| Revision as of 16:25, 18 September 2019 edit80.136.184.204 (talk)No edit summary← Previous edit | Latest revision as of 13:37, 18 December 2024 edit undoAnnh07 (talk | contribs)Extended confirmed users, Page movers, New page reviewers, Pending changes reviewers, Rollbackers43,804 editsm Reverted edits by Gracey creates (talk) to last version by 168.229.254.62Tag: Rollback | ||
| (636 intermediate revisions by more than 100 users not shown) | |||
| Line 1: | Line 1: | ||
| {{Short description|Legal control of the internet}} | |||
| {{Use dmy dates|date=November 2020}} | |||
| {{Internet}} | {{Internet}} | ||
| '''Internet censorship''' is the ] of what can be accessed, published, or viewed on the ] enacted by regulators, or on their own initiative. Individuals and organizations may engage in ] for moral, religious, or business reasons, to conform to societal norms, due to intimidation, or out of fear of legal or other consequences.<ref name="NYT-20181015">{{cite news |author=The Editorial Board |title=There May Soon Be Three Internets. America's Won't Necessarily Be the Best. - A breakup of the web grants privacy, security and freedom to some, and not so much to others. |url=https://www.nytimes.com/2018/10/15/opinion/internet-google-china-balkanization.html |date=15 October 2018 |work=] |accessdate=16 October 2018 }}</ref><ref name="NYT-20140311">{{cite news |last1=Schmidt |first1=Eric E. |last2=Cohen |first2=Jared |authorlink1=Eric Schmidt |authorlink2=Jared Cohen |title=The Future of Internet Freedom |url=https://www.nytimes.com/2014/03/12/opinion/the-future-of-internet-freedom.html |date=11 March 2014 |work=] |accessdate=11 March 2014 }}</ref> | |||
| '''Internet censorship''' is the legal ] of what can be accessed, published, or viewed on the ]. ] is most often applied to specific ]s (such as ''Misplaced Pages.org'', for example) but exceptionally may extend to all Internet resources located outside the ] of the censoring state. Internet censorship may also put restrictions on what information can be made internet accessible.<ref>{{Cite web |url=https://www.iplocation.net/internet-censorship |access-date=2021-05-01 |title=What is Internet Censorship? |archive-date=1 May 2021 |website=www.iplocation.net |archive-url=https://web.archive.org/web/20210501213345/https://www.iplocation.net/internet-censorship|url-status=live}}</ref> Organizations providing internet access{{snd}}such as schools and libraries{{snd}} may choose to preclude access to material that they consider undesirable, offensive, ] or even illegal, and regard this as ethical behavior rather than censorship. Individuals and organizations may engage in ] of material they publish, for moral, religious, or business reasons, to conform to ], political views, due to intimidation, or out of fear of legal or other consequences.<ref name="NYT-20181015">{{cite news |author=The Editorial Board |title=There May Soon Be Three Internets. America's Won't Necessarily Be the Best. - A breakup of the web grants privacy, security and freedom to some, and not so much to others. |url=https://www.nytimes.com/2018/10/15/opinion/internet-google-china-balkanization.html |date=15 October 2018 |work=] |access-date=16 October 2018 |archive-date=9 July 2021 |archive-url=https://web.archive.org/web/20210709190555/https://www.nytimes.com/2018/10/15/opinion/internet-google-china-balkanization.html |url-status=live |url-access=subscription}}</ref><ref name="NYT-20140311">{{cite news |last1=Schmidt |first1=Eric E. |last2=Cohen |first2=Jared |author-link1=Eric Schmidt |author-link2=Jared Cohen |title=The Future of Internet Freedom |url=https://www.nytimes.com/2014/03/12/opinion/the-future-of-internet-freedom.html |date=11 March 2014 |work=] |access-date=11 March 2014 |archive-url=https://web.archive.org/web/20201212132407/https://www.nytimes.com/2014/03/12/opinion/the-future-of-internet-freedom.html |archive-date=12 December 2020 |url-status=live }}</ref> | |||
| The extent of Internet censorship varies on a country-to-country basis. While most democratic countries have moderate Internet censorship, other countries go as far as to limit the access of information such as news and suppress discussion among citizens.<ref name="NYT-20140311" /> Internet censorship also occurs in response to or in anticipation of events such as elections, protests, and riots. An example is the increased censorship due to the events of the ]. Other areas of censorship include copyrights, defamation, harassment, and obscene material. | |||
| The extent of Internet censorship varies on a country-to-country basis. While some countries have moderate Internet censorship, other countries go as far as to limit the access of information such as news and suppress and silence discussion among citizens.<ref name="NYT-20140311" /> Internet censorship also occurs in response to or in anticipation of events such as elections, protests, and riots. An example is the increased censorship due to the events of the ]. Other types of censorship include the ], ], ], and various obscene material claims as a way to deliberately suppress content. | |||
| Government agencies have various tools to implement restrictions but supporters of internet freedom are trying to overcome such barriers and filters. Access to restricted sites was effectively blocked by tracing and blocking DNS requests but companies like baidu.com, mail.ru, rambler.ru, talktalk.co.uk, wanadoo.fr, Cloudflare, Mozilla and Google are shifting DNS to TLS layer and making it difficult to intercept.<ref>{{Cite web|url=https://sslretail.com/blog/dns-over-https-ultimate-guide/|title=DNS over HTTPS (DoH): Ultimate Guide (.pdf) - SSL Retail|website=sslretail.com|access-date=2019-02-13}}</ref> | |||
| Support for and opposition to Internet censorship also varies. In a ] 71% of respondents agreed that "censorship should exist in some form on the Internet". In the same survey 83% agreed that "access to the Internet should be considered a basic human right" and 86% agreed that "] should be guaranteed on the Internet". Perception of internet censorship in the US is largely based on the First Amendment and the right for expansive free speech and access to content without regard to the consequences.<ref>{{Cite journal|last=Goldberg|first=Erica |
Support for and opposition to Internet censorship also varies. In a ], 71% of respondents agreed that "censorship should exist in some form on the Internet". In the same survey, 83% agreed that "access to the Internet should be considered a basic human right" and 86% agreed that "] should be guaranteed on the Internet". Perception of internet censorship in the US is largely based on the ] and the right for expansive free speech and access to content without regard to the consequences.<ref>{{Cite journal |last=Goldberg|first=Erica|journal=Columbia Law Review|volume=116|issue=3|pages=687–694|jstor=43783393 |year=2016|title=Free Speech Consequentialism}}</ref> According to ], over 400 million people use ]s to ] or for increased user ].<ref name="Guardian 5 December 2014"/> | ||
| ==Overview== | ==Overview== | ||
| Many of the challenges associated with Internet censorship are similar to those for offline censorship of more traditional media such as newspapers, magazines, books, music, radio, television, and film. One difference is that national borders are more permeable online: residents of a country that bans certain information can find it on websites hosted outside the country. Thus censors must work to prevent access to information even though they lack physical or legal control over the websites themselves. This in turn requires the use of technical censorship methods that are unique to the Internet, such as site blocking and content filtering.<ref name=UNESCO-2011/> | Many of the challenges associated with Internet censorship are similar to those for offline censorship of more traditional media such as newspapers, magazines, books, music, radio, television, and film. One difference is that national borders are more permeable online: residents of a country that bans certain information can find it on websites hosted outside the country. Thus censors must work to prevent ] even though they lack physical or legal control over the websites themselves. This in turn requires the use of technical censorship methods that are unique to the Internet, such as site blocking and content filtering.<ref name=UNESCO-2011/> | ||
| Views about the feasibility and effectiveness of Internet censorship have evolved in parallel with the development of the Internet and censorship technologies: | Views about the feasibility and effectiveness of Internet censorship have evolved in parallel with the development of the Internet and censorship technologies: | ||
| * A 1993 ''Time Magazine'' article quotes computer scientist ], one of the founders of the ], as saying "The Net interprets censorship as damage and routes around it."<ref>, Philip Elmer-Dewitt, ''Time'', 6 December 1993, No.49</ref> | * A 1993 '']'' article quotes computer scientist ], one of the founders of the ], as saying "The Net interprets censorship as damage and routes around it."<ref>, Philip Elmer-Dewitt, ''Time'', 6 December 1993, No.49</ref> | ||
| * In November 2007, "Father of the Internet" ] stated that he sees government control of the Internet failing because the Web is almost entirely privately owned.<ref>, Pedro Fonseca, Reuters, |
* In November 2007, "Father of the Internet" ] stated that he sees government control of the Internet failing because the Web is almost entirely privately owned.<ref> {{Webarchive|url=https://web.archive.org/web/20201103032125/https://www.reuters.com/article/reutersEdge/idUSN1420689320071114?sp=true |date=3 November 2020 }}, Pedro Fonseca, Reuters, 15 November 2006</ref> | ||
| * A report of research conducted in 2007 and published in 2009 by the ] at Harvard University stated that: "We are confident that the |
* A report of research conducted in 2007 and published in 2009 by the ] at Harvard University stated that: "We are confident that the {{bracket|]}} tool developers will for the most part keep ahead of the governments' blocking efforts", but also that "...we believe that less than two percent of all filtered Internet users use circumvention tools."<ref> {{Webarchive|url=https://web.archive.org/web/20111111152457/http://cyber.law.harvard.edu/sites/cyber.law.harvard.edu/files/2007_Circumvention_Landscape.pdf |date=11 November 2011 }}, Hal Roberts, Ethan Zuckerman, and John Palfrey, Beckman Center for Internet & Society at Harvard University, March 2009</ref> | ||
| * In contrast, a 2011 report by researchers at the ] published by ] concludes "... the control of information on the Internet and Web is certainly feasible, and technological advances do not therefore guarantee greater freedom of speech."<ref name=UNESCO-2011/> | * In contrast, a 2011 report by researchers at the ] published by ] concludes "... the control of information on the Internet and Web is certainly feasible, and technological advances do not therefore guarantee greater freedom of speech."<ref name=UNESCO-2011/> | ||
| Blocking and filtering can be based on relatively static ]s or be determined more dynamically based on a real-time examination of the information being exchanged. Blacklists may be produced manually or automatically and are often not available to non-customers of the blocking software. Blocking or filtering can be done at a centralized national level, at a decentralized sub-national level, or at an institutional level, |
Blocking and filtering can be based on relatively static ]s or be determined more dynamically based on a real-time examination of the information being exchanged. Blacklists may be produced manually or automatically and are often not available to non-customers of the blocking software. Blocking or filtering can be done at a centralized national level, at a decentralized sub-national level, or at an institutional level, e.g., in libraries, universities or ]s.<ref name="NYT-20140311" /> Blocking and filtering may also vary within a country across different ISPs.<ref name=Chadwick-2009>{{Cite book| last = Chadwick| first = Andrew| title = Routledge handbook of Internet politics| publisher = Taylor and Francis| series = Routledge international handbooks| year = 2009| pages = 332 | url = https://books.google.com/books?id=GJdfuGSa1xUC| isbn = 978-0-415-42914-6}}</ref> Countries may filter sensitive content on an ongoing basis and/or introduce temporary filtering during key time periods such as elections. In some cases, the censoring authorities may surreptitiously block content to mislead the public into believing that censorship has not been applied. This is achieved by returning a fake ] error message when an attempt is made to access a blocked website.<ref name=Faris-2008/> | ||
| Unless the censor has total control over all Internet-connected computers, such as in ] (who |
Unless the censor has total control over all Internet-connected computers, such as in ] (who employs an ] that only privileged citizens can access), or ], total censorship of information is very difficult or impossible to achieve due to the underlying distributed technology of the Internet. ] and ]s (such as ]) protect ] using technologies that guarantee material cannot be removed and prevents the identification of authors. Technologically savvy users can often find ways to access blocked content. Nevertheless, blocking remains an effective means of limiting access to sensitive information for most users when censors, such as those in ], are able to devote significant resources to building and maintaining a comprehensive censorship system.<ref name=UNESCO-2011/> | ||
| The term "]" is sometimes used to describe the effects of national ]. The verb "]" colloquially refers to censorship of the Internet, particularly in Asia.<ref name="RC">{{Cite web|author=Lao Wai|title=I've Been Rivercrabbed!|work=An American |
The term "]" is sometimes used to describe the effects of national ]. The verb "]" colloquially refers to censorship of the Internet, particularly in Asia.<ref name="RC">{{Cite web |author=Lao Wai|title=I've Been Rivercrabbed! |work=An American in Beijing|date=21 October 2007 |url=http://americaninbeijing.blogspot.com/2007/10/ive-been-rivercrabbed.html|access-date=28 May 2011 |archive-date=11 August 2011|archive-url=https://web.archive.org/web/20110811103536/http://americaninbeijing.blogspot.com/2007/10/ive-been-rivercrabbed.html|url-status=live}}</ref> | ||
| == Content suppression methods == | == Content suppression methods == | ||
| Line 27: | Line 28: | ||
| ===Technical censorship=== | ===Technical censorship=== | ||
| Various parties are using different technical methods of preventing public access to undesirable resources, with varying levels of effectiveness, costs and side effects. | |||
| As per Hoffmann, different methods are used to block certain websites or pages including ], blocking access to ], analyzing and ], inspecting filter packets and resetting connections.<ref name="howto">{{cite web |last1=Hoffman |first1=Chris |title=How the "Great Firewall of China" Works to Censor China's Internet |url=https://www.howtogeek.com/162092/htg-explains-how-the-great-firewall-of-china-works/ |website=https://www.howtogeek.com |publisher=How to geek |accessdate=15 August 2018}}</ref> | |||
| ==== |
==== Blacklist ==== | ||
| Entities mandating and implementing the censorship usually identify them by one of the following items: keywords, ]s and ]es. Lists are populated from different sources, ranging from private supplier through courts to specialized government agencies (] of China, Islamic Guidance in Iran).<ref name=":0">{{Cite web |url=https://tools.ietf.org/html/draft-irtf-pearg-censorship-00.html|title=A Survey of Worldwide Censorship Techniques|last1=Jones |first1=Ben|last2=Feamster|first2=Nick |publisher=IETF|language=en |access-date=2019-09-30|last3=Hall|first3=Joseph|last4=Adams |first4=Stan|last5=Aaron|first5=Michael |date=23 August 2019 |archive-date=19 September 2020|archive-url=https://web.archive.org/web/20200919111121/https://tools.ietf.org/html/draft-irtf-pearg-censorship-00.html |url-status=live}}</ref> | |||
| Internet content is subject to technical censorship methods, including:<ref name="NYT-20140311" /><ref name=UNESCO-2011>, Dutton, March 2003</ref> | |||
| * '''Internet Protocol (IP) address blocking''': Access to a certain ] is denied. If the target Web site is hosted in a ], all websites on the same server will be blocked. This affects IP-based protocols such as ], ] and ]. A typical circumvention method is to find ] that have access to the target websites, but proxies may be jammed or blocked, and some Web sites, such as Misplaced Pages (when editing), also block proxies. Some large websites such as ] have allocated additional IP addresses to circumvent the block, but later the block was extended to cover the new addresses. Due to challenges with ], ] is normally implemented via IP address blocking. | |||
| * '''Domain name system (DNS) filtering and redirection''': Blocked ]s are not resolved, or an incorrect IP address is returned via ] or other means. This affects all IP-based protocols such as HTTP, FTP and POP. A typical circumvention method is to find an alternative ] that resolves domain names correctly, but domain name servers are subject to blockage as well, especially IP address blocking. Another workaround is to bypass DNS if the IP address is obtainable from other sources and is not itself blocked. Examples are modifying the ] or typing the IP address instead of the domain name as part of a URL given to a ]. | |||
| * '''Uniform Resource Locator (URL) filtering''': ] strings are scanned for target keywords regardless of the domain name specified in the URL. This affects the ] protocol. Typical circumvention methods are to use ] in the URL, or to use encrypted protocols such as ] and ].<ref>For an example, see ]</ref> | |||
| * '''Packet filtering''': Terminate ] ] transmissions when a certain number of controversial keywords are detected. This affects all TCP-based protocols such as HTTP, FTP and POP, but ]s are more likely to be censored. Typical circumvention methods are to use encrypted connections – such as VPN and TLS/SSL – to escape the HTML content, or by reducing the ] ]'s ]/] to reduce the amount of text contained in a given packet. | |||
| * '''Connection reset''': If a previous ] connection is blocked by the filter, future connection attempts from both sides can also be blocked for some variable amount of time. Depending on the location of the block, other users or websites may also be blocked, if the communication is ] through the blocking location. A circumvention method is to ignore the reset packet sent by the firewall.<ref>{{cite web|url=http://www.zdnetasia.com/news/security/0,39044215,39372326,00.htm|title=Topics - ZDNet|work=ZDNet|accessdate=5 April 2015}}</ref> | |||
| * '''Network disconnection''': A technically simpler method of Internet censorship is to completely cut off all routers, either by software or by hardware (turning off machines, pulling out cables). A circumvention method could be to use a satellite ISP to access Internet.<ref>{{Cite news|url=https://www.wired.com/2016/04/ingenious-way-iranians-using-satellite-tv-beam-banned-data/|title=The Ingenious Way Iranians Are Using Satellite TV to Beam in Banned Internet|last=Greenberg|first=Andy|work=WIRED|access-date=2018-01-25|language=en-US}}</ref> | |||
| * '''Portal censorship''' and '''search result removal''': Major portals, including ]s, may exclude web sites that they would ordinarily include. This renders a site invisible to people who do not know where to find it. When a major portal does this, it has a similar effect as censorship. Sometimes this exclusion is done to satisfy a legal or other requirement, other times it is purely at the discretion of the portal. For example, Google.de and Google.fr remove ] and other listings in compliance with German and French law.<ref>, Declan McCullagh, CNET News, 23 October 2002, 8:55 pm PDT. Retrieved 22 April 2007 00:40 UTC</ref> | |||
| * '''Computer network attacks''': ]s and attacks that deface opposition websites can produce the same result as other blocking techniques, preventing or limiting access to certain websites or other online services, although only for a limited period of time. This technique might be used during the lead up to an election or some other sensitive period. It is more frequently used by non-state actors seeking to disrupt services.<ref>, Helmi Noman, OpenNet Initiative, May 2011</ref> | |||
| As per Hoffmann, different methods are used to block certain websites or pages including ], blocking access to ], analyzing and ], inspecting filter packets and resetting connections.<ref name="howto">{{cite web |last1=Hoffman |first1=Chris |title=How the "Great Firewall of China" Works to Censor China's Internet |url=https://www.howtogeek.com/162092/htg-explains-how-the-great-firewall-of-china-works/ |website=www.howtogeek.com |date=22 September 2016 |publisher=How to geek |access-date=15 August 2018 |archive-date=15 August 2018 |archive-url=https://web.archive.org/web/20180815131540/https://www.howtogeek.com/162092/htg-explains-how-the-great-firewall-of-china-works/ |url-status=live }}</ref> | |||
| {{See also |Internet forum#Word censor|Anti-spam techniques#Detecting spam}} | |||
| ==== Points of control ==== | |||
| Enforcement of the censor-nominated technologies can be applied at various levels of countries and Internet infrastructure:<ref name=":0" /> | |||
| * ], including ] with international networks (]), operators of ]s, ] points, international ] etc. In addition to facing huge performance challenges due to large bandwidths involved, these do not give censors access to information exchanged within the country. | |||
| * ], which involves installation of voluntary (such as in the ]) or mandatory (such as in ]) Internet surveillance and blocking equipment. | |||
| * Individual institutions, which in most cases implement some form of Internet access controls to enforce their own policies, but, especially in case of public or educational institutions, may be requested or coerced to do this on the request from the government. | |||
| * Personal devices, whose manufacturers or vendors may be required by law to install censorship software. | |||
| * Application service providers (e.g. social media companies), who may be legally required to remove particular content. Foreign providers with business presence in given country may be also coerced into restricting access to specific contents for visitors from the requesting country. | |||
| * ] may be required to issue counterfeit ] certificates controlled by the government, allowing ] surveillance of ] encrypted connections. | |||
| * ] providers who tend to aggregate large amounts of content (e.g. images) may be also an attractive target for censorship authorities. | |||
| ====Approaches==== | |||
| Internet content is subject to technical censorship methods, including:<ref name="NYT-20140311" /><ref name=UNESCO-2011> {{Webarchive|url=https://web.archive.org/web/20110928033105/http://www.unesco.org/new/en/communication-and-information/resources/publications-and-communication-materials/publications/full-list/freedom-of-connection-freedom-of-expression-the-changing-legal-and-regulatory-ecology-shaping-the-internet/ |date=28 September 2011 }}, Dutton, March 2003</ref> | |||
| * '''Internet Protocol (IP) address blocking''': Access to a certain ] is denied. If the target Web site is hosted in a ], all websites on the same server will be blocked. This affects IP-based protocols such as ], ] and ]. A typical circumvention method is to find ] that have access to the target websites, but proxies may be jammed or blocked, and some Web sites, such as Misplaced Pages (when editing), also block proxies. Some large websites such as ] have allocated additional IP addresses to circumvent the block, but later the block was extended to cover the new addresses{{Citation needed|date=April 2022|reason=Who extended the block? When is later? How do I know that happened?}}. Due to challenges with ], ] is normally implemented via IP address blocking. | |||
| * '''Domain name system (DNS) filtering and redirection''': Connections to blocked ]s are not resolved, or an incorrect IP address is returned via ] or other means. This affects all IP-based protocols such as HTTP, FTP and POP. A typical circumvention method is to find an alternative ] that resolves domain names correctly, but domain name servers are subject to blockage as well, especially IP address blocking. Another workaround is to bypass DNS if the IP address is obtainable from other sources and is not itself blocked. Examples are modifying the ] or typing the IP address instead of the domain name as part of a URL given to a ]. | |||
| * '''Uniform Resource Locator (URL) filtering''': ] strings are scanned for target keywords regardless of the domain name specified in the URL. This affects the ] protocol. Typical circumvention methods are to use ] in the URL, or to use encrypted protocols such as ] and ].<ref>For an example, see ]</ref> | |||
