hauben, Michael; Hauben, Ronda (1997). "5 The Vision of Interactive Computing And the Future". Netizens: On the History and Impact of Usenet and the Internet (PDF). Wiley. ISBN 978-0-8186-7706-9. Archived (PDF) from the original on 3 January 2021. Retrieved 2 March 2020.
- Zelnick, Bob; Zelnick, Eva (2013). The Illusion of Net Neutrality: Political Alarmism, Regulatory Creep and the Real Threat to Internet Freedom. Hoover Press. ISBN 978-0-8179-1596-4. Archived from the original on 10 January 2021. Retrieved 7 May 2020.
- Peter, Ian (2004). "So, who really did invent the Internet?". The Internet History Project. Archived from the original on 3 September 2011. Retrieved 27 June 2014.
- Gromov, Gregory (1995). "Roads and Crossroads of Internet History". Archived from the original on 27 January 2016.
- Hafner, Katie (1998). Where Wizards Stay Up Late: The Origins of the Internet. Simon & Schuster. ISBN 978-0-684-83267-8.
- Hauben, Ronda (2001). "From the ARPANET to the Internet". Archived from the original on 21 July 2009. Retrieved 28 May 2009.
- "Internet Pioneers Discuss the Future of Money, Books, and Paper in 1972". Paleofuture. 23 July 2013. Archived from the original on 17 October 2020. Retrieved 31 August 2020.
- Townsend, Anthony (2001). "The Internet and the Rise of the New Network Cities, 1969–1999". Environment and Planning B: Planning and Design. 28 (1): 39–58. Bibcode:2001EnPlB..28...39T. doi:10.1068/b2688. ISSN 0265-8135. S2CID 11574572.
- Kim, Byung-Keun (2005). Internationalising the Internet the Co-evolution of Influence and Technology. Edward Elgar. pp. 51–55. ISBN 978-1-84542-675-0.
- "NORSAR and the Internet". NORSAR. Archived from the original on 21 January 2013.
- Kirstein, P.T. (1999). "Early experiences with the Arpanet and Internet in the United Kingdom" (PDF). IEEE Annals of the History of Computing. 21 (1): 38–44. doi:10.1109/85.759368. ISSN 1934-1547. S2CID 1558618. Archived from the original (PDF) on 7 February 2020.
- Leiner, Barry M. "Brief History of the Internet: The Initial Internetting Concepts". Internet Society. Archived from the original on 9 April 2016. Retrieved 27 June 2014.
- ^ Cerf, V.; Kahn, R. (1974). "A Protocol for Packet Network Intercommunication" (PDF). IEEE Transactions on Communications. 22 (5): 637–648. doi:10.1109/TCOM.1974.1092259. ISSN 1558-0857. Archived (PDF) from the original on 13 September 2006.
The authors wish to thank a number of colleagues for helpful comments during early discussions of international network protocols, especially R. Metcalfe, R. Scantlebury, D. Walden, and H. Zimmerman; D. Davies and L. Pouzin who constructively commented on the fragmentation and accounting issues; and S. Crocker who commented on the creation and destruction of associations.
- "The internet's fifth man". The Economist. 30 November 2013. ISSN 0013-0613. Archived from the original on 19 April 2020. Retrieved 22 April 2020.
In the early 1970s Mr Pouzin created an innovative data network that linked locations in France, Italy and Britain. Its simplicity and efficiency pointed the way to a network that could connect not just dozens of machines, but millions of them. It captured the imagination of Dr Cerf and Dr Kahn, who included aspects of its design in the protocols that now power the internet.
- Schatt, Stan (1991). Linking LANs: A Micro Manager's Guide. McGraw-Hill. p. 200. ISBN 0-8306-3755-9.
- Frazer, Karen D. (1995). "NSFNET: A Partnership for High-Speed Networking, Final Report 1987–1995" (PDF). Merit Network, Inc. Archived from the original (PDF) on 10 February 2015.
- Ben Segal (1995). "A Short History of Internet Protocols at CERN". Archived from the original on 8 June 2023. Retrieved 14 October 2011.
- Réseaux IP Européens (RIPE)
- "Internet History in Asia". 16th APAN Meetings/Advanced Network Conference in Busan. Archived from the original on 1 February 2006. Retrieved 25 December 2005.
