| Revision as of 16:19, 13 December 2005 edit86.125.12.85 (talk) →External links← Previous edit | Latest revision as of 19:03, 24 December 2024 edit undoGKNishimoto (talk | contribs)498 edits →Example from modern practiceTags: Mobile edit Mobile web edit Advanced mobile edit | ||
| Line 1: | Line 1: | ||
| {{short description|Hiding messages in other messages}} | |||
| :''This article is about ''steganography'' (hidden writing), not to be confused with '']'' (shorthand).'' | |||
| {{Use dmy dates|date=November 2023}} | |||
| {{for-multi|the process of writing in shorthand|Stenography|the prefix "Stego-" as used in taxonomy|List of commonly used taxonomic affixes}} | |||
| ] | |||
| '''Steganography''' ({{IPAc-en|audio=en-us-steganography.ogg|ˌ|s|t|ɛ|ɡ|ə|ˈ|n|ɒ|ɡ|r|ə|f|i}} {{respell|STEG|ə|NOG|rə-fee}}) is the practice of representing information within another message or physical object, in such a manner that the presence of the concealed information would not be evident to an unsuspecting person's examination. In computing/electronic contexts, a ], message, image, or video is concealed within another file, message, image, or video. The word ''steganography'' comes from ] ''steganographia'', which combines the words ''steganós'' ({{Wikt-lang|el|στεγανός}}), meaning "covered or concealed", and ''-graphia'' ({{Wikt-lang|el|γραφή}}) meaning "writing".<ref>{{Cite web|url=https://www.merriam-webster.com/dictionary/steganography|title=Definition of STEGANOGRAPHY|website=Merriam-webster.com|access-date=14 December 2021}}</ref> | |||
| '''Steganography''' is the art and science of writing hidden messages in such a way that no one apart from the intended recipient knows of the existence of the message; this is in contrast to ], where the existence of the message itself is not disguised, but the meaning is obscured. | |||
| The first recorded use of the term was in 1499 by ] in his '']'', a treatise on ] and steganography, disguised as a book on magic. Generally, the hidden messages appear to be (or to be part of) something else: images, articles, shopping lists, or some other cover text. For example, the hidden message may be in ] between the visible lines of a private letter. Some implementations of steganography that lack a formal ] are forms of ], while key-dependent steganographic schemes try to adhere to ].<ref name=stegokey>{{cite journal|last=Fridrich|first=Jessica|author2=M. Goljan|author3=D. Soukal|title=Searching for the Stego Key|journal=Proc. SPIE, Electronic Imaging, Security, Steganography, and Watermarking of Multimedia Contents VI|year=2004|volume=5306|pages=70–82|url=http://www.ws.binghamton.edu/fridrich/Research/Keysearch_SPIE.pdf|access-date=23 January 2014|doi=10.1117/12.521353|series=Security, Steganography, and Watermarking of Multimedia Contents VI|bibcode=2004SPIE.5306...70F|s2cid=6773772|editor1-last=Delp Iii|editor1-first=Edward J|editor2-last=Wong|editor2-first=Ping W}}</ref> | |||
| The word "''Steganography''" is of Greek origin and means ''"covered, or hidden writing"''. Its ancient origins can be traced back to 440 BC. ] mentions two examples of Steganography in '']''. Demeratus sent a warning about a forthcoming attack to Xerxes by writing it on a wooden panel and covering it in wax, which was itself inscribed with a message. ]s were in common use then as re-usable writing surface, sometimes used for ]. The second ancient example is Histaeus who shaved the head of his most trusted slave and tattooed a message on his head. After his hair had grown the message was hidden. The purpose was to instigate a revolt against the Persians. Later, ]'s book ''Steganographia'' is a treatise on cryptography and steganography disguised as a book on ]. | |||
| The advantage of steganography over cryptography alone is that the intended secret message does not attract attention to itself as an object of scrutiny. Plainly visible ] messages, no matter how unbreakable they are, arouse interest and may in themselves be incriminating in countries in which encryption is illegal.<ref>{{cite web|url=http://www.alternet.org/story/11986/|title=Confounding Carnivore: How to Protect Your Online Privacy|publisher=]|archive-url=https://web.archive.org/web/20070716093719/http://www.alternet.org/story/11986/|archive-date=16 July 2007|access-date=2 September 2008|last=Pahati|first=OJ|date=29 November 2001}}</ref> Whereas cryptography is the practice of protecting the contents of a message alone, steganography is concerned with concealing both the fact that a secret message is being sent ''and'' its contents. | |||
| Generally, a steganographic message will appear to be something else: a picture, an article, a shopping list, or some other message - the '''covertext'''. Classically, it may be hidden by using ] between the visible lines of innocuous documents, or even written onto clothing. In WW2 a message was once written in ] along two-colored knitting yarn. Another method is invisible ink underlining, or simply pin pricking of individual letters in a newspaper article, thus forming a message. It may even be a few words written under a postage stamp, the stamp then being the covertext. | |||
| Steganography includes the concealment of information within computer files. In digital steganography, electronic communications may include steganographic coding inside of a transport layer, such as a document file, image file, program, or protocol. Media files are ideal for steganographic transmission because of their large size. For example, a sender might start with an innocuous image file and adjust the color of every hundredth ] to correspond to a letter in the alphabet. The change is so subtle that someone who is not specifically looking for it is unlikely to notice the change. | |||
| The '''advantage of steganography''' over cryptography alone, is that messages do not attract attention to themselves, messengers or to recipients. An unhidden coded message, no matter how unbreakable it is, will arouse suspicion and may in itself be incriminating. In some countries encryption is illegal. | |||
| ==History== | |||
| ]'s '']'' copied by ] in 1591]] | |||
| The first recorded uses of steganography can be traced back to 440 BC in ], when ] mentions two examples in his '']''.<ref>{{cite journal |url=http://www.cl.cam.ac.uk/~fapp2/publications/ieee99-infohiding.pdf |title=Information Hiding: A survey |journal=Proceedings of the IEEE |last= Petitcolas |first=FAP |author2=Anderson RJ |author3=Kuhn MG |volume=87 |issue=7 |pages=1062–78 |access-date=2 September 2008 |doi=10.1109/5.771065 |year=1999|citeseerx=10.1.1.333.9397 }}</ref> ] sent a message to his vassal, ], by shaving the head of his most trusted servant, "marking" the message onto his scalp, then sending him on his way once his hair had regrown, with the instruction, "When thou art come to Miletus, bid Aristagoras shave thy head, and look thereon." Additionally, ] sent a warning about a forthcoming attack to Greece by writing it directly on the wooden backing of a ] before applying its beeswax surface. Wax tablets were in common use then as reusable writing surfaces, sometimes used for ]. | |||
| '''Steganography uses in electronic communication''' include steganographic coding inside of a transport layer such an ] file or a protocol such as ]. | |||
| In his work ''],'' ] developed his so-called "]" that can hide information in a Latin praise of God. "''Auctor Sapientissimus Conseruans Angelica Deferat Nobis Charitas Potentissimi Creatoris''" for example contains the concealed word ''VICIPEDIA''.<ref>{{cite web |url=http://daten.digitale-sammlungen.de/~db/0002/bsb00026190/images/index.html?seite=71|title=Polygraphiae (cf. p. 71f) |publisher = Digitale Sammlungen |language = de |access-date=27 May 2015}}</ref> | |||
| Steganographic messages are often first ] by some traditional means, and then a ''covertext'' is modified in some way to contain the encrypted message, resulting in '''stegotext'''. For example, the letter size, spacing, ], or other characteristics of a covertext can be manipulated to carry the hidden message; only the recipient (who must know the technique used) can recover the message and then decrypt it. ] is known to have suggested such a technique to hide messages. | |||
| ==Techniques== | |||
| ==An example from modern practice== | |||
| {{main|List of steganography techniques}} | |||
| ]s of each ], an almost completely black image results. Making the resulting image 85 times brighter results in the second image.]] | |||
| ] operation with the number 3 to the image, and make the image 85 times brighter, and you get the above image.]] | |||
| The larger the cover message is (in data content terms — number of ]s) relative to the hidden message, the easier it is to hide the latter. | |||
| For this reason, ]s (which contain large amounts of data) are used to hide messages on the ] and on other communication media. It is not clear how commonly this is actually done. For example: a 24-bit ] will have 8 bits representing each of the three color values (red, green, and blue) at each ]. If we consider just the blue there will be 2<sup>8</sup> different values of blue. The difference between say 11111111 and 11111110 in the value for blue intensity is likely to be undetectable by the human eye. Therefore, the ] can be used (more or less undetectably) for something else other than color information. If we do it with the green and the red as well we can get one letter of ] text for every three ]s. | |||
| ] | |||
| Stated somewhat more formally, the objective for making steganographic encoding difficult to detect is to ensure that the changes to the carrier (the original signal) due to the injection of the payload (the signal to covertly embed) are visually (and ideally, statistically) negligible; that is to say, the changes are indistinguishable from the noise floor of the carrier. | |||
| Numerous techniques throughout history have been developed to embed a message within another medium. | |||
| (From an ] point of view, this means that the ] must have more ] than the 'surface' ] requires, i.e., there is ]. For a digital image, this may be ] from the imaging element; for ], it may be noise from recording techniques or ] equipment. Any system with an ] amplification stage will also introduce so-called ] or "1/f" noise, which can be exploited as a noise cover. In addition, ] schemes (such as ]) always introduce some error into the decompressed data; it is possible to exploit this for steganographic use as well.) | |||
| ===Physical=== | |||
| Steganography can be used for ]ing, where a message (being simply an identifier) is hidden in an image so that its source can be tracked or verified. | |||
| Placing the message in a physical item has been widely used for centuries.<ref name=knit>{{Cite web|url=https://getpocket.com/explore/item/the-wartime-spies-who-used-knitting-as-an-espionage-tool|title=The Wartime Spies Who Used Knitting as an Espionage Tool – Atlas Obscura|website=Pocket|access-date=4 March 2020}}</ref> Some notable examples include ] on paper, writing a message in ] on ] worn by a courier,<ref name=knit /> ]s, or using a ] to hide messages as ]s in ].<ref>{{Cite magazine |last=Newman |first=Lily Hay |title=How a Saxophonist Tricked the KGB by Encrypting Secrets in Music |language=en-US |magazine=Wired |url=https://www.wired.com/story/merryl-goldberg-music-encryption-ussr-phantom-orchestra/ |access-date=9 June 2022 |archive-url=https://web.archive.org/web/20220608222058/https://www.wired.com/story/merryl-goldberg-music-encryption-ussr-phantom-orchestra/ |archive-date=8 June 2022 |issn=1059-1028}}</ref> | |||
| ==== Social steganography ==== | |||
| ==Steganographic techniques== | |||
| In communities with social or government taboos or censorship, people use cultural steganography—hiding messages in idiom, pop culture references, and other messages they share publicly and assume are monitored. This relies on social context to make the underlying messages visible only to certain readers.<ref>, Boing Boing, 22 May 2013. Retrieved 7 June 2014.</ref><ref> {{Webarchive|url=https://web.archive.org/web/20140714143900/http://www.scenariomagazine.com/social-steganography/ |date=14 July 2014 }}, Scenario Magazine, 2013.</ref> Examples include: | |||
| Steganography has been widely used in historical times, especially before cryptographic systems were developed. | |||
| Examples of historical usage include: | |||
| * Hidden messages in ]s: in ancient ], people wrote messages on the wood, then covered it with ] so that it looked like an ordinary, unused, tablet. | |||
| * Hidden messages on messenger's body: also in ancient Greece. ] tells the story of a message ]ed on a ]'s ]d head, hidden by the growth of his hair, and exposed by shaving his head again. The message, if the story is true, carried a warning to Greece about ]n ] ]s. | |||
| * Hidden messages on paper written in ]s under other messages or on the blank parts of other messages. | |||
| * During and after ], ] agents used ]s to send information back and forth. Since the dots were typically extremely small -- the size of a ] produced by a ] (perhaps in a font with 10 or 12 characters per inch) or even smaller -- the stegotext was whatever the dot was hidden within. If a letter or an address, it was some alphabetic characters. If under a postage stamp, it was the presence of the stamp. | |||