| * '''Packet filtering''': Terminate ] ] transmissions when a certain number of controversial keywords are detected. This affects all TCP-based protocols such as HTTP, FTP and POP, but ]s are more likely to be censored. Typical circumvention methods are to use encrypted connections – such as VPN and TLS/SSL – to escape the HTML content, or by reducing the ] ]'s ]/] to reduce the amount of text contained in a given packet. | |||
| * '''Connection reset''': If a previous ] connection is blocked by the filter, future connection attempts from both sides can also be blocked for some variable amount of time. Depending on the location of the block, other users or websites may also be blocked, if the communication is ] through the blocking location. A circumvention method is to ignore the reset packet sent by the firewall.<ref>{{cite web|author=Tom Espiner|date=July 4, 2006 |url=http://www.zdnetasia.com/news/security/0,39044215,39372326,00.htm|title=Academics break the Great Firewall of China|access-date=5 April 2015 |archive-date=8 October 2009 |archive-url=https://web.archive.org/web/20091008214629/http://www.zdnetasia.com/news/security/0,39044215,39372326,00.htm|url-status=dead|work=ZDNet}}</ref> | |||
| * '''Network disconnection''': A technically simpler method of Internet censorship is to completely cut off all routers, either by software or by hardware (turning off machines, pulling out cables). A circumvention method could be to use a satellite ISP to access Internet.<ref>{{Cite magazine |url=https://www.wired.com/2016/04/ingenious-way-iranians-using-satellite-tv-beam-banned-data/ |title=The Ingenious Way Iranians Are Using Satellite TV to Beam in Banned Internet |last=Greenberg |first=Andy |magazine=WIRED |access-date=2018-01-25 |language=en-US |archive-date=8 November 2020 |archive-url=https://web.archive.org/web/20201108132433/http://www.wired.com/2016/04/ingenious-way-iranians-using-satellite-tv-beam-banned-data/ |url-status=live}}</ref> | |||
| * '''Portal censorship''' and '''search result removal''': Major portals, including ]s, may exclude web sites that they would ordinarily include. This renders a site invisible to people who do not know where to find it. When a major portal does this, it has a similar effect to censorship. Sometimes this exclusion is done to satisfy a legal or other requirement, other times it is purely at the discretion of the portal. For example, Google.de and Google.fr remove ] and other listings in compliance with German and French law.<ref> {{Webarchive|url=https://web.archive.org/web/20201123064639/http://www.cnet.com/news/google-excluding-controversial-sites/ |date=23 November 2020 }}, Declan McCullagh, CNET News, 23 October 2002, 8:55 pm PDT. Retrieved 22 April 2007 00:40 UTC</ref> | |||
| * '''Computer network attacks''': ]s and attacks that deface opposition websites can produce the same result as other blocking techniques, preventing or limiting access to certain websites or other online services, although only for a limited period of time. This technique might be used during the lead up to an election or some other sensitive period. It is more frequently used by non-state actors seeking to disrupt services.<ref> {{Webarchive |url=https://web.archive.org/web/20200514223923/http://opennet.net/emergence-open-and-organized-pro-government-cyber-attacks-middle-east-case-syrian-electronic-army |date=14 May 2020 }}, Helmi Noman, OpenNet Initiative, May 2011</ref> | |||
| {{See also|Internet censorship circumvention|Internet forum#Word censor|Anti-spam techniques#Detecting spam}} | |||
| ====Over and under blocking==== | ====Over and under blocking==== | ||
| Technical censorship techniques are subject to both over- and under-blocking since it is often impossible to always block exactly the targeted content without blocking other permissible material or allowing some access to targeted material and so providing more or less protection than desired.<ref name=UNESCO-2011/> An example is blocking an IP-address of a server that hosts multiple websites, which prevents access to all of the websites rather than just those that contain content deemed offensive.<ref>, Andrew Orlowski, The Register, 24 September 2003</ref> | Technical censorship techniques are subject to both over- and under-blocking since it is often impossible to always block exactly the targeted content without blocking other permissible material or allowing some access to targeted material and so providing more or less protection than desired.<ref name=UNESCO-2011/> An example is blocking an IP-address of a server that hosts multiple websites, which prevents access to all of the websites rather than just those that contain content deemed offensive.<ref> {{Webarchive|url=https://web.archive.org/web/20180917002008/https://www.theregister.co.uk/2003/09/24/india_blocks_yahoo_groups/ |date=17 September 2018 }}, Andrew Orlowski, The Register, 24 September 2003</ref> | ||
| ==== Use of commercial filtering software ==== | ==== Use of commercial filtering software ==== | ||
| ] blocking Facebook in an |
] blocking Facebook in an organization where it has been configured to block a category named "Personals and Dating"]] | ||
| {{Main |Content-control software}} | {{Main |Content-control software}} | ||
| Writing in 2009 ], professor of political science at the ] and co-founder and one of the principal investigators of the ], and, writing in 2011, Evgeny Morzov, a visiting scholar at ] and an |
Writing in 2009, ], professor of political science at the ] and co-founder and one of the principal investigators of the ], and, writing in 2011, Evgeny Morzov, a visiting scholar at ] and an op-ed contributor to '']'', explain that companies in the United States, Finland, France, Germany, Britain, Canada, and South Africa are in part responsible for the increasing sophistication of online content filtering worldwide. While the off-the-shelf ] sold by Internet security companies are primarily marketed to businesses and individuals seeking to protect themselves and their employees and families, they are also used by governments to block what they consider sensitive content.<ref name=Chadwick2009-1>{{Cite book| last = Chadwick| first = Andrew| title = Routledge handbook of Internet politics| publisher = Taylor and Francis| series = Routledge international handbooks| year = 2009| pages = 330–331 | url = https://books.google.com/books?id=GJdfuGSa1xUC| isbn = 978-0-415-42914-6}}</ref><ref> {{Webarchive|url=https://web.archive.org/web/20201112021347/https://www.nytimes.com/2011/09/02/opinion/political-repression-2-0.html |date=12 November 2020 }}, Evgeny Morzov, Op-Ed Contributor to the ''New York Times'', 1 September 2011</ref> | ||
| Among the most popular filtering software programs is ] by ] in California, which was bought by ] in 2008. SmartFilter has been used by ], Saudi Arabia, ], the ], Kuwait, ], Iran, and ], as well as the United States and the UK.<ref name="guardian.co.uk">{{cite news |url=https://www.theguardian.com/commentisfree/2008/nov/17/censorship-internet |title=The big business of net censorship |last=Glanville |first=Jo |date=17 November 2008 |work=The Guardian | |
Among the most popular filtering software programs is ] by ] in California, which was bought by ] in 2008. SmartFilter has been used by ], Saudi Arabia, ], the ], Kuwait, ], Iran, and ], as well as the United States and the UK.<ref name="guardian.co.uk">{{cite news |url=https://www.theguardian.com/commentisfree/2008/nov/17/censorship-internet |title=The big business of net censorship |last=Glanville |first=Jo |date=17 November 2008 |work=The Guardian |location=London |access-date=11 December 2016 |archive-date=28 January 2013 |archive-url=https://web.archive.org/web/20130128195629/http://www.guardian.co.uk/commentisfree/2008/nov/17/censorship-internet |url-status=live }}</ref> ] and ] have used filtering software from ]. The ] commercial filter Netsweeper<ref> {{Webarchive|url=https://web.archive.org/web/20131217224810/http://www.netsweeper.com/index.php?page=netsw_prod_content_filtering |date=17 December 2013 }}, Netsweeper, Inc. web site. Retrieved 1 September 2011</ref> is used in ], the ], and ].<ref name=Noman-2011> {{Webarchive|url=https://web.archive.org/web/20180918231144/http://opennet.net/west-censoring-east-the-use-western-technologies-middle-east-censors-2010-2011 |date=18 September 2018 }}, Helmi Noman and Jillian C. York, OpenNet Initiative, March 2011</ref> The Canadian organization CitizenLab has reported that ] and ] products are used in Turkey and Egypt.<ref>{{Cite news|url=https://citizenlab.ca/2018/03/bad-traffic-sandvines-packetlogic-devices-deploy-government-spyware-turkey-syria/|title=BAD TRAFFIC: Sandvine's PacketLogic Devices Used to Deploy Government Spyware in Turkey and Redirect Egyptian Users to Affiliate Ads?|date=2018-03-09|work=The Citizen Lab|access-date=2018-05-10|language=en-US|archive-date=10 December 2020|archive-url=https://web.archive.org/web/20201210231719/https://citizenlab.ca/2018/03/bad-traffic-sandvines-packetlogic-devices-deploy-government-spyware-turkey-syria/|url-status=live}}</ref> | ||
| On 12 March 2013 in a ''Special |
On 12 March 2013, in a ''Special Report on Internet Surveillance'', Reporters Without Borders named five "Corporate Enemies of the Internet": ] (France), ] (U.S.), ] (UK and Germany), ] (Italy), and Trovicor (Germany). The companies sell products that are liable to be used by governments to violate human rights and freedom of information. RWB said that the list is not exhaustive and will be expanded in the coming months.<ref name="RSFSRS-March2013"/> | ||
| In a U.S. lawsuit filed in May 2011, ] is accused of helping the ] build a firewall, known widely as the ], to censor the Internet and keep tabs on dissidents. Cisco said it had made nothing special for China. Cisco is also accused of aiding the Chinese government in monitoring and apprehending members of the banned ] group.<ref> |
In a U.S. lawsuit filed in May 2011, ] is accused of helping the ] build a firewall, known widely as the ], to censor the Internet and keep tabs on dissidents.<ref>{{Cite web |url=https://www.socialstudies.org/publications/socialeducation/april2007/the-great-firewall-of-china |title=The Great Firewall of China|date=2016-05-27|website=National Council for the Social Studies |language=en|access-date=2020-03-29|archive-date=29 March 2020|archive-url=https://web.archive.org/web/20200329012734/https://www.socialstudies.org/publications/socialeducation/april2007/the-great-firewall-of-china|url-status=live}}</ref> Cisco said it had made nothing special for China. Cisco is also accused of aiding the Chinese government in monitoring and apprehending members of the banned ] group.<ref>{{cite web |url=https://www.nytimes.com/2011/09/03/technology/group-says-it-has-new-evidence-of-ciscos-misdeeds-in-china.html |title=Group Says It Has New Evidence of Cisco's Misdeeds in China |archive-date=12 November 2020 |archive-url=https://web.archive.org/web/20201112041653/https://www.nytimes.com/2011/09/03/technology/group-says-it-has-new-evidence-of-ciscos-misdeeds-in-china.html |author=Somini Sengupta |work=The New York Times |date=2 September 2011}}</ref> | ||
| Many filtering programs allow blocking to be configured based on dozens of categories and sub-categories such as these from Websense: "abortion" (pro-life, pro-choice), "adult material" (adult content, lingerie and swimsuit, nudity, sex, sex education), "advocacy groups" (sites that promote change or reform in public policy, public opinion, social practice, economic activities, and relationships), "drugs" (abused drugs, marijuana, prescribed medications, supplements and unregulated compounds), "religion" (non-traditional religions occult and folklore, traditional religions), ....<ref name=Noman-2011/> The blocking categories used by the filtering programs may contain errors leading to the unintended blocking of websites.<ref name=Chadwick2009-1/> The blocking of ] in early 2007 by Tunisian authorities was, according to the ], due to Secure Computing wrongly categorizing Dailymotion as pornography for its SmartFilter filtering software. It was initially thought that Tunisia had blocked Dailymotion due to satirical videos about human rights violations in Tunisia, but after Secure Computing corrected the mistake access to Dailymotion was gradually restored in Tunisia.<ref>{{Cite book| last = |
Many filtering programs allow blocking to be configured based on dozens of categories and sub-categories such as these from Websense: "abortion" (pro-life, pro-choice), "adult material" (adult content, lingerie and swimsuit, nudity, sex, sex education), "advocacy groups" (sites that promote change or reform in public policy, public opinion, social practice, economic activities, and relationships), "drugs" (abused drugs, marijuana, prescribed medications, supplements and unregulated compounds), "religion" (non-traditional religions occult and folklore, traditional religions), ....<ref name=Noman-2011/> The blocking categories used by the filtering programs may contain errors leading to the unintended blocking of websites.<ref name=Chadwick2009-1/> The blocking of ] in early 2007 by Tunisian authorities was, according to the ], due to Secure Computing wrongly categorizing Dailymotion as pornography for its SmartFilter filtering software. It was initially thought that Tunisia had blocked Dailymotion due to satirical videos about human rights violations in Tunisia, but after Secure Computing corrected the mistake access to Dailymotion was gradually restored in Tunisia.<ref>{{Cite book| last = Chadwick| first = Andrew| title = Routledge handbook of Internet politics| publisher = Taylor and Francis| series = Routledge international handbooks| year = 2009| pages = 323–324 | url = https://books.google.com/books?id=GJdfuGSa1xUC| isbn = 978-0-415-42914-6}}</ref> | ||
| Organizations such as the ], the ], ], and the ] have successfully lobbied some vendors such as ] to make changes to their software, to refrain from doing business with repressive governments, and to educate schools who have inadvertently reconfigured their filtering software too strictly.<ref name="riaclu">{{cite |
Organizations such as the ], the ], ], and the ] have successfully lobbied some vendors such as ] to make changes to their software, to refrain from doing business with repressive governments, and to educate schools who have inadvertently reconfigured their filtering software too strictly.<ref name="riaclu">{{cite press release |publisher=ACLU |url=http://www.riaclu.org/20050418.html |archive-url=https://web.archive.org/web/20081205070114/http://www.riaclu.org/20050418.html |title=R.I. ACLU releases report on "troubling" internet censorship in public libraries |date=18 April 2005 |archive-date=5 December 2008}} {{cite report |author=((The Rhode Island affiliate, American Civil Liberties Union)) |date=April 2005 |title=Reader's block: Internet censorship in Rhode Island public libraries |url=http://www.riaclu.org/friendly/documents/2005libraryinternetreport.pdf |archive-url= https://web.archive.org/web/20050906002316/http://www.riaclu.org/friendly/documents/2005libraryinternetreport.pdf |archive-date=2005-09-06 |url-status=dead}}</ref><ref>{{cite web |url=https://www.eff.org/deeplinks/2011/11/week-internet-censorship%20|access-date=27 March 2012 |publisher=] |date=7 November 2011|title=This Week in Internet Censorship Egypt Imprisons Alaa, Other Pro-democracy Bloggers |first1=Maira |last1=Sutton|first2=Trevor|last2=Timm |archive-url=https://web.archive.org/web/20200812105306/https://www.eff.org/deeplinks/2011/11/week-internet-censorship%20|archive-date=12 August 2020|url-status=live}}</ref><ref name="amnesty china"> {{Webarchive |url=https://web.archive.org/web/20200925141537/https://www.amnesty.org/en/documents/asa17/001/2004/en/ |date=25 September 2020 }} "], ], ], Websense and ]", citing Amnesty International: People's Republic of China: State Control of the Internet in China, ASA, 17/007/2002, November 2002.</ref> Nevertheless, regulations and accountability related to the use of commercial filters and services are often non-existent, and there is relatively little oversight from civil society or other independent groups. Vendors often consider information about what sites and content is blocked valuable intellectual property that is not made available outside the company, sometimes not even to the organizations purchasing the filters. Thus by relying upon out-of-the-box filtering systems, the detailed task of deciding what is or is not acceptable speech may be outsourced to the commercial vendors.<ref name=Noman-2011/> | ||
| ===Non-technical censorship=== | ===Non-technical censorship=== | ||
| {{Main |Censorship}} | {{Main |Censorship}} | ||
| ] | |||
| Internet content is also subject to censorship methods similar to those used with more traditional media. For example:<ref name=UNESCO-2011/> | Internet content is also subject to censorship methods similar to those used with more traditional media. For example:<ref name=UNESCO-2011/> | ||
| Line 70: | Line 87: | ||
| * Publishers, authors, and ISPs may be subject to arrest, criminal prosecution, fines, and imprisonment. | * Publishers, authors, and ISPs may be subject to arrest, criminal prosecution, fines, and imprisonment. | ||
| * Publishers, authors, and ISPs may be subject to ]s. | * Publishers, authors, and ISPs may be subject to ]s. | ||
| * Equipment may be ] and/or destroyed. | * Equipment may be ] and/or destroyed. | ||
| * Publishers and ISPs may be closed or required licenses may be withheld or revoked. | * Publishers and ISPs may be closed or required licenses may be withheld or revoked. | ||
| * Publishers, authors, and ISPs may be subject to ]s. | * Publishers, authors, and ISPs may be subject to ]s. | ||
| * Publishers, authors, and their families may be subject to threats, attacks, beatings, and even murder.<ref> {{webarchive|url=https:// |
* Publishers, authors, and their families may be subject to threats, attacks, beatings, and even murder.<ref> {{webarchive|url=https://web.archive.org/web/20121011003850/http://thelede.blogs.nytimes.com/2011/09/15/in-mexico-social-media-becomes-a-battleground-in-the-drug-war/ |date=11 October 2012 }}, J. David Goodman, ''The Lede, The New York Times'', 15 September 2011</ref> | ||
| * Publishers, authors, and their families may be threatened with or actually lose their jobs. | * Publishers, authors, and their families may be threatened with or actually lose their jobs. | ||
| * Individuals may be paid to write articles and comments in support of particular positions or attacking opposition positions, usually without acknowledging the payments to readers and viewers.<ref name=InLineAsLongAs>Provision of information in this fashion is in keeping with principles of freedom of expression, as long as it is done transparently and does not overwhelm alternative sources of information.</ref><ref> {{webarchive|url=https://web.archive.org/web/20111013195601/http://blog.freedomhouse.org/weblog/2011/10/chinas-growing-army-of-paid-internet-commentators.html |date=13 October 2011 }}, Sarah Cook and Maggie Shum, Freedom House, 11 October 2011</ref> | * Individuals may be paid to write articles and comments in support of particular positions or attacking opposition positions, usually without acknowledging the payments to readers and viewers.<ref name=InLineAsLongAs>Provision of information in this fashion is in keeping with principles of freedom of expression, as long as it is done transparently and does not overwhelm alternative sources of information.</ref><ref> {{webarchive|url=https://web.archive.org/web/20111013195601/http://blog.freedomhouse.org/weblog/2011/10/chinas-growing-army-of-paid-internet-commentators.html |date=13 October 2011 }}, Sarah Cook and Maggie Shum, Freedom House, 11 October 2011</ref> | ||
| * Censors may create their own online publications and Web sites to guide online opinion.<ref name=InLineAsLongAs/> | * Censors may create their own online publications and Web sites to guide online opinion.<ref name=InLineAsLongAs/> | ||
| * Access to the Internet may be limited due to restrictive licensing policies or high costs. | * Access to the Internet may be limited due to restrictive licensing policies or high costs. | ||
| * Access to the Internet may be limited due to a lack of the necessary infrastructure, deliberate or not. | * Access to the Internet may be limited due to a lack of the necessary infrastructure, deliberate or not. | ||
| * Access to search results may be restricted due to government involvement in the censorship of specific search terms, content may be excluded due to terms set with search engines. By allowing search engines to operate in new territory they must agree to abide to censorship standards set by the government in that country.<ref>{{Cite web|url=http://link.galegroup.com/apps/doc/EJ3010901220/OVIC?sid=OVIC&xid=c9f2fc86|title=Google Ends Internet Censorship, Dares China to Make Next Move|last=Farrell|first=Michael B|date=22 March 2010|website=link.galegroup.com|publisher=Christian Science Monitor|language=en|access-date=2018-11-15}}</ref> | * Access to search results may be restricted due to government involvement in the censorship of specific search terms, content may be excluded due to terms set with search engines. By allowing search engines to operate in new territory they must agree to abide to censorship standards set by the government in that country.<ref>{{Cite web |url=http://link.galegroup.com/apps/doc/EJ3010901220/OVIC?sid=OVIC&xid=c9f2fc86 |title=Google Ends Internet Censorship, Dares China to Make Next Move |last=Farrell |first=Michael B |date=22 March 2010 |website=link.galegroup.com |publisher=The Christian Science Monitor |language=en |access-date=2018-11-15 |archive-date=17 January 2023 |archive-url=https://web.archive.org/web/20230117054812/https://go.gale.com/ps/i.do?p=OVIC&u=nm_p_oweb&id=GALE%7CEJ3010901220&v=2.1&it=r&sid=OVIC&asid=c9f2fc86 |url-status=live}}</ref> | ||
| === |
===Censorship of users by web service operators=== | ||
| ====Removal of user accounts based on controversial content==== | ====Removal of user accounts based on controversial content==== | ||
| {{Main|Deplatforming}} | {{Main|Deplatforming}} | ||
| ] is a form of Internet censorship in which controversial speakers or speech are suspended, banned, or otherwise shut down by ] platforms and other service providers that generally provide a venue for free speech or expression.<ref name=Reynolds/> Banking and financial service providers, among other companies, have also denied services to controversial activists or organizations, a practice known as "]". | ] is a form of Internet censorship in which controversial speakers or speech are suspended, banned, or otherwise shut down by ] platforms and other service providers that generally provide a venue for free speech or expression.<ref name=Reynolds/> Banking and financial service providers, among other companies, have also denied services to controversial activists or organizations, a practice known as "]". | ||
| Law professor ] dubbed 2018 the "Year of Deplatforming", in an August 2018 article in '']''.<ref name=Reynolds/> According to Reynolds, in 2018 "the internet giants decided to slam the gates on a number of people and ideas they don't like |
Law professor ] dubbed 2018 the "Year of Deplatforming", in an August 2018 article in '']''.<ref name=Reynolds/> According to Reynolds, in 2018 "the internet giants decided to slam the gates on a number of people and ideas they don't like."<ref name=Reynolds>{{cite news |title=When Digital Platforms Become Censors |first=Glenn Harlan |last=Reynolds |date=18 August 2018 |newspaper=The Wall Street Journal |url=https://www.wsj.com/articles/when-digital-platforms-become-censors-1534514122?mod=rsswn |url-status=live |archive-url=https://web.archive.org/web/20190330045941/https://www.wsj.com/articles/when-digital-platforms-become-censors-1534514122?mod=rsswn |archive-date=2019-03-30 }}</ref> On 6 August 2018, for example, several major platforms, including ] and ], executed a coordinated, permanent ban on all accounts and media associated with conservative talk show host ] and his media platform ], citing "]" and "glorifying violence."<ref name=NPR>{{cite news |first1=Bill |last1=Chappell |first2=Anastasia |last2=Tsioulcas |website=NPR |title=YouTube, Apple and Facebook Ban Infowars, Which Decries 'Mega Purge' |date=6 August 2018 |url=https://www.npr.org/2018/08/06/636030043/youtube-apple-and-facebook-ban-infowars-which-decries-mega-purge |access-date=2 September 2018 |archive-date=3 May 2019 |archive-url=https://web.archive.org/web/20190503221538/https://www.npr.org/2018/08/06/636030043/youtube-apple-and-facebook-ban-infowars-which-decries-mega-purge |url-status=live }}</ref> | ||
| ====Official statements regarding site and content removal==== | ====Official statements regarding site and content removal==== | ||
| {{See also|Twitter suspensions|Terms of |
{{See also|Twitter suspensions|Terms of service}} | ||
| Most major web service operators reserve to themselves broad rights to remove or pre-screen content, and to suspend or terminate user accounts, sometimes without giving a specific list or only a vague general list of the reasons allowing the removal. The phrases "at our sole discretion", "without prior notice", and "for other reasons" are common in ] agreements. | Most major web service operators reserve to themselves broad rights to remove or pre-screen content, and to suspend or terminate user accounts, sometimes without giving a specific list or only a vague general list of the reasons allowing the removal. The phrases "at our sole discretion", "without prior notice", and "for other reasons" are common in ] agreements. | ||