- "The History of NORDUnet" (PDF). Archived from the original (PDF) on 4 March 2016.
- Clarke, Roger. "Origins and Nature of the Internet in Australia". Archived from the original on 9 February 2021. Retrieved 21 January 2014.
- Zakon, Robert (November 1997). RFC 2235. IETF. p. 8. doi:10.17487/RFC2235. Retrieved 2 December 2020.
- "InfoWorld". 25 September 1989. Archived from the original on 29 January 2017 – via Google Books.
- "INTERNET MONTHLY REPORTS". February 1990. Archived from the original on 25 May 2017. Retrieved 28 November 2020.
- Berners-Lee, Tim. "The Original HTTP as defined in 1991". W3C.org. Archived from the original on 5 June 1997.
- "The website of the world's first-ever web server". info.cern.ch. Archived from the original on 5 January 2010.
- "Stanford Federal Credit Union Pioneers Online Financial Services" (Press release). 21 June 1995. Archived from the original on 21 December 2018. Retrieved 21 December 2018.
- "History – About us – OP Group". Archived from the original on 21 December 2018. Retrieved 21 December 2018.
- Harris, Susan R.; Gerich, Elise (April 1996). "Retiring the NSFNET Backbone Service: Chronicling the End of an Era". ConneXions. 10 (4). Archived from the original on 17 August 2013.
- "Measuring digital development: Facts and figures 2023". Telecommunication Development Bureau, International Telecommunication Union (ITU). Retrieved 14 June 2024.
- "Total Midyear Population for the World: 1950-2050"". International Programs Center for Demographic and Economic Studies, U.S. Census Bureau. Archived from the original on 17 April 2017. Retrieved 28 February 2020.
- Jindal, R. P. (2009). "From millibits to terabits per second and beyond - over 60 years of innovation". 2009 2nd International Workshop on Electron Devices and Semiconductor Technology. Vol. 49. pp. 1–6. doi:10.1109/EDST.2009.5166093. ISBN 978-1-4244-3831-0. S2CID 25112828. Archived from the original on 23 August 2019. Retrieved 24 August 2019.
- Ward, Mark (3 August 2006). "How the web went world wide". Technology Correspondent. BBC News. Archived from the original on 21 November 2011. Retrieved 24 January 2011.
- "Brazil, Russia, India and China to Lead Internet Growth Through 2011". Clickz.com. Archived from the original on 4 October 2008. Retrieved 28 May 2009.
- Coffman, K.G; Odlyzko, A.M. (2 October 1998). "The size and growth rate of the Internet" (PDF). AT&T Labs. Archived from the original (PDF) on 14 June 2007. Retrieved 21 May 2007.
- Comer, Douglas (2006). The Internet book. Prentice Hall. p. 64. ISBN 978-0-13-233553-9.
- "World Internet Users and Population Stats". Internet World Stats. Miniwatts Marketing Group. 22 June 2011. Archived from the original on 23 June 2011. Retrieved 23 June 2011.
- Hilbert, Martin; López, Priscila (April 2011). "The World's Technological Capacity to Store, Communicate, and Compute Information". Science. 332 (6025): 60–65. Bibcode:2011Sci...332...60H. doi:10.1126/science.1200970. PMID 21310967. S2CID 206531385.
- Klein, Hans (2004). "ICANN and Non-Territorial Sovereignty: Government Without the Nation State". Internet and Public Policy Project. Georgia Institute of Technology. Archived from the original on 24 May 2013.
- Packard, Ashley (2010). Digital Media Law. Wiley-Blackwell. p. 65. ISBN 978-1-4051-8169-3.
- McCarthy, Kieren (1 July 2005). "Bush administration annexes internet". The Register. Archived from the original on 19 September 2011.
- Mueller, Milton L. (2010). Networks and States: The Global Politics of Internet Governance. MIT Press. p. 61. ISBN 978-0-262-01459-5.
- "ICG Applauds Transfer of IANA Stewardship". IANA Stewardship Transition Coordination Group (ICG). Archived from the original on 12 July 2017. Retrieved 8 June 2017.
- "Internet Society (ISOC) All About The Internet: History of the Internet". ISOC. Archived from the original on 27 November 2011. Retrieved 19 December 2013.