| * More obscurely, during ], a ]ese spy in ], ], sent information to ]es in neutral ]. She was a dealer in ]s, and her letters discussed how many of this or that doll to ship. The stegotext in this case was the doll orders; the 'plaintext' being concealed was itself a ] giving information about ship movements, etc. Her case became somewhat famous and she became known as the Doll Woman. | |||
| * The ] is a theoretically unbreakable cipher that produces ciphertexts indistinguishable from random texts: only those who have the private key can distinguish these ciphertexts from any other perfectly random texts. Thus, any perfectly random data can be used as a covertext for a theoretically unbreakable steganography. | |||
| * In the manga ], a main plot device is a Yagyū letter which has a message written in mulberry extract. They see the message by placing it in a bowl of silkworms and seeing where they eat. | |||
| * Hiding a message in the title and context of a shared video or image. | |||
| Some more recent steganography techniques: | |||
| * Misspelling names or words that are popular in the media in a given week, to suggest an alternate meaning. | |||
| * ] | |||
| * Hiding a picture that can be traced by using Paint or any other drawing tool.{{citation needed|date=December 2016}} | |||
| * ] | |||
| * ]s | |||
| * Concealed messages in tampered executable files, exploiting redundancy in the i386 instruction set . | |||
| == |
=== Digital messages === | ||
| ]s of each ] and a subsequent ]. The hidden image is shown below.]] | |||
| In general, terminology analogous to (and consistent with) more conventional radio and communications technology is used; however, a brief description of some terms which show up in software specifically, and are easily confused, is appropriate. These are most relevant to digital steganographic systems. | |||
| ] | |||
| Since the dawn of computers, techniques have been developed to embed messages in digital cover mediums. The message to conceal is often encrypted, then used to overwrite part of a much larger block of encrypted data or a block of random data (an unbreakable cipher like the ] generates ciphertexts that look perfectly random without the private key). | |||
| The ''payload'' is the data it is desirable to transport (and, therefore, to hide). The ''carrier'' is the signal, stream, or data file into which the payload is hidden; contrast "''channel''" (typically used to refer to the type of input, such as "a JPEG image"). The resulting signal, stream, or data file which has the payload encoded into it is sometimes referred to as the ''package''. The percentage of bytes, samples, or other signal elements which are modified to encode the payload is referred to as the ''encoding density'' and is typically expressed as a floating-point number between 0 and 1. | |||
| Examples of this include changing pixels in image or sound files,<ref>{{cite journal|doi=10.1016/j.sigpro.2009.08.010|title=Digital image steganography: Survey and analysis of current methods|journal=Signal Processing|volume=90|issue=3|pages=727–752|year=2010|last1=Cheddad|first1=Abbas|last2=Condell|first2=Joan|last3=Curran|first3=Kevin|last4=Mc Kevitt|first4=Paul|bibcode=2010SigPr..90..727C }}</ref> properties of digital text such as spacing and font choice, ], ]s, modifying the echo of a sound file (Echo Steganography).{{citation needed|date=April 2024}}<!-- Original citation irretrievably lost -->, and including data in ignored sections of a file.<ref>{{cite journal | last1= Bender | first1= W. | last2= Gruhl | first2= D. | last3= Morimoto | first3= N. | last4= Lu | first4= A. | title= Techniques for data hiding | journal= IBM Systems Journal | publisher= IBM Corp.| date=1996 | volume= 35 | issn= 0018-8670 | url= https://pdfs.semanticscholar.org/8c82/c93dfc7d3672e58efd982a23791a8a419053.pdf | archive-url= https://web.archive.org/web/20200611050549/https://pdfs.semanticscholar.org/8c82/c93dfc7d3672e58efd982a23791a8a419053.pdf | url-status= dead | archive-date= 11 June 2020 |issue = 3.4| pages=313–336| doi= 10.1147/sj.353.0313 | s2cid= 16672162 }}</ref> | |||
| In a set of files, those files considered likely to contain a payload are called ''suspects''. If the ''suspect'' was identified through some type of statistical analysis, it may be referred to as a ''candidate''. | |||
| {{Multiple image | |||
| == Rumored usage in terrorism == | |||
| |align=center | |||
| |direction=horizontal | |||
| |header=Images hidden in sound files | |||
| |image1=Drawing of the word Misplaced Pages in Coagula.jpg | |||
| |caption1=1. The word "Misplaced Pages" is drawn using computer software | |||
| |alt1=The word "Misplaced Pages" written in green and red on black background | |||
| |width1=250 | |||
| |image2=Drawing of the word Misplaced Pages transformed into a wav file (Coagula software).wav | |||
| |caption2=2. The image is converted into an audio file | |||
| |alt2= | |||
| |image3=Misplaced Pages wavefile by Coagula - logarihtmic spectrogram.svg | |||
| |caption3=3. Finally, the audio is analysed through a spectrogram, revealing the initial image | |||
| |alt3=The word "Misplaced Pages" in yellow over a dark blue/black background | |||
| |width3=250 | |||
| |image4=Spectrogram - Nine Inch Nails - My Violent Heart.png | |||
| |caption4=] of a ] encoded as sound in the song "My Violent Heart" by ] from the '']'' album (2007) | |||
| |alt4=image of a blue arm and hand over white, pixelated dots | |||
| |width4=200 | |||
| }} | |||
| === Steganography in streaming media === | |||
| The rumors about terrorists using steganography started first in the daily newspaper ] on February 5th 2001. The articles are still available online, and were titled "Terrorist instructions hidden online", and the same day, "Terror groups hide behind Web encryption". In July of the same year, the information looked even more precise: "Militants wire Web with links to jihad". A citation: "''Lately, al-Qaeda operatives have been sending hundreds of encrypted messages that have been hidden in files on digital photographs on the auction site eBay.com''". These rumors were cited many times - without ever showing any actual proof - by other media worldwide, especially after the terrorist attack of ]. | |||
| Since the era of evolving network applications, steganography research has shifted from image steganography to steganography in streaming media such as ] (VoIP). | |||
| In 2003, Giannoula et al. developed a data hiding technique leading to compressed forms of source video signals on a frame-by-frame basis.<ref>{{Cite book|last1=Giannoula|first1=A.|last2=Hatzinakos|first2=D.|title=Proceedings 2003 International Conference on Image Processing (Cat. No.03CH37429) |chapter=Compressive data hiding for video signals |volume=1|pages=I–529–32|publisher=IEEE|doi=10.1109/icip.2003.1247015|isbn=0780377508|year=2003|s2cid=361883}}</ref> | |||
| The USA Today articles were written by veteran foreign correspondent ], who in 2004 was fired in a big scandal, because it appeared that he fabricated a lot of stories and invented sources that didn't exist. | |||
| In 2005, Dittmann et al. studied steganography and watermarking of multimedia contents such as VoIP.<ref>{{Cite journal|last1=Dittmann|first1=Jana|last2=Hesse|first2=Danny|last3=Hillert|first3=Reyk|date=21 March 2005|title=Steganography and steganalysis in voice-over IP scenarios: operational aspects and first experiences with a new steganalysis tool set|journal=Security, Steganography, and Watermarking of Multimedia Contents VII|volume=5681|pages=607|publisher=SPIE|doi=10.1117/12.586579|bibcode=2005SPIE.5681..607D|s2cid=206413447|editor1-last=Delp Iii|editor1-first=Edward J|editor2-last=Wong|editor2-first=Ping W}}</ref> | |||
| In ], the ] published an article claiming that ] had used steganographic techniques to encode messages into images, and then transported these via email and possibly via ] to prepare and execute the ]. Despite being dismissed by security experts, the story has been widely repeated and resurfaces frequently. It was noted that the story apparently originated with a press release from "iomart" , a vendor of ] software. No corroborating evidence has been produced by any other source. | |||
| In 2008, Yongfeng Huang and Shanyu Tang presented a novel approach to information hiding in low bit-rate VoIP speech stream, and their published work on steganography is the first-ever effort to improve the codebook partition by using Graph theory along with Quantization Index Modulation in low bit-rate streaming media.<ref>B. Xiao, Y. Huang, and S. Tang, "An Approach to Information Hiding in Low Bit-Rate Speech Stream", in ''IEEE GLOBECOM 2008'', IEEE, pp. 371–375, 2008. {{ISBN|978-1-4244-2324-8}}.</ref> | |||
| Moreover, a captured al-Qaeda training manual makes no mention of this method of steganography. The chapter on communications in the al-Qaeda manual acknowledges the technical superiority of US security services, and generally advocates low-technology forms of covert communication. The chapter on "codes and ciphers" places considerable emphasis on using ]s in traditional paper letters, plus simple ciphers such as ] with nulls; computerized image steganography is not mentioned. | |||
| In 2011 and 2012, Yongfeng Huang and Shanyu Tang devised new steganographic algorithms that use codec parameters as cover object to realise real-time covert VoIP steganography. Their findings were published in ''IEEE Transactions on Information Forensics and Security''.<ref>{{Cite journal|last1=Huang|first1=Yong Feng|last2=Tang|first2=Shanyu|last3=Yuan|first3=Jian|date=June 2011|title=Steganography in Inactive Frames of VoIP Streams Encoded by Source Codec|journal=IEEE Transactions on Information Forensics and Security|volume=6|issue=2|pages=296–306|doi=10.1109/tifs.2011.2108649|s2cid=15096702|issn=1556-6013|url=https://repository.uwl.ac.uk/id/eprint/3935/1/Steganography%20in%20inactive%20frames%20of%20VoIP%20streams%20encoded%20by%20source%20codec.pdf}}</ref><ref>{{Cite journal|last1=Huang|first1=Yongfeng|last2=Liu|first2=Chenghao|last3=Tang|first3=Shanyu|last4=Bai|first4=Sen|date=December 2012|title=Steganography Integration Into a Low-Bit Rate Speech Codec|journal=IEEE Transactions on Information Forensics and Security|volume=7|issue=6|pages=1865–1875|doi=10.1109/tifs.2012.2218599|s2cid=16539562|issn=1556-6013|url=https://repository.uwl.ac.uk/id/eprint/3932/1/Steganography%20Integration%20into%20a%20low-bit%20rate%20speech%20codec.pdf}}</ref><ref>{{Cite journal|title=Application of Lah transform for security and privacy of data through information hiding in telecommunication|journal=Transactions on Emerging Telecommunications Technologies|year=2020|doi=10.1002/ett.3984|last1=Ghosal|first1=Sudipta Kr|last2=Mukhopadhyay|first2=Souradeep|last3=Hossain|first3=Sabbir|last4=Sarkar|first4=Ram|volume=32|issue=2|s2cid=225866797}}</ref> | |||
| Nevertheless public efforts were mounted to detect the presence of steganographic information in images on the web (especially on ], which had been mentioned in the New York Times article). To date these scans have examined millions of images without detecting any steganographic content (see "Detecting Steganographic Content on the Internet" under external links), other than test images used to test the system, and instructional images on web sites about steganography. | |||
| In 2024, Cheddad & Cheddad proposed a new framework <ref>{{Cite book|last1=Cheddad|first1= Zohra Adila|last2=Cheddad|first2=Abbas|title=Proceedings 2023 Intelligent Systems Conference (IntelliSys'23)|chapter= Active Restoration of Lost Audio Signals Using Machine Learning and Latent Information |series= Lecture Notes in Networks and Systems|volume= 822|publisher=LNCS,Springer|doi=10.1007/978-3-031-47721-8_1|year=2024 |pages= 1–16|isbn= 978-3-031-47720-1}}</ref> for reconstructing lost or corrupted audio signals using a combination of machine learning techniques and latent information. The main idea of their paper is to enhance audio signal reconstruction by fusing steganography, halftoning (dithering), and state-of-the-art shallow and deep learning methods (e.g., RF, LSTM). This combination of steganography, halftoning, and machine learning for audio signal reconstruction may inspire further research in optimizing this approach or applying it to other domains, such as image reconstruction (i.e., inpainting). | |||
| Effective detection of steganographically encoded materials in communications intercepts between suspected terrorists is therefore extremely important, but very complicated, as we will see below. | |||
| === Adaptive-Steganography === | |||
| == Countermeasures == | |||