| * ]: Among other things, the Facebook Statement of Rights and Responsibilities says: "You will not post content that: is hateful, threatening, or pornographic; incites violence; or contains nudity or graphic or gratuitous violence", "You will not use Facebook to do anything unlawful, misleading, malicious, or discriminatory", "We can remove any content or information you post on Facebook if we believe that it violates this Statement", and "If you are located in a country embargoed by the United States, or are on the U.S. Treasury Department's list of Specially Designated Nationals you will not engage in commercial activities on Facebook (such as advertising or payments) or operate a Platform application or website".<ref>, Facebook, 26 April 2011. Retrieved 18 August 2011</ref> | * ]: Among other things, the Facebook Statement of Rights and Responsibilities says: "You will not post content that: is hateful, threatening, or pornographic; incites violence; or contains nudity or graphic or gratuitous violence", "You will not use Facebook to do anything unlawful, misleading, malicious, or discriminatory", "We can remove any content or information you post on Facebook if we believe that it violates this Statement", and "If you are located in a country embargoed by the United States, or are on the U.S. Treasury Department's list of Specially Designated Nationals you will not engage in commercial activities on Facebook (such as advertising or payments) or operate a Platform application or website".<ref> {{Webarchive|url=https://web.archive.org/web/20181226015301/https://www.facebook.com/legal/terms |date=26 December 2018 }}, Facebook, 26 April 2011. Retrieved 18 August 2011</ref> | ||
| * ]: Google's general Terms of Service, which were updated on 1 March 2012, state: "We may suspend or stop providing our Services to you if you do not comply with our terms or policies or if we are investigating suspected misconduct", "We may review content to determine whether it is illegal or violates our policies, and we may remove or refuse to display content that we reasonably believe violates our policies or the law", and "We respond to notices of alleged copyright infringement and terminate accounts of repeat infringers according to the process set out in the U.S. ]".<ref>, Policies & Principles, Google, Inc.. Retrieved 1 April 2012</ref> | * ]: Google's general Terms of Service, which were updated on 1 March 2012, state: "We may suspend or stop providing our Services to you if you do not comply with our terms or policies or if we are investigating suspected misconduct", "We may review content to determine whether it is illegal or violates our policies, and we may remove or refuse to display content that we reasonably believe violates our policies or the law", and "We respond to notices of alleged copyright infringement and terminate accounts of repeat infringers according to the process set out in the U.S. ]".<ref> {{Webarchive|url=https://web.archive.org/web/20201215063934/http://www.google.com/intl/en/policies/terms/ |date=15 December 2020 }}, Policies & Principles, Google, Inc.. Retrieved 1 April 2012</ref> | ||
| ** ]: Google's Webmaster Tools help includes the following statement: "Google may temporarily or permanently remove sites from its index and search results if it believes it is obligated to do so by law, if the sites do not meet Google's quality guidelines, or for other reasons, such as if the sites detract from users' ability to locate relevant information."<ref>, Google Webmaster Tools Help. Retrieved 22 April 2007 00:43 UTC</ref> | ** ]: Google's Webmaster Tools help includes the following statement: "Google may temporarily or permanently remove sites from its index and search results if it believes it is obligated to do so by law, if the sites do not meet Google's quality guidelines, or for other reasons, such as if the sites detract from users' ability to locate relevant information."<ref> {{Webarchive|url=https://web.archive.org/web/20070506171954/http://www.google.com/support/webmasters/bin/answer.py?answer=40052 |date=6 May 2007 }}, Google Webmaster Tools Help. Retrieved 22 April 2007 00:43 UTC</ref> | ||
| * ]: The Twitter Terms of Service state: "We reserve the right at all times (but will not have an obligation) to remove or refuse to distribute any Content on the Services and to terminate users or reclaim usernames" and "We reserve the right to remove Content alleged to be |
* ]: The Twitter Terms of Service state: "We reserve the right at all times (but will not have an obligation) to remove or refuse to distribute any Content on the Services and to terminate users or reclaim usernames" and "We reserve the right to remove Content alleged to be copyright infringing without prior notice and at our sole discretion".<ref> {{Webarchive|url=https://web.archive.org/web/20201215170628/https://twitter.com/Tos |date=15 December 2020 }}, Twitter, 1 June 2011. Retrieved 18 August 2011</ref> | ||
| * ]: The YouTube Terms of Service include the statements: "YouTube reserves the right to decide whether Content violates these Terms of Service for reasons other than copyright infringement, such as, but not limited to, pornography, obscenity, or excessive length. YouTube may at any time, without prior notice and in its sole discretion, remove such Content and/or terminate a user's account for submitting such material in violation of these Terms of Service", "YouTube will remove all Content if properly notified that such Content infringes on another's intellectual property rights", and "YouTube reserves the right to remove Content without prior notice".<ref>, YouTube, 9 June 2010. Retrieved 18 August 2011</ref> | * ]: The YouTube Terms of Service include the statements: "YouTube reserves the right to decide whether Content violates these Terms of Service for reasons other than copyright infringement, such as, but not limited to, pornography, obscenity, or excessive length. YouTube may at any time, without prior notice and in its sole discretion, remove such Content and/or terminate a user's account for submitting such material in violation of these Terms of Service", "YouTube will remove all Content if properly notified that such Content infringes on another's intellectual property rights", and "YouTube reserves the right to remove Content without prior notice".<ref> {{Webarchive|url=https://web.archive.org/web/20161226062628/https://www.youtube.com/static?gl=US&template=terms |date=26 December 2016 }}, YouTube, 9 June 2010. Retrieved 18 August 2011</ref> | ||
| * ]<span class="anchor" id="Misplaced Pages"></span>: The site's content may be modified or ] by any editor as part of the normal process of editing and updating articles. Misplaced Pages's deletion policy outlines the circumstances in which entire articles can be deleted. Any editor who believes a page doesn't belong in the encyclopedia can propose its deletion. Such a page can be deleted by any ] if, after seven days, no one objects to the ]. ] allows for outright deletion of articles that are so clearly in violation of rules of the website that they do not need to undergo a ]. All deletion decisions may be ], either informally or formally. An additional means of hiding specific content within Misplaced Pages articles is revision deletion, or RevDel, by which an administrator can perform ] of specific revisions of an article, thereby hiding certain information from the view of non-administrators.<ref>{{cite book | first1=Andrew Granville | last1=West | first2=Insup | last2=Lee | chapter=What Misplaced Pages deletes: Characterizing dangerous collaborative content | chapter-url= https://www.researchgate.net/publication/221367712 | title=Proceedings of the 7th International Symposium on Wikis and Open Collaboration | date=October 2011 | pages=25–28 | doi= 10.1145/2038558.2038563| isbn=978-1-4503-0909-7 | s2cid=10396423 }}</ref><ref name="Jemielniak">{{cite book | last=Jemielniak | first=Dariusz | title=Common Knowledge?: An Ethnography of Misplaced Pages | year=2014 | publisher=Stanford University Press}}</ref>{{rp|216}} | |||
| {{anchor|Misplaced Pages}} | |||
| * ]: Yahoo!'s Terms of Service (TOS) state: "You acknowledge that Yahoo! may or may not pre-screen Content, but that Yahoo! and its designees shall have the right (but not the obligation) in their sole discretion to pre-screen, refuse, or remove any Content that is available via the Yahoo! Services. Without limiting the foregoing, Yahoo! and its designees shall have the right to remove any Content that violates the TOS or is otherwise objectionable."<ref> {{Webarchive|url=https://web.archive.org/web/20140718103831/https://info.yahoo.com/legal/us/yahoo/utos/utos-173.html |date=18 July 2014 }}, Yahoo!, 24 November 2008. Retrieved 18 August 2011</ref> | |||
| * ]: Content within a Misplaced Pages article may be modified or deleted by any editor as part of the normal process of editing and updating articles. All editing decisions are open to discussion and review. The Misplaced Pages Deletion policy outlines the circumstances in which entire articles can be deleted. Any editor who believes a page doesn't belong in an encyclopedia can propose its deletion. Such a page can be deleted by any administrator if, after seven days, no one objects to the proposed deletion. Speedy deletion allows for the deletion of articles without discussion and is used to remove pages that are so obviously inappropriate for Misplaced Pages that they have no chance of surviving a deletion discussion. All deletion decisions may be reviewed, either informally or formally.<ref>], Misplaced Pages. Retrieved 18 August 2011</ref> | |||
| * ]: Yahoo!'s Terms of Service (TOS) state: "You acknowledge that Yahoo! may or may not pre-screen Content, but that Yahoo! and its designees shall have the right (but not the obligation) in their sole discretion to pre-screen, refuse, or remove any Content that is available via the Yahoo! Services. Without limiting the foregoing, Yahoo! and its designees shall have the right to remove any Content that violates the TOS or is otherwise objectionable."<ref>, Yahoo!, 24 November 2008. Retrieved 18 August 2011</ref> | |||
| ==Circumvention== | ==Circumvention== | ||
| {{Main|Internet censorship circumvention}} | {{Main|Internet censorship circumvention}} | ||
| Internet censorship circumvention is the processes used by technologically savvy Internet users to bypass the technical aspects of Internet filtering and gain access to the otherwise censored material. Circumvention is an inherent problem for those wishing to censor the Internet because filtering and blocking do not remove content from the Internet, but instead block access to it. Therefore, as long as there is at least one publicly accessible uncensored system, it will often be possible to gain access to the otherwise censored material. However circumvention may not be possible by non-tech-savvy users, so blocking and filtering remain effective means of censoring the Internet access of large numbers of users.<ref name=UNESCO-2011/> | Internet censorship circumvention is one of the processes used by technologically savvy Internet users to bypass the technical aspects of Internet filtering and gain access to the otherwise censored material. Circumvention is an inherent problem for those wishing to censor the Internet because filtering and blocking do not remove content from the Internet, but instead block access to it. Therefore, as long as there is at least one publicly accessible uncensored system, it will often be possible to gain access to the otherwise censored material. However circumvention may not be possible by non-tech-savvy users, so blocking and filtering remain effective means of censoring the Internet access of large numbers of users.<ref name=UNESCO-2011/> | ||
| Different techniques and resources are used to bypass Internet censorship, including ], ]s, ]s, and circumvention software tools. Solutions have differing ease of use, speed, security, and risks. Most, however, rely on gaining access to an Internet connection that is not subject to filtering, often in a different jurisdiction not subject to the same censorship laws. According to ], over 400 |
Different techniques and resources are used to bypass Internet censorship, including ], ]s, ]s, the ] and circumvention software tools. Solutions have differing ease of use, speed, security, and risks. Most, however, rely on gaining access to an Internet connection that is not subject to filtering, often in a different jurisdiction not subject to the same censorship laws. According to ], over 400 million people use virtual private networks to circumvent censorship or for an increased level of privacy.<ref name="Guardian 5 December 2014"/> The majority of circumvention techniques are not suitable for day to day use.<ref>Roberts, H., Zuckerman, E., & Palfrey, J. (2009, March). 2007 Circumvention Landscape Report: Methods, Uses, and Tools (Rep.). Retrieved 18 March 2016, from The Berkman Center for Internet & Society at Harvard University. | ||
| </ref> | </ref> | ||
| There are risks to using circumvention software or other methods to bypass Internet censorship. In some countries, individuals that gain access to otherwise restricted content may be violating the law and if caught can be expelled, fired, jailed, or subject to other punishments and loss of access.<ref name="NYT-20140311" /><ref>, ''Internet censorship wiki''. Retrieved 2 September 2011</ref> | There are risks to using circumvention software or other methods to bypass Internet censorship. In some countries, individuals that gain access to otherwise restricted content may be violating the law and if caught can be expelled, fired, jailed, or subject to other punishments and loss of access.<ref name="NYT-20140311" /><ref> {{Webarchive|url=https://web.archive.org/web/20110908041315/http://en.cship.org/Risks |date=8 September 2011 }}, ''Internet censorship wiki''. Retrieved 2 September 2011</ref> | ||
| In June 2011 |
In June 2011, ''The New York Times'' reported that the U.S. is engaged in a "global effort to deploy 'shadow' Internet and mobile phone systems that dissidents can use to undermine repressive governments that seek to silence them by censoring or shutting down telecommunications networks."<ref> {{Webarchive|url=https://web.archive.org/web/20201111175637/http://www.nytimes.com/2011/06/12/world/12internet.html?pagewanted=all |date=11 November 2020 }}, James Glanz and John Markoff, ''The New York Times'', 12 June 2011</ref> | ||
| Another way to circumvent Internet censorship is to physically go to an area where the Internet is not censored. In 2017 a so-called "Internet refugee camp" was established by IT workers in the village of Bonako, just outside an area of Cameroon where the Internet is regularly blocked.<ref>https://qz.com/942879/an-internet-shutdown-in-cameroon-has-forced-startups-to-create-an-internet-refugee-camp-in-bonako-village/</ref><ref> |
Another way to circumvent Internet censorship is to physically go to an area where the Internet is not censored. In 2017, a so-called "Internet refugee camp" was established by IT workers in the village of Bonako, just outside an area of Cameroon where the Internet is regularly blocked.<ref>{{Cite web |url=https://qz.com/africa/942879/an-internet-shutdown-in-cameroon-has-forced-startups-to-create-an-internet-refugee-camp-in-bonako-village/|title=Reeling from an internet shutdown, startups in Cameroon have created an "internet refugee camp"|first=Abdi Latif|last=Dahir|website=Quartz Africa|date=28 March 2017 |access-date=30 January 2020|archive-date=12 November 2020|archive-url=https://web.archive.org/web/20201112015837/https://qz.com/africa/942879/an-internet-shutdown-in-cameroon-has-forced-startups-to-create-an-internet-refugee-camp-in-bonako-village/|url-status=live}}</ref><ref>{{Cite web|url=https://www.aljazeera.com/news/2018/01/cameroon-internet-shutdowns-cost-anglophones-millions-180123202824701.html|title=Cameroon internet shutdowns cost Anglophones millions |website=Al Jazeera |date=26 Jan 2018 |first1=Yarno |last1=Ritzen |access-date=30 January 2020|archive-date=22 September 2020|archive-url=https://web.archive.org/web/20200922042211/https://www.aljazeera.com/news/2018/01/cameroon-internet-shutdowns-cost-anglophones-millions-180123202824701.html|url-status=live}}</ref> | ||
| === Increased use of HTTPS === | |||
| The use of ] versus what originally was ] in web searches created greater accessibility to most sites originally blocked or heavily monitored. Many social media sites including, Facebook, Google, and Twitter have added an automatic redirection to HTTPS as of 2017.<ref name="Connolly">{{Cite web|url=https://thenextweb.com/media/2016/01/27/medium-stands-by-investigative-journalists-as-malaysia-blocks-the-site/|title=Medium stands by journalists as Malaysia blocks the site|last=Connolly|first=Amanda|date=2016-01-27|website=The Next Web|language=en-us|access-date=2020-04-26|archive-date=29 November 2020|archive-url=https://web.archive.org/web/20201129195843/https://thenextweb.com/media/2016/01/27/medium-stands-by-investigative-journalists-as-malaysia-blocks-the-site/|url-status=live}}</ref> With the added adoption of HTTPS use, "censors" are left with limited options of either completely blocking all content or none of it.<ref name=":02">{{Cite web |url=https://dash.harvard.edu/bitstream/handle/1/33084425/The%20Shifting%20Landscape%20of%20Global%20Internet%20Censorship-%20Internet%20Monitor%202017.pdf|title=The Shifting Landscape of Global Internet Censorship|last1=Zittrain |last2=Faris |last3=Noman |last4=Clark |last5=Tilton |last6=Morrison-Westphal |first1=Jonathan |first2=Robert |first3=Helmi |first4=Justin |first5=Casey |first6=Ryan |date=June 2017 |website=Dash.Harvard.Edu|url-status=live|archive-url=https://web.archive.org/web/20181206170555/https://dash.harvard.edu/bitstream/handle/1/33084425/The%20Shifting%20Landscape%20of%20Global%20Internet%20Censorship-%20Internet%20Monitor%202017.pdf|archive-date=6 December 2018|access-date=25 April 2020}}</ref> | |||
| The use of ] does not inherently prevent the censorship of an entire domain, as the domain name is left unencrypted in the ClientHello of the ] handshake. The ] TLS extension expands on HTTPS and encrypts the entire ClientHello but this depends on both client and server support.<ref>{{Cite web|date=24 September 2018|title=Encrypting SNI: Fixing One of the Core Internet Bugs |url=https://blog.cloudflare.com/esni/|access-date=22 August 2020|website=The Cloudflare Blog|language=en |archive-date=12 December 2020|archive-url=https://web.archive.org/web/20201212025956/https://blog.cloudflare.com/esni/|url-status=live}}</ref><ref>{{Cite web|last1=Oku|first1=Kazuho |last2=Wood|first2=Christopher|last3=Rescorla |first3=Eric |last4=Sullivan|first4=Nick |title=Encrypted Server Name Indication for TLS 1.3 |publisher=IETF |date=June 2020 |url=https://tools.ietf.org/html/draft-ietf-tls-esni-07.html|access-date=22 August 2020 |language=en |archive-date=16 July 2020|archive-url=https://web.archive.org/web/20200716061945/https://tools.ietf.org/html/draft-ietf-tls-esni-07.html |url-status=live}}</ref> | |||
| ==Common targets== | ==Common targets== | ||
| There are several motives or rationales for Internet filtering: politics and power, social norms and morals, and security concerns. Protecting existing economic interests is an additional emergent motive for Internet filtering. In addition, networking tools and applications that allow the sharing of information related to these motives are themselves subjected to filtering and blocking. And while there is considerable variation from country to country, the blocking of web sites in a local language is roughly twice that of web sites available only in English or other international languages.<ref name=Faris-2008>, Robert Faris and Nart Villeneuve, in {{webarchive|url=https://web.archive.org/web/20090226100258/http://mitpress.mit.edu/catalog/item/default.asp?ttype=2&tid=11329 |date=26 February 2009 }}, Ronald Deibert, John Palfrey, Rafal Rohozinski, and Jonathan Zittrain, eds., MIT Press (Cambridge), 2008</ref> | There are several motives or rationales for Internet filtering: politics and power, social norms and morals, and security concerns. Protecting existing economic interests is an additional emergent motive for Internet filtering. In addition, networking tools and applications that allow the sharing of information related to these motives are themselves subjected to filtering and blocking. And while there is considerable variation from country to country, the blocking of web sites in a local language is roughly twice that of web sites available only in English or other international languages.<ref name=Faris-2008> {{Webarchive|url=https://web.archive.org/web/20200809044356/http://opennet.net/sites/opennet.net/files/Deibert_02_Ch01_005-028.pdf |date=9 August 2020 }}, Robert Faris and Nart Villeneuve, in {{webarchive|url=https://web.archive.org/web/20090226100258/http://mitpress.mit.edu/catalog/item/default.asp?ttype=2&tid=11329 |date=26 February 2009 }}, Ronald Deibert, John Palfrey, Rafal Rohozinski, and Jonathan Zittrain, eds., MIT Press (Cambridge), 2008</ref> | ||
| ===Politics and power=== | ===Politics and power=== | ||
| Line 121: | Line 142: | ||
| Examples include: | Examples include: | ||
| * Political blogs and |
* Political blogs and websites<ref>{{cite web |url=http://www.news.com/Blog-censorship-gains-support/2100-1028_3-5670096.html |archive-url=https://archive.today/20120529125713/http://www.news.com/Blog-censorship-gains-support/2100-1028_3-5670096.html |url-status=dead |archive-date=29 May 2012 |title=Blog censorship gains support |work=CNET |access-date=5 April 2015 }}</ref> | ||
| * '']'' sites, sites with content that offends the dignity of or challenges the authority of a reigning ] or of a ] | * '']'' sites, sites with content that offends the dignity of or challenges the authority of a reigning ] or of a ] | ||
| * ] and ] group sites in ] or ], ] faith, and indigenous ] sites in ] | * ] and ] group sites in ] or ], ] faith, and indigenous ] sites in ] | ||
| * ], or "50 Cent Army" that worked to sway negative public opinion on the ]<ref>{{Cite web|url=http://feer.com:80/essays/2008/august/chinas-guerrilla-war-for-the-web|archive-url=https://web.archive.org/web/20090225113222/http://feer.com/essays/2008/august/chinas-guerrilla-war-for-the-web|url-status=dead|archive-date=25 February 2009|title=Far Eastern Economic Review {{!}} China's Guerrilla War for the Web|date=2009-02-25|access-date=2020-04-25}}</ref> | |||
| * ] | |||
| * Sites aimed at religious conversion from Islam to Christianity<ref name=Faris-2008/> | * Sites aimed at religious conversion from Islam to Christianity<ref name=Faris-2008/> | ||
| * Sites criticizing the government or an authority in the country<ref name=time20151123/> | * Sites criticizing the government or an authority in the country<ref name=time20151123/> | ||
| * Sites that comment on political parties that oppose the current government of a country<ref name=time20151123/> | * Sites that comment on political parties that oppose the current government of a country<ref name=time20151123/> | ||
| * Sites that accuse authorities of corruption<ref name=time20151123/> | * Sites that accuse authorities of corruption<ref name=time20151123/> | ||
| * Sites that comment on minorities or ] issues<ref name=time20151123/> | * Sites that comment on minorities or ] issues<ref name=time20151123/> | ||
| * ] symbols and imagery in ], ], ], ], ], ], ], and ] | |||
| * ] and similar websites, particularly in ] and ]<ref>{{cite news |url=http://www.theaustralian.news.com.au/story/0,25197,22885402-12335,00.html |title=Latest Stories From News.Com.Au |access-date=8 December 2007 |archive-url=https://web.archive.org/web/20081211175806/http://www.theaustralian.news.com.au/story/0,25197,22885402-12335,00.html |archive-date=11 December 2008 |url-status=dead }}</ref> | |||
| ===Social norms=== | ===Social norms=== | ||
| Social filtering is censorship of topics that are held to be antithetical to accepted societal norms.<ref name=Faris-2008/> In particular censorship of ] and |
Social filtering is censorship of topics that are held to be antithetical to accepted societal norms.<ref name=Faris-2008/> In particular censorship of ] and content deemed ] enjoys very widespread public support and such content is subject to censorship and other restrictions in most countries. | ||
| Examples include: | Examples include: | ||
| * Sites that include ] inciting ], ], ], or other forms of bigotry | * Sites that include ] inciting ], ], ], or other forms of bigotry | ||
| * Sites seen as promoting ] (])<ref> The Fix 2013-02-28</ref> | * Sites seen as promoting ] (such as ])<ref> {{Webarchive|url=https://web.archive.org/web/20201111213509/http://www.thefix.com/content/russia-blacklists-drug-wikipedia-erowid91343 |date=11 November 2020 }} The Fix 2013-02-28</ref> | ||
| * ], ], prostitution, and ] sites | * ], ], prostitution, and ] sites | ||
| * ] and ] |
* ] and ]-related sites (see also ]) | ||