- Pasternak, Sean B. (7 March 2006). "Toronto Hydro to Install Wireless Network in Downtown Toronto". Bloomberg. Archived from the original on 10 April 2006. Retrieved 8 August 2011.
- "Mobile and Tablet Internet Usage Exceeds Desktop for First Time Worldwide". StatCounter: Global Stats, Press Release. 1 November 2016. Archived from the original on 1 November 2016.
StatCounter Global Stats finds that mobile and tablet devices accounted for 51.3% of Internet usage worldwide in October compared to 48.7% by desktop.
- "World Telecommunication/ICT Indicators Database 2020 (24th Edition/July 2020)". International Telecommunication Union (ITU). 2017a. Archived from the original on 21 April 2019.
Key ICT indicators for developed and developing countries and the world (totals and penetration rates). World Telecommunication/ICT Indicators database
- ^ World Trends in Freedom of Expression and Media Development Global Report 2017/2018 (PDF). UNESCO. 2018. Archived (PDF) from the original on 20 September 2018. Retrieved 29 May 2018.
- ^ "GSMA The Mobile Economy 2019". 11 March 2019. Archived from the original on 11 March 2019. Retrieved 28 November 2020.
- Galpaya, Helani (12 April 2019). "Zero-rating in Emerging Economies" (PDF). Global Commission on Internet Governance. Archived (PDF) from the original on 12 April 2019. Retrieved 28 November 2020.
- "Alliance for Affordable Internet (A4AI). 2015. Models of Mobile Data Services in Developing Countries. Research brief. The Impacts of Emerging Mobile Data Services in Developing Countries".
- Gillwald, Alison; Chair, Chenai; Futter, Ariel; Koranteng, Kweku; Odufuwa, Fola; Walubengo, John (12 September 2016). "Much Ado About Nothing? Zero Rating in the African Context" (PDF). Researchictafrica. Archived (PDF) from the original on 16 December 2020. Retrieved 28 November 2020.
- ^ J. Postel, ed. (September 1981). Internet Protocol, DARPA Internet Program Protocol Specification. IETF. doi:10.17487/RFC0791. RFC 791. Updated by RFC 1349, 2474, 6864
- Huston, Geoff. "IPv4 Address Report, daily generated". Archived from the original on 1 April 2009. Retrieved 20 May 2009.
- S. Deering; R. Hinden (December 1995). Internet Protocol, Version 6 (IPv6) Specification. Network Working Group. doi:10.17487/RFC1883. RFC 1883.
- S. Deering; R. Hinden (December 1998). Internet Protocol, Version 6 (IPv6) Specification. Network Working Group. doi:10.17487/RFC2460. RFC 2460.
- S. Deering; R. Hinden (July 2017). Internet Protocol, Version 6 (IPv6) Specification. IETF. doi:10.17487/RFC8200. RFC 8200.
- "Notice of Internet Protocol version 4 (IPv4) Address Depletion" (PDF). Archived from the original (PDF) on 7 January 2010. Retrieved 7 August 2009.
- Jeffrey Mogul; Jon Postel (August 1985). Internet Standard Subnetting Procedure. IETF. doi:10.17487/RFC0950. RFC 950. Updated by RFC 6918.
- Fisher, Tim. "How to Find Your Default Gateway IP Address". Lifewire. Archived from the original on 25 February 2019. Retrieved 25 February 2019.
- "Default Gateway". techopedia.com. 30 June 2020. Archived from the original on 26 October 2020.
- "IETF Home Page". Ietf.org. Archived from the original on 18 June 2009. Retrieved 20 June 2009.
- "The Difference Between the Internet and the World Wide Web". Webopedia. QuinStreet Inc. 24 June 2010. Archived from the original on 2 May 2014. Retrieved 1 May 2014.
- "IAB Internet advertising revenue report: 2012 full year results" (PDF). PricewaterhouseCoopers, Internet Advertising Bureau. April 2013. Archived from the original (PDF) on 4 October 2014. Retrieved 12 June 2013.
- Brown, Ron (26 October 1972). "Fax invades the mail market". New Scientist. 56 (817): 218–221.
- Luckett, Herbert P. (March 1973). "What's News: Electronic-mail delivery gets started". Popular Science. 202 (3): 85.