| Adaptive steganography is a technique for concealing information within digital media by tailoring the embedding process to the specific features of the cover medium. An example of this approach is demonstrated in the work.<ref>{{cite journal|title=A skin tone detection algorithm for an adaptive approach to steganography|journal=Signal Processing|volume=89|issue=12|pages=2465–2478|year=2009|doi=10.1016/j.sigpro.2009.04.022|last1=Cheddad|first1=Abbas|last2=Condell|first2=Joan|last3=Curran|first3=Kevin|last4=Mc Kevitt|first4=Paul|bibcode=2009SigPr..89.2465C }}</ref> Their method develops a skin tone detection algorithm, capable of identifying facial features, which is then applied to adaptive steganography. By incorporating face rotation into their approach, the technique aims to enhance its adaptivity to conceal information in a manner that is both less detectable and more robust across various facial orientations within images. This strategy can potentially improve the efficacy of information hiding in both static images and video content. | |||
| === Cyber-physical systems/Internet of Things === | |||
| The detection of steganographically encoded packages is called ]. The simplest method to detect modified files, however, is to compare them to the originals. To detect information being moved through the graphics on a website, for example, an analyst can maintain known-clean copies of these materials and compare them against the current contents of the site. The differences (assuming the carrier is the same) will compose the payload. | |||
| Academic work since 2012 demonstrated the feasibility of steganography for ]s (CPS)/the ] (IoT). Some techniques of CPS/IoT steganography overlap with network steganography, i.e. hiding data in communication protocols used in CPS/the IoT. However, specific techniques hide data in CPS components. For instance, data can be stored in unused registers of IoT/CPS components and in the states of IoT/CPS actuators.<ref>{{cite journal|last1=Wendzel|first1=Steffen|last2=Mazurczyk|first2=Wojciech|last3=Haas|first3=Georg|title=Don't You Touch My Nuts: Information Hiding In Cyber Physical Systems Using Smart Buildings|journal=Proceedings of the 2017 IEEE Security & Privacy Workshops|language=en|publisher=IEEE}}</ref><ref>{{cite journal|last1=Tuptuk|first1=Nilufer|last2=Hailes|first2=Stephen|title=Covert channel attacks in pervasive computing|journal=Proceedings 2015 IEEE International Conference on Pervasive Computing and Communications (PerCom)}}</ref> | |||
| In general, using an extremely high compression rate makes steganography difficult, but not impossible; while compression errors provide a good place to hide data, high compression reduces the amount of data available to hide the payload in, raising the encoding density and facilitating easier detection (in the extreme case, even by casual observation).. | |||
| == |
===Printed=== | ||
| Digital steganography output may be in the form of printed documents. A message, the '']'', may be first encrypted by traditional means, producing a '']''. Then, an innocuous ''cover text'' is modified in some way so as to contain the ciphertext, resulting in the ''stegotext''. For example, the letter size, spacing, ], or other characteristics of a cover text can be manipulated to carry the hidden message. Only a recipient who knows the technique used can recover the message and then decrypt it. ] developed ] as such a technique. | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ]s | |||
| * ] | |||
| The ciphertext produced by most digital steganography methods, however, is not printable. Traditional digital methods rely on perturbing noise in the channel file to hide the message, and as such, the channel file must be transmitted to the recipient with no additional noise from the transmission. Printing introduces much noise in the ciphertext, generally rendering the message unrecoverable. There are techniques that address this limitation, one notable example being ASCII Art Steganography.<ref>{{cite web|url=https://pictureworthsthousandwords.appspot.com/|title=ASCII Art Steganography|author=Vincent Chu|website=Pictureworthsthousandwords.appspot.com}}</ref> | |||
| ==External links== | |||
| ''Steganography articles'' | |||
| * at Forensics.nl | |||
| * | |||
| * | |||
| ] | |||
| ''Steganalysis'' | |||
| Although not classic steganography, some types of modern color laser printers integrate the model, serial number, and timestamps on each printout for traceability reasons using a dot-matrix code made of small, yellow dots not recognizable to the naked eye — see ] for details. | |||
| * For every clever method and tool being developed to hide information in multimedia data, an equal number of clever methods and tools are being developed to detect and reveal its secrets. | |||
| * , PDF file, 813 KB. | |||
| * Some sample pages of | |||
| * An example of ongoing research on Steganography. | |||
| === Network === | |||
| ''Implementations'' | |||
| In 2015, a taxonomy of 109 network hiding methods was presented by Steffen Wendzel, Sebastian Zander et al. that summarized core concepts used in network steganography research.<ref>{{cite journal |last1=Wendzel |first1=Steffen |last2=Zander |first2=Sebastian |last3=Fechner |first3=Bernhard |last4=Herdin |first4=Christian |title=Pattern-Based Survey and Categorization of Network Covert Channel Techniques |journal=ACM Computing Surveys |date=16 April 2015 |volume=47 |issue=3 |pages=1–26 |doi=10.1145/2684195 |arxiv=1406.2901 |s2cid=14654993 |url=https://www.researchgate.net/publication/263048788}}</ref> The taxonomy was developed further in recent years by several publications and authors and adjusted to new domains, such as CPS steganography.<ref>{{cite book |last1=Mazurczyk |first1=Wojciech |last2=Wendzel |first2=Steffen |last3=Cabaj |first3=Krzysztof |title=Proceedings of the 13th International Conference on Availability, Reliability and Security |chapter=Towards Deriving Insights into Data Hiding Methods Using Pattern-based Approach |date=27 August 2018 |pages=1–10 |doi=10.1145/3230833.3233261|isbn=9781450364485 |s2cid=51976841 }}</ref><ref>{{cite journal |last1=Hildebrandt |first1=Mario |last2=Altschaffel |first2=Robert |last3=Lamshöft |first3=Kevin |last4=Lange |first4=Matthias |last5=Szemkus |first5=Martin |last6=Neubert |first6=Tom |last7=Vielhauer |first7=Claus |last8=Ding |first8=Yongjian |last9=Dittmann |first9=Jana |title=Threat Analysis of Steganographic and Covert Communication in Nuclear I&C Systems |journal=International Conference on Nuclear Security: Sustaining and Strengthening Efforts |date=2020}}</ref><ref>{{cite journal |last1=Mileva |first1=Aleksandra |last2=Velinov |first2=Aleksandar |last3=Hartmann |first3=Laura |last4=Wendzel |first4=Steffen |last5=Mazurczyk |first5=Wojciech |title=Comprehensive analysis of MQTT 5.0 susceptibility to network covert channels |journal=Computers & Security |date=May 2021 |volume=104 |pages=102207 |doi=10.1016/j.cose.2021.102207|s2cid=232342523 |doi-access=free }}</ref> | |||
| * Steganography software - hide information in five innocent looking files types: JPEG, PNG, BMP, HTML and WAV.It also features: strong encryption algorithms; a locker that allows you to password protect certain applications; a password management solution and a real-random password generator; a shredder that helps you destroy beyond recovery files, folders and internet traces; the ability to create self-decrypting packages; secured password transfer. | |||
| * protects your disks with Deniable Encryption, aka data hidden in another encrypted data. | |||
| In 1977, Kent concisely described the potential for covert channel signaling in general network communication protocols, even if the traffic is encrypted (in a footnote) in "Encryption-Based Protection for Interactive User/Computer Communication," Proceedings of the Fifth Data Communications Symposium, September 1977. | |||
| * will take a sentence that you provide and turn it into text that looks to all the world like spam. | |||
| * | |||
| In 1987, Girling first studied covert channels on a local area network (LAN), identified and realised three obvious covert channels (two storage channels and one timing channel), and his research paper entitled “Covert channels in LAN’s” published in ''IEEE Transactions on Software Engineering'', vol. SE-13 of 2, in February 1987.<ref>{{Cite journal|last=Girling|first=C.G.|date=February 1987|title=Covert Channels in LAN's|journal=IEEE Transactions on Software Engineering|volume=SE-13|issue=2|pages=292–296|doi=10.1109/tse.1987.233153|s2cid=3042941|issn=0098-5589}}</ref> | |||
| * A Cutting Edge Free Steganographic Software | |||
| * Hiding text and files in images | |||
| In 1989, Wolf implemented covert channels in LAN protocols, e.g. using the reserved fields, pad fields, and undefined fields in the TCP/IP protocol.<ref>M. Wolf, “Covert channels in LAN protocols,” in Proceedings of the Workshop on Local Area Network Security (LANSEC’89) (T.A. Berson and T. Beth, eds.), pp. 91–102, 1989.</ref> | |||
| * Steganography by justified plain text. | |||
| * An open-source cross-platform image steganography suite that includes both steganography and steganalysis implementations. | |||
| In 1997, Rowland used the IP identification field, the TCP initial sequence number and acknowledge sequence number fields in TCP/IP headers to build covert channels.<ref>{{Cite journal|last=Rowland|first=Craig H.|date=5 May 1997|title=Covert channels in the TCP/IP protocol suite|journal=First Monday|volume=2|issue=5|doi=10.5210/fm.v2i5.528|issn=1396-0466 |doi-access=free }}</ref> | |||
| * Free .jpeg and .wav encryption for Linux and other operating systems. | |||
| * Windows steganography software for hiding a file of any size in one or more BMP image files. | |||
| In 2002, Kamran Ahsan made an excellent summary of research on network steganography.<ref>Kamran Ahsan, “Covert Channel Analysis and Data Hiding in TCP/IP,” MSc Thesis, University of Toronto, 2002.</ref> | |||
| * Free, open-source Windows/Linux disk encryption software that supports hiding one encrypted volume inside another, without leaving any evidence that the second encrypted volume exists. | |||
| In 2005, Steven J. Murdoch and Stephen Lewis contributed a chapter entitled "Embedding Covert Channels into TCP/IP" in the "''Information Hiding''" book published by Springer.<ref>{{Citation|last1=Murdoch|first1=Steven J.|title=Embedding Covert Channels into TCP/IP|date=2005|work=Information Hiding|pages=247–261|publisher=Springer Berlin Heidelberg|isbn=9783540290391|last2=Lewis|first2=Stephen|doi=10.1007/11558859_19}}</ref> | |||
| All information hiding techniques that may be used to exchange steganograms in telecommunication networks can be classified under the general term of network steganography. This nomenclature was originally introduced by Krzysztof Szczypiorski in 2003.<ref>{{cite web |url=http://www.tele.pw.edu.pl/~krzysiek/pdf/steg-seminar-2003.pdf |title=Steganography in TCP/IP Networks. State of the Art and a Proposal of a New System – HICCUPS |author=Krzysztof Szczypiorski |access-date=17 June 2010 |work=Institute of Telecommunications Seminar |date=4 November 2003}}</ref> Contrary to typical steganographic methods that use digital media (images, audio and video files) to hide data, network steganography uses communication protocols' control elements and their intrinsic functionality. As a result, such methods can be harder to detect and eliminate.<ref>{{cite web |url=http://irevolution.wordpress.com/2009/06/05/steganography-2-0-digital-resistance-against-repressive-regimes/ |title=Steganography 2.0: Digital Resistance against Repressive Regimes |author=Patrick Philippe Meier |access-date=17 June 2010 |work=irevolution.wordpress.com |date=5 June 2009}}</ref> | |||
| Typical network steganography methods involve modification of the properties of a single network protocol. Such modification can be applied to the ] (PDU),<ref>{{cite web |url=http://firstmonday.org/htbin/cgiwrap/bin/ojs/index.php/fm/issue/view/80 |title=Covert Channels in the TCP/IP Suite |author=Craig Rowland |access-date=16 June 2010 |work=First Monday Journal |date=May 1997 |archive-date=26 January 2013 |archive-url=https://web.archive.org/web/20130126135920/http://firstmonday.org/htbin/cgiwrap/bin/ojs/index.php/fm/issue/view/80 |url-status=dead }}</ref><ref>{{cite web |url=http://www.cl.cam.ac.uk/~sjm217/papers/ih05coverttcp.pdf |title=Embedding Covert Channels into TCP/IP |author1=Steven J. Murdoch |author2=Stephen Lewis |name-list-style=amp |access-date=16 June 2010 |work=Information Hiding Workshop |year=2005}}</ref><ref>{{cite web |url=http://wwwiti.cs.uni-magdeburg.de/iti_amsl/acm/acm02/ahsan_kundur.pdf |title=Practical Data Hiding in TCP/IP |author1=Kamran Ahsan |author2=Deepa Kundur |name-list-style=amp |access-date=16 June 2010 |work=ACM Wksp. Multimedia Security |date=December 2002 |archive-date=29 October 2012 |archive-url=https://web.archive.org/web/20121029155725/http://wwwiti.cs.uni-magdeburg.de/iti_amsl/acm/acm02/ahsan_kundur.pdf |url-status=dead }}</ref> to the time relations between the exchanged PDUs,<ref>{{cite web |url=http://www.ece.tamu.edu/~deepa/pub/KunAhsTXSecWrkshp03.pdf |title=Practical Internet Steganography: Data Hiding in IP |author1=Kundur D. |author2=Ahsan K. |name-list-style=amp |access-date=16 June 2010 |work=Texas Wksp. Security of Information Systems |date=April 2003 |archive-date=29 October 2012 |archive-url=https://web.archive.org/web/20121029155725/http://www.ece.tamu.edu/~deepa/pub/KunAhsTXSecWrkshp03.pdf |url-status=dead }}</ref> or both (hybrid methods).<ref>{{cite book |chapter=Steganography of VoIP Streams |author1=Wojciech Mazurczyk |author2=Krzysztof Szczypiorski |title=On the Move to Meaningful Internet Systems: OTM 2008 |name-list-style=amp |doi=10.1007/978-3-540-88873-4_6 |series=Lecture Notes in Computer Science |date=November 2008|volume=5332 |pages=1001–1018 |arxiv=0805.2938 |isbn=978-3-540-88872-7 |s2cid=14336157 }}</ref> | |||