| * Gambling sites | * Gambling sites | ||
| * Sites encouraging or inciting violence<ref name=time20151123>{{cite magazine |title= |
* Sites encouraging or inciting violence<ref name="time20151123">{{cite magazine |date=2015-11-23 |title=Which Countries Censor the Internet? |url=https://time.com/4109882/which-countries-censor-the-internet/ |url-status=live |magazine=] |page=36 |archive-url=https://web.archive.org/web/20151112231055/https://time.com/4109882/which-countries-censor-the-internet/ |archive-date=2015-11-12 |access-date=2023-08-05 |url-access=subscription}}</ref> | ||
| * Sites promoting criminal activity<ref name=time20151123/> | * Sites promoting criminal activity<ref name=time20151123/> | ||
| * Sites that contain ] content, particularly when directed at a majority or state supported religion<ref name=time20151123/> | |||
| * ] symbols and imagery in ], ], ], ], ], and ] | |||
| * ] and similar websites, particularly in ] and ]<ref>{{cite news |url=http://www.theaustralian.news.com.au/story/0,25197,22885402-12335,00.html |title=Latest Stories From News.Com.Au}}</ref> | |||
| * Sites that contain ] content, particularly when directed at a majority or state supported religion<ref name=time20151123/> | |||
| * Sites that contain ] content<ref name=time20151123/> | * Sites that contain ] content<ref name=time20151123/> | ||
| * Sites that include ]<ref name=time20151123/> | * Sites that include ]<ref name=time20151123/> | ||
| Line 149: | Line 172: | ||
| ===Security concerns=== | ===Security concerns=== | ||
| Many organizations implement filtering as part of a ] strategy to protect their environments from ],<ref>{{cite web |url=http://www.gartner.com/id=747218 |publisher=] |title=Why Malware Filtering Is Necessary in the Web Gateway |date=26 August 2008 | |
Many organizations implement filtering as part of a ] strategy to protect their environments from ],<ref>{{cite web |url=http://www.gartner.com/id=747218 |archive-url=https://wayback.archive-it.org/all/20171018210253/https://www.gartner.com/id=747218 |url-status=dead |archive-date=18 October 2017 |publisher=] |title=Why Malware Filtering Is Necessary in the Web Gateway |date=26 August 2008 |access-date=14 April 2012}}</ref> and to protect their reputations in the event of their networks being used, for example, to carry out sexual harassment. | ||
| Internet filtering related to threats to ] that targets the Web sites of ], ], and terrorists often enjoys wide public support.<ref name=Faris-2008/> | Internet filtering related to threats to ] that targets the Web sites of ], ], and terrorists often enjoys wide public support.<ref name=Faris-2008/> | ||
| Examples include: | Examples include: | ||
| * ]<ref>, OpenNet Initiative: Bulletin 009, 31 January 2005</ref> | * ]<ref> {{Webarchive|url=https://web.archive.org/web/20201209213747/http://opennet.net/bulletins/009/ |date=9 December 2020 }}, OpenNet Initiative: Bulletin 009, 31 January 2005</ref> | ||
| * Blocking sites of groups that foment domestic conflict in ] | * Blocking of sites of groups that foment domestic conflict in ]<ref name="Faris-2008" /> | ||
| * Blocking of sites of the ] in some countries in the Middle East | * Blocking of sites of the ] in some countries in the Middle East | ||
| * Blocking of sites such as ] thought to be related to the internet hacker group ]<ref> {{Webarchive|url=https://web.archive.org/web/20201209213950/https://www.washingtonpost.com/politics/federal-authorities-take-on-anonymous-hackers/2011/09/11/gIQAYrhgMK_story.html |date=9 December 2020 }}, Associated Press in the Washington Post, 12 September 2011</ref> | |||
| * Blocking ]<ref>{{cite web |url=https://wikileaks.org/Australia_secretly_censors_Wikileaks_press_release_and_Danish_Internet_censorship_list%2C_16_Mar_2009 |title=Australia secretly censors Wikileaks press release and Danish Internet censorship list |date=16 March 2009 |work=wikileaks.org |accessdate=5 April 2015}}</ref> | |||
| * Blocking sites such as ] thought to be related to the group ]<ref>, Associated Press in the Washington Post, 12 September 2011</ref> | |||
| ===Protection of existing economic interests and copyright=== | ===Protection of existing economic interests and copyright=== | ||
| The protection of existing economic interests is sometimes the motivation for blocking new Internet services such as low-cost telephone services that use ] (VoIP). These services can reduce the customer base of telecommunications companies, many of which enjoy entrenched monopoly positions and some of which are government sponsored or controlled.<ref name=Faris-2008/> | The protection of existing economic interests is sometimes the motivation for blocking new Internet services such as low-cost telephone services that use ] (VoIP). These services can reduce the customer base of telecommunications companies, many of which enjoy entrenched monopoly positions and some of which are government sponsored or controlled.<ref name=Faris-2008/> | ||
| ] activists ], ] and ] have alleged that censorship of child pornography is being used as a pretext by copyright lobby organizations to get politicians to implement similar site blocking legislation against copyright-related piracy.<ref>{{cite web |url=https://torrentfreak.com/the-copyright-lobby-absolutely-loves-child-pornography-110709/ |title=The Copyright Lobby Absolutely Loves Child Pornography |author=Rick Falkvinge |date=9 July 2011 |work=] | |
] activists ], ] and ] have alleged that censorship of child pornography is being used as a pretext by copyright lobby organizations to get politicians to implement similar site blocking legislation against copyright-related piracy.<ref>{{cite web |url=https://torrentfreak.com/the-copyright-lobby-absolutely-loves-child-pornography-110709/ |title=The Copyright Lobby Absolutely Loves Child Pornography |author=Rick Falkvinge |date=9 July 2011 |work=] |access-date=26 July 2012 |author-link=Rick Falkvinge |archive-date=9 December 2020 |archive-url=https://web.archive.org/web/20201209214207/https://torrentfreak.com/the-copyright-lobby-absolutely-loves-child-pornography-110709/ |url-status=live }}</ref> | ||
| Examples include: | Examples include: | ||
| * ] and ] (P2P) related websites such as ] | * ] and ] (P2P) related websites such as ] | ||
| * ] | * ] | ||
| * Sites that sell or distribute music, but are not 'approved' by rights holders, such as ] | * Sites that sell or distribute music, but are not 'approved' by rights holders, such as ] | ||
| ===Network tools=== | ===Network tools=== | ||
| Line 174: | Line 196: | ||
| Examples include: | Examples include: | ||
| * Media sharing websites (e.g. ] and ])<ref>{{cite web |url=http://mashable.com/2007/03/11/youtube-blocked-inthailand/ |title=YouTube Blocked in...Thailand |date=11 March 2007 |work=Mashable | |
* Media sharing websites (e.g. ] and ])<ref>{{cite web |url=http://mashable.com/2007/03/11/youtube-blocked-inthailand/ |title=YouTube Blocked in...Thailand |date=11 March 2007 |work=Mashable |access-date=5 April 2015 |archive-date=9 August 2020 |archive-url=https://web.archive.org/web/20200809115202/https://mashable.com/2007/03/11/youtube-blocked-inthailand/ |url-status=live }}</ref> | ||
| * ] (e.g. ] and Instagram) | * ] (e.g. ] and Instagram) | ||
| * Translation sites and tools | * Translation sites and tools | ||
| * E-mail providers | * E-mail providers | ||
| * ] sites | * ] sites | ||
| * ] sites such as ] | * ] sites such as ] and ] | ||
| * ] sites such as ] and ]<ref>, Agence France-Presse (AFP) in ''The Independent'', 8 September 2011</ref> | * ] sites such as ] and ]<ref> {{Webarchive|url=https://web.archive.org/web/20171104175518/https://www.independent.co.uk/life-style/gadgets-and-tech/china-struggles-to-tame-microblogging-masses-2351509.html |date=4 November 2017 }}, Agence France-Presse (AFP) in ''The Independent'', 8 September 2011</ref> | ||
| * ] | * ] | ||
| * ] | * ] | ||
| ** ]s | ** ]s | ||
| ** ] | ** ] | ||
| * ] such as ]<ref>", Helmi Noman, OpenNet Initiative, March 2010</ref> and ]<ref>, OpenNet Initiative: Bulletin 006, 3 September 2004</ref><ref>, Benjamin Edelman, Berkman Center for Internet & Society, Harvard Law School, 13 April 2003</ref> – particularly in ] and ]<ref>{{cite news |url=http://news.bbc.co.uk/2/hi/technology/2231101.stm |work=BBC News |title=China blocking Google |date=2 September 2002 | |
* ] such as ]<ref> {{Webarchive|url=https://web.archive.org/web/20201213174600/http://opennet.net/sex-social-mores-and-keyword-filtering-microsoft-bing-arabian-countries |date=13 December 2020 }}", Helmi Noman, OpenNet Initiative, March 2010</ref> and ]<ref> {{Webarchive|url=https://web.archive.org/web/20200808234634/http://opennet.net/bulletins/006/ |date=8 August 2020 }}, OpenNet Initiative: Bulletin 006, 3 September 2004</ref><ref> {{Webarchive|url=https://web.archive.org/web/20130304235802/http://cyber.law.harvard.edu/archived_content/people/edelman/google-safesearch/ |date=4 March 2013 }}, Benjamin Edelman, Berkman Center for Internet & Society, Harvard Law School, 13 April 2003</ref> – particularly in ] and ]<ref>{{cite news |url=http://news.bbc.co.uk/2/hi/technology/2231101.stm |work=BBC News |title=China blocking Google |date=2 September 2002 |access-date=5 May 2010 |archive-date=11 December 2020 |archive-url=https://web.archive.org/web/20201211035040/http://news.bbc.co.uk/2/hi/technology/2231101.stm |url-status=live }}</ref> | ||
| ===Information about individuals=== | ===Information about individuals=== | ||
| {{main|Right to be forgotten}} | {{main|Right to be forgotten}} | ||
| The ''right to be forgotten'' is a concept that has been discussed and put into practice in the ]. In May 2014, the ] ruled against ] in '']'', a case brought by a Spanish man who requested the removal of a link to a digitized 1998 article in ''La Vanguardia'' newspaper about an auction for his foreclosed home, for a debt that he had subsequently paid.<ref>{{cite web |url=https://www.wired.co.uk/news/archive/2014-05/15/google-vs-spain |title=What we can salvage from 'right to be forgotten' ruling |publisher=Wired.co.uk |date=15 May 2014 | |
The ''right to be forgotten'' is a concept that has been discussed and put into practice in the ]. In May 2014, the ] ruled against ] in '']'', a case brought by a Spanish man who requested the removal of a link to a digitized 1998 article in ''La Vanguardia'' newspaper about an auction for his foreclosed home, for a debt that he had subsequently paid.<ref>{{cite web |url=https://www.wired.co.uk/news/archive/2014-05/15/google-vs-spain |title=What we can salvage from 'right to be forgotten' ruling |publisher=Wired.co.uk |date=15 May 2014 |access-date=16 May 2014 |author=Julia Powles |url-status=dead |archive-url=https://web.archive.org/web/20140516024112/http://www.wired.co.uk/news/archive/2014-05/15/google-vs-spain |archive-date=16 May 2014}}</ref> He initially attempted to have the article removed by complaining to Spain's data protection agency—''Agencia Española de Protección de Datos''—which rejected the claim on the grounds that it was lawful and accurate, but accepted a complaint against Google and asked Google to remove the results.<ref>{{cite web |last=Solon |first=Olivia |title=People have the right to be forgotten, rules EU court |url=https://www.wired.co.uk/news/archive/2014-05/13/right-to-be-forgotten-ruling |work=Wired.co.uk |publisher=Conde Nast Digital |access-date=13 May 2014 |date=13 May 2014 |url-status=dead |archive-url=https://web.archive.org/web/20140514071400/http://www.wired.co.uk/news/archive/2014-05/13/right-to-be-forgotten-ruling |archive-date=14 May 2014}}</ref> Google sued in Spain and the lawsuit was transferred to the European Court of Justice. The court ruled in ''Costeja'' that search engines are responsible for the content they point to and thus, Google was required to comply with EU ] laws.<ref>{{cite news |title=EU court backs 'right to be forgotten' in Google case |url=https://www.bbc.com/news/world-europe-27388289 |work=BBC News |access-date=13 May 2014 |date=13 May 2014 |archive-date=25 November 2020 |archive-url=https://web.archive.org/web/20201125060034/https://www.bbc.com/news/world-europe-27388289 |url-status=live }}</ref><ref>{{cite web |title=EU court rules Google must tweak search results in test of "right to be forgotten" |url=http://www.cbsnews.com/news/eu-court-google-must-tweak-search-results-right-to-be-forgotten/ |publisher=CBS News |access-date=13 May 2014 |date=13 May 2014 |archive-date=3 December 2019 |archive-url=https://web.archive.org/web/20191203105145/https://www.cbsnews.com/news/eu-court-google-must-tweak-search-results-right-to-be-forgotten/ |url-status=live }}</ref> It began compliance on 30 May 2014 during which it received 12,000 requests to have personal details removed from its search engine.<ref name="GoogleEU">{{cite news |title=Removal of Google personal information could become work intensive |url=http://www.europenews.net/index.php/sid/222490797/scat/88176adfdf246af5/ht/Removal-of-Google-personal-information-could-become-work-intensive |access-date=2 June 2014 |publisher=Europe News.Net |archive-url=https://web.archive.org/web/20141021150331/http://www.europenews.net/index.php/sid/222490797/scat/88176adfdf246af5/ht/Removal-of-Google-personal-information-could-become-work-intensive |archive-date=21 October 2014 |url-status=dead }}</ref> | ||
| ] claimed that "'']'' ruling ... allows individuals to complain to search engines about information they do not like with no legal oversight. This is akin to marching into a library and forcing it to pulp books. Although the ruling is intended for private individuals it opens the door to anyone who wants to whitewash their personal history....The |
] claimed that "'']'' ruling ... allows individuals to complain to search engines about information they do not like with no legal oversight. This is akin to marching into a library and forcing it to pulp books. Although the ruling is intended for private individuals it opens the door to anyone who wants to whitewash their personal history....The Court's decision is a retrograde move that misunderstands the role and responsibility of search engines and the wider internet. It should send chills down the spine of everyone in the European Union who believes in the crucial importance of free expression and freedom of information."<ref>{{cite web |url=http://www.indexoncensorship.org/2014/05/index-blasts-eu-court-ruling-right-forgotten/ |title=Index blasts EU court ruling on "right to be forgotten" |work=indexoncensorship.org |date=13 May 2014 |access-date=5 April 2015 |archive-date=19 September 2020 |archive-url=https://web.archive.org/web/20200919094343/http://www.indexoncensorship.org/2014/05/index-blasts-eu-court-ruling-right-forgotten/ |url-status=live }}</ref> | ||
| ==Resilience== | |||
| Various contexts influence whether or not an internet user will be resilient to censorship attempts. Users are more resilient to censorship if they are aware that information is being manipulated. This awareness of censorship leads to users finding ways to circumvent it. Awareness of censorship also allows users to factor this manipulation into their belief systems. Knowledge of censorship also offers some citizens incentive to try to discover information that is being concealed. In contrast, those that lack awareness of censorship cannot easily compensate for information manipulation.<ref name="Roberts">{{cite journal |doi=10.1146/annurev-polisci-050718-032837|doi-access=free|title=Resilience to Online Censorship|year=2020 |last1=Roberts|first1=Margaret E.|journal=Annual Review of Political Science|volume=23|pages=401–419}}</ref> | |||
| Other important factors for censorship resiliency are the demand for the information being concealed, and the ability to pay the costs to circumvent censorship. Entertainment content is more resilient to online censorship than political content, and users with more education, technology access, and wider, more diverse social networks are more resilient to censorship attempts.<ref name="Roberts"/> | |||
| ==Around the world== | ==Around the world== | ||
| {{Main |Internet censorship by country |Censorship by country}} | {{Main |Internet censorship and surveillance by country |Censorship by country}} | ||
| {{clear}} | |||
| ]'''<ref name=FOTN-2018> | |||
| As more people in more places begin using the Internet for important activities, there is an increase in online censorship, using increasingly sophisticated techniques. The motives, scope, and effectiveness of Internet censorship vary widely from country to country. The countries engaged in state-mandated filtering are clustered in three main regions of the world: east Asia, central Asia, and the ]. | |||
| {{cite web |title=Freedom on the Net 2018 |url=https://freedomhouse.org/sites/default/files/FOTN_2018_Final%20Booklet_11_1_2018.pdf |website=Freedom House |date=November 2018 |accessdate=1 November 2018}}</ref><ref name=ONISS-Nov2011>OpenNet Initiative , 8 November 2011 and , the OpenNet Initiative is a collaborative partnership of the Citizen Lab at the Munk School of Global Affairs, University of Toronto; the Berkman Center for Internet & Society at Harvard University; and the SecDev Group, Ottawa</ref><ref name=ONIChildPornLegal/><ref name=RWBEnemies2014/><ref name=RWBEnemies2012/><!-- defined by template:RWB Internet lists --></center> | |||
| <blockquote> | |||
| Countries in other regions also practice certain forms of filtering. In the ], state-mandated Internet filtering occurs on some computers in libraries and ]. Content related to ] or ] is blocked in ] and ]. ] and ] are blocked in many countries throughout the world.<ref name=Zittrain-2008>{{cite web |url=http://mitpress.mit.edu/books/chapters/0262541963intro1.pdf |title=Introduction |access-date=2011-09-14 |url-status=dead |archive-url=https://web.archive.org/web/20120629074247/http://mitpress.mit.edu/books/chapters/0262541963intro1.pdf |archive-date=29 June 2012}}, Jonathan Zittrain and John Palfrey, in {{webarchive|url=https://web.archive.org/web/20090226100258/http://mitpress.mit.edu/catalog/item/default.asp?ttype=2&tid=11329 |date=26 February 2009 }}, Ronald Deibert, John Palfrey, Rafal Rohozinski, and Jonathan Zittrain, eds., MIT Press (Cambridge), 2008</ref> In fact, many countries throughout the world, including some democracies with long traditions of strong support for ] and ], are engaged in some amount of online censorship, often with substantial public support.<ref> {{Webarchive|url=https://web.archive.org/web/20200919121222/http://opennet.net/sites/opennet.net/files/Deibert_03_Ch02_029-056.pdf |date=19 September 2020 }}, Jonathan Zittrain and John Palfrey, in {{webarchive|url=https://web.archive.org/web/20090226100258/http://mitpress.mit.edu/catalog/item/default.asp?ttype=2&tid=11329 |date=26 February 2009 }}, Ronald Deibert, John Palfrey, Rafal Rohozinski, and Jonathan Zittrain, eds., MIT Press (Cambridge), 2008</ref> | |||
| {{Col begin}} | |||
| {{Col-1-of-2}} | |||
| Internet censorship in ] is among the most stringent in the world. The government blocks Web sites that discuss the ], the 1989 crackdown on ], the banned spiritual practice ], as well as many general Internet sites.<ref>{{cite news|title=Internet Censorship in China |url=http://topics.nytimes.com/top/news/international/countriesandterritories/china/internet_censorship/index.html|access-date=9 March 2013|newspaper=The New York Times|date=28 December 2012|archive-date=4 March 2016|archive-url=https://web.archive.org/web/20160304050504/http://topics.nytimes.com/top/news/international/countriesandterritories/china/internet_censorship/index.html|url-status=live}}</ref> The government requires Internet search firms and state media to censor issues deemed officially "sensitive," and blocks access to foreign websites including ], ], and ].<ref>{{cite book|last=Human Rights Watch|title=World Report 2012: China|date=22 January 2012|url=https://www.hrw.org/world-report-2012/world-report-2012-china|access-date=9 March 2013|archive-date=11 March 2013|archive-url=https://web.archive.org/web/20130311193943/http://www.hrw.org/world-report-2012/world-report-2012-china|url-status=live}}</ref> According to a study in 2014,<ref>{{cite journal|author=G. King |s2cid=5398090|title=Reverse-engineering censorship in China: Randomized experimentation and participant observation|journal=Science |doi=10.1126/science.1251722|date=22 August 2014 |volume=345|issue=6199 |page=891|display-authors=etal|pmid=25146296|url=http://nrs.harvard.edu/urn-3:HUL.InstRepos:37091695 |access-date=11 July 2019|archive-date=24 August 2020|archive-url=https://web.archive.org/web/20200824001559/https://dash.harvard.edu/handle/1/37091695|url-status=live}}</ref> censorship in China is used to muzzle those outside government who attempt to spur the creation of crowds for any reason—in opposition to, in support of, or unrelated to the government. | |||
| {{legend|#F9D|Pervasive: ''Large and broad''}} | |||
| {{legend|#FDD|Substantial: ''Medium''}} | |||
| {{legend|#FFD|Selective: ''Small and specific''}} | |||
| {{Col-2-of-2}} | |||
| {{legend|#98FB98|Little or no}} | |||
| {{legend|#e0e0e0|Not classified / no data}} | |||
| {{Col end}} | |||
| </blockquote> | |||
| ]]{{clear}} | |||
| As more people in more places begin using the Internet for important activities, there is an increase in online censorship, using increasingly sophisticated techniques. The motives, scope, and effectiveness of Internet censorship vary widely from country to country. The countries engaged in state-mandated filtering are clustered in three main regions of the world: east Asia, central Asia, and the ]. | |||
| There are international bodies that oppose internet censorship, for example "Internet censorship is open to challenge at the World Trade Organization (WTO) as it can restrict trade in online services, a forthcoming study argues".<ref>{{Cite journal|title=WTO could challenge Internet censorship |journal=Newsletter on Intellectual Freedom|volume=59|issue=1|location=Chicago|publisher=American Library Association|date=January 2010|page=6|id={{ProQuest|217137198}}}}</ref> | |||
| Countries in other regions also practice certain forms of filtering. In the ] state-mandated Internet filtering occurs on some computers in libraries and ]. Content related to ] or ] is blocked in ] and ]. ] and ] are blocked in many countries throughout the world.<ref name=Zittrain-2008>{{cite web |url=http://mitpress.mit.edu/books/chapters/0262541963intro1.pdf |title=Introduction |accessdate=2011-09-14 |deadurl=bot: unknown |archiveurl=https://web.archive.org/web/20120629074247/http://mitpress.mit.edu/books/chapters/0262541963intro1.pdf |archivedate=29 June 2012 |df=dmy-all }}, Jonathan Zittrain and John Palfrey, in {{webarchive|url=https://web.archive.org/web/20090226100258/http://mitpress.mit.edu/catalog/item/default.asp?ttype=2&tid=11329 |date=26 February 2009 }}, Ronald Deibert, John Palfrey, Rafal Rohozinski, and Jonathan Zittrain, eds., MIT Press (Cambridge), 2008</ref> In fact, many countries throughout the world, including some democracies with long traditions of strong support for ] and ], are engaged in some amount of online censorship, often with substantial public support.<ref>, Jonathan Zittrain and John Palfrey, in {{webarchive|url=https://web.archive.org/web/20090226100258/http://mitpress.mit.edu/catalog/item/default.asp?ttype=2&tid=11329 |date=26 February 2009 }}, Ronald Deibert, John Palfrey, Rafal Rohozinski, and Jonathan Zittrain, eds., MIT Press (Cambridge), 2008</ref> | |||
| ===International concerns=== | |||
| Internet censorship in ] is among the most stringent in the world. The government blocks Web sites that discuss the ], the 1989 crackdown on ], the banned spiritual practice ], as well as many general Internet sites.<ref>{{cite news|title=Internet Censorship in China|url=http://topics.nytimes.com/top/news/international/countriesandterritories/china/internet_censorship/index.html|accessdate=9 March 2013|newspaper=The New York Times|date=December 28, 2012}}</ref> The government requires Internet search firms and state media to censor issues deemed officially “sensitive,” and blocks access to foreign websites including ], ], and ].<ref>{{cite web|last=Human Rights Watch|title=World Report 2012: China|url=https://www.hrw.org/world-report-2012/world-report-2012-china|accessdate=9 March 2013}}</ref> According to a recent{{when|date=May 2019}} study,<ref>{{cite journal|author=G. King|title=Reverse-engineering censorship in China: Randomized experimentation and participant observation|journal=Science|doi= 10.1126/science.1251722 |date=22 August 2014|volume= 345 |issue= 6199 |page=891|display-authors=etal |pmid=25146296|url=http://nrs.harvard.edu/urn-3:HUL.InstRepos:37091695}}</ref> censorship in China is used to muzzle those outside government who attempt to spur the creation of crowds for any reason—in opposition to, in support of, or unrelated to the government. The government allows the Chinese people to say whatever they like about the state, its leaders, or their policies, because talk about any subject unconnected to collective action is not censored. The value that Chinese leaders find in allowing and then measuring criticism by hundreds of millions of Chinese people creates actionable information for them and, as a result, also for academic scholars and public policy analysts. | |||