- Booth, C (2010). "Chapter 2: IP Phones, Software VoIP, and Integrated and Mobile VoIP". Library Technology Reports. 46 (5): 11–19.
- Morrison, Geoff (18 November 2010). "What to know before buying a 'connected' TV – Technology & science – Tech and gadgets – Tech Holiday Guide". NBC News. Archived from the original on 12 February 2020. Retrieved 8 August 2011.
- "Press". YouTube. Archived from the original on 11 November 2017. Retrieved 19 August 2020.
- "YouTube now defaults to HTML5". YouTube Engineering and Developers Blog. Archived from the original on 10 September 2018. Retrieved 10 September 2018.
- Carlson, Kathie; Flanagin, Michael N.; Martin, Kathleen; Martin, Mary E.; Mendelsohn, John; Rodgers, Priscilla Young; Ronnberg, Ami; Salman, Sherry; Wesley, Deborah A. (2010). Arm, Karen; Ueda, Kako; Thulin, Anne; Langerak, Allison; Kiley, Timothy Gus; Wolff, Mary (eds.). The Book of Symbols: Reflections on Archetypal Images. Köln: Taschen. p. 518. ISBN 978-3-8365-1448-4.
- Ritchie, Hannah; Roser, Max (2 October 2017). "Technology Adoption". Our World in Data. Archived from the original on 12 October 2019. Retrieved 12 October 2019.
- "Individuals using the Internet 2005 to 2014" Archived 28 May 2015 at the Wayback Machine, Key ICT indicators for developed and developing countries and the world (totals and penetration rates), International Telecommunication Union (ITU). Retrieved 25 May 2015.
- "Internet users per 100 inhabitants 1997 to 2007" Archived 17 May 2015 at the Wayback Machine, ICT Data and Statistics (IDS), International Telecommunication Union (ITU). Retrieved 25 May 2015.
- Internet users graphs Archived 9 May 2020 at the Wayback Machine, Market Information and Statistics, International Telecommunication Union
- "Google Earth demonstrates how technology benefits RI's civil society, govt". Antara News. 26 May 2011. Archived from the original on 29 October 2012. Retrieved 19 November 2012.
- Steve Dent (25 November 2014). "There are now 3 billion Internet users, mostly in rich countries". Archived from the original on 28 November 2014. Retrieved 25 November 2014.
- "Statistical Report on Internet Development in China" (PDF). Cnnic.com. January 2018. Archived (PDF) from the original on 12 April 2019.
- "World Internet Users Statistics and 2019 World Population Stats". internetworldstats.com. Archived from the original on 24 November 2017. Retrieved 17 March 2019.
- "World Internet Usage Statistics News and Population Stats". 30 June 2023. Archived from the original on 19 March 2017. Retrieved 14 December 2023.
- "Percentage of Individuals using the Internet 2000–2012" Archived 9 February 2014 at the Wayback Machine, International Telecommunication Union (Geneva), June 2013. Retrieved 22 June 2013.
- "World Internet Users Statistics and 2023 World Population Stats". Internet World Stats. Archived from the original on 19 March 2024.
- ^ "Top Ten Internet Languages". Internet World Stats, Miniwatts Marketing Group. 18 March 2012. Archived from the original on 26 April 2012. Retrieved 22 April 2012.
- Fallows, Deborah (28 December 2005). "How Women and Men Use the Internet". Pew Research Center. Archived from the original on 8 June 2023.
- "Rapleaf Study Reveals Gender and Age Data of Social Network Users". Rapleaf. 29 July 2008. Archived from the original on 20 March 2009.
- "Women Ahead of Men in Online Tv, Dvr, Games, And Social Media". Entrepreneur. 1 May 2008. Archived from the original on 16 September 2008. Retrieved 8 August 2011.
- "State of the Blogosphere". Technorati. Archived from the original on 2 October 2009. Retrieved 8 August 2011.
- Seese, Michael (2009). Scrappy Information Security. Happy About. p. 130. ISBN 978-1-60005-132-6. Archived from the original on 5 September 2017. Retrieved 5 June 2015.
- "netizen", Dictionary.com. Archived 21 April 2012 at the Wayback Machine.