| Moreover, it is feasible to utilize the relation between two or more different network protocols to enable secret communication. These applications fall under the term inter-protocol steganography.<ref>{{cite arXiv |eprint=1005.1925 |title=Information Hiding Using Improper Frame Padding |author1=Bartosz Jankowski |author2=Wojciech Mazurczyk |author3=Krzysztof Szczypiorski |name-list-style=amp |date=11 May 2010 |class=cs.CR}}</ref> Alternatively, multiple network protocols can be used simultaneously to transfer hidden information and so-called control protocols can be embedded into steganographic communications to extend their capabilities, e.g. to allow dynamic overlay routing or the switching of utilized hiding methods and network protocols.<ref>{{cite book|last1=Wendzel|first1=Steffen|last2=Keller|first2=Joerg|title=Communications and Multimedia Security |chapter=Low-Attention Forwarding for Mobile Network Covert Channels |volume=7025|date=20 October 2011|pages=122–133|doi=10.1007/978-3-642-24712-5_10|url=https://www.researchgate.net/publication/215661202|access-date=4 September 2016|series=Lecture Notes in Computer Science|isbn=978-3-642-24711-8}}</ref><ref name="Wiley-IEEE">{{cite book|url=http://eu.wiley.com/WileyCDA/WileyTitle/productCd-1118861698.html|title=Information Hiding in Communication Networks: Fundamentals, Mechanisms, and Applications|last1=Mazurczyk|first1=Wojciech|last2=Wendzel|first2=Steffen|last3=Zander|first3=Sebastian|last4=Houmansadr|first4=Amir|last5=Szczypiorski|first5=Krzysztof|date=2016|publisher=Wiley-IEEE|isbn=978-1-118-86169-1|edition=1}}</ref> | |||
| Network steganography covers a broad spectrum of techniques, which include, among others: | |||
| * Steganophony – the concealment of messages in ] conversations, e.g. the employment of delayed or corrupted packets that would normally be ignored by the receiver (this method is called LACK – Lost Audio Packets Steganography), or, alternatively, hiding information in unused header fields.<ref>{{cite web |url=https://spectrum.ieee.org/vice-over-ip-the-voip-steganography-threat |title=Vice Over IP: The VoIP Steganography Threat |author1=Józef Lubacz |author2=Wojciech Mazurczyk |author3=Krzysztof Szczypiorski |access-date=11 February 2010 |work=IEEE Spectrum |date=February 2010}}</ref> | |||
| * WLAN Steganography – transmission of steganograms in Wireless Local Area Networks. A practical example of WLAN Steganography is the HICCUPS system (Hidden Communication System for Corrupted Networks)<ref>{{cite web |url=http://krzysiek.tele.pw.edu.pl/pdf/acs2003-hiccups.pdf |title=HICCUPS: Hidden Communication System for Corrupted Networks |author= Krzysztof Szczypiorski |access-date=11 February 2010 |work=In Proc. of: The Tenth International Multi-Conference on Advanced Computer Systems ACS'2003, pp. 31–40 |date=October 2003}}</ref> | |||
| ==Additional terminology== | |||
| {{further|Security through obscurity}} | |||
| Discussions of steganography generally use terminology analogous to and consistent with conventional radio and communications technology. However, some terms appear specifically in software and are easily confused. These are the most relevant ones to digital steganographic systems: | |||
| The ''payload'' is the data covertly communicated. The ''carrier'' is the signal, stream, or data file that hides the payload, which differs from the ''channel'', which typically means the type of input, such as a JPEG image. The resulting signal, stream, or data file with the encoded payload is sometimes called the ''package'', ''stego file'', or ''covert message''. The proportion of bytes, samples, or other signal elements modified to encode the payload is called the ''encoding density'' and is typically expressed as a number between 0 and 1. | |||
| In a set of files, the files that are considered likely to contain a payload are ''suspects''. A ''suspect'' identified through some type of statistical analysis can be referred to as a ''candidate''. | |||
| ==Countermeasures and detection== | |||
| Detecting physical steganography requires a careful physical examination, including the use of magnification, developer chemicals, and ]. It is a time-consuming process with obvious resource implications, even in countries that employ many people to spy on their fellow nationals. However, it is feasible to screen mail of certain suspected individuals or institutions, such as prisons or prisoner-of-war (POW) camps. | |||
| During ], prisoner of war camps gave prisoners specially-treated ] that would reveal ]. An article in the 24 June 1948 issue of ''Paper Trade Journal'' by the Technical Director of the ] had Morris S. Kantrowitz describe in general terms the development of this paper. Three prototype papers (''Sensicoat'', ''Anilith'', and ''Coatalith'') were used to manufacture postcards and stationery provided to German prisoners of war in the US and Canada. If POWs tried to write a hidden message, the special paper rendered it visible. The US granted at least two ]s related to the technology, one to Kantrowitz, {{US Patent|2515232}}, "Water-Detecting paper and Water-Detecting Coating Composition Therefor," patented 18 July 1950, and an earlier one, "Moisture-Sensitive Paper and the Manufacture Thereof," {{US Patent|2445586}}, patented 20 July 1948. A similar strategy issues prisoners with writing paper ruled with a water-soluble ink that runs in contact with water-based invisible ink. | |||
| In computing, steganographically encoded package detection is called ]. The simplest method to detect modified files, however, is to compare them to known originals. For example, to detect information being moved through the graphics on a website, an analyst can maintain known clean copies of the materials and then compare them against the current contents of the site. The differences, if the carrier is the same, comprise the payload. In general, using extremely high compression rates makes steganography difficult but not impossible. Compression errors provide a hiding place for data, but high compression reduces the amount of data available to hold the payload, raising the encoding density, which facilitates easier detection (in extreme cases, even by casual observation). | |||
| There are a variety of basic tests that can be done to identify whether or not a secret message exists. This process is not concerned with the extraction of the message, which is a different process and a separate step. The most basic approaches of ] are visual or aural attacks, structural attacks, and statistical attacks. These approaches attempt to detect the steganographic algorithms that were used.<ref name="Wanyer2009">Wayner, Peter (2009). ''Disappearing Cryptography: Information Hiding: Steganography & Watermarking'', Morgan Kaufmann Publishers, Amsterdam; Boston {{ISBN?}}</ref> These algorithms range from unsophisticated to very sophisticated, with early algorithms being much easier to detect due to statistical anomalies that were present. The size of the message that is being hidden is a factor in how difficult it is to detect. The overall size of the cover object also plays a factor as well. If the cover object is small and the message is large, this can distort the statistics and make it easier to detect. A larger cover object with a small message decreases the statistics and gives it a better chance of going unnoticed. | |||
| Steganalysis that targets a particular algorithm has much better success as it is able to key in on the anomalies that are left behind. This is because the analysis can perform a targeted search to discover known tendencies since it is aware of the behaviors that it commonly exhibits. When analyzing an image the least significant bits of many images are actually not random. The camera sensor, especially lower-end sensors are not the best quality and can introduce some random bits. This can also be affected by the file compression done on the image. Secret messages can be introduced into the least significant bits in an image and then hidden. A steganography tool can be used to camouflage the secret message in the least significant bits but it can introduce a random area that is too perfect. This area of perfect randomization stands out and can be detected by comparing the least significant bits to the next-to-least significant bits on an image that hasn't been compressed.<ref name=Wanyer2009 /> | |||
| Generally, though, there are many techniques known to be able to hide messages in data using steganographic techniques. None are, by definition, obvious when users employ standard applications, but some can be detected by specialist tools. Others, however, are resistant to detection—or rather it is not possible to reliably distinguish data containing a hidden message from data containing just noise—even when the most sophisticated analysis is performed. Steganography is being used to conceal and deliver more effective cyber attacks, referred to as ''Stegware''. The term Stegware was first introduced in 2017<ref>{{cite web|url=https://www.mcafee.com/blogs/enterprise/seeing-through-stegware/|title=What's Hidden in That Picture Online? Seeing Through "Stegware"|publisher=]|last=Lancioni|first=German|date=16 October 2017}}</ref> to describe any malicious operation involving steganography as a vehicle to conceal an attack. Detection of steganography is challenging, and because of that, not an adequate defence. Therefore, the only way of defeating the threat is to transform data in a way that destroys any hidden messages,<ref>{{cite report |url=https://www.researchgate.net/publication/319943090 |title=Defenders Guide to Steganography |year=2017 |doi=10.13140/RG.2.2.21608.98561 |last1=Wiseman |first1=Simon}}</ref> a process called ]. | |||
| ==Applications== | |||
| ===Use in modern printers=== | |||
| {{Main|Printer steganography}} | |||
| Some modern computer printers use steganography, including ] and ] brand color laser printers. The printers add tiny yellow dots to each page. The barely-visible dots contain encoded printer serial numbers and date and time stamps.<ref>{{cite web |url=https://www.eff.org/press/archives/2005/10/16 |title=Secret Code in Color Printers Lets Government Track You; Tiny Dots Show Where and When You Made Your Print |publisher=] |date=16 October 2005}}</ref> | |||
| ===Example from modern practice=== | |||
| The larger the cover message (in binary data, the number of ]s) relative to the hidden message, the easier it is to hide the hidden message (as an analogy, the larger the "haystack", the easier it is to hide a "needle"). So ]s, which contain much data, are sometimes used to hide messages on the ] and on other digital communication media. It is not clear how common this practice actually is. | |||
| For example, a 24-bit ] uses 8 bits to represent each of the three color values (red, green, and blue) of each ]. The blue alone has 2<sup>8</sup> different levels of blue intensity. The difference between 11111111<sub>2</sub> and 11111110<sub>2</sub> in the value for blue intensity is likely to be undetectable by the human eye. Therefore, the ] can be used more or less undetectably for something else other than color information. If that is repeated for the green and the red elements of each pixel as well, it is possible to encode one letter of ] text for every three ]s. | |||
| Stated somewhat more formally, the objective for making steganographic encoding difficult to detect is to ensure that the changes to the carrier (the original signal) because of the injection of the payload (the signal to covertly embed) are visually (and ideally, statistically) negligible. The changes are indistinguishable from the ] of the carrier. All media can be a carrier, but media with a large amount of redundant or compressible information is better suited. | |||
| From an ] point of view, that means that the ] must have more ] than the "surface" ] requires. There must be ]. For a digital image, it may be ] from the imaging element; for ], it may be noise from recording techniques or ] equipment. In general, electronics that digitize an ] suffer from several noise sources, such as ], ], and ]. The noise provides enough variation in the captured digital information that it can be exploited as a noise cover for hidden data. In addition, ] schemes (such as ]) always introduce some error to the decompressed data, and it is possible to exploit that for steganographic use, as well. | |||