| Generally, national laws affecting content within a country only apply to services that operate within that country and do not affect international services, but this has not been established clearly by international case law. There are concerns that due to the vast differences in freedom of speech between countries, that the ability for one country to affect speech across the global Internet could have chilling effects. | |||
| For example, ] had won a case at the ] in September 2019 that ruled that the EU's right to be forgotten only applied to services within the EU, and not globally.<ref>{{cite web |url=https://www.bbc.com/news/technology-49808208 |title=Google wins landmark right to be forgotten case |first=Leo |last=Kelion |date=24 September 2019 |access-date=3 October 2019 |publisher=] |url-status=live |archive-url=https://web.archive.org/web/20201201130541/https://www.bbc.com/news/technology-49808208 |archive-date=1 December 2020}}</ref> | |||
| There are international bodies that oppose internet censorship, for example "Internet censorship is open to challenge at the World Trade Organization (WTO) as it can restrict trade in online services, a forthcoming study argues".<ref></ref> | |||
| But in a contrary decision in October 2019, the same court ruled that ] was required to globally comply with a takedown request made in relationship to defamatory material that was posted to Facebook by an Austrian that was libelous of another, which had been determined to be illegal under Austrian laws. The case created a problematic precedent that the Internet may become subject to regulation under the strictest national defamation laws, and would limit free speech that may be acceptable in other countries.<ref>{{cite web |url=https://www.nytimes.com/2019/10/03/technology/eu-facebook-defamation.html |title=Facebook Can Be Forced to Delete Content, E.U.'s Top Court Rules |first=Adam |last=Satariano |date=3 October 2019 |access-date=3 October 2019 |work=] |archive-date=3 October 2019 |archive-url= https://web.archive.org/web/20191003125237/https://www.nytimes.com/2019/10/03/technology/eu-facebook-defamation.html |url-status=live}}</ref> | |||
| ===Internet shutdowns=== | ===Internet shutdowns=== | ||
| {{see also|Internet outage}} | |||
| Several governments have resorted to shutting down most or all Internet connections in the country. | Several governments have resorted to shutting down most or all Internet connections in all or part of the country. | ||
| This appears to have been the case on 27 and 28 January 2011 during the ], in what has been widely described as an "unprecedented" internet block.<ref name="jamescowie_techdetails_Egyptfullblock">{{cite web|last=Cowie |first=James |title=Egypt Leaves the Internet |publisher=Renesys |url=http://research.dyn.com/2011/01/egypt-leaves-the-internet/ | |
This appears to have been the case on 27 and 28 January 2011 during the ], in what has been widely described as an "unprecedented" internet block.<ref name="jamescowie_techdetails_Egyptfullblock">{{cite web|last=Cowie |first=James |title=Egypt Leaves the Internet |publisher=Renesys |url=http://research.dyn.com/2011/01/egypt-leaves-the-internet/ |access-date=28 January 2011 |archive-url=https://web.archive.org/web/20110129105030/http://www.renesys.com/blog/2011/01/egypt-leaves-the-internet.shtml |archive-date=29 January 2011 |url-status=live}}</ref><ref name="IDGnews_Egyptfullblock">{{cite news|first=Jeremy |last=Kirk |title=With Wired Internet Locked, Egypt Looks to the Sky |date=28 January 2011 |publisher=IDG News/] |url=https://www.pcworld.com/article/218064/with_wired_internet_locked_egypt_looks_to_the_sky.html |access-date=28 January 2011 |archive-url=https://web.archive.org/web/20110130223855/http://www.pcworld.com/businesscenter/article/218064/with_wired_internet_locked_egypt_looks_to_the_sky.html |archive-date=30 January 2011 |url-status=live}}</ref> About 3500 ] (BGP) routes to Egyptian networks were shut down from about 22:10 to 22:35 UTC 27 January.<ref name="jamescowie_techdetails_Egyptfullblock" /> This full block was implemented without cutting off major intercontinental ] links, with Renesys stating on 27 January, "Critical European-Asian fiber-optic routes through Egypt appear to be unaffected for now."<ref name="jamescowie_techdetails_Egyptfullblock" /> | ||
| Full blocks also occurred in ] in 2007,<ref>{{cite web|url=http://opennet.net/research/bulletins/013|title=Pulling the Plug: A Technical Review of the Internet Shutdown in Burma|work=opennet.net|access-date=5 April 2015|archive-date=15 November 2020|archive-url=https://web.archive.org/web/20201115195441/https://opennet.net/research/bulletins/013|url-status=live}}</ref> ] in 2011,<ref name=Libya-RWB-2011>{{cite web|title=Journalists confined to their hotels, Internet disconnected |url=http://en.rsf.org/journalists-confined-to-their-04-03-2011,39681.html|publisher=Reporters Without Borders|access-date=21 March 2011|archive-date=4 March 2016|archive-url=https://web.archive.org/web/20160304070847/http://en.rsf.org/journalists-confined-to-their-04-03-2011,39681.html|url-status=dead}}</ref> ] in 2019,<ref>{{Cite web|last=Skinner|first=Helena|date=2019-11-22|title=How did Iran's government pull the plug on the Internet?|url=https://www.euronews.com/2019/11/22/how-did-iran-s-government-pulled-the-plug-on-the-internet|access-date=2020-11-09|website=euronews|language=en|archive-date=27 November 2019|archive-url=https://web.archive.org/web/20191127185512/https://www.euronews.com/2019/11/22/how-did-iran-s-government-pulled-the-plug-on-the-internet|url-status=live}}</ref> and ] during the ]. | |||
| Almost all Internet connections in ] were disconnected from 3 June to 9 July 2019, in response to a political opposition sit-in seeking civilian rule.<ref>{{Cite news|url=https://www.npr.org/2019/06/16/733158506/sudans-internet-outage|title=Sudan's Internet Outage|website=NPR.org|access-date=30 July 2019|archive-date=8 August 2020|archive-url=https://web.archive.org/web/20200808065504/https://www.npr.org/2019/06/16/733158506/sudans-internet-outage|url-status=live}}</ref><ref>{{Cite web|url=https://netblocks.org/reports/sudan-internet-recovery-after-month-long-shutdown-98aZpOAo|title=Sudan internet shows signs of recovery after month-long shutdown|date=9 July 2019|access-date=30 July 2019|archive-date=14 October 2020|archive-url=https://web.archive.org/web/20201014055615/https://netblocks.org/reports/sudan-internet-recovery-after-month-long-shutdown-98aZpOAo|url-status=live}}</ref> A near-complete shutdown in ] lasted for a week after the ].<ref>{{Cite web|url=https://netblocks.org/reports/ethiopia-partially-restores-internet-days-after-amhara-coup-attempt-blackout-V8xxlo8k|title=Ethiopia partially restores internet access days after blackout following reported Amhara coup attempt|date=27 June 2019|access-date=30 July 2019|archive-date=14 October 2020|archive-url=https://web.archive.org/web/20201014125618/https://netblocks.org/reports/ethiopia-partially-restores-internet-days-after-amhara-coup-attempt-blackout-V8xxlo8k|url-status=live}}</ref> A week-long shutdown in ] followed disputes over the ].<ref>{{Cite web|url=https://netblocks.org/reports/post-election-internet-shutdown-in-mauritania-following-widespread-mobile-disruptions-JA6zmeAQ|title=Post-election internet shutdown in Mauritania following widespread mobile disruptions|date=25 June 2019|access-date=30 July 2019|archive-date=19 November 2020|archive-url=https://web.archive.org/web/20201119190509/https://netblocks.org/reports/post-election-internet-shutdown-in-mauritania-following-widespread-mobile-disruptions-JA6zmeAQ|url-status=live}}</ref> Other country-wide shutdowns in 2019 include ] after a gasoline price protests triggered police violence, ] during the ], and during or after elections in ], ], ], and ].<ref name="proton">{{Cite web|url=https://protonvpn.com/blog/internet-shutdown-2019/|title=Government that have shut down the Internet in 2019|date=26 June 2019|access-date=30 July 2019|archive-date=1 November 2020|archive-url=https://web.archive.org/web/20201101131214/https://protonvpn.com/blog/internet-shutdown-2019/|url-status=live}}</ref> | |||
| Full blocks also occurred in ] in 2007,<ref>{{cite web|url=http://opennet.net/research/bulletins/013|title=Pulling the Plug: A Technical Review of the Internet Shutdown in Burma|work=opennet.net|accessdate=5 April 2015}}</ref> ] in 2011,<ref name=Libya-RWB-2011>{{cite web|title=Journalists confined to their hotels, Internet disconnected|url=http://en.rsf.org/journalists-confined-to-their-04-03-2011,39681.html|publisher=Reporters Without Borders|accessdate=21 March 2011}}</ref> and ] during the ]. | |||
| Local shutdowns are frequently ordered in India during times of unrest and security concerns.<ref>{{Cite web|url=https://internetshutdowns.in/|title=Internet Shutdowns in India|website=internetshutdowns.in|access-date=30 July 2019|archive-date=16 November 2021|archive-url=https://web.archive.org/web/20211116233248/https://internetshutdowns.in/|url-status=live}}</ref><ref>{{Cite web|last=Krishna Mohan|first=Vaishnavi|date=2021-01-30|title=Internet Shutdowns in India: From Kashmir to Haryana|url=https://www.globalviews360.com/articles/internet-shutdowns-in-india-from-kashmir-to-haryana|access-date=2021-01-30|website=Global Views 360|language=en|archive-date=31 January 2021|archive-url=https://web.archive.org/web/20210131133650/https://www.globalviews360.com/articles/internet-shutdowns-in-india-from-kashmir-to-haryana|url-status=live}}</ref> Some countries have used localized Internet shutdowns to combat cheating during exams, including ],<ref>{{Cite web|url=https://netblocks.org/reports/iraq-shuts-down-internet-to-prevent-cheating-in-national-science-exams-gBLk94A4|title=Iraq shuts down internet to prevent cheating in national science exams|date=26 June 2019|access-date=30 July 2019|archive-date=27 October 2020|archive-url=https://web.archive.org/web/20201027100323/https://netblocks.org/reports/iraq-shuts-down-internet-to-prevent-cheating-in-national-science-exams-gBLk94A4|url-status=live}}</ref> ], ], ], and ].<ref name="proton" /> | |||
| Almost all Internet connections in ] were disconnected from 3 June to 9 July, 2019, in response to a political opposition sit-in seeking civilian rule.<ref></ref><ref></ref> A near-complete shutdown in ] lasted for a week after the ].<ref>https://netblocks.org/reports/ethiopia-partially-restores-internet-days-after-amhara-coup-attempt-blackout-V8xxlo8k</ref> A week-long shutdown in ] followed disputes over the ].<ref></ref> Other country-wide shutdowns in 2019 include ] after a gasoline price protests triggered police violence, ] during the ], and during or after elections in ], ], ], and ].<ref name="proton"></ref> | |||
| The Iranian government imposed a ] from 16 to 23 November 2019, in response to ].<ref>{{Cite web|url=https://netblocks.org/reports/internet-restored-in-iran-after-protest-shutdown-dAmqddA9|title=Internet being restored in Iran after week-long shutdown|date=2019-11-23|website=NetBlocks|language=en-US|access-date=2019-12-10|archive-date=28 November 2019|archive-url=https://web.archive.org/web/20191128081744/https://netblocks.org/reports/internet-restored-in-iran-after-protest-shutdown-dAmqddA9|url-status=live}}</ref> ], the director of Internet analysis at ], has described the operation as "unusual in its scale" and way more advanced.<ref name=":1">{{Cite web|author=Ivana Kottasová and Sara Mazloumsaki|title=What makes Iran's internet blackout different|url=https://www.cnn.com/2019/11/19/middleeast/iran-internet-shutdown-intl/index.html|access-date=2020-11-09|website=CNN|date=19 November 2019|archive-date=21 November 2019|archive-url=https://web.archive.org/web/20191121024946/https://www.cnn.com/2019/11/19/middleeast/iran-internet-shutdown-intl/index.html|url-status=live}}</ref> Beginning Saturday afternoon on 16 November 2019, the government of ] ordered the disconnection of much of the country's internet connectivity as a response to widespread protests against the government's decision to raise gas prices. While ] is no stranger to government-directed interference in its citizens’ access to the ], this outage is notable in how it differs from past events. Unlike previous efforts at censorship and bandwidth throttling, the internet of Iran is presently experiencing a multi-day wholesale disconnection for much of its population – arguably the largest such event ever for Iran.<ref name=":1" /><ref>{{Cite web|title=Iran shuts down country's internet in the wake of fuel protests|url=https://techcrunch.com/2019/11/17/iran-shuts-down-countrys-internet-in-the-wake-of-fuel-protests/|access-date=2020-11-09|website=TechCrunch|date=17 November 2019 |language=en-US|archive-date=25 November 2020|archive-url=https://web.archive.org/web/20201125173810/https://techcrunch.com/2019/11/17/iran-shuts-down-countrys-internet-in-the-wake-of-fuel-protests/|url-status=live}}</ref><ref>{{Cite web|last=Mihalcik|first=Carrie|title=Iran's internet has been shut down for days amid protests|url=https://www.cnet.com/news/irans-internet-has-been-shut-down-for-days-amid-protests/|access-date=2020-11-09|website=CNET|language=en|archive-date=26 November 2019|archive-url=https://web.archive.org/web/20191126051521/https://www.cnet.com/news/irans-internet-has-been-shut-down-for-days-amid-protests/|url-status=live}}</ref> | |||
| Local shutdowns are frequently ordered in India during times of unrest and security concerns.<ref>https://internetshutdowns.in/</ref> Some countries have used localized Internet shutdowns to combat cheating during exams, including ],<ref>[https://netblocks.org/reports/iraq-shuts-down-internet-to-prevent-cheating-in-national-science-exams-gBLk94A4 | |||
| Iraq shuts down internet to prevent cheating in national science exams]</ref> ], ], ], and ].<ref name="proton" /> | |||
| ===Reports, ratings, and trends=== | ===Reports, ratings, and trends=== | ||
| ]''' |
]'''}} | ||
| <blockquote> | <blockquote> | ||
| {{Col begin}} | {{Col begin}} | ||
| Line 245: | Line 266: | ||
| {{clear}} | {{clear}} | ||
| Detailed country by country information on Internet censorship is provided by the ], ], ], and in the ] ]'s ''Human Rights Reports''.<ref>, Bureau of Democracy, Human Rights, and Labor, U.S. Department of State, 8 April 2011</ref> The ratings produced by several of these organizations are summarized in the ] and the ] articles. | Detailed country by country information on Internet censorship is provided by the ], ], ], ], ] and in the ] ]'s ''Human Rights Reports''.<ref>, Bureau of Democracy, Human Rights, and Labor, U.S. Department of State, 8 April 2011</ref> The ratings produced by several of these organizations are summarized in the ] and the ] articles. | ||
| ====OpenNet Initiative reports==== | ====OpenNet Initiative reports==== | ||
| Through 2010 the OpenNet Initiative had documented Internet filtering by governments in over forty countries worldwide.<ref name=Noman-2011/> The level of filtering in 26 countries in 2007 and in 25 countries in 2009 was classified in the political, social, and security areas. Of the 41 separate countries classified, seven were found to show no evidence of filtering in all three areas (], ], ], ], ], ], and ]), while one was found to engage in pervasive filtering in all three areas (]), 13 were found to engage in pervasive filtering in one or more areas, and 34 were found to engage in some level of filtering in one or more areas. Of the 10 countries classified in both 2007 and 2009, one reduced its level of filtering (]), five increased their level of filtering (], ], ], ], and ]), and four maintained the same level of filtering (], ], ], and ]).<ref name=UNESCO-2011/><ref name=ONIChildPornLegal>Due to legal concerns the ] does not check for filtering of ] and because their classifications focus on technical filtering, they do not include other types of censorship.</ref> | Through 2010, the OpenNet Initiative had documented Internet filtering by governments in over forty countries worldwide.<ref name=Noman-2011/> The level of filtering in 26 countries in 2007 and in 25 countries in 2009 was classified in the political, social, and security areas. Of the 41 separate countries classified, seven were found to show no evidence of filtering in all three areas (], ], ], ], ], ], and ]), while one was found to engage in pervasive filtering in all three areas (]), 13 were found to engage in pervasive filtering in one or more areas, and 34 were found to engage in some level of filtering in one or more areas. Of the 10 countries classified in both 2007 and 2009, one reduced its level of filtering (]), five increased their level of filtering (], ], ], ], and ]), and four maintained the same level of filtering (], ], ], and ]).<ref name=UNESCO-2011/><ref name=ONIChildPornLegal>Due to legal concerns the ] does not check for filtering of ] and because their classifications focus on technical filtering, they do not include other types of censorship.</ref> | ||
| ====Freedom on the Net reports==== | ====Freedom on the Net reports==== | ||
| The ''Freedom on the Net'' reports from ] provide analytical reports and numerical ratings regarding the state of ] for countries worldwide.<ref name=FOTN-2018/> The countries surveyed represent a sample with a broad range of geographical diversity and levels of economic development, as well as varying levels of political and media freedom. The surveys ask a set of questions designed to measure each country's level of Internet and digital media freedom, as well as the access and openness of other digital means of transmitting information, particularly mobile phones and text messaging services. Results are presented for three areas: Obstacles to Access, Limits on Content, and Violations of User Rights. | The ''Freedom on the Net'' reports from ] provide analytical reports and numerical ratings regarding the state of ] for countries worldwide.<ref name=FOTN-2018>{{cite web |title=Freedom on the Net 2018 |url=https://freedomhouse.org/sites/default/files/FOTN_2018_Final%20Booklet_11_1_2018.pdf |website=Freedom House |date=November 2018 |access-date=1 November 2018 |archive-date=1 November 2018 |archive-url=https://web.archive.org/web/20181101192951/https://freedomhouse.org/sites/default/files/FOTN_2018_Final%20Booklet_11_1_2018.pdf |url-status=dead }}</ref> The countries surveyed represent a sample with a broad range of geographical diversity and levels of economic development, as well as varying levels of political and media freedom. The surveys ask a set of questions designed to measure each country's level of Internet and digital media freedom, as well as the access and openness of other digital means of transmitting information, particularly mobile phones and text messaging services. Results are presented for three areas: Obstacles to Access, Limits on Content, and Violations of User Rights. | ||
| The results from the three areas are combined into a total score for a country (from 0 for best to 100 for worst) and countries are rated as "Free" (0 to 30), "Partly Free" (31 to 60), or "Not Free" (61 to 100) based on the totals. | The results from the three areas are combined into a total score for a country (from 0 for best to 100 for worst) and countries are rated as "Free" (0 to 30), "Partly Free" (31 to 60), or "Not Free" (61 to 100) based on the totals. | ||
| Starting in 2009 Freedom House has produced nine editions of the report.<ref name=FOTN-2009>, Freedom House, accessed 16 April 2012</ref><ref name=FOTN-2011>, Freedom House, accessed 15 April 2012</ref><ref name=FOTN-2012>, Freedom House, accessed 24 September 2012</ref><ref name=FOTN-2013>, Freedom House, 3 October 2013. Retrieved 12 October 2013.</ref><ref name=FOTN-2014>{{cite web|title=Freedom on the Net 2014 |url=https://freedomhouse.org/sites/default/files/FOTN_2014_Full_Report_compressedv2_0.pdf |website=Freedom House | |
Starting in 2009 Freedom House has produced nine editions of the report.<ref name=FOTN-2009> {{Webarchive|url=https://web.archive.org/web/20180326064334/https://freedomhouse.org/sites/default/files/Freedom%20OnThe%20Net_Full%20Report.pdf |date=26 March 2018 }}, Freedom House, accessed 16 April 2012</ref><ref name=FOTN-2011> {{Webarchive|url=https://web.archive.org/web/20180616180428/http://www.freedomhouse.org/report/freedom-net/freedom-net-2011 |date=16 June 2018 }}, Freedom House, accessed 15 April 2012</ref><ref name=FOTN-2012> {{Webarchive|url=https://web.archive.org/web/20190412122311/http://www.freedomhouse.org/sites/default/files/inline_images/FOTN%202012%20FINAL.pdf |date=12 April 2019 }}, Freedom House, accessed 24 September 2012</ref><ref name=FOTN-2013> {{Webarchive|url=https://web.archive.org/web/20180422031920/http://freedomhouse.org/sites/default/files/resources/FOTN%202013_Full%20Report_0.pdf |date=22 April 2018 }}, Freedom House, 3 October 2013. Retrieved 12 October 2013.</ref><ref name=FOTN-2014>{{cite web |title=Freedom on the Net 2014 |url=https://freedomhouse.org/sites/default/files/FOTN_2014_Full_Report_compressedv2_0.pdf |website=Freedom House |access-date=14 December 2014 |archive-date=12 April 2019 |archive-url=https://web.archive.org/web/20190412122528/https://freedomhouse.org/sites/default/files/FOTN_2014_Full_Report_compressedv2_0.pdf |url-status=live }}</ref><ref name=FOTN-2015>{{cite web |title=Freedom on the Net 2015 |url=https://freedomhouse.org/sites/default/files/FH_FOTN_2015Report.pdf |website=Freedom House |date=October 2015 |access-date=27 December 2015 |archive-date=11 April 2019 |archive-url=https://web.archive.org/web/20190411210207/https://freedomhouse.org/sites/default/files/FH_FOTN_2015Report.pdf |url-status=live }}</ref><ref name=FOTN-2016>{{cite web |title=Freedom on the Net 2016 |url=https://freedomhouse.org/sites/default/files/FOTN_2016_Full_Report.pdf |website=Freedom House |date=October 2016 |access-date=25 March 2018 |archive-date=12 April 2019 |archive-url=https://web.archive.org/web/20190412122543/https://freedomhouse.org/sites/default/files/FOTN_2016_Full_Report.pdf |url-status=live }}</ref><ref name=FOTN-2017>{{cite web |title=Freedom on the Net 2017 |url=https://freedomhouse.org/sites/default/files/FOTN_2017_Full_Report.pdf |website=Freedom House |date=October 2017 |access-date=25 March 2018 |archive-date=12 April 2019 |archive-url=https://web.archive.org/web/20190412122603/https://freedomhouse.org/sites/default/files/FOTN_2017_Full_Report.pdf |url-status=dead }}</ref><ref name=FOTN-2018/> | ||
| {{cite web |title=Freedom on the Net 2015 |url=https://freedomhouse.org/sites/default/files/FH_FOTN_2015Report.pdf |website=Freedom House |date=October 2015 |accessdate=27 December 2015}}</ref><ref name=FOTN-2016> | |||
| {{cite web |title=Freedom on the Net 2016 |url=https://freedomhouse.org/sites/default/files/FOTN_2016_Full_Report.pdf |website=Freedom House |date=October 2016 |accessdate=25 March 2018}}</ref><ref name=FOTN-2017> | |||
| {{cite web |title=Freedom on the Net 2017 |url=https://freedomhouse.org/sites/default/files/FOTN_2017_Full_Report.pdf |website=Freedom House |date=October 2017 |accessdate=25 March 2018}}</ref><ref name=FOTN-2018/> | |||
| There was no report in 2010. The reports generally cover the period from June through May. | There was no report in 2010. The reports generally cover the period from June through May. | ||
| Line 283: | Line 301: | ||
| |} | |} | ||
| The 2014 report assessed 65 countries and reported that 36 countries experienced a negative trajectory in Internet freedom since the previous year, with the most significant declines in ], ] and ]. According to the report, few countries demonstrated any gains in Internet freedom, and the improvements that were recorded reflected less vigorous application of existing controls rather than new steps taken by governments to actively increase Internet freedom. The year's largest improvement was recorded in ], where restrictions to content and access were relaxed from what had been imposed in 2013 to stifle rioting in the northeastern states. Notable improvement was also recorded in ], where lawmakers approved the bill ], which contains significant provisions governing net neutrality and safeguarding privacy protection.<ref name=FOTN-2014/> | The 2014 report assessed 65 countries and reported that 36 countries experienced a negative trajectory in Internet freedom since the previous year, with the most significant declines in ], ] and ]. According to the report, few countries demonstrated any gains in Internet freedom, and the improvements that were recorded reflected less vigorous application of existing controls rather than new steps taken by governments to actively increase Internet freedom. The year's largest improvement was recorded in ], where restrictions to content and access were relaxed from what had been imposed in 2013 to stifle rioting in the northeastern states. Notable improvement was also recorded in ], where lawmakers approved the bill ], which contains significant provisions governing net neutrality and safeguarding privacy protection.<ref name=FOTN-2014/> | ||
| ====Reporters Without Borders ( |
====Reporters Without Borders (RSF)==== | ||
| =====RWB "Internet enemies" and "countries under surveillance" lists===== | =====RWB "Internet enemies" and "countries under surveillance" lists===== | ||