- Hauben, Michael (5 June 1996). "The Net and Netizens". Columbia University. Archived from the original on 4 June 2011.
- Leiner, B M.; Cerf, V G.; Clark, D D.; Kahn, R E.; Kleinrock, L; Lynch, D C.; Postel, J; Roberts, L G.; Wolff, S (10 December 2003). "A Brief History of the Internet". the Internet Society. Archived from the original on 4 June 2007.
- "internaut". Oxford Dictionaries. Archived from the original on 13 June 2015. Retrieved 6 June 2015.
- Mossberger, Karen; Tolbert, Caroline J.; McNeal, Ramona S. (2011). Digital Citizenship – The Internet, Society and Participation. SPIE Press. ISBN 978-0-8194-5606-9.
- "Usage of content languages for websites". W3Techs. Archived from the original on 17 July 2012. Retrieved 26 April 2013.
- "Fixed (wired)-broadband subscriptions per 100 inhabitants 2012" Archived 26 July 2019 at the Wayback Machine, Dynamic Report, ITU ITC EYE, International Telecommunication Union. Retrieved 29 June 2013.
- "Active mobile-broadband subscriptions per 100 inhabitants 2012" Archived 26 July 2019 at the Wayback Machine, Dynamic Report, ITU ITC EYE, International Telecommunication Union. Retrieved 29 June 2013.
- Reips, U.-D. (2008). "How Internet-mediated research changes science". Psychological aspects of cyberspace: Theory, research, applications. Cambridge: Cambridge University Press. pp. 268–294. ISBN 978-0-521-69464-3. Archived from the original on 9 August 2014.
- "The Virtual Private Nightmare: VPN". Librenix. 4 August 2004. Archived from the original on 15 May 2011. Retrieved 21 July 2010.
- Dariusz Jemielniak; Aleksandra Przegalinska (2020). Collaborative Society. MIT Press. ISBN 978-0-262-35645-9. Archived from the original on 23 November 2020. Retrieved 26 November 2020.
- Moore, Keith (27 July 2013). "Twitter 'report abuse' button calls after rape threats". BBC News. Archived from the original on 4 September 2014. Retrieved 7 December 2014.
- Kessler, Sarah (11 October 2010). "5 Fun and Safe Social Networks for Children". Mashable. Archived from the original on 20 December 2014. Retrieved 7 December 2014.
- ^ "Communication in our life". StudFiles (in Russian). Retrieved 16 May 2023.
- Goldman, Russell (22 January 2008). "Do It Yourself! Amateur Porn Stars Make Bank". ABC News. Archived from the original on 30 December 2011.
- Spohn, Dave (15 December 2009). "Top Online Game Trends of the Decade". About.com. Archived from the original on 29 September 2011.
- Spohn, Dave (2 June 2011). "Internet Game Timeline: 1963–2004". About.com. Archived from the original on 25 April 2006.
- Carole Hughes; Boston College. "The Relationship Between Internet Use and Loneliness Among College Students". Boston College. Archived from the original on 7 November 2015. Retrieved 11 August 2011.
- Barker, Eric (2017). Barking Up the Wrong Tree. HarperCollins. pp. 235–236. ISBN 978-0-06-241604-9.
- Thornton, Patricia M. (2003). "The New Cybersects: Resistance and Repression in the Reform era". In Perry, Elizabeth; Selden, Mark (eds.). Chinese Society: Change, Conflict and Resistance (2 ed.). London and New York: Routledge. pp. 149–150. ISBN 978-0-415-56074-0.
- "Net abuse hits small city firms". The Scotsman. Edinburgh. 11 September 2003. Archived from the original on 20 October 2012. Retrieved 7 August 2009.
- Carr, Nicholas G. (2010). The Shallows: What the Internet Is Doing to Our Brains. W.W. Norton. p. 276. ISBN 978-0-393-07222-8.
- "The New Digital Economy: How it will transform business" (PDF). Oxford Economics. 2 July 2011. Archived from the original (PDF) on 6 July 2014.
- Badger, Emily (6 February 2013). "How the Internet Reinforces Inequality in the Real World". The Atlantic. Archived from the original on 11 February 2013. Retrieved 13 February 2013.
- "E-commerce will make the shopping mall a retail wasteland". ZDNet. 17 January 2013. Archived from the original on 19 February 2013.