| Although steganography and digital watermarking seem similar, they are not. In steganography, the hidden message should remain intact until it reaches its destination. Steganography can be used for ]ing in which a message (being simply an identifier) is hidden in an image so that its source can be tracked or verified (for example, ]) or even just to identify an image (as in the ]). In such a case, the technique of hiding the message (here, the watermark) must be robust to prevent tampering. However, digital watermarking sometimes requires a brittle watermark, which can be modified easily, to check whether the image has been tampered with. That is the key difference between steganography and digital watermarking. | |||
| ===Alleged use by intelligence services=== | |||
| In 2010, the ] alleged that the ] uses customized steganography software for embedding encrypted text messages inside image files for certain communications with "illegal agents" (agents without diplomatic cover) stationed abroad.<ref>{{cite web|title=Criminal complaint by Special Agent Ricci against alleged Russian agents|url=https://www.justice.gov/opa/documents/062810complaint2.pdf|publisher=United States Department of Justice}}</ref> | |||
| On 23 April 2019 the U.S. Department of Justice unsealed an indictment charging Xiaoqing Zheng, a Chinese businessman and former Principal Engineer at General Electric, with 14 counts of conspiring to steal intellectual property and trade secrets from General Electric. Zheng had allegedly used steganography to exfiltrate 20,000 documents from General Electric to Tianyi Aviation Technology Co. in Nanjing, China, a company the FBI accused him of starting with backing from the Chinese government.<ref>{{cite web|title=GE Engineer Charged in Elaborate Theft of Trade Secrets|url=https://blog.twinstate.com/news/ge-trade-secrets-theft|publisher=Twinstate Technologies}}</ref> | |||
| ===Distributed steganography=== | |||
| There are distributed steganography methods,<ref>{{cite book |chapter=Distributed Steganography |publisher=] |year= 2011|doi=10.1109/IIHMSP.2011.20 |isbn=978-1-4577-1397-2 |title=2011 Seventh International Conference on Intelligent Information Hiding and Multimedia Signal Processing |last1=Liao |first1=Xin |last2=Wen |first2=Qiao-yan |last3=Shi |first3=Sha |pages=153–156 |s2cid=17769131 }}</ref> including methodologies that distribute the payload through multiple carrier files in diverse locations to make detection more difficult. For example, {{US Patent|8527779}} by cryptographer William Easttom (]). | |||
| ===Online challenge=== | |||
| The puzzles that are presented by ] incorporate steganography with cryptography and other solving techniques since 2012.<ref>{{cite news|title=Cicada 3301: The darknet treasure trail reopens|author=Jane Wakefield |url=https://www.bbc.co.uk/news/technology-25667292|work=BBC News|access-date=11 January 2014 |date=9 January 2014}}</ref> Puzzles involving steganography have also been featured in other ]s. | |||
| The communications<ref>{{Cite web|url=http://www.maydaymystery.org/mayday/texts/index.html|title=The texts|website=Maydaymystery.org|access-date=23 November 2017}}</ref><ref>{{Cite web|url=http://www.maydaymystery.org/mayday/recent.html|title=Recent things|website=Maydaymystery.org|access-date=23 November 2017}}</ref> of ] incorporate steganography and other solving techniques since 1981.<ref>{{Cite web|url=http://www.maydaymystery.org/mayday/mystery.html|title=The Mystery|website=Maydaymystery.org|access-date=23 November 2017}}</ref> | |||
| === Computer malware === | |||
| {{Main|Stegomalware}} | |||
| It is possible to steganographically hide computer malware into digital images, videos, audio and various other files in order to evade detection by ]. This type of malware is called stegomalware. It can be activated by external code, which can be malicious or even non-malicious if some vulnerability in the software reading the file is exploited.<ref name="Chaganti-2021">{{Cite report |last1=Chaganti |first1=Raj |last2=R |first2=Vinayakumar |last3=Alazab |first3=Mamoun |last4=Pham |first4=Tuan |date=12 October 2021 |title=Stegomalware: A Systematic Survey of Malware Hiding and Detection in Images, Machine Learning Models and Research Challenges |url=https://www.techrxiv.org/articles/preprint/Stegomalware_A_Systematic_Survey_of_Malware_Hiding_and_Detection_in_Images_Machine_Learning_Models_and_Research_Challenges/16755457/1 |language=en |doi=10.36227/techrxiv.16755457.v1|arxiv=2110.02504 }} (pre-print, not peer reviewed)</ref> | |||
| Stegomalware can be removed from certain files without knowing whether they contain stegomalware or not. This is done through ] (CDR) software, and it involves reprocessing the entire file or removing parts from it.<ref>{{Cite web |last=Votiro |date=30 November 2021 |title=Finding a Content Disarm & Reconstruction (CDR) Vendor |url=https://votiro.com/blog/what-to-look-for-in-cdr-file-sanitization-vendors/ |access-date=11 January 2023 |website=Votiro |language=en-US}}</ref><ref>{{Cite web |title=Content Disarm and Reconstruct – SecureIQLab |date=12 April 2022 |url=https://secureiqlab.com/content-disarm-and-reconstruct/ |access-date=11 January 2023 |language=en-US}}</ref> Actually detecting stegomalware in a file can be difficult and may involve testing the file behaviour in ] environments or ] analysis of the file.<ref name="Chaganti-2021" /> | |||
| == Steganalysis == | |||
| {{main|Steganalysis}} | |||
| === Stegoanalytical algorithms === | |||
| Stegoanalytical algorithms can be cataloged in different ways, highlighting: according to the available information and according to the purpose sought. | |||
| ==== According to the information available ==== | |||
| There is the possibility of cataloging these algorithms based on the information held by the stegoanalyst in terms of clear and encrypted messages. It is a technique similar to cryptography, however, they have several differences: | |||
| * Chosen stego attack: the stegoanalyst perceives the final target stego and the steganographic algorithm used. | |||
| * Known cover attack: the stegoanalyst comprises the initial conductive target and the final target stego. | |||
| * Known stego attack: the stegoanalyst knows the initial carrier target and the final target stego, in addition to the algorithm used. | |||
| * Stego only attack: the stegoanalyst perceives exclusively the stego target. | |||
| * Chosen message attack: the stegoanalyst, following a message selected by him, originates a stego target. | |||
| * Known message attack: the stegoanalyst owns the stego target and the hidden message, which is known to them. | |||
| ==== According to the purpose sought ==== | |||
| The principal purpose of steganography is to transfer information unnoticed, however, it is possible for an attacker to have two different pretensions: | |||
| * Passive steganalysis: does not alter the target stego, therefore, it examines the target stego in order to establish whether it carries hidden information and recovers the hidden message, the key used or both. | |||
| * Active steganalysis: changes the initial stego target, therefore, it seeks to suppress the transfer of information, if it exists. | |||
| ==See also== | |||
| <!-- Please respect alphabetical order --> | |||
| {{div col}} | |||
| * {{annotated link|40-track mode}} | |||
| * {{annotated link|Acrostic}} | |||
| * {{annotated link|BPCS-Steganography}} | |||
| * {{annotated link|Hacktivismo#Camera.2FShy|Camera/Shy}} | |||
| * {{annotated link|Canary trap}} | |||
| * {{annotated link|Warrant canary}} | |||
| * {{annotated link|Covert channel}} | |||
| * {{annotated link|Cryptography}} | |||
| * {{annotated link|Deniable encryption}} | |||
| * {{annotated link|Digital watermarking}} | |||
| * {{annotated link|Invisible ink}} | |||
| * ] – Hiding a message using musical notation | |||
| * {{annotated link|Polybius square}} | |||
| * {{annotated link|Security engineering}} | |||
| * {{annotated link|Semiotics}} | |||
| * {{annotated link|Steganographic file system}} | |||
| * {{annotated link|Steganography tools}} | |||
| * {{annotated link|Audio watermark}} | |||
| * {{annotated link|Visual cryptography}} | |||
| * {{annotated link|Security printing}} | |||
| {{div col end}} | |||
| ==References== | |||
| {{Reflist}} | |||
| ==Sources== | |||
| {{Refbegin}} | |||
| * {{cite book |author=Wayner, Peter |title=Disappearing cryptography: information hiding: steganography & watermarking |publisher=MK/Morgan Kaufmann Publishers |location=Amsterdam |year=2002 |isbn=978-1-558-60769-9 |url=http://www.wayner.org/node/6 |access-date=4 November 2010 |archive-date=24 December 2010 |archive-url=https://web.archive.org/web/20101224093251/http://www.wayner.org/node/6 |url-status=dead }} | |||
| * {{cite book |author=Wayner, Peter |title=Disappearing cryptography 3rd Edition: information hiding: steganography & watermarking |publisher=MK/Morgan Kaufmann Publishers |location=Amsterdam |year=2009 |isbn=978-0-123-74479-1 |url=http://www.wayner.org/node/13 |access-date=4 November 2010 |archive-date=24 December 2010 |archive-url=https://web.archive.org/web/20101224093238/http://www.wayner.org/node/13 |url-status=dead }} | |||
| * {{cite book |author1=Petitcolas, Fabien A.P. |author2=Katzenbeisser, Stefan |title=Information Hiding Techniques for Steganography and Digital Watermarking |publisher=Artech House Publishers |year=2000 |isbn=978-1-580-53035-4 |url=http://petitcolas.net/fabien/publications/book99-ih/ }} | |||
| * {{cite book |author1=Johnson, Neil |author2=Duric, Zoran |author3=Jajodia, Sushil |title=Information hiding: steganography and watermarking: attacks and countermeasures |publisher=Springer |year=2001 |isbn=978-0-792-37204-2}} | |||
| * {{cite book |author1=Petitcolas, Fabien A.P. |author2=Katzenbeisser, Stefan |title=Information Hiding |publisher=Artech House Publishers |year=2016 |isbn=978-1608079285 |url=http://petitcolas.net/book15-ih/ }} | |||
| {{Refend}} | |||
| ==External links== | |||
| {{External links|section|date=May 2024}} | |||
| {{Commons category}} | |||
| * by Chris League, Long Island University, 2015 | |||
| * | |||
| * Papers and information about steganography and steganalysis research from 1995 to the present. Includes Steganography Software Wiki list. Dr. Neil F. Johnson. | |||
| * 2002 paper by ] and Peter Honeyman published in ''Proceedings of the Network and Distributed System Security Symposium'' (San Diego, CA, 6–8 February 2002). NDSS 2002. Internet Society, Washington, D.C. | |||
| * {{Webarchive|url=https://web.archive.org/web/20121023122054/http://firstmonday.org/htbin/cgiwrap/bin/ojs/index.php/fm/article/view/528/449 |date=23 October 2012 }}{{snd}}1996 paper by Craig Rowland detailing the hiding of data in TCP/IP packets. | |||
| * {{Webarchive|url=https://web.archive.org/web/20171216153846/http://stegano.net/tutorials.html |date=16 December 2017 }}. How-to articles on the subject of network steganography (Wireless LANs, VoIP – Steganophony, TCP/IP protocols and mechanisms, Steganographic Router, Inter-protocol steganography). By Krzysztof Szczypiorski and Wojciech Mazurczyk from Network Security Group. | |||
| * | |||
| * , DefCon 12 (1 August 2004) | |||
| * by Blake W. Ford and Khosrow Kaikhah | |||
| * 2006 paper by Konakhovich G. F., Puzyrenko A. Yu. published in ''MK-Press'' Kyiv, Ukraine | |||
| * a Free and Open Source steganography web service. | |||
| {{Cryptography navbox}} | |||
| ] | |||
| {{Espionage}} | |||
| {{intelligence cycle management}} | |||
| {{Hidden messages}} | |||
| {{Authority control}} | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
Latest revision as of 19:03, 24 December 2024
Hiding messages in other messagesFor the process of writing in shorthand, see Stenography. For the prefix "Stego-" as used in taxonomy, see List of commonly used taxonomic affixes.

Steganography (/ˌstɛɡəˈnɒɡrəfi/ STEG-ə-NOG-rə-fee) is the practice of representing information within another message or physical object, in such a manner that the presence of the concealed information would not be evident to an unsuspecting person's examination. In computing/electronic contexts, a computer file, message, image, or video is concealed within another file, message, image, or video. The word steganography comes from Greek steganographia, which combines the words steganós (στεγανός), meaning "covered or concealed", and -graphia (γραφή) meaning "writing".
The first recorded use of the term was in 1499 by Johannes Trithemius in his Steganographia, a treatise on cryptography and steganography, disguised as a book on magic. Generally, the hidden messages appear to be (or to be part of) something else: images, articles, shopping lists, or some other cover text. For example, the hidden message may be in invisible ink between the visible lines of a private letter. Some implementations of steganography that lack a formal shared secret are forms of security through obscurity, while key-dependent steganographic schemes try to adhere to Kerckhoffs's principle.
The advantage of steganography over cryptography alone is that the intended secret message does not attract attention to itself as an object of scrutiny. Plainly visible encrypted messages, no matter how unbreakable they are, arouse interest and may in themselves be incriminating in countries in which encryption is illegal. Whereas cryptography is the practice of protecting the contents of a message alone, steganography is concerned with concealing both the fact that a secret message is being sent and its contents.