| In 2006, Reporters without Borders (''Reporters sans frontières'', RSF), a Paris-based international ] that advocates ], started publishing a list of "Enemies of the Internet".<ref name="RSFEnemies2006"> Reporters Without Borders (Paris), 11 July 2006, .</ref> The organization classifies a country as an enemy of the internet because "all of these countries mark themselves out not just for their capacity to censor news and information online but also for their almost systematic repression of Internet users."<ref name="RSFEnemies2009">, Reporters Without Borders (Paris), 12 March 2009, {{webarchive|url=https://web.archive.org/web/20090316065534/http://www.rsf.org/IMG/pdf/Internet_enemies_2009_2_.pdf|date=16 March 2009}}.</ref> In 2007 a second list of countries "Under Surveillance" (originally "Under Watch") was added.<ref name="RSFEnemies2010"> Reporters Without Borders (Paris), 18 March 2010, {{webarchive|url=https://web.archive.org/web/20100314045541/http://www.rsf.org/ennemis.html|date=14 March 2010}}.</ref> | |||
| {{RWB Internet lists}} | |||
| {{Col-begin}} | |||
| {{col-break}}'''Enemies of the Internet:'''<ref name=RWBEnemies2012> {{webarchive|url=https://web.archive.org/web/20120323215225/http://march12.rsf.org/i/Report_EnemiesoftheInternet_2012.pdf |date=2012-03-23 }}, Reporters Without Borders (Paris), 12 March 2012</ref><ref name=RWBEnemies2014>, ''Enemies of the Internet 2014: Entities at the heart of censorship and surveillance'', Reporters Without Borders (Paris), 11 March 2014. {{webarchive|url=https://web.archive.org/web/20140312120731/http://12mars.rsf.org/2014-en/|date=12 March 2014}}. Retrieved 24 June 2014.</ref> | |||
| * {{flag|Bahrain}}: 2012–2014 | |||
| * {{flag|Belarus}}: 2006–2008, 2012–2014 | |||
| * {{flag|Bangladesh}}: 2009–2014 | |||
| * {{flag|China|People's Republic of China}}: 2008–2014 | |||
| * {{flag|Cuba}}: 2006–2014 | |||
| * {{flag|Egypt}}: 2006–2010 | |||
| * {{flag|Ethiopia}}: 2014 | |||
| * {{flag|India}}: 2014 | |||
| * {{flag|Iran}}: 2006–2014 | |||
| * {{flag|Myanmar}}: 2006–2013 | |||
| * {{flag|North Korea}}: 2006–2014 | |||
| * {{flag|Pakistan}}: 2014 | |||
| * {{flag|Russia}}: 2014 | |||
| * {{flag|Saudi Arabia}}: 2006–2014 | |||
| * {{flag|Sudan}}: 2014 | |||
| * {{flag|Syria}}: 2006–2014 | |||
| * {{flag|Tunisia}}: 2006–2010 | |||
| * {{flag|Turkmenistan}}: 2006–2014 | |||
| * {{flag|United Arab Emirates}}: 2014 | |||
| * {{flag|United Kingdom}}: 2014 | |||
| * {{flag|United States}}: 2014 | |||
| * {{flag|Uzbekistan}}: 2006–2014 | |||
| * {{flag|Vietnam}}: 2006–2014 | |||
| {{col-break}}'''Current Countries Under Surveillance:'''<ref name=RWBEnemies2012/>{{not in citation given|date=May 2022}} | |||
| * {{flag|Australia}}: 2009–present | |||
| * {{flag|Bangladesh}}: 2009–present | |||
| * {{flag|Egypt}}: 2011–present | |||
| * {{flag|Eritrea}}: 2008–2009, 2011–present | |||
| * {{flag|France}}: 2011–present | |||
| * {{flag|Kazakhstan}}: 2008–present | |||
| * {{flag|Malaysia}}: 2008–2009, 2011–present | |||
| * {{flag|South Korea}}: 2009–present | |||
| * {{flag|Sri Lanka}}: 2008–2009, 2011–present | |||
| * {{flag|Thailand}}: 2008–present | |||
| * {{flag|Tunisia}}: 2011–present | |||
| * {{flag|Turkey}}: 2010–present | |||
| * {{flag|Norway}}: 2020–present (only the metadata on traffic that crosses Norwegian borders) | |||
| '''Past Countries Under Surveillance:''' | |||
| * {{flag|Bahrain}}: 2008–2009 and 2011 | |||
| * {{flag|Belarus}}: 2009–2011 | |||
| * {{flag|India}}: 2008–13 | |||
| * {{flag|Jordan}}: 2008 | |||
| * {{flag|Libya}}: 2008 and 2011 | |||
| * {{flag|Russia}}: 2010–2013 | |||
| * {{flag|Tajikistan}}: 2008 | |||
| * {{flag|United Arab Emirates}}: 2008–2013 | |||
| * {{flag|Venezuela}}: 2011 | |||
| * {{flag|Yemen}}: 2008–2009 | |||
| {{col-end}} | |||
| When the "Enemies of the Internet" list was introduced in 2006, it listed 13 countries. From 2006 to 2012 the number of countries listed fell to 10 and then rose to 12. The list was not updated in 2013. In 2014 the list grew to 19 with an increased emphasis on ] in addition to censorship. The list has not been updated since 2014. | |||
| When the "Countries under surveillance" list was introduced in 2008, it listed 10 countries. Between 2008 and 2012 the number of countries listed grew to 16 and then fell to 11. The number grew to 12 with the addition of Norway in 2020. The list was last updated in 2020.{{cn|date=May 2022}} | |||
| =====RWB ''Special report on Internet Surveillance''===== | =====RWB ''Special report on Internet Surveillance''===== | ||
| Line 297: | Line 374: | ||
| The five "State Enemies of the Internet" named in March 2013 are: ], ], ], ], and ].<ref name=RSFSRS-March2013/> | The five "State Enemies of the Internet" named in March 2013 are: ], ], ], ], and ].<ref name=RSFSRS-March2013/> | ||
| The five "Corporate Enemies of the Internet" named in March 2013 are: ] (France), ] (U.S.), ] (UK and Germany), ] (Italy), and Trovicor (Germany).<ref name=RSFSRS-March2013/> | The five "Corporate Enemies of the Internet" named in March 2013 are: ] (France), ] (U.S.), ] (UK and Germany), ] (Italy), and Trovicor (Germany).<ref name=RSFSRS-March2013/> | ||
| ==== V-Dem Digital Societies Project ==== | |||
| The V-Dem Digital Societies Project measures a range of questions related to internet censorship, misinformation online, and internet shutdowns.<ref>Mechkova, V., Daniel P., Brigitte S.,&Steven W. (2020). Digital Society Project Dataset v2.Varieties of Democracy (V-Dem) Project http://digitalsocietyproject.org/ {{Webarchive|url=https://web.archive.org/web/20210519024936/http://digitalsocietyproject.org/ |date=19 May 2021 }}</ref> This annual report includes 35 indicators assessing five areas: disinformation, digital media freedom, state regulation of digital media, polarization of online media, and online social cleavages.<ref name=":2">{{Cite book|last1=Mechkova|first1=Valeriya |url=http://digitalsocietyproject.org/wp-content/uploads/2021/04/DSP-Codebook-v3.pdf|title=Digital Society Survey Codebook|last2=Pemstein|first2=Daniel|last3=Seim|first3=Brigitte|last4=Wilson|first4=Steven |publisher=Digital Society Project|year=2021|access-date=27 May 2021|archive-date=27 May 2021|archive-url=https://web.archive.org/web/20210527015848/http://digitalsocietyproject.org/wp-content/uploads/2021/04/DSP-Codebook-v3.pdf|url-status=live}}</ref> The data set uses V-Dem's methodology of aggregating surveys of experts from around the world.<ref name=":2" /> It has been updated each year starting in 2019, with data covering from 2000–2021.<ref name=":2" /> These ratings are more similar to other expert analyses like Freedom House than remotely sensed data from Access Now.<ref name=":3">{{Cite conference|last1=Fletcher|first1=Terry |last2=Hayes-Birchler|first2=Andria|date=2020-07-30|title=Comparing Measures of Internet Censorship: Analyzing the Tradeoffs between Expert Analysis and Remote Measurement |conference=Data for Policy 2020, 15-17 September 2020|doi=10.5281/zenodo.3967398 |s2cid=244992072 |url=https://zenodo.org/record/3967398|access-date=27 May 2021|archive-date=27 May 2021 |archive-url=https://web.archive.org/web/20210527015846/https://zenodo.org/record/3967398|url-status=live}}</ref> | |||
| ==== Access Now #KeepItOn ==== | |||
| Access Now maintains an annual list of internet shutdowns, throttling, and blockages as part of the #KeepItOn project.<ref name=":3" /><ref>Taye, B. (2020). Targeted, Cut Off, and Left in the DarkThe #KeepItOn Report on internet shutdowns in 2019. Access Now. https://www.accessnow.org/keepiton/</ref><ref>{{Cite news|last=Taye|first=Berhan|date=2021|title=Shattered Dreams and Lost Opportunities|work=]|url=https://www.accessnow.org/cms/assets/uploads/2021/03/KeepItOn-report-on-the-2020-data_Mar-2021_3.pdf|access-date=27 May 2021|archive-date=2 June 2021|archive-url=https://web.archive.org/web/20210602120100/https://www.accessnow.org/cms/assets/uploads/2021/03/KeepItOn-report-on-the-2020-data_Mar-2021_3.pdf|url-status=live}}</ref> These data track several features of shutdowns including their location, their duration, the particular services impacted, the government's justification for the shutdown, and actual reasons for the shutdown as reported by independent media.<ref name=":4">{{Cite web|last=Access Now|date=2021|title=STOP Methodology|url=https://www.accessnow.org/cms/assets/uploads/2021/02/Read-Me_-How-to-view-the-Access-Now-Internet-Shutdown-Tracker-Updated-Mar-2021.pdf|website=Access Now|access-date=27 May 2021|archive-date=17 January 2023|archive-url=https://web.archive.org/web/20230117054652/https://www.accessnow.org/cms/assets/uploads/2021/02/Read-Me_-How-to-view-the-Access-Now-Internet-Shutdown-Tracker-Updated-Mar-2021.pdf|url-status=live}}</ref> Unlike Freedom House or V-Dem, Access Now detects shutdowns using ] and then confirms these instances with reports from civil society, government, in-country volunteers, or ISPs.<ref name=":4" /><ref name=":3" /> These methods have been found to be less prone to false positives.<ref name=":3" /> | |||
| ====BBC World Service global public opinion poll==== | ====BBC World Service global public opinion poll==== | ||
| A poll of 27,973 adults in 26 countries, including 14,306 Internet users,<ref>For the BBC poll Internet users are those who used the Internet within the previous six months.</ref> was conducted for the ] by the international polling firm ] using telephone and in-person interviews between 30 November 2009 and 7 February 2010. GlobeScan Chairman Doug Miller felt, overall, that the poll showed that: | A poll of 27,973 adults in 26 countries, including 14,306 Internet users,<ref>For the BBC poll Internet users are those who used the Internet within the previous six months.</ref> was conducted for the ] by the international polling firm ] using telephone and in-person interviews between 30 November 2009 and 7 February 2010. GlobeScan Chairman Doug Miller felt, overall, that the poll showed that: | ||
| :Despite worries about privacy and fraud, people around the world see access to the internet as their fundamental right. They think the web is a force for good, and most |
:Despite worries about privacy and fraud, people around the world see access to the internet as their fundamental right. They think the web is a force for good, and most don't want governments to regulate it.<ref name=BBCPoll-2010> {{Webarchive|url=https://web.archive.org/web/20130601163736/http://news.bbc.co.uk/1/shared/bsp/hi/pdfs/08_03_10_BBC_internet_poll.pdf |date=1 June 2013 }}, BBC World Service, 8 March 2010</ref> | ||
| Findings from the poll include:<ref name=BBCPoll-2010/> | Findings from the poll include:<ref name=BBCPoll-2010/> | ||
| * Nearly four in five (78%) Internet users felt that the Internet had brought them greater freedom. | * Nearly four in five (78%) Internet users felt that the Internet had brought them greater freedom. | ||
| * Most Internet users (53%) felt that "the internet should never be regulated by any level of government anywhere". | * Most Internet users (53%) felt that "the internet should never be regulated by any level of government anywhere". | ||
| * Opinion was evenly split between Internet users who felt that |
* Opinion was evenly split between Internet users who felt that "the internet is a safe place to express my opinions" (48%) and those who disagreed (49%). Users in ] and ] agreed the least, followed by users in a highly filtered country such as ], while users in ], ] and ] agreed more strongly.<ref name=UNESCO-2011/> | ||
| * The aspects of the Internet that cause the most concern include: fraud (32%), violent and explicit content (27%), threats to ] (20%), state censorship of content (6%), and the extent of corporate presence (3%). | * The aspects of the Internet that cause the most concern include: fraud (32%), violent and explicit content (27%), threats to ] (20%), state censorship of content (6%), and the extent of corporate presence (3%). | ||
| * Almost four in five Internet users and non-users around the world felt that access to the Internet was a fundamental right (50% strongly agreed, 29% somewhat agreed, 9% somewhat disagreed, 6% strongly disagreed, and 6% gave no opinion).<ref>, ''BBC News'', 8 March 2010</ref> And while there is strong support for this right in all of the countries surveyed, it is surprising that the United States and Canada were among the top five countries where people most strongly disagreed that access to the Internet was a fundamental right of all people (13% in ], 11% in the ], 11% in ], 11% in ], and 10% in ] strongly disagree).<ref name=UNESCO-2011/> | * Almost four in five Internet users and non-users around the world felt that access to the Internet was a fundamental right (50% strongly agreed, 29% somewhat agreed, 9% somewhat disagreed, 6% strongly disagreed, and 6% gave no opinion).<ref> {{Webarchive|url=https://web.archive.org/web/20120107075123/http://news.bbc.co.uk/2/hi/8548190.stm |date=7 January 2012 }}, ''BBC News'', 8 March 2010</ref> And while there is strong support for this right in all of the countries surveyed, it is surprising that the United States and Canada were among the top five countries where people most strongly disagreed that access to the Internet was a fundamental right of all people (13% in ], 11% in the ], 11% in ], 11% in ], and 10% in ] strongly disagree).<ref name=UNESCO-2011/> | ||
| ====Internet Society's Global Internet User Survey==== | ====Internet Society's Global Internet User Survey==== | ||
| In July and August 2012 the ] conducted online interviews of more than 10,000 Internet users in 20 countries. Some of the results relevant to Internet censorship are summarized below.<ref> {{webarchive|url=https://web.archive.org/web/20130314063616/https://www.internetsociety.org/sites/default/files/GIUS2012-GlobalData-Table-20121120_0.pdf |date=14 March 2013 }}, Internet Society, 20 November 2012</ref> | In July and August 2012, the ] conducted online interviews of more than 10,000 Internet users in 20 countries. Some of the results relevant to Internet censorship are summarized below.<ref> {{webarchive|url=https://web.archive.org/web/20130314063616/https://www.internetsociety.org/sites/default/files/GIUS2012-GlobalData-Table-20121120_0.pdf |date=14 March 2013 }}, Internet Society, 20 November 2012</ref> | ||
| {{sticky header}} | |||
| {| class= "wikitable" | {| class= "wikitable sticky-header" | ||
| |- | |- | ||
| ! width="50%" | Question | ! width="50%" | Question | ||
| Line 337: | Line 420: | ||
| | Each individual country has the right to govern the Internet the way they see fit. | | Each individual country has the right to govern the Internet the way they see fit. | ||
| | align="center" | 10,789 | | align="center" | 10,789 | ||
| | 67% somewhat or strongly agree,<br />29% somewhat or strongly disagree,<br /> 4% don't know /not applicable | | 67% somewhat or strongly agree,<br />29% somewhat or strongly disagree,<br /> 4% don't know / not applicable | ||
| |- | |- | ||
| | The Internet does more to help society than it does to hurt it. | | The Internet does more to help society than it does to hurt it. | ||
| Line 351: | Line 434: | ||
| | 27% all the time,<br />36% most of the time,<br />29% sometimes,<br /> 9% never | | 27% all the time,<br />36% most of the time,<br />29% sometimes,<br /> 9% never | ||
| |- | |- | ||
| | Do you use |
| Do you use "anonymization" services, for example, the "anonymize" feature in your web browser, specialized software like Tor, third - party redirection services like duckduckgo.com? | ||
| | align="center" | 10,789 | | align="center" | 10,789 | ||
| | 16% yes,<br />38% no,<br />43% don't know / not aware of these types of services,<br /> 3% would like to use them but I am not able to | | 16% yes,<br />38% no,<br />43% don't know / not aware of these types of services,<br /> 3% would like to use them but I am not able to | ||
| Line 382: | Line 465: | ||
| ===Transparency of filtering or blocking activities=== | ===Transparency of filtering or blocking activities=== | ||
| Among the countries that filter or block online content, few openly admit to or fully disclose their filtering and blocking activities. States are frequently opaque and/or deceptive about the blocking of access to political information.<ref name=Chadwick-2009/> For example: | Among the countries that filter or block online content, few openly admit to or fully disclose their filtering and blocking activities. States are frequently opaque and/or deceptive about the blocking of access to political information.<ref name=Chadwick-2009/> For example: | ||
| * ] and the ] (UAE) are among the few states that publish detailed information about their filtering practices and display a notification to the user when attempting to access a blocked website. The websites that are blocked are mostly ] or considered un-Islamic. | * ] and the ] (UAE) are among the few states that publish detailed information about their filtering practices and display a notification to the user when attempting to access a blocked website. The websites that are blocked are mostly ] or considered un-Islamic. | ||
| * In contrast, countries such as ] and ] send users a false error indication. China blocks requests by users for a banned website at the ] and a connection error is returned, effectively preventing the user's ] from making further ] requests for a varying time, which appears to the user as "time-out" error with no explanation. Tunisia has altered the block page functionality of ], the commercial filtering software it uses, so that users attempting to access blocked websites receive a fake "File not found" error page. | * In contrast, countries such as ] and ] send users a false error indication. China blocks requests by users for a banned website at the ] and a connection error is returned, effectively preventing the user's ] from making further ] requests for a varying time, which appears to the user as "time-out" error with no explanation. Tunisia has altered the block page functionality of ], the commercial filtering software it uses, so that users attempting to access blocked websites receive a fake "File not found" error page. | ||
| * In ] users are frequently sent block pages stating that the website is blocked because of pornography, even when the page contains no pornography. Uzbeki ISPs may also redirect users' request for blocked websites to unrelated websites, or sites similar to the banned websites, but with different information.<ref>{{Cite book| last = |
* In ], users are frequently sent block pages stating that the website is blocked because of pornography, even when the page contains no pornography. Uzbeki ISPs may also redirect users' request for blocked websites to unrelated websites, or sites similar to the banned websites, but with different information.<ref>{{Cite book| last = Chadwick| first = Andrew| title = Routledge handbook of Internet politics| publisher = Taylor and Francis| series = Routledge international handbooks| year = 2009| page = 331 | url = https://books.google.com/books?id=GJdfuGSa1xUC| isbn = 978-0-415-42914-6}}</ref> | ||
| ===Arab Spring=== | ===Arab Spring=== | ||
| {{See also|Internet censorship in the Arab Spring|Internet in Egypt#2011 Internet shutdown|Free speech in the media during the Libyan civil war (2011)}} | |||
| During the ] of 2011, media ] (media struggle) was extensive. Internet and mobile technologies, particularly social networks such as Facebook and Twitter, played and are playing important new and unique roles in organizing and spreading the protests and making them visible to the rest of the world. An activist in Egypt tweeted, |
During the ] of 2011, media ] (media struggle) was extensive. Internet and mobile technologies, particularly social networks such as Facebook and Twitter, played and are playing important new and unique roles in organizing and spreading the protests and making them visible to the rest of the world. An activist in Egypt tweeted, "we use Facebook to schedule the protests, Twitter to coordinate, and YouTube to tell the world".<ref> {{webarchive|url=https://web.archive.org/web/20110227051329/http://www.miller-mccune.com/politics/the-cascading-effects-of-the-arab-spring-28575/ |date=27 February 2011 }}, Philip N. Howard, Miller-McCune, 23 February 2011</ref> | ||
| This successful use of digital media in turn led to increased censorship including the complete loss of Internet access for periods of time in Egypt<ref name="jamescowie_techdetails_Egyptfullblock"/><ref name="IDGnews_Egyptfullblock"/><ref>, Craig Labovitz, Arbor Networks</ref> and ] in 2011.<ref name=Libya-RWB-2011/><ref name="Analysis of Egyptian and Libyan outages">{{cite web| url=http://www.caida.org/publications/papers/2011/outages_censorship/outages_censorship.pdf| title=Analysis of Country-wide Internet Outages Caused by Censorship|last=Dainotti|year=2011| publisher=ACM|display-authors=etal}}</ref> In Syria, the Syrian Electronic Army (SEA), an organization that operates with at least tacit support of the government, claims responsibility for defacing or otherwise compromising scores of websites that it contends spread news hostile to the Syrian government. SEA disseminates denial of service (DoS) software designed to target media websites including those of ], ], Syrian satellite broadcaster ], and Dubai-based ] TV.<ref>, OpenNet Initiative, 25 June 2011</ref> | This successful use of digital media in turn led to increased censorship including the complete loss of Internet access for periods of time in Egypt<ref name="jamescowie_techdetails_Egyptfullblock"/><ref name="IDGnews_Egyptfullblock"/><ref> {{Webarchive|url=https://web.archive.org/web/20110225204810/http://monkey.org/~labovit/blog/viewpage.php?page=middle_east_scorecard_feb20 |date=25 February 2011 }}, Craig Labovitz, Arbor Networks</ref> and ] in 2011.<ref name=Libya-RWB-2011/><ref name="Analysis of Egyptian and Libyan outages">{{cite web| url=http://www.caida.org/publications/papers/2011/outages_censorship/outages_censorship.pdf| title=Analysis of Country-wide Internet Outages Caused by Censorship| last=Dainotti| year=2011| publisher=ACM| display-authors=etal| access-date=14 April 2012| archive-date=17 June 2012| archive-url=https://web.archive.org/web/20120617034714/http://www.caida.org/publications/papers/2011/outages_censorship/outages_censorship.pdf| url-status=live}}</ref> In Syria, the Syrian Electronic Army (SEA), an organization that operates with at least tacit support of the government, claims responsibility for defacing or otherwise compromising scores of websites that it contends spread news hostile to the Syrian government. SEA disseminates denial of service (DoS) software designed to target media websites including those of ], ], Syrian satellite broadcaster ], and Dubai-based ] TV.<ref> {{Webarchive|url=https://web.archive.org/web/20180720171155/https://opennet.net/syrian-electronic-army-disruptive-attacks-and-hyped-targets |date=20 July 2018 }}, OpenNet Initiative, 25 June 2011</ref> | ||
| In response to the greater freedom of expression brought about by the Arab Spring revolutions in countries that were previously subject to very strict censorship, in March 2011, Reporters Without Borders moved ] and ] from its "Internet enemies" list to its list of countries "under surveillance"<ref> {{webarchive|url=https://web.archive.org/web/20160304060153/http://en.rsf.org/surveillance-egypt,39740.html |date=4 March 2016 }}, Reporters Without Borders, March 2011</ref> and in 2012 dropped ] from the list entirely.<ref name=RWBEnemies2012/><!-- defined by template:RWB Internet lists --> At the same time, there were warnings that Internet censorship might increase in other countries following the events of the Arab Spring.<ref> {{webarchive|url=https://web.archive.org/web/20120126060054/http://www.future500.org/blog/censorship-fallout-from-the-arab-spring/ |date=26 January 2012 }}, Juliette Terzieff, The Future 500, 29 June 2011</ref><ref>, Peter Apps, Reuters Canada, 28 September 2011</ref> However, in 2013, Libyan communication company ] blocked the pornographic websites.<ref> |
In response to the greater freedom of expression brought about by the Arab Spring revolutions in countries that were previously subject to very strict censorship, in March 2011, Reporters Without Borders moved ] and ] from its "Internet enemies" list to its list of countries "under surveillance"<ref> {{webarchive|url=https://web.archive.org/web/20160304060153/http://en.rsf.org/surveillance-egypt,39740.html |date=4 March 2016 }}, Reporters Without Borders, March 2011</ref> and in 2012 dropped ] from the list entirely.<ref name=RWBEnemies2012/><!-- defined by template:RWB Internet lists --> At the same time, there were warnings that Internet censorship might increase in other countries following the events of the Arab Spring.<ref> {{webarchive|url=https://web.archive.org/web/20120126060054/http://www.future500.org/blog/censorship-fallout-from-the-arab-spring/ |date=26 January 2012 }}, Juliette Terzieff, The Future 500, 29 June 2011</ref><ref> {{Webarchive|url=https://web.archive.org/web/20111106132945/http://ca.reuters.com/article/technologyNews/idCATRE78R3CM20110928?pageNumber=1&virtualBrandChannel=0 |date=6 November 2011 }}, Peter Apps, Reuters Canada, 28 September 2011</ref> However, in 2013, Libyan communication company ] blocked the pornographic websites.<ref>{{Cite web|url=https://www.libya-businessnews.com/2013/09/13/ltt-blocks-pornographic-websites/|title=LTT Blocks Pornographic Websites|date=13 September 2013|access-date=10 August 2017|archive-date=11 August 2017|archive-url=https://web.archive.org/web/20170811010930/https://www.libya-businessnews.com/2013/09/13/ltt-blocks-pornographic-websites/|url-status=live}}</ref> It even blocked the family-filtered videos of ordinary websites like ].<ref>{{Cite journal|last=Shishkina|first=Alisa|date=November 2018|title=Internet Censorship in Arab Countries: Religious and Moral Aspects|journal=Religions|volume=9|issue=11|pages=358|doi=10.3390/rel9110358|doi-access=free}}</ref> | ||