- "'Free Shipping Day' Promotion Spurs Late-Season Online Spending Surge, Improving Season-to-Date Growth Rate to 16 Percent vs. Year Ago". Comscore. 23 December 2012. Archived from the original on 28 January 2013.
- "The Death of the American Shopping Mall". The Atlantic – Cities. 26 December 2012. Archived from the original on 15 February 2013.
- Harris, Michael (2 January 2015). "Book review: 'The Internet Is Not the Answer' by Andrew Keen". The Washington Post. Archived from the original on 20 January 2015. Retrieved 25 January 2015.
- MM Wanderley; D Birnbaum; J Malloch (2006). New Interfaces For Musical Expression. IRCAM – Centre Pompidou. p. 180. ISBN 978-2-84426-314-8.
- Nancy T. Lombardo (June 2008). "Putting Wikis to Work in Libraries". Medical Reference Services Quarterly. 27 (2): 129–145. doi:10.1080/02763860802114223. PMID 18844087. S2CID 11552140.
- Noveck, Beth Simone (March 2007). "Misplaced Pages and the Future of Legal Education". Journal of Legal Education. 57 (1). Archived from the original on 3 July 2014.(subscription required)
- "WikiStats by S23". S23Wiki. 3 April 2008. Archived from the original on 25 August 2014. Retrieved 7 April 2007.
- "Alexa Web Search – Top 500". Alexa Internet. Archived from the original on 2 March 2015. Retrieved 2 March 2015.
- "The Arab Uprising's Cascading Effects". Miller-mccune.com. 23 February 2011. Archived from the original on 27 February 2011. Retrieved 27 February 2011.
- "The Role of the Internet in Democratic Transition: Case Study of the Arab Spring" (PDF). 5 July 2012. Archived from the original (PDF) on 5 July 2012., Davit Chokoshvili, Master's Thesis, June 2011
- Kirkpatrick, David D. (9 February 2011). "Wired and Shrewd, Young Egyptians Guide Revolt". The New York Times. Archived from the original on 29 January 2017.
- Ronald Deibert; John Palfrey; Rafal Rohozinski; Jonathan Zittrain (2008). Access Denied: The Practice and Policy of Global Internet Filtering. MIT Press. ISBN 978-0-262-29072-2.
- Larry Diamond; Marc F. Plattner (2012). Liberation Technology: Social Media and the Struggle for Democracy. JHU Press. ISBN 978-1-4214-0568-1.
- Manoharan, Aroon P.; Melitski, James; Holzer, Marc (20 January 2022). "Digital Governance: An Assessment of Performance and Best Practices". Public Organization Review. 23 (1): 265–283. doi:10.1007/s11115-021-00584-8. ISSN 1573-7098. PMC 8769785.
- Caves, R. W. (2004). Encyclopedia of the City. Routledge. p. 180.
- Roodman, David (2 October 2009). "Kiva Is Not Quite What It Seems". Center for Global Development. Archived from the original on 10 February 2010. Retrieved 16 January 2010.
- Strom, Stephanie (9 November 2009). "Confusion on Where Money Lent via Kiva Goes". The New York Times. p. 6. Archived from the original on 29 January 2017.
- Gralla, Preston (2007). How the Internet Works. Indianapolis: Que Pub. ISBN 978-0-7897-2132-7.
- Andriole, Steve. "Cyberwarfare Will Explode In 2020 (Because It's Cheap, Easy And Effective)". Forbes. Retrieved 18 May 2021.
- Kim, Jin-Young; Bu, Seok-Jun; Cho, Sung-Bae (1 September 2018). "Zero-day malware detection using transferred generative adversarial networks based on deep autoencoders". Information Sciences. 460–461: 83–102. doi:10.1016/j.ins.2018.04.092. ISSN 0020-0255. S2CID 51882216. Retrieved 2 December 2021.
- Razak, Mohd Faizal Ab; Anuar, Nor Badrul; Salleh, Rosli; Firdaus, Ahmad (1 November 2016). "The rise of "malware": Bibliometric analysis of malware study". Journal of Network and Computer Applications. 75: 58–76. doi:10.1016/j.jnca.2016.08.022. Retrieved 30 April 2022.