Steganography includes the concealment of information within computer files. In digital steganography, electronic communications may include steganographic coding inside of a transport layer, such as a document file, image file, program, or protocol. Media files are ideal for steganographic transmission because of their large size. For example, a sender might start with an innocuous image file and adjust the color of every hundredth pixel to correspond to a letter in the alphabet. The change is so subtle that someone who is not specifically looking for it is unlikely to notice the change.
History

The first recorded uses of steganography can be traced back to 440 BC in Greece, when Herodotus mentions two examples in his Histories. Histiaeus sent a message to his vassal, Aristagoras, by shaving the head of his most trusted servant, "marking" the message onto his scalp, then sending him on his way once his hair had regrown, with the instruction, "When thou art come to Miletus, bid Aristagoras shave thy head, and look thereon." Additionally, Demaratus sent a warning about a forthcoming attack to Greece by writing it directly on the wooden backing of a wax tablet before applying its beeswax surface. Wax tablets were in common use then as reusable writing surfaces, sometimes used for shorthand.
In his work Polygraphiae, Johannes Trithemius developed his so-called "Ave-Maria-Cipher" that can hide information in a Latin praise of God. "Auctor Sapientissimus Conseruans Angelica Deferat Nobis Charitas Potentissimi Creatoris" for example contains the concealed word VICIPEDIA.
Techniques
Main article: List of steganography techniques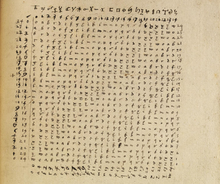
Numerous techniques throughout history have been developed to embed a message within another medium.
Physical
Placing the message in a physical item has been widely used for centuries. Some notable examples include invisible ink on paper, writing a message in Morse code on yarn worn by a courier, microdots, or using a music cipher to hide messages as musical notes in sheet music.
Social steganography
In communities with social or government taboos or censorship, people use cultural steganography—hiding messages in idiom, pop culture references, and other messages they share publicly and assume are monitored. This relies on social context to make the underlying messages visible only to certain readers. Examples include:
- Hiding a message in the title and context of a shared video or image.
- Misspelling names or words that are popular in the media in a given week, to suggest an alternate meaning.
- Hiding a picture that can be traced by using Paint or any other drawing tool.
Digital messages

Since the dawn of computers, techniques have been developed to embed messages in digital cover mediums. The message to conceal is often encrypted, then used to overwrite part of a much larger block of encrypted data or a block of random data (an unbreakable cipher like the one-time pad generates ciphertexts that look perfectly random without the private key).
Examples of this include changing pixels in image or sound files, properties of digital text such as spacing and font choice, Chaffing and winnowing, Mimic functions, modifying the echo of a sound file (Echo Steganography)., and including data in ignored sections of a file.
Images hidden in sound files 1. The word "Misplaced Pages" is drawn using computer software2. The image is converted into an audio file
1. The word "Misplaced Pages" is drawn using computer software2. The image is converted into an audio file 3. Finally, the audio is analysed through a spectrogram, revealing the initial image
3. Finally, the audio is analysed through a spectrogram, revealing the initial image Spectrogram of a hidden image encoded as sound in the song "My Violent Heart" by Nine Inch Nails from the Year Zero album (2007)
Spectrogram of a hidden image encoded as sound in the song "My Violent Heart" by Nine Inch Nails from the Year Zero album (2007)
Steganography in streaming media
Since the era of evolving network applications, steganography research has shifted from image steganography to steganography in streaming media such as Voice over Internet Protocol (VoIP).
In 2003, Giannoula et al. developed a data hiding technique leading to compressed forms of source video signals on a frame-by-frame basis.
In 2005, Dittmann et al. studied steganography and watermarking of multimedia contents such as VoIP.
In 2008, Yongfeng Huang and Shanyu Tang presented a novel approach to information hiding in low bit-rate VoIP speech stream, and their published work on steganography is the first-ever effort to improve the codebook partition by using Graph theory along with Quantization Index Modulation in low bit-rate streaming media.
In 2011 and 2012, Yongfeng Huang and Shanyu Tang devised new steganographic algorithms that use codec parameters as cover object to realise real-time covert VoIP steganography. Their findings were published in IEEE Transactions on Information Forensics and Security.
In 2024, Cheddad & Cheddad proposed a new framework for reconstructing lost or corrupted audio signals using a combination of machine learning techniques and latent information. The main idea of their paper is to enhance audio signal reconstruction by fusing steganography, halftoning (dithering), and state-of-the-art shallow and deep learning methods (e.g., RF, LSTM). This combination of steganography, halftoning, and machine learning for audio signal reconstruction may inspire further research in optimizing this approach or applying it to other domains, such as image reconstruction (i.e., inpainting).
Adaptive-Steganography
Adaptive steganography is a technique for concealing information within digital media by tailoring the embedding process to the specific features of the cover medium. An example of this approach is demonstrated in the work. Their method develops a skin tone detection algorithm, capable of identifying facial features, which is then applied to adaptive steganography. By incorporating face rotation into their approach, the technique aims to enhance its adaptivity to conceal information in a manner that is both less detectable and more robust across various facial orientations within images. This strategy can potentially improve the efficacy of information hiding in both static images and video content.
Cyber-physical systems/Internet of Things
Academic work since 2012 demonstrated the feasibility of steganography for cyber-physical systems (CPS)/the Internet of Things (IoT). Some techniques of CPS/IoT steganography overlap with network steganography, i.e. hiding data in communication protocols used in CPS/the IoT. However, specific techniques hide data in CPS components. For instance, data can be stored in unused registers of IoT/CPS components and in the states of IoT/CPS actuators.
Printed
Digital steganography output may be in the form of printed documents. A message, the plaintext, may be first encrypted by traditional means, producing a ciphertext. Then, an innocuous cover text is modified in some way so as to contain the ciphertext, resulting in the stegotext. For example, the letter size, spacing, typeface, or other characteristics of a cover text can be manipulated to carry the hidden message. Only a recipient who knows the technique used can recover the message and then decrypt it. Francis Bacon developed Bacon's cipher as such a technique.
The ciphertext produced by most digital steganography methods, however, is not printable. Traditional digital methods rely on perturbing noise in the channel file to hide the message, and as such, the channel file must be transmitted to the recipient with no additional noise from the transmission. Printing introduces much noise in the ciphertext, generally rendering the message unrecoverable. There are techniques that address this limitation, one notable example being ASCII Art Steganography.

Although not classic steganography, some types of modern color laser printers integrate the model, serial number, and timestamps on each printout for traceability reasons using a dot-matrix code made of small, yellow dots not recognizable to the naked eye — see printer steganography for details.
Network
In 2015, a taxonomy of 109 network hiding methods was presented by Steffen Wendzel, Sebastian Zander et al. that summarized core concepts used in network steganography research. The taxonomy was developed further in recent years by several publications and authors and adjusted to new domains, such as CPS steganography.
In 1977, Kent concisely described the potential for covert channel signaling in general network communication protocols, even if the traffic is encrypted (in a footnote) in "Encryption-Based Protection for Interactive User/Computer Communication," Proceedings of the Fifth Data Communications Symposium, September 1977.
In 1987, Girling first studied covert channels on a local area network (LAN), identified and realised three obvious covert channels (two storage channels and one timing channel), and his research paper entitled “Covert channels in LAN’s” published in IEEE Transactions on Software Engineering, vol. SE-13 of 2, in February 1987.
In 1989, Wolf implemented covert channels in LAN protocols, e.g. using the reserved fields, pad fields, and undefined fields in the TCP/IP protocol.
In 1997, Rowland used the IP identification field, the TCP initial sequence number and acknowledge sequence number fields in TCP/IP headers to build covert channels.
In 2002, Kamran Ahsan made an excellent summary of research on network steganography.
In 2005, Steven J. Murdoch and Stephen Lewis contributed a chapter entitled "Embedding Covert Channels into TCP/IP" in the "Information Hiding" book published by Springer.
All information hiding techniques that may be used to exchange steganograms in telecommunication networks can be classified under the general term of network steganography. This nomenclature was originally introduced by Krzysztof Szczypiorski in 2003. Contrary to typical steganographic methods that use digital media (images, audio and video files) to hide data, network steganography uses communication protocols' control elements and their intrinsic functionality. As a result, such methods can be harder to detect and eliminate.
Typical network steganography methods involve modification of the properties of a single network protocol. Such modification can be applied to the protocol data unit (PDU), to the time relations between the exchanged PDUs, or both (hybrid methods).
Moreover, it is feasible to utilize the relation between two or more different network protocols to enable secret communication. These applications fall under the term inter-protocol steganography. Alternatively, multiple network protocols can be used simultaneously to transfer hidden information and so-called control protocols can be embedded into steganographic communications to extend their capabilities, e.g. to allow dynamic overlay routing or the switching of utilized hiding methods and network protocols.
Network steganography covers a broad spectrum of techniques, which include, among others:
- Steganophony – the concealment of messages in Voice-over-IP conversations, e.g. the employment of delayed or corrupted packets that would normally be ignored by the receiver (this method is called LACK – Lost Audio Packets Steganography), or, alternatively, hiding information in unused header fields.
- WLAN Steganography – transmission of steganograms in Wireless Local Area Networks. A practical example of WLAN Steganography is the HICCUPS system (Hidden Communication System for Corrupted Networks)
Additional terminology
Further information: Security through obscurityDiscussions of steganography generally use terminology analogous to and consistent with conventional radio and communications technology. However, some terms appear specifically in software and are easily confused. These are the most relevant ones to digital steganographic systems:
The payload is the data covertly communicated. The carrier is the signal, stream, or data file that hides the payload, which differs from the channel, which typically means the type of input, such as a JPEG image. The resulting signal, stream, or data file with the encoded payload is sometimes called the package, stego file, or covert message. The proportion of bytes, samples, or other signal elements modified to encode the payload is called the encoding density and is typically expressed as a number between 0 and 1.
In a set of files, the files that are considered likely to contain a payload are suspects. A suspect identified through some type of statistical analysis can be referred to as a candidate.
Countermeasures and detection
Detecting physical steganography requires a careful physical examination, including the use of magnification, developer chemicals, and ultraviolet light. It is a time-consuming process with obvious resource implications, even in countries that employ many people to spy on their fellow nationals. However, it is feasible to screen mail of certain suspected individuals or institutions, such as prisons or prisoner-of-war (POW) camps.
During World War II, prisoner of war camps gave prisoners specially-treated paper that would reveal invisible ink. An article in the 24 June 1948 issue of Paper Trade Journal by the Technical Director of the United States Government Printing Office had Morris S. Kantrowitz describe in general terms the development of this paper. Three prototype papers (Sensicoat, Anilith, and Coatalith) were used to manufacture postcards and stationery provided to German prisoners of war in the US and Canada. If POWs tried to write a hidden message, the special paper rendered it visible. The US granted at least two patents related to the technology, one to Kantrowitz, U.S. patent 2,515,232, "Water-Detecting paper and Water-Detecting Coating Composition Therefor," patented 18 July 1950, and an earlier one, "Moisture-Sensitive Paper and the Manufacture Thereof," U.S. patent 2,445,586, patented 20 July 1948. A similar strategy issues prisoners with writing paper ruled with a water-soluble ink that runs in contact with water-based invisible ink.
In computing, steganographically encoded package detection is called steganalysis. The simplest method to detect modified files, however, is to compare them to known originals. For example, to detect information being moved through the graphics on a website, an analyst can maintain known clean copies of the materials and then compare them against the current contents of the site. The differences, if the carrier is the same, comprise the payload. In general, using extremely high compression rates makes steganography difficult but not impossible. Compression errors provide a hiding place for data, but high compression reduces the amount of data available to hold the payload, raising the encoding density, which facilitates easier detection (in extreme cases, even by casual observation).
There are a variety of basic tests that can be done to identify whether or not a secret message exists. This process is not concerned with the extraction of the message, which is a different process and a separate step. The most basic approaches of steganalysis are visual or aural attacks, structural attacks, and statistical attacks. These approaches attempt to detect the steganographic algorithms that were used. These algorithms range from unsophisticated to very sophisticated, with early algorithms being much easier to detect due to statistical anomalies that were present. The size of the message that is being hidden is a factor in how difficult it is to detect. The overall size of the cover object also plays a factor as well. If the cover object is small and the message is large, this can distort the statistics and make it easier to detect. A larger cover object with a small message decreases the statistics and gives it a better chance of going unnoticed.