| ===Russian invasion of Ukraine=== | |||
| During the ] in 2022, Russia was reported to have blocked the internet websites ] and ]. Facebook was noted as being suspended due to an objection to its policy of reviewing news stories for authenticity where they were produced by Russian state-backed media before allowing them to be published on its platform. It was subject to a total ban whereas Twitter was suspended regionally. Reports have identified that ] use has enabled people to circumvent the restrictions by installing software.<ref>{{Cite news |date=2022-02-26 |title=Ukraine invasion: Russia restricts social media access |language=en-GB |work=BBC News |url=https://www.bbc.com/news/technology-60533083 |access-date=2022-02-26 |archive-date=2 March 2022 |archive-url=https://web.archive.org/web/20220302202156/https://www.bbc.com/news/technology-60533083 |url-status=live }}</ref> | |||
| It been reported that the ] would seek to censor Russian media outlets regarded as producing propaganda.{{cn|date=March 2022}} | |||
| ==See also== | ==See also== | ||
| {{Col begin}} | {{Col begin}} | ||
| {{Col-1-of-2}} | {{Col-1-of-2}} | ||
| '''Organizations and projects''' |
'''Organizations and projects''' | ||
| * ] – an online hacktivist collective that express its opposition to Internet censorship through protests and online hacking in several countries. | * ] – an online hacktivist collective that express its opposition to Internet censorship through protests and online hacking in several countries. | ||
| * ] (Cospol Internet Related Child Abusive Material Project) – a project of the European Chiefs of Police Task Force to combat commercial and organized distribution of ] | * ] (Cospol Internet Related Child Abusive Material Project) – a project of the European Chiefs of Police Task Force to combat commercial and organized distribution of ] | ||
| * The ] project – a European Union-funded project with the stated aim of suppressing terrorist activity | * The ] – a European Union-funded project with the stated aim of suppressing terrorist activity | ||
| * ] – an international non-profit digital rights advocacy and legal organization | * ] – an international non-profit digital rights advocacy and legal organization | ||
| * ] – a coalition of credit card issuers and Internet services companies that seeks to eliminate commercial child pornography by taking action on the payment systems that fund these operations | * ] – a coalition of credit card issuers and Internet services companies that seeks to eliminate commercial child pornography by taking action on the payment systems that fund these operations | ||
| * ] – a U.S.-based non-profit that produces the ''Freedom on the Net'' reports, among others. | * ] – a U.S.-based non-profit that produces the ''Freedom on the Net'' reports, among others. | ||
| * ] (GIFC) – a consortium of organizations that develop and deploy anti-censorship technologies | * ] (GIFC) – a consortium of organizations that develop and deploy anti-censorship technologies | ||
| * ] (GIFT) – an initiative within the ] | * ] (GIFT) – an initiative within the ] | ||
| * ] |
* ] – a global network of non-governmental organizations that promotes and defends the right to freedom of expression | ||
| ** ] – a coalition within IFEX that monitors free expression in Tunisia | ** ] – a coalition within IFEX that monitors free expression in Tunisia | ||
| * ] (IGF) – a United Nations multi-stakeholder policy dialogue initiative | * ] (IGF) – a United Nations multi-stakeholder policy dialogue initiative | ||
| * ] – a government-supported charity that manages the blacklist used by UK ISPs to block access to websites hosting child abuse content | * ] – a government-supported charity that manages the blacklist used by UK ISPs to block access to websites hosting child abuse content | ||
| * ] (formerly Chilling Effects) – a joint project of the Electronic Frontier Foundation and several U.S. university law schools and clinics | * ] (formerly Chilling Effects) – a joint project of the Electronic Frontier Foundation and several U.S. university law schools and clinics | ||
| * ] - a global watchdog organization that monitors cybersecurity and the ] | |||
| * ] - a free software, global observation network created to detect censorship, surveillance and traffic manipulation on the internet | |||
| * ] (OTF) – a U.S. Government funded program created in 2012 at Radio Free Asia to support global Internet freedom technologies | * ] (OTF) – a U.S. Government funded program created in 2012 at Radio Free Asia to support global Internet freedom technologies | ||
| * ] – a joint project to monitor and report on Internet filtering and surveillance practices by nations | * ] – a joint project to monitor and report on Internet filtering and surveillance practices by nations | ||
| * ] – a U.S.-based website dedicated to "preserving First Amendment rights for Internet users, particularly those younger than 18" | * ] – a U.S.-based website dedicated to "preserving First Amendment rights for Internet users, particularly those younger than 18" | ||
| * ] – a political movement that aims to reform laws regarding ] and patents, strengthen the ], and increase the ] | * ] – a political movement that aims to reform laws regarding ] and patents, strengthen the ], and increase the ] | ||
| * '']'' (]) – a France-based international non-governmental organization that advocates freedom of the press | * '']'' (]) – a France-based international non-governmental organization that advocates freedom of the press | ||
| {{Col-2-of-2}} | {{Col-2-of-2}} | ||
| {{Misplaced Pages books|Internet}} | |||
| {{Portal|Internet|Freedom of speech}} | {{Portal|Internet|Freedom of speech}} | ||
| '''Topics''' |
'''Topics''' | ||
| * ] | * ] | ||
| * ] | |||
| * ] – a technical measure intended to restrict access to information or resources | * ] – a technical measure intended to restrict access to information or resources | ||
| * ] – a content blocking system in use in the UK and Canada | * ] – a content blocking system in use in the UK and Canada | ||
| * ] | * ] | ||
| * ] | * ] | ||
| * ] | |||
| * ] | |||
| * ] | * ] | ||
| * ] – a 2003 article about Internet censorship and ] by ], co-founder of the ] software company ] | * ] – a 2003 article about Internet censorship and ] by ], co-founder of the ] software company ] | ||
| * ] | * ] | ||
| * ] | |||
| * ] | |||
| * ] | * ] | ||
| * ] | |||
| * ] | * ] | ||
| * ] | * ] | ||
| * ] of Iran | |||
| ** ] | |||
| * ] | * ] | ||
| * Laws and proposed laws: | * Laws and proposed laws: | ||
| ** ] by country | ** ] by country | ||
| ** ] (ACTA) – multinational treaty | ** ] (ACTA) – multinational treaty | ||
| ** ] – a US law ruled unconstitutional | ** ] – a US law ruled unconstitutional | ||
| *** ] | *** ] | ||
| ** ] (DMCA) – a US law | ** ] (DMCA) – a US law | ||
| ** ] |
** ] | ||
| ** ] – New Zealand | ** ] – New Zealand | ||
| *** ] | *** ] | ||
| Line 458: | Line 551: | ||
| * ] | * ] | ||
| * ] | * ] | ||
| * ] | * ] | ||
| * ] | * ] | ||
| * ] | * ] | ||
| * ] | * ] | ||
| * ] | |||
| * ] | * ] | ||
| {{Col end}} | {{Col end}} | ||
| ==References== | ==References== | ||
| ] ''This article incorporates ] from the ] web site.<ref>] ], see the lower right corner of pages at the </ref>'' | |||
| {{Reflist|30em|refs= | {{Reflist|30em|refs= | ||
| <ref name="Guardian 5 December 2014">Marcello Mari. . '']''. Friday 5 December 2014.</ref> | <ref name="Guardian 5 December 2014">Marcello Mari. {{Webarchive|url=https://web.archive.org/web/20160610180205/https://www.theguardian.com/technology/2014/dec/05/how-faceboook-tor-service-encourage-open-web |date=10 June 2016 }}. '']''. Friday 5 December 2014.</ref> | ||
| }} | }} | ||
| ==Sources== | |||
| * ] ''This article incorporates ] from the ] web site.<ref>] ], see the lower right corner of pages at the {{Webarchive|url=https://web.archive.org/web/20180925044301/http://opennet.net/ |date=25 September 2018 }}</ref>'' | |||
| ==Further reading== | |||
| * King Gary, Pan, Jennifer, & Robert, Margaret. (2013). "]" American Political Science Review, 107(2), 326–343. | |||
| ==External links== | ==External links== | ||
| {{Commons category}} | {{Commons category-inline}} | ||
| * , an anti-censorship site that catalogs past and present censored works, using verifiable sources, and a forum to discuss organizing against and circumventing censorship. | * , an anti-censorship site that catalogs past and present censored works, using verifiable sources, and a forum to discuss organizing against and circumventing censorship. | ||
| * , |
* , website of ], a London-based organization and magazine that promotes freedom of expression. | ||
| * |
* ({{web archive|url=https://web.archive.org/web/20170607114422/https://en.cship.org/Main_Page|date=2017-06-07}}) provided information about different methods of access filtering and ways to bypass them. | ||
| * , We Fight Censorship project of ]. | * , We Fight Censorship project of ]. | ||
| * by the ], Vienna, 2004. | * by the ], Vienna, 2004. | ||
| * , also known by the titles: ''Bypassing Internet Censorship'' or ''Circumvention Tools'', a ] Manual, 10 March 2011, 240 pp. | * , also known by the titles: ''Bypassing Internet Censorship'' or ''Circumvention Tools'', a ] Manual, 10 March 2011, 240 pp. | ||
| * {{cite web|url= https://www.thesslstore.com/blog/wikipedia-https-censorship|author1= V. Lynch|title= A New Harvard Study Found a Decrease In Censorship Following Misplaced Pages's Migration to HTTPS in 2015|date= Jun 2, 2017|language= en|access-date= Aug 8, 2018|archive-url= https://web.archive.org/web/20180808121223/https://www.thesslstore.com/blog/wikipedia-https-censorship|archive-date= 8 August 2018|deadurl= no}} | |||
| {{Censorship}} | {{Censorship}} | ||
| Line 487: | Line 584: | ||
| {{Media manipulation}} | {{Media manipulation}} | ||
| {{Internet censorship circumvention technologies}} | {{Internet censorship circumvention technologies}} | ||
| {{Authority control}} | |||
| {{Use dmy dates|date=November 2012}} | |||
| ] | ] | ||
Latest revision as of 13:37, 18 December 2024
Legal control of the internet
| Internet |
|---|
 An Opte Project visualization of routing paths through a portion of the Internet An Opte Project visualization of routing paths through a portion of the Internet |
| General |
| Governance |
| Information infrastructure |
| Services |
| History |
| Guides |
|
|
Internet censorship is the legal control or suppression of what can be accessed, published, or viewed on the Internet. Censorship is most often applied to specific internet domains (such as Misplaced Pages.org, for example) but exceptionally may extend to all Internet resources located outside the jurisdiction of the censoring state. Internet censorship may also put restrictions on what information can be made internet accessible. Organizations providing internet access – such as schools and libraries – may choose to preclude access to material that they consider undesirable, offensive, age-inappropriate or even illegal, and regard this as ethical behavior rather than censorship. Individuals and organizations may engage in self-censorship of material they publish, for moral, religious, or business reasons, to conform to societal norms, political views, due to intimidation, or out of fear of legal or other consequences.
The extent of Internet censorship varies on a country-to-country basis. While some countries have moderate Internet censorship, other countries go as far as to limit the access of information such as news and suppress and silence discussion among citizens. Internet censorship also occurs in response to or in anticipation of events such as elections, protests, and riots. An example is the increased censorship due to the events of the Arab Spring. Other types of censorship include the use of copyrights, defamation, harassment, and various obscene material claims as a way to deliberately suppress content.
Support for and opposition to Internet censorship also varies. In a 2012 Internet Society survey, 71% of respondents agreed that "censorship should exist in some form on the Internet". In the same survey, 83% agreed that "access to the Internet should be considered a basic human right" and 86% agreed that "freedom of expression should be guaranteed on the Internet". Perception of internet censorship in the US is largely based on the First Amendment and the right for expansive free speech and access to content without regard to the consequences. According to GlobalWebIndex, over 400 million people use virtual private networks to circumvent censorship or for increased user privacy.
Overview
Many of the challenges associated with Internet censorship are similar to those for offline censorship of more traditional media such as newspapers, magazines, books, music, radio, television, and film. One difference is that national borders are more permeable online: residents of a country that bans certain information can find it on websites hosted outside the country. Thus censors must work to prevent access to information even though they lack physical or legal control over the websites themselves. This in turn requires the use of technical censorship methods that are unique to the Internet, such as site blocking and content filtering.
Views about the feasibility and effectiveness of Internet censorship have evolved in parallel with the development of the Internet and censorship technologies:
- A 1993 Time Magazine article quotes computer scientist John Gilmore, one of the founders of the Electronic Frontier Foundation, as saying "The Net interprets censorship as damage and routes around it."
- In November 2007, "Father of the Internet" Vint Cerf stated that he sees government control of the Internet failing because the Web is almost entirely privately owned.
- A report of research conducted in 2007 and published in 2009 by the Berkman Klein Center for Internet & Society at Harvard University stated that: "We are confident that the [censorship circumvention] tool developers will for the most part keep ahead of the governments' blocking efforts", but also that "...we believe that less than two percent of all filtered Internet users use circumvention tools."
- In contrast, a 2011 report by researchers at the Oxford Internet Institute published by UNESCO concludes "... the control of information on the Internet and Web is certainly feasible, and technological advances do not therefore guarantee greater freedom of speech."
Blocking and filtering can be based on relatively static blacklists or be determined more dynamically based on a real-time examination of the information being exchanged. Blacklists may be produced manually or automatically and are often not available to non-customers of the blocking software. Blocking or filtering can be done at a centralized national level, at a decentralized sub-national level, or at an institutional level, e.g., in libraries, universities or Internet cafés. Blocking and filtering may also vary within a country across different ISPs. Countries may filter sensitive content on an ongoing basis and/or introduce temporary filtering during key time periods such as elections. In some cases, the censoring authorities may surreptitiously block content to mislead the public into believing that censorship has not been applied. This is achieved by returning a fake "Not Found" error message when an attempt is made to access a blocked website.
Unless the censor has total control over all Internet-connected computers, such as in North Korea (who employs an intranet that only privileged citizens can access), or Cuba, total censorship of information is very difficult or impossible to achieve due to the underlying distributed technology of the Internet. Pseudonymity and data havens (such as Hyphanet) protect free speech using technologies that guarantee material cannot be removed and prevents the identification of authors. Technologically savvy users can often find ways to access blocked content. Nevertheless, blocking remains an effective means of limiting access to sensitive information for most users when censors, such as those in China, are able to devote significant resources to building and maintaining a comprehensive censorship system.
The term "splinternet" is sometimes used to describe the effects of national firewalls. The verb "rivercrab" colloquially refers to censorship of the Internet, particularly in Asia.
Content suppression methods
Technical censorship
Various parties are using different technical methods of preventing public access to undesirable resources, with varying levels of effectiveness, costs and side effects.
Blacklist
Entities mandating and implementing the censorship usually identify them by one of the following items: keywords, domain names and IP addresses. Lists are populated from different sources, ranging from private supplier through courts to specialized government agencies (Ministry of Industry and Information Technology of China, Islamic Guidance in Iran).
As per Hoffmann, different methods are used to block certain websites or pages including DNS spoofing, blocking access to IPs, analyzing and filtering URLs, inspecting filter packets and resetting connections.
Points of control
Enforcement of the censor-nominated technologies can be applied at various levels of countries and Internet infrastructure:
- Internet backbone, including Internet exchange points (IXP) with international networks (Autonomous Systems), operators of submarine communications cables, satellite Internet access points, international optical fibre links etc. In addition to facing huge performance challenges due to large bandwidths involved, these do not give censors access to information exchanged within the country.
- Internet Service Providers, which involves installation of voluntary (such as in the UK) or mandatory (such as in Russia) Internet surveillance and blocking equipment.
- Individual institutions, which in most cases implement some form of Internet access controls to enforce their own policies, but, especially in case of public or educational institutions, may be requested or coerced to do this on the request from the government.
- Personal devices, whose manufacturers or vendors may be required by law to install censorship software.
- Application service providers (e.g. social media companies), who may be legally required to remove particular content. Foreign providers with business presence in given country may be also coerced into restricting access to specific contents for visitors from the requesting country.
- Certificate authorities may be required to issue counterfeit X.509 certificates controlled by the government, allowing man-in-the-middle surveillance of TLS encrypted connections.
- Content Delivery Network providers who tend to aggregate large amounts of content (e.g. images) may be also an attractive target for censorship authorities.
Approaches
Internet content is subject to technical censorship methods, including:
- Internet Protocol (IP) address blocking: Access to a certain IP address is denied. If the target Web site is hosted in a shared hosting server, all websites on the same server will be blocked. This affects IP-based protocols such as HTTP, FTP and POP. A typical circumvention method is to find proxies that have access to the target websites, but proxies may be jammed or blocked, and some Web sites, such as Misplaced Pages (when editing), also block proxies. Some large websites such as Google have allocated additional IP addresses to circumvent the block, but later the block was extended to cover the new addresses. Due to challenges with geopositioning, geo-blocking is normally implemented via IP address blocking.
- Domain name system (DNS) filtering and redirection: Connections to blocked domain names are not resolved, or an incorrect IP address is returned via DNS hijacking or other means. This affects all IP-based protocols such as HTTP, FTP and POP. A typical circumvention method is to find an alternative DNS resolver that resolves domain names correctly, but domain name servers are subject to blockage as well, especially IP address blocking. Another workaround is to bypass DNS if the IP address is obtainable from other sources and is not itself blocked. Examples are modifying the Hosts file or typing the IP address instead of the domain name as part of a URL given to a Web browser.
- Uniform Resource Locator (URL) filtering: URL strings are scanned for target keywords regardless of the domain name specified in the URL. This affects the HTTP protocol. Typical circumvention methods are to use escaped characters in the URL, or to use encrypted protocols such as VPN and TLS/SSL.
- Packet filtering: Terminate TCP packet transmissions when a certain number of controversial keywords are detected. This affects all TCP-based protocols such as HTTP, FTP and POP, but Search engine results pages are more likely to be censored. Typical circumvention methods are to use encrypted connections – such as VPN and TLS/SSL – to escape the HTML content, or by reducing the TCP/IP stack's MTU/MSS to reduce the amount of text contained in a given packet.
- Connection reset: If a previous TCP connection is blocked by the filter, future connection attempts from both sides can also be blocked for some variable amount of time. Depending on the location of the block, other users or websites may also be blocked, if the communication is routed through the blocking location. A circumvention method is to ignore the reset packet sent by the firewall.
- Network disconnection: A technically simpler method of Internet censorship is to completely cut off all routers, either by software or by hardware (turning off machines, pulling out cables). A circumvention method could be to use a satellite ISP to access Internet.
- Portal censorship and search result removal: Major portals, including search engines, may exclude web sites that they would ordinarily include. This renders a site invisible to people who do not know where to find it. When a major portal does this, it has a similar effect to censorship. Sometimes this exclusion is done to satisfy a legal or other requirement, other times it is purely at the discretion of the portal. For example, Google.de and Google.fr remove Neo-Nazi and other listings in compliance with German and French law.
- Computer network attacks: Denial-of-service attacks and attacks that deface opposition websites can produce the same result as other blocking techniques, preventing or limiting access to certain websites or other online services, although only for a limited period of time. This technique might be used during the lead up to an election or some other sensitive period. It is more frequently used by non-state actors seeking to disrupt services.
Over and under blocking
Technical censorship techniques are subject to both over- and under-blocking since it is often impossible to always block exactly the targeted content without blocking other permissible material or allowing some access to targeted material and so providing more or less protection than desired. An example is blocking an IP-address of a server that hosts multiple websites, which prevents access to all of the websites rather than just those that contain content deemed offensive.
Use of commercial filtering software
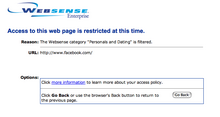
Writing in 2009, Ronald Deibert, professor of political science at the University of Toronto and co-founder and one of the principal investigators of the OpenNet Initiative, and, writing in 2011, Evgeny Morzov, a visiting scholar at Stanford University and an op-ed contributor to The New York Times, explain that companies in the United States, Finland, France, Germany, Britain, Canada, and South Africa are in part responsible for the increasing sophistication of online content filtering worldwide. While the off-the-shelf filtering software sold by Internet security companies are primarily marketed to businesses and individuals seeking to protect themselves and their employees and families, they are also used by governments to block what they consider sensitive content.
Among the most popular filtering software programs is SmartFilter by Secure Computing in California, which was bought by McAfee in 2008. SmartFilter has been used by Tunisia, Saudi Arabia, Sudan, the UAE, Kuwait, Bahrain, Iran, and Oman, as well as the United States and the UK. Myanmar and Yemen have used filtering software from Websense. The Canadian-made commercial filter Netsweeper is used in Qatar, the UAE, and Yemen. The Canadian organization CitizenLab has reported that Sandvine and Procera products are used in Turkey and Egypt.