- Xiao, Fei; Sun, Yi; Du, Donggao; Li, Xuelei; Luo, Min (21 March 2020). "A Novel Malware Classification Method Based on Crucial Behavior". Mathematical Problems in Engineering. 2020: 1–12. doi:10.1155/2020/6804290. ISSN 1024-123X.
- Morgan, Steve (13 November 2020). "Cybercrime To Cost The World $10.5 Trillion Annually By 2025". Cybercrime magazine website. Cybersecurity ventures. Archived from the original on 5 March 2022. Retrieved 5 March 2022.
- Eder-Neuhauser, Peter; Zseby, Tanja; Fabini, Joachim (1 June 2019). "Malware propagation in smart grid networks: metrics, simulation and comparison of three malware types". Journal of Computer Virology and Hacking Techniques. 15 (2): 109–125. doi:10.1007/s11416-018-0325-y. ISSN 2263-8733. S2CID 255164530.
- Razak, Mohd Faizal Ab; Anuar, Nor Badrul; Salleh, Rosli; Firdaus, Ahmad (1 November 2016). "The rise of "malware": Bibliometric analysis of malware study". Journal of Network and Computer Applications. 75: 58–76. doi:10.1016/j.jnca.2016.08.022. ISSN 1084-8045.
- Spring, Tom (12 June 2023). "Obfuscation tool 'BatCloak' can evade 80% of AV engines". SC Media. Retrieved 21 December 2023.
- Nam, Nguyen (10 January 2023). "Kiểm tra ip". Retrieved 21 December 2023.
- Amos, Zac. "How Ransomware Can Evade Antivirus Software". gca.isa.org. Retrieved 21 December 2023.
- Diffie, Whitfield; Susan Landau (August 2008). "Internet Eavesdropping: A Brave New World of Wiretapping". Scientific American. Archived from the original on 13 November 2008. Retrieved 13 March 2009.
- "CALEA Archive". Electronic Frontier Foundation (website). Archived from the original on 25 October 2008. Retrieved 14 March 2009.
- "CALEA: The Perils of Wiretapping the Internet". Electronic Frontier Foundation (website). Archived from the original on 16 March 2009. Retrieved 14 March 2009.
- "CALEA: Frequently Asked Questions". Electronic Frontier Foundation (website). 20 September 2007. Archived from the original on 1 May 2009. Retrieved 14 March 2009.
- "American Council on Education vs. FCC, Decision, United States Court of Appeals for the District of Columbia Circuit" (PDF). 9 June 2006. Archived from the original (PDF) on 7 September 2012. Retrieved 8 September 2013.
- Hill, Michael (11 October 2004). "Government funds chat room surveillance research". USA Today. Associated Press. Archived from the original on 11 May 2010. Retrieved 19 March 2009.
- McCullagh, Declan (30 January 2007). "FBI turns to broad new wiretap method". ZDNet News. Archived from the original on 7 April 2010. Retrieved 13 March 2009.
- "First round in Internet war goes to Iranian intelligence". Debkafile. 28 June 2009. Archived from the original on 21 December 2013.
- "Freedom on the Net 2018" (PDF). Freedom House. November 2018. Archived from the original (PDF) on 1 November 2018. Retrieved 1 November 2018.
- OpenNet Initiative "Summarized global Internet filtering data spreadsheet" Archived 10 January 2012 at the Wayback Machine, 8 November 2011 and "Country Profiles" Archived 26 August 2011 at the Wayback Machine, the OpenNet Initiative is a collaborative partnership of the Citizen Lab at the Munk School of Global Affairs, University of Toronto; the Berkman Center for Internet & Society at Harvard University; and the SecDev Group, Ottawa
- "Enemies of the Internet 2014: Entities at the heart of censorship and surveillance". Reporters Without Borders. Paris. 11 March 2014. Archived from the original on 12 March 2014.
- "Internet Enemies" (PDF). Reporters Without Borders. Paris. 12 March 2012. Archived from the original (PDF) on 3 July 2017.
- Deibert, Ronald J.; Palfrey, John G.; Rohozinski, Rafal; Zittrain, Jonathan (2010). Access Controlled: The Shaping of Power, Rights, and Rule in Cyberspace. MIT Press. ISBN 978-0-262-51435-4. Archived from the original on 4 June 2011.