Steganalysis that targets a particular algorithm has much better success as it is able to key in on the anomalies that are left behind. This is because the analysis can perform a targeted search to discover known tendencies since it is aware of the behaviors that it commonly exhibits. When analyzing an image the least significant bits of many images are actually not random. The camera sensor, especially lower-end sensors are not the best quality and can introduce some random bits. This can also be affected by the file compression done on the image. Secret messages can be introduced into the least significant bits in an image and then hidden. A steganography tool can be used to camouflage the secret message in the least significant bits but it can introduce a random area that is too perfect. This area of perfect randomization stands out and can be detected by comparing the least significant bits to the next-to-least significant bits on an image that hasn't been compressed.
Generally, though, there are many techniques known to be able to hide messages in data using steganographic techniques. None are, by definition, obvious when users employ standard applications, but some can be detected by specialist tools. Others, however, are resistant to detection—or rather it is not possible to reliably distinguish data containing a hidden message from data containing just noise—even when the most sophisticated analysis is performed. Steganography is being used to conceal and deliver more effective cyber attacks, referred to as Stegware. The term Stegware was first introduced in 2017 to describe any malicious operation involving steganography as a vehicle to conceal an attack. Detection of steganography is challenging, and because of that, not an adequate defence. Therefore, the only way of defeating the threat is to transform data in a way that destroys any hidden messages, a process called Content Threat Removal.
Applications
Use in modern printers
Main article: Printer steganographySome modern computer printers use steganography, including Hewlett-Packard and Xerox brand color laser printers. The printers add tiny yellow dots to each page. The barely-visible dots contain encoded printer serial numbers and date and time stamps.
Example from modern practice
The larger the cover message (in binary data, the number of bits) relative to the hidden message, the easier it is to hide the hidden message (as an analogy, the larger the "haystack", the easier it is to hide a "needle"). So digital pictures, which contain much data, are sometimes used to hide messages on the Internet and on other digital communication media. It is not clear how common this practice actually is.
For example, a 24-bit bitmap uses 8 bits to represent each of the three color values (red, green, and blue) of each pixel. The blue alone has 2 different levels of blue intensity. The difference between 111111112 and 111111102 in the value for blue intensity is likely to be undetectable by the human eye. Therefore, the least significant bit can be used more or less undetectably for something else other than color information. If that is repeated for the green and the red elements of each pixel as well, it is possible to encode one letter of ASCII text for every three pixels.
Stated somewhat more formally, the objective for making steganographic encoding difficult to detect is to ensure that the changes to the carrier (the original signal) because of the injection of the payload (the signal to covertly embed) are visually (and ideally, statistically) negligible. The changes are indistinguishable from the noise floor of the carrier. All media can be a carrier, but media with a large amount of redundant or compressible information is better suited.
From an information theoretical point of view, that means that the channel must have more capacity than the "surface" signal requires. There must be redundancy. For a digital image, it may be noise from the imaging element; for digital audio, it may be noise from recording techniques or amplification equipment. In general, electronics that digitize an analog signal suffer from several noise sources, such as thermal noise, flicker noise, and shot noise. The noise provides enough variation in the captured digital information that it can be exploited as a noise cover for hidden data. In addition, lossy compression schemes (such as JPEG) always introduce some error to the decompressed data, and it is possible to exploit that for steganographic use, as well.
Although steganography and digital watermarking seem similar, they are not. In steganography, the hidden message should remain intact until it reaches its destination. Steganography can be used for digital watermarking in which a message (being simply an identifier) is hidden in an image so that its source can be tracked or verified (for example, Coded Anti-Piracy) or even just to identify an image (as in the EURion constellation). In such a case, the technique of hiding the message (here, the watermark) must be robust to prevent tampering. However, digital watermarking sometimes requires a brittle watermark, which can be modified easily, to check whether the image has been tampered with. That is the key difference between steganography and digital watermarking.
Alleged use by intelligence services
In 2010, the Federal Bureau of Investigation alleged that the Russian foreign intelligence service uses customized steganography software for embedding encrypted text messages inside image files for certain communications with "illegal agents" (agents without diplomatic cover) stationed abroad.
On 23 April 2019 the U.S. Department of Justice unsealed an indictment charging Xiaoqing Zheng, a Chinese businessman and former Principal Engineer at General Electric, with 14 counts of conspiring to steal intellectual property and trade secrets from General Electric. Zheng had allegedly used steganography to exfiltrate 20,000 documents from General Electric to Tianyi Aviation Technology Co. in Nanjing, China, a company the FBI accused him of starting with backing from the Chinese government.
Distributed steganography
There are distributed steganography methods, including methodologies that distribute the payload through multiple carrier files in diverse locations to make detection more difficult. For example, U.S. patent 8,527,779 by cryptographer William Easttom (Chuck Easttom).
Online challenge
The puzzles that are presented by Cicada 3301 incorporate steganography with cryptography and other solving techniques since 2012. Puzzles involving steganography have also been featured in other alternate reality games.
The communications of The May Day mystery incorporate steganography and other solving techniques since 1981.
Computer malware
Main article: StegomalwareIt is possible to steganographically hide computer malware into digital images, videos, audio and various other files in order to evade detection by antivirus software. This type of malware is called stegomalware. It can be activated by external code, which can be malicious or even non-malicious if some vulnerability in the software reading the file is exploited.
Stegomalware can be removed from certain files without knowing whether they contain stegomalware or not. This is done through content disarm and reconstruction (CDR) software, and it involves reprocessing the entire file or removing parts from it. Actually detecting stegomalware in a file can be difficult and may involve testing the file behaviour in virtual environments or deep learning analysis of the file.
Steganalysis
Main article: SteganalysisStegoanalytical algorithms
Stegoanalytical algorithms can be cataloged in different ways, highlighting: according to the available information and according to the purpose sought.
According to the information available
There is the possibility of cataloging these algorithms based on the information held by the stegoanalyst in terms of clear and encrypted messages. It is a technique similar to cryptography, however, they have several differences:
- Chosen stego attack: the stegoanalyst perceives the final target stego and the steganographic algorithm used.
- Known cover attack: the stegoanalyst comprises the initial conductive target and the final target stego.
- Known stego attack: the stegoanalyst knows the initial carrier target and the final target stego, in addition to the algorithm used.
- Stego only attack: the stegoanalyst perceives exclusively the stego target.
- Chosen message attack: the stegoanalyst, following a message selected by him, originates a stego target.
- Known message attack: the stegoanalyst owns the stego target and the hidden message, which is known to them.
According to the purpose sought
The principal purpose of steganography is to transfer information unnoticed, however, it is possible for an attacker to have two different pretensions:
- Passive steganalysis: does not alter the target stego, therefore, it examines the target stego in order to establish whether it carries hidden information and recovers the hidden message, the key used or both.
- Active steganalysis: changes the initial stego target, therefore, it seeks to suppress the transfer of information, if it exists.
See also
- 40-track mode – Method for hiding data on a floppy disk
- Acrostic – Text formed from parts of another text
- BPCS-Steganography – computer message obfuscation technologyPages displaying wikidata descriptions as a fallback
- Camera/Shy
- Canary trap – Method for exposing an information leak
- Warrant canary – Method of indirect notification of a subpoena
- Covert channel – Computer security attack
- Cryptography – Practice and study of secure communication techniques
- Deniable encryption – Encryption techniques where an adversary cannot prove that the plaintext data exists
- Digital watermarking – Marker covertly embedded in a signal
- Invisible ink – Substance used for writing which is invisible and can later be made visible
- Musical Steganography – Hiding a message using musical notation
- Polybius square – Type of code
- Security engineering – Process of incorporating security controls into an information system
- Semiotics – Study of signs and sign processes
- Steganographic file system
- Steganography tools – Software for embedding hidden data inside a carrier file
- Audio watermark – Electronic identifier embedded in an audio signal
- Visual cryptography – Cryptographic technique
- Security printing – Field of the printing industry for banknotes and other security products
References
- "Definition of STEGANOGRAPHY". Merriam-webster.com. Retrieved 14 December 2021.
- Fridrich, Jessica; M. Goljan; D. Soukal (2004). Delp Iii, Edward J; Wong, Ping W (eds.). "Searching for the Stego Key" (PDF). Proc. SPIE, Electronic Imaging, Security, Steganography, and Watermarking of Multimedia Contents VI. Security, Steganography, and Watermarking of Multimedia Contents VI. 5306: 70–82. Bibcode:2004SPIE.5306...70F. doi:10.1117/12.521353. S2CID 6773772. Retrieved 23 January 2014.
- Pahati, OJ (29 November 2001). "Confounding Carnivore: How to Protect Your Online Privacy". AlterNet. Archived from the original on 16 July 2007. Retrieved 2 September 2008.
- Petitcolas, FAP; Anderson RJ; Kuhn MG (1999). "Information Hiding: A survey" (PDF). Proceedings of the IEEE. 87 (7): 1062–78. CiteSeerX 10.1.1.333.9397. doi:10.1109/5.771065. Retrieved 2 September 2008.
- "Polygraphiae (cf. p. 71f)" (in German). Digitale Sammlungen. Retrieved 27 May 2015.
- ^ "The Wartime Spies Who Used Knitting as an Espionage Tool – Atlas Obscura". Pocket. Retrieved 4 March 2020.
- Newman, Lily Hay. "How a Saxophonist Tricked the KGB by Encrypting Secrets in Music". Wired. ISSN 1059-1028. Archived from the original on 8 June 2022. Retrieved 9 June 2022.
- Social Steganography: how teens smuggle meaning past the authority figures in their lives, Boing Boing, 22 May 2013. Retrieved 7 June 2014.
- Social Steganography Archived 14 July 2014 at the Wayback Machine, Scenario Magazine, 2013.
- Cheddad, Abbas; Condell, Joan; Curran, Kevin; Mc Kevitt, Paul (2010). "Digital image steganography: Survey and analysis of current methods". Signal Processing. 90 (3): 727–752. Bibcode:2010SigPr..90..727C. doi:10.1016/j.sigpro.2009.08.010.
- Bender, W.; Gruhl, D.; Morimoto, N.; Lu, A. (1996). "Techniques for data hiding" (PDF). IBM Systems Journal. 35 (3.4). IBM Corp.: 313–336. doi:10.1147/sj.353.0313. ISSN 0018-8670. S2CID 16672162. Archived from the original (PDF) on 11 June 2020.
- Giannoula, A.; Hatzinakos, D. (2003). "Compressive data hiding for video signals". Proceedings 2003 International Conference on Image Processing (Cat. No.03CH37429). Vol. 1. IEEE. pp. I–529–32. doi:10.1109/icip.2003.1247015. ISBN 0780377508. S2CID 361883.
- Dittmann, Jana; Hesse, Danny; Hillert, Reyk (21 March 2005). Delp Iii, Edward J; Wong, Ping W (eds.). "Steganography and steganalysis in voice-over IP scenarios: operational aspects and first experiences with a new steganalysis tool set". Security, Steganography, and Watermarking of Multimedia Contents VII. 5681. SPIE: 607. Bibcode:2005SPIE.5681..607D. doi:10.1117/12.586579. S2CID 206413447.
- B. Xiao, Y. Huang, and S. Tang, "An Approach to Information Hiding in Low Bit-Rate Speech Stream", in IEEE GLOBECOM 2008, IEEE, pp. 371–375, 2008. ISBN 978-1-4244-2324-8.
- Huang, Yong Feng; Tang, Shanyu; Yuan, Jian (June 2011). "Steganography in Inactive Frames of VoIP Streams Encoded by Source Codec" (PDF). IEEE Transactions on Information Forensics and Security. 6 (2): 296–306. doi:10.1109/tifs.2011.2108649. ISSN 1556-6013. S2CID 15096702.
- Huang, Yongfeng; Liu, Chenghao; Tang, Shanyu; Bai, Sen (December 2012). "Steganography Integration Into a Low-Bit Rate Speech Codec" (PDF). IEEE Transactions on Information Forensics and Security. 7 (6): 1865–1875. doi:10.1109/tifs.2012.2218599. ISSN 1556-6013. S2CID 16539562.