- "Finland censors anti-censorship site". The Register. 18 February 2008. Archived from the original on 20 February 2008. Retrieved 19 February 2008.
- Albert, Réka; Jeong, Hawoong; Barabási, Albert-László (9 September 1999). "Diameter of the World-Wide Web". Nature. 401 (6749): 130–131. arXiv:cond-mat/9907038. Bibcode:1999Natur.401..130A. doi:10.1038/43601. S2CID 4419938.
- "Georgian woman cuts off web access to whole of Armenia". The Guardian. 6 April 2011. Archived from the original on 25 August 2013. Retrieved 11 April 2012.
- Cowie, James. "Egypt Leaves the Internet". Renesys. Archived from the original on 28 January 2011. Retrieved 28 January 2011.
- "Egypt severs internet connection amid growing unrest". BBC News. 28 January 2011. Archived from the original on 23 January 2012.
- ^ Coroama, Vlad C.; Hilty, Lorenz M. (February 2014). "Assessing Internet energy intensity: A review of methods and results" (PDF). Environmental Impact Assessment Review. 45: 63–68. Bibcode:2014EIARv..45...63C. doi:10.1016/j.eiar.2013.12.004. Archived (PDF) from the original on 23 September 2020. Retrieved 9 March 2020.
- Giles, Jim (26 October 2011). "Internet responsible for 2 per cent of global energy usage". New Scientist. Archived from the original on 1 October 2014.,
- Raghavan, Barath; Ma, Justin (14 November 2011). "The energy and emergy of the internet" (PDF). Proceedings of the 10th ACM Workshop on Hot Topics in Networks. Cambridge, MA.: ACM SIGCOMM. pp. 1–6. doi:10.1145/2070562.2070571. ISBN 978-1-4503-1059-8. S2CID 6125953. Archived from the original (PDF) on 10 August 2014.
- Cwienk, Jeannette (11 July 2019). "Is Netflix bad for the environment? How streaming video contributes to climate change | DW | 11.07.2019". Deutsche Welle. Archived from the original on 12 July 2019. Retrieved 19 July 2019.
- ""Climate crisis: The Unsustainable Use of Online Video": Our new report". The Shift Project. 10 July 2019. Archived from the original on 21 July 2019. Retrieved 19 July 2019.
Sources
 This article incorporates text from a free content work. Text taken from World Trends in Freedom of Expression and Media Development Global Report 2017/2018, 202, UNESCO.
This article incorporates text from a free content work. Text taken from World Trends in Freedom of Expression and Media Development Global Report 2017/2018, 202, UNESCO.- Abbate, Janet (1999). Inventing the Internet. Cambridge, Massachusetts: MIT Press. ISBN 978-0-262-01172-3.
Further reading
- First Monday, a peer-reviewed journal on the Internet by the University Library of the University of Illinois at Chicago, ISSN 1396-0466
- The Internet Explained, Vincent Zegna & Mike Pepper, Sonet Digital, November 2005, pp. 1–7.
- Castells, Manuel (2010). The Rise of the Network Society. Wiley. ISBN 978-1-4051-9686-4.
- Yeo, ShinJoung (2023), Behind the Search Box: Google and the Global Internet Industry, U of Illinois Press, ISBN 978-0-252-04499-1, JSTOR 10.5406/jj.4116455
External links
- The Internet Society
- Living Internet, Internet history and related information, including information from many creators of the Internet
| Media culture | |||||||
|---|---|---|---|---|---|---|---|
| Media | |||||||
| Principles | |||||||
| Ideology | |||||||
| Deception |
| ||||||
| Philosophers | |||||||
| Counterculture | |||||||
| In academia | |||||||
| Issues | |||||||
| Synonyms | |||||||
| Semantic Web | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|
| Background | |||||||||||
| Sub-topics | |||||||||||
| Applications | |||||||||||
| Related topics | |||||||||||
| Standards |
| ||||||||||
- Internet
- 1969 establishments in the United States
- American inventions
- Computer-related introductions in 1969
- Cultural globalization
- Digital technology
- Mass media technology
- Telecommunications
- New media
- Promotion and marketing communications
- Public services
- Telegraphy
- Transport systems
- Virtual reality
- Main topic articles