- Ghosal, Sudipta Kr; Mukhopadhyay, Souradeep; Hossain, Sabbir; Sarkar, Ram (2020). "Application of Lah transform for security and privacy of data through information hiding in telecommunication". Transactions on Emerging Telecommunications Technologies. 32 (2). doi:10.1002/ett.3984. S2CID 225866797.
- Cheddad, Zohra Adila; Cheddad, Abbas (2024). "Active Restoration of Lost Audio Signals Using Machine Learning and Latent Information". Proceedings 2023 Intelligent Systems Conference (IntelliSys'23). Lecture Notes in Networks and Systems. Vol. 822. LNCS,Springer. pp. 1–16. doi:10.1007/978-3-031-47721-8_1. ISBN 978-3-031-47720-1.
- Cheddad, Abbas; Condell, Joan; Curran, Kevin; Mc Kevitt, Paul (2009). "A skin tone detection algorithm for an adaptive approach to steganography". Signal Processing. 89 (12): 2465–2478. Bibcode:2009SigPr..89.2465C. doi:10.1016/j.sigpro.2009.04.022.
- Wendzel, Steffen; Mazurczyk, Wojciech; Haas, Georg. "Don't You Touch My Nuts: Information Hiding In Cyber Physical Systems Using Smart Buildings". Proceedings of the 2017 IEEE Security & Privacy Workshops. IEEE.
- Tuptuk, Nilufer; Hailes, Stephen. "Covert channel attacks in pervasive computing". Proceedings 2015 IEEE International Conference on Pervasive Computing and Communications (PerCom).
- Vincent Chu. "ASCII Art Steganography". Pictureworthsthousandwords.appspot.com.
- Wendzel, Steffen; Zander, Sebastian; Fechner, Bernhard; Herdin, Christian (16 April 2015). "Pattern-Based Survey and Categorization of Network Covert Channel Techniques". ACM Computing Surveys. 47 (3): 1–26. arXiv:1406.2901. doi:10.1145/2684195. S2CID 14654993.
- Mazurczyk, Wojciech; Wendzel, Steffen; Cabaj, Krzysztof (27 August 2018). "Towards Deriving Insights into Data Hiding Methods Using Pattern-based Approach". Proceedings of the 13th International Conference on Availability, Reliability and Security. pp. 1–10. doi:10.1145/3230833.3233261. ISBN 9781450364485. S2CID 51976841.
- Hildebrandt, Mario; Altschaffel, Robert; Lamshöft, Kevin; Lange, Matthias; Szemkus, Martin; Neubert, Tom; Vielhauer, Claus; Ding, Yongjian; Dittmann, Jana (2020). "Threat Analysis of Steganographic and Covert Communication in Nuclear I&C Systems". International Conference on Nuclear Security: Sustaining and Strengthening Efforts.
- Mileva, Aleksandra; Velinov, Aleksandar; Hartmann, Laura; Wendzel, Steffen; Mazurczyk, Wojciech (May 2021). "Comprehensive analysis of MQTT 5.0 susceptibility to network covert channels". Computers & Security. 104: 102207. doi:10.1016/j.cose.2021.102207. S2CID 232342523.
- Girling, C.G. (February 1987). "Covert Channels in LAN's". IEEE Transactions on Software Engineering. SE-13 (2): 292–296. doi:10.1109/tse.1987.233153. ISSN 0098-5589. S2CID 3042941.
- M. Wolf, “Covert channels in LAN protocols,” in Proceedings of the Workshop on Local Area Network Security (LANSEC’89) (T.A. Berson and T. Beth, eds.), pp. 91–102, 1989.
- Rowland, Craig H. (5 May 1997). "Covert channels in the TCP/IP protocol suite". First Monday. 2 (5). doi:10.5210/fm.v2i5.528. ISSN 1396-0466.
- Kamran Ahsan, “Covert Channel Analysis and Data Hiding in TCP/IP,” MSc Thesis, University of Toronto, 2002.
- Murdoch, Steven J.; Lewis, Stephen (2005), "Embedding Covert Channels into TCP/IP", Information Hiding, Springer Berlin Heidelberg, pp. 247–261, doi:10.1007/11558859_19, ISBN 9783540290391
- Krzysztof Szczypiorski (4 November 2003). "Steganography in TCP/IP Networks. State of the Art and a Proposal of a New System – HICCUPS" (PDF). Institute of Telecommunications Seminar. Retrieved 17 June 2010.
- Patrick Philippe Meier (5 June 2009). "Steganography 2.0: Digital Resistance against Repressive Regimes". irevolution.wordpress.com. Retrieved 17 June 2010.
- Craig Rowland (May 1997). "Covert Channels in the TCP/IP Suite". First Monday Journal. Archived from the original on 26 January 2013. Retrieved 16 June 2010.
- Steven J. Murdoch & Stephen Lewis (2005). "Embedding Covert Channels into TCP/IP" (PDF). Information Hiding Workshop. Retrieved 16 June 2010.
- Kamran Ahsan & Deepa Kundur (December 2002). "Practical Data Hiding in TCP/IP" (PDF). ACM Wksp. Multimedia Security. Archived from the original (PDF) on 29 October 2012. Retrieved 16 June 2010.
- Kundur D. & Ahsan K. (April 2003). "Practical Internet Steganography: Data Hiding in IP" (PDF). Texas Wksp. Security of Information Systems. Archived from the original (PDF) on 29 October 2012. Retrieved 16 June 2010.
- Wojciech Mazurczyk & Krzysztof Szczypiorski (November 2008). "Steganography of VoIP Streams". On the Move to Meaningful Internet Systems: OTM 2008. Lecture Notes in Computer Science. Vol. 5332. pp. 1001–1018. arXiv:0805.2938. doi:10.1007/978-3-540-88873-4_6. ISBN 978-3-540-88872-7. S2CID 14336157.
- Bartosz Jankowski; Wojciech Mazurczyk & Krzysztof Szczypiorski (11 May 2010). "Information Hiding Using Improper Frame Padding". arXiv:1005.1925 .
- Wendzel, Steffen; Keller, Joerg (20 October 2011). "Low-Attention Forwarding for Mobile Network Covert Channels". Communications and Multimedia Security. Lecture Notes in Computer Science. Vol. 7025. pp. 122–133. doi:10.1007/978-3-642-24712-5_10. ISBN 978-3-642-24711-8. Retrieved 4 September 2016.
- Mazurczyk, Wojciech; Wendzel, Steffen; Zander, Sebastian; Houmansadr, Amir; Szczypiorski, Krzysztof (2016). Information Hiding in Communication Networks: Fundamentals, Mechanisms, and Applications (1 ed.). Wiley-IEEE. ISBN 978-1-118-86169-1.
- Józef Lubacz; Wojciech Mazurczyk; Krzysztof Szczypiorski (February 2010). "Vice Over IP: The VoIP Steganography Threat". IEEE Spectrum. Retrieved 11 February 2010.
- Krzysztof Szczypiorski (October 2003). "HICCUPS: Hidden Communication System for Corrupted Networks" (PDF). In Proc. of: The Tenth International Multi-Conference on Advanced Computer Systems ACS'2003, pp. 31–40. Retrieved 11 February 2010.
- ^ Wayner, Peter (2009). Disappearing Cryptography: Information Hiding: Steganography & Watermarking, Morgan Kaufmann Publishers, Amsterdam; Boston
- Lancioni, German (16 October 2017). "What's Hidden in That Picture Online? Seeing Through "Stegware"". McAfee.
- Wiseman, Simon (2017). Defenders Guide to Steganography (Report). doi:10.13140/RG.2.2.21608.98561.
- "Secret Code in Color Printers Lets Government Track You; Tiny Dots Show Where and When You Made Your Print". Electronic Frontier Foundation. 16 October 2005.
- "Criminal complaint by Special Agent Ricci against alleged Russian agents" (PDF). United States Department of Justice.
- "GE Engineer Charged in Elaborate Theft of Trade Secrets". Twinstate Technologies.
- Liao, Xin; Wen, Qiao-yan; Shi, Sha (2011). "Distributed Steganography". 2011 Seventh International Conference on Intelligent Information Hiding and Multimedia Signal Processing. IEEE. pp. 153–156. doi:10.1109/IIHMSP.2011.20. ISBN 978-1-4577-1397-2. S2CID 17769131.
- Jane Wakefield (9 January 2014). "Cicada 3301: The darknet treasure trail reopens". BBC News. Retrieved 11 January 2014.
- "The texts". Maydaymystery.org. Retrieved 23 November 2017.
- "Recent things". Maydaymystery.org. Retrieved 23 November 2017.
- "The Mystery". Maydaymystery.org. Retrieved 23 November 2017.
- ^ Chaganti, Raj; R, Vinayakumar; Alazab, Mamoun; Pham, Tuan (12 October 2021). Stegomalware: A Systematic Survey of Malware Hiding and Detection in Images, Machine Learning Models and Research Challenges (Report). arXiv:2110.02504. doi:10.36227/techrxiv.16755457.v1. (pre-print, not peer reviewed)
- Votiro (30 November 2021). "Finding a Content Disarm & Reconstruction (CDR) Vendor". Votiro. Retrieved 11 January 2023.
- "Content Disarm and Reconstruct – SecureIQLab". 12 April 2022. Retrieved 11 January 2023.
Sources
- Wayner, Peter (2002). Disappearing cryptography: information hiding: steganography & watermarking. Amsterdam: MK/Morgan Kaufmann Publishers. ISBN 978-1-558-60769-9. Archived from the original on 24 December 2010. Retrieved 4 November 2010.
- Wayner, Peter (2009). Disappearing cryptography 3rd Edition: information hiding: steganography & watermarking. Amsterdam: MK/Morgan Kaufmann Publishers. ISBN 978-0-123-74479-1. Archived from the original on 24 December 2010. Retrieved 4 November 2010.
- Petitcolas, Fabien A.P.; Katzenbeisser, Stefan (2000). Information Hiding Techniques for Steganography and Digital Watermarking. Artech House Publishers. ISBN 978-1-580-53035-4.
- Johnson, Neil; Duric, Zoran; Jajodia, Sushil (2001). Information hiding: steganography and watermarking: attacks and countermeasures. Springer. ISBN 978-0-792-37204-2.
- Petitcolas, Fabien A.P.; Katzenbeisser, Stefan (2016). Information Hiding. Artech House Publishers. ISBN 978-1608079285.
External links
| This section's use of external links may not follow Misplaced Pages's policies or guidelines. Please improve this article by removing excessive or inappropriate external links, and converting useful links where appropriate into footnote references. (May 2024) (Learn how and when to remove this message) |
- An overview of digital steganography, particularly within images, for the computationally curious by Chris League, Long Island University, 2015
- Examples showing images hidden in other images
- Information Hiding: Steganography & Digital Watermarking. Papers and information about steganography and steganalysis research from 1995 to the present. Includes Steganography Software Wiki list. Dr. Neil F. Johnson.
- Detecting Steganographic Content on the Internet. 2002 paper by Niels Provos and Peter Honeyman published in Proceedings of the Network and Distributed System Security Symposium (San Diego, CA, 6–8 February 2002). NDSS 2002. Internet Society, Washington, D.C.
- Covert Channels in the TCP/IP Suite Archived 23 October 2012 at the Wayback Machine – 1996 paper by Craig Rowland detailing the hiding of data in TCP/IP packets.
- Network Steganography Centre Tutorials Archived 16 December 2017 at the Wayback Machine. How-to articles on the subject of network steganography (Wireless LANs, VoIP – Steganophony, TCP/IP protocols and mechanisms, Steganographic Router, Inter-protocol steganography). By Krzysztof Szczypiorski and Wojciech Mazurczyk from Network Security Group.
- Invitation to BPCS-Steganography.
- Steganography by Michael T. Raggo, DefCon 12 (1 August 2004)
- File Format Extension Through Steganography by Blake W. Ford and Khosrow Kaikhah
- Computer steganography. Theory and practice with Mathcad (Rus) 2006 paper by Konakhovich G. F., Puzyrenko A. Yu. published in MK-Press Kyiv, Ukraine
- stegano a Free and Open Source steganography web service.
| Espionage | |
|---|---|
| Analysis | |
| Devices and communications | |
| Tradecraft and techniques | |
| Operations | |
| Intelligence management | |||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Collection |
| ||||||||||||||
| Analysis | |||||||||||||||
| Dissemination | |||||||||||||||
| Hidden messages | |
|---|---|
| Main | |
| Audio | |
| Numeric | |
| Visual | |
| Other | |