On 12 March 2013, in a Special Report on Internet Surveillance, Reporters Without Borders named five "Corporate Enemies of the Internet": Amesys (France), Blue Coat Systems (U.S.), Gamma (UK and Germany), HackingTeam (Italy), and Trovicor (Germany). The companies sell products that are liable to be used by governments to violate human rights and freedom of information. RWB said that the list is not exhaustive and will be expanded in the coming months.
In a U.S. lawsuit filed in May 2011, Cisco is accused of helping the Chinese government build a firewall, known widely as the Golden Shield, to censor the Internet and keep tabs on dissidents. Cisco said it had made nothing special for China. Cisco is also accused of aiding the Chinese government in monitoring and apprehending members of the banned Falun Gong group.
Many filtering programs allow blocking to be configured based on dozens of categories and sub-categories such as these from Websense: "abortion" (pro-life, pro-choice), "adult material" (adult content, lingerie and swimsuit, nudity, sex, sex education), "advocacy groups" (sites that promote change or reform in public policy, public opinion, social practice, economic activities, and relationships), "drugs" (abused drugs, marijuana, prescribed medications, supplements and unregulated compounds), "religion" (non-traditional religions occult and folklore, traditional religions), .... The blocking categories used by the filtering programs may contain errors leading to the unintended blocking of websites. The blocking of Dailymotion in early 2007 by Tunisian authorities was, according to the OpenNet Initiative, due to Secure Computing wrongly categorizing Dailymotion as pornography for its SmartFilter filtering software. It was initially thought that Tunisia had blocked Dailymotion due to satirical videos about human rights violations in Tunisia, but after Secure Computing corrected the mistake access to Dailymotion was gradually restored in Tunisia.
Organizations such as the Global Network Initiative, the Electronic Frontier Foundation, Amnesty International, and the American Civil Liberties Union have successfully lobbied some vendors such as Websense to make changes to their software, to refrain from doing business with repressive governments, and to educate schools who have inadvertently reconfigured their filtering software too strictly. Nevertheless, regulations and accountability related to the use of commercial filters and services are often non-existent, and there is relatively little oversight from civil society or other independent groups. Vendors often consider information about what sites and content is blocked valuable intellectual property that is not made available outside the company, sometimes not even to the organizations purchasing the filters. Thus by relying upon out-of-the-box filtering systems, the detailed task of deciding what is or is not acceptable speech may be outsourced to the commercial vendors.
Non-technical censorship
Main article: Censorship
Internet content is also subject to censorship methods similar to those used with more traditional media. For example:
- Laws and regulations may prohibit various types of content and/or require that content be removed or blocked either proactively or in response to requests.
- Publishers, authors, and ISPs may receive formal and informal requests to remove, alter, slant, or block access to specific sites or content.
- Publishers and authors may accept bribes to include, withdraw, or slant the information they present.
- Publishers, authors, and ISPs may be subject to arrest, criminal prosecution, fines, and imprisonment.
- Publishers, authors, and ISPs may be subject to civil lawsuits.
- Equipment may be confiscated and/or destroyed.
- Publishers and ISPs may be closed or required licenses may be withheld or revoked.
- Publishers, authors, and ISPs may be subject to boycotts.
- Publishers, authors, and their families may be subject to threats, attacks, beatings, and even murder.
- Publishers, authors, and their families may be threatened with or actually lose their jobs.
- Individuals may be paid to write articles and comments in support of particular positions or attacking opposition positions, usually without acknowledging the payments to readers and viewers.
- Censors may create their own online publications and Web sites to guide online opinion.
- Access to the Internet may be limited due to restrictive licensing policies or high costs.
- Access to the Internet may be limited due to a lack of the necessary infrastructure, deliberate or not.
- Access to search results may be restricted due to government involvement in the censorship of specific search terms, content may be excluded due to terms set with search engines. By allowing search engines to operate in new territory they must agree to abide to censorship standards set by the government in that country.
Censorship of users by web service operators
Removal of user accounts based on controversial content
Main article: DeplatformingDeplatforming is a form of Internet censorship in which controversial speakers or speech are suspended, banned, or otherwise shut down by social media platforms and other service providers that generally provide a venue for free speech or expression. Banking and financial service providers, among other companies, have also denied services to controversial activists or organizations, a practice known as "financial deplatforming".
Law professor Glenn Reynolds dubbed 2018 the "Year of Deplatforming", in an August 2018 article in The Wall Street Journal. According to Reynolds, in 2018 "the internet giants decided to slam the gates on a number of people and ideas they don't like." On 6 August 2018, for example, several major platforms, including YouTube and Facebook, executed a coordinated, permanent ban on all accounts and media associated with conservative talk show host Alex Jones and his media platform InfoWars, citing "hate speech" and "glorifying violence."
Official statements regarding site and content removal
See also: Twitter suspensions and Terms of serviceMost major web service operators reserve to themselves broad rights to remove or pre-screen content, and to suspend or terminate user accounts, sometimes without giving a specific list or only a vague general list of the reasons allowing the removal. The phrases "at our sole discretion", "without prior notice", and "for other reasons" are common in Terms of service agreements.
- Facebook: Among other things, the Facebook Statement of Rights and Responsibilities says: "You will not post content that: is hateful, threatening, or pornographic; incites violence; or contains nudity or graphic or gratuitous violence", "You will not use Facebook to do anything unlawful, misleading, malicious, or discriminatory", "We can remove any content or information you post on Facebook if we believe that it violates this Statement", and "If you are located in a country embargoed by the United States, or are on the U.S. Treasury Department's list of Specially Designated Nationals you will not engage in commercial activities on Facebook (such as advertising or payments) or operate a Platform application or website".
- Google: Google's general Terms of Service, which were updated on 1 March 2012, state: "We may suspend or stop providing our Services to you if you do not comply with our terms or policies or if we are investigating suspected misconduct", "We may review content to determine whether it is illegal or violates our policies, and we may remove or refuse to display content that we reasonably believe violates our policies or the law", and "We respond to notices of alleged copyright infringement and terminate accounts of repeat infringers according to the process set out in the U.S. Digital Millennium Copyright Act".
- Google Search: Google's Webmaster Tools help includes the following statement: "Google may temporarily or permanently remove sites from its index and search results if it believes it is obligated to do so by law, if the sites do not meet Google's quality guidelines, or for other reasons, such as if the sites detract from users' ability to locate relevant information."
- Twitter: The Twitter Terms of Service state: "We reserve the right at all times (but will not have an obligation) to remove or refuse to distribute any Content on the Services and to terminate users or reclaim usernames" and "We reserve the right to remove Content alleged to be copyright infringing without prior notice and at our sole discretion".
- YouTube: The YouTube Terms of Service include the statements: "YouTube reserves the right to decide whether Content violates these Terms of Service for reasons other than copyright infringement, such as, but not limited to, pornography, obscenity, or excessive length. YouTube may at any time, without prior notice and in its sole discretion, remove such Content and/or terminate a user's account for submitting such material in violation of these Terms of Service", "YouTube will remove all Content if properly notified that such Content infringes on another's intellectual property rights", and "YouTube reserves the right to remove Content without prior notice".
- Misplaced Pages: The site's content may be modified or deleted by any editor as part of the normal process of editing and updating articles. Misplaced Pages's deletion policy outlines the circumstances in which entire articles can be deleted. Any editor who believes a page doesn't belong in the encyclopedia can propose its deletion. Such a page can be deleted by any administrator if, after seven days, no one objects to the proposed deletion. Speedy deletion allows for outright deletion of articles that are so clearly in violation of rules of the website that they do not need to undergo a full deletion discussion. All deletion decisions may be reviewed, either informally or formally. An additional means of hiding specific content within Misplaced Pages articles is revision deletion, or RevDel, by which an administrator can perform sanitization/redaction of specific revisions of an article, thereby hiding certain information from the view of non-administrators.
- Yahoo: Yahoo!'s Terms of Service (TOS) state: "You acknowledge that Yahoo! may or may not pre-screen Content, but that Yahoo! and its designees shall have the right (but not the obligation) in their sole discretion to pre-screen, refuse, or remove any Content that is available via the Yahoo! Services. Without limiting the foregoing, Yahoo! and its designees shall have the right to remove any Content that violates the TOS or is otherwise objectionable."
Circumvention
Main article: Internet censorship circumventionInternet censorship circumvention is one of the processes used by technologically savvy Internet users to bypass the technical aspects of Internet filtering and gain access to the otherwise censored material. Circumvention is an inherent problem for those wishing to censor the Internet because filtering and blocking do not remove content from the Internet, but instead block access to it. Therefore, as long as there is at least one publicly accessible uncensored system, it will often be possible to gain access to the otherwise censored material. However circumvention may not be possible by non-tech-savvy users, so blocking and filtering remain effective means of censoring the Internet access of large numbers of users.
Different techniques and resources are used to bypass Internet censorship, including proxy websites, virtual private networks, sneakernets, the dark web and circumvention software tools. Solutions have differing ease of use, speed, security, and risks. Most, however, rely on gaining access to an Internet connection that is not subject to filtering, often in a different jurisdiction not subject to the same censorship laws. According to GlobalWebIndex, over 400 million people use virtual private networks to circumvent censorship or for an increased level of privacy. The majority of circumvention techniques are not suitable for day to day use.
There are risks to using circumvention software or other methods to bypass Internet censorship. In some countries, individuals that gain access to otherwise restricted content may be violating the law and if caught can be expelled, fired, jailed, or subject to other punishments and loss of access.
In June 2011, The New York Times reported that the U.S. is engaged in a "global effort to deploy 'shadow' Internet and mobile phone systems that dissidents can use to undermine repressive governments that seek to silence them by censoring or shutting down telecommunications networks."
Another way to circumvent Internet censorship is to physically go to an area where the Internet is not censored. In 2017, a so-called "Internet refugee camp" was established by IT workers in the village of Bonako, just outside an area of Cameroon where the Internet is regularly blocked.
Increased use of HTTPS
The use of HTTPS versus what originally was HTTP in web searches created greater accessibility to most sites originally blocked or heavily monitored. Many social media sites including, Facebook, Google, and Twitter have added an automatic redirection to HTTPS as of 2017. With the added adoption of HTTPS use, "censors" are left with limited options of either completely blocking all content or none of it.
The use of HTTPS does not inherently prevent the censorship of an entire domain, as the domain name is left unencrypted in the ClientHello of the TLS handshake. The Encrypted Client Hello TLS extension expands on HTTPS and encrypts the entire ClientHello but this depends on both client and server support.
Common targets
There are several motives or rationales for Internet filtering: politics and power, social norms and morals, and security concerns. Protecting existing economic interests is an additional emergent motive for Internet filtering. In addition, networking tools and applications that allow the sharing of information related to these motives are themselves subjected to filtering and blocking. And while there is considerable variation from country to country, the blocking of web sites in a local language is roughly twice that of web sites available only in English or other international languages.
Politics and power
Censorship directed at political opposition to the ruling government is common in authoritarian and repressive regimes. Some countries block web sites related to religion and minority groups, often when these movements represent a threat to the ruling regimes.
Examples include:
- Political blogs and websites
- Lèse-majesté sites, sites with content that offends the dignity of or challenges the authority of a reigning sovereign or of a state
- Falun Gong and Tibetan exile group sites in China or Buddhist, Cao Dai faith, and indigenous hill tribes sites in Vietnam
- 50 Cent Party, or "50 Cent Army" that worked to sway negative public opinion on the Chinese Communist Party
- Russian web brigades
- Sites aimed at religious conversion from Islam to Christianity
- Sites criticizing the government or an authority in the country
- Sites that comment on political parties that oppose the current government of a country
- Sites that accuse authorities of corruption
- Sites that comment on minorities or LGBTQ issues
- Communist symbols and imagery in Poland, Lithuania, Ukraine, Georgia, Latvia, Moldova, Hungary, and Indonesia
- Neo-Nazi and similar websites, particularly in France and Germany
Social norms
Social filtering is censorship of topics that are held to be antithetical to accepted societal norms. In particular censorship of child pornography and content deemed inappropriate for children enjoys very widespread public support and such content is subject to censorship and other restrictions in most countries.
Examples include:
- Sites that include hate speech inciting racism, sexism, homophobia, or other forms of bigotry
- Sites seen as promoting illegal drug use (such as Erowid)
- Sex and erotic, fetishism, prostitution, and pornographic sites
- Child pornography and pedophile-related sites (see also CIRCAMP)
- Gambling sites
- Sites encouraging or inciting violence
- Sites promoting criminal activity
- Sites that contain blasphemous content, particularly when directed at a majority or state supported religion
- Sites that contain defamatory, slanderous, or libelous content
- Sites that include political satire
- Sites that contain information on social issues or "online protests, petitions and campaigns"
Security concerns
Many organizations implement filtering as part of a defense in depth strategy to protect their environments from malware, and to protect their reputations in the event of their networks being used, for example, to carry out sexual harassment.
Internet filtering related to threats to national security that targets the Web sites of insurgents, extremists, and terrorists often enjoys wide public support.
Examples include:
- Blocking of pro–North Korean sites by South Korea
- Blocking of sites of groups that foment domestic conflict in India
- Blocking of sites of the Muslim Brotherhood in some countries in the Middle East
- Blocking of sites such as 4chan thought to be related to the internet hacker group Anonymous
Protection of existing economic interests and copyright
The protection of existing economic interests is sometimes the motivation for blocking new Internet services such as low-cost telephone services that use Voice over Internet Protocol (VoIP). These services can reduce the customer base of telecommunications companies, many of which enjoy entrenched monopoly positions and some of which are government sponsored or controlled.
Anti-copyright activists Christian Engström, Rick Falkvinge and Oscar Swartz have alleged that censorship of child pornography is being used as a pretext by copyright lobby organizations to get politicians to implement similar site blocking legislation against copyright-related piracy.
Examples include:
- File sharing and peer-to-peer (P2P) related websites such as The Pirate Bay
- Skype
- Sites that sell or distribute music, but are not 'approved' by rights holders, such as AllOfMP3
Network tools
Blocking the intermediate tools and applications of the Internet that can be used to assist users in accessing and sharing sensitive material is common in many countries.
Examples include:
- Media sharing websites (e.g. Flickr and YouTube)
- Social networks (e.g. Facebook and Instagram)
- Translation sites and tools
- E-mail providers
- Web hosting sites
- Blog hosting sites such as Blogspot and Medium
- Microblogging sites such as Twitter and Weibo
- Misplaced Pages
- Censorship circumvention sites
- Search engines such as Bing and Google – particularly in Mainland China and Cuba
Information about individuals
Main article: Right to be forgottenThe right to be forgotten is a concept that has been discussed and put into practice in the European Union. In May 2014, the European Court of Justice ruled against Google in Costeja, a case brought by a Spanish man who requested the removal of a link to a digitized 1998 article in La Vanguardia newspaper about an auction for his foreclosed home, for a debt that he had subsequently paid. He initially attempted to have the article removed by complaining to Spain's data protection agency—Agencia Española de Protección de Datos—which rejected the claim on the grounds that it was lawful and accurate, but accepted a complaint against Google and asked Google to remove the results. Google sued in Spain and the lawsuit was transferred to the European Court of Justice. The court ruled in Costeja that search engines are responsible for the content they point to and thus, Google was required to comply with EU data privacy laws. It began compliance on 30 May 2014 during which it received 12,000 requests to have personal details removed from its search engine.
Index on Censorship claimed that "Costeja ruling ... allows individuals to complain to search engines about information they do not like with no legal oversight. This is akin to marching into a library and forcing it to pulp books. Although the ruling is intended for private individuals it opens the door to anyone who wants to whitewash their personal history....The Court's decision is a retrograde move that misunderstands the role and responsibility of search engines and the wider internet. It should send chills down the spine of everyone in the European Union who believes in the crucial importance of free expression and freedom of information."
Resilience
Various contexts influence whether or not an internet user will be resilient to censorship attempts. Users are more resilient to censorship if they are aware that information is being manipulated. This awareness of censorship leads to users finding ways to circumvent it. Awareness of censorship also allows users to factor this manipulation into their belief systems. Knowledge of censorship also offers some citizens incentive to try to discover information that is being concealed. In contrast, those that lack awareness of censorship cannot easily compensate for information manipulation.
Other important factors for censorship resiliency are the demand for the information being concealed, and the ability to pay the costs to circumvent censorship. Entertainment content is more resilient to online censorship than political content, and users with more education, technology access, and wider, more diverse social networks are more resilient to censorship attempts.
Around the world
Main articles: Internet censorship and surveillance by country and Censorship by countryAs more people in more places begin using the Internet for important activities, there is an increase in online censorship, using increasingly sophisticated techniques. The motives, scope, and effectiveness of Internet censorship vary widely from country to country. The countries engaged in state-mandated filtering are clustered in three main regions of the world: east Asia, central Asia, and the Middle East/North Africa.
Countries in other regions also practice certain forms of filtering. In the United States, state-mandated Internet filtering occurs on some computers in libraries and K–12 schools. Content related to Nazism or Holocaust denial is blocked in France and Germany. Child pornography and hate speech are blocked in many countries throughout the world. In fact, many countries throughout the world, including some democracies with long traditions of strong support for freedom of expression and freedom of the press, are engaged in some amount of online censorship, often with substantial public support.
Internet censorship in China is among the most stringent in the world. The government blocks Web sites that discuss the Dalai Lama, the 1989 crackdown on Tiananmen Square protesters, the banned spiritual practice Falun Gong, as well as many general Internet sites. The government requires Internet search firms and state media to censor issues deemed officially "sensitive," and blocks access to foreign websites including Facebook, Twitter, and YouTube. According to a study in 2014, censorship in China is used to muzzle those outside government who attempt to spur the creation of crowds for any reason—in opposition to, in support of, or unrelated to the government.
There are international bodies that oppose internet censorship, for example "Internet censorship is open to challenge at the World Trade Organization (WTO) as it can restrict trade in online services, a forthcoming study argues".
International concerns
Generally, national laws affecting content within a country only apply to services that operate within that country and do not affect international services, but this has not been established clearly by international case law. There are concerns that due to the vast differences in freedom of speech between countries, that the ability for one country to affect speech across the global Internet could have chilling effects.
For example, Google had won a case at the European Court of Justice in September 2019 that ruled that the EU's right to be forgotten only applied to services within the EU, and not globally. But in a contrary decision in October 2019, the same court ruled that Facebook was required to globally comply with a takedown request made in relationship to defamatory material that was posted to Facebook by an Austrian that was libelous of another, which had been determined to be illegal under Austrian laws. The case created a problematic precedent that the Internet may become subject to regulation under the strictest national defamation laws, and would limit free speech that may be acceptable in other countries.
Internet shutdowns
See also: Internet outageSeveral governments have resorted to shutting down most or all Internet connections in all or part of the country.
This appears to have been the case on 27 and 28 January 2011 during the 2011 Egyptian revolution, in what has been widely described as an "unprecedented" internet block. About 3500 Border Gateway Protocol (BGP) routes to Egyptian networks were shut down from about 22:10 to 22:35 UTC 27 January. This full block was implemented without cutting off major intercontinental fibre-optic links, with Renesys stating on 27 January, "Critical European-Asian fiber-optic routes through Egypt appear to be unaffected for now." Full blocks also occurred in Myanmar/Burma in 2007, Libya in 2011, Iran in 2019, and Syria during the Syrian civil war.
Almost all Internet connections in Sudan were disconnected from 3 June to 9 July 2019, in response to a political opposition sit-in seeking civilian rule. A near-complete shutdown in Ethiopia lasted for a week after the Amhara Region coup attempt. A week-long shutdown in Mauritania followed disputes over the 2019 Mauritanian presidential election. Other country-wide shutdowns in 2019 include Zimbabwe after a gasoline price protests triggered police violence, Gabon during the 2019 Gabonese coup attempt, and during or after elections in Democratic Republic of the Congo, Benin, Malawi, and Kazakhstan.
Local shutdowns are frequently ordered in India during times of unrest and security concerns. Some countries have used localized Internet shutdowns to combat cheating during exams, including Iraq, Ethiopia, India, Algeria, and Uzbekistan.
The Iranian government imposed a total internet shutdown from 16 to 23 November 2019, in response to the fuel protests. Doug Madory, the director of Internet analysis at Oracle, has described the operation as "unusual in its scale" and way more advanced. Beginning Saturday afternoon on 16 November 2019, the government of Iran ordered the disconnection of much of the country's internet connectivity as a response to widespread protests against the government's decision to raise gas prices. While Iran is no stranger to government-directed interference in its citizens’ access to the internet, this outage is notable in how it differs from past events. Unlike previous efforts at censorship and bandwidth throttling, the internet of Iran is presently experiencing a multi-day wholesale disconnection for much of its population – arguably the largest such event ever for Iran.
Reports, ratings, and trends

Has local YouTube version Accessible Blocked Previously blocked
Detailed country by country information on Internet censorship is provided by the OpenNet Initiative, Reporters Without Borders, Freedom House, V-Dem Institute, Access Now and in the US State Department Bureau of Democracy, Human Rights, and Labor's Human Rights Reports. The ratings produced by several of these organizations are summarized in the Internet censorship and surveillance by country and the Censorship by country articles.
OpenNet Initiative reports
Through 2010, the OpenNet Initiative had documented Internet filtering by governments in over forty countries worldwide. The level of filtering in 26 countries in 2007 and in 25 countries in 2009 was classified in the political, social, and security areas. Of the 41 separate countries classified, seven were found to show no evidence of filtering in all three areas (Egypt, France, Germany, India, Ukraine, United Kingdom, and United States), while one was found to engage in pervasive filtering in all three areas (China), 13 were found to engage in pervasive filtering in one or more areas, and 34 were found to engage in some level of filtering in one or more areas. Of the 10 countries classified in both 2007 and 2009, one reduced its level of filtering (Pakistan), five increased their level of filtering (Azerbaijan, Belarus, Kazakhstan, South Korea, and Uzbekistan), and four maintained the same level of filtering (China, Iran, Myanmar, and Tajikistan).
Freedom on the Net reports
The Freedom on the Net reports from Freedom House provide analytical reports and numerical ratings regarding the state of Internet freedom for countries worldwide. The countries surveyed represent a sample with a broad range of geographical diversity and levels of economic development, as well as varying levels of political and media freedom. The surveys ask a set of questions designed to measure each country's level of Internet and digital media freedom, as well as the access and openness of other digital means of transmitting information, particularly mobile phones and text messaging services. Results are presented for three areas: Obstacles to Access, Limits on Content, and Violations of User Rights. The results from the three areas are combined into a total score for a country (from 0 for best to 100 for worst) and countries are rated as "Free" (0 to 30), "Partly Free" (31 to 60), or "Not Free" (61 to 100) based on the totals.
Starting in 2009 Freedom House has produced nine editions of the report. There was no report in 2010. The reports generally cover the period from June through May.
Freedom on the Net Survey Results 2009 2011 2012 2013 2014 2015 2016 2017 2018 Countries 15 37 47 60 65 65 65 65 65 Free 4 (27%) 8 (22%) 14 (30%) 17 (29%) 19 (29%) 18 (28%) 17 (26%) 16 (25%) 15 (23%) Partly free 7 (47%) 18 (49%) 20 (43%) 29 (48%) 31 (48%) 28 (43%) 28 (43%) 28 (43%) 30 (46%) Not free 4 (27%) 11 (30%) 13 (28%) 14 (23%) 15 (23%) 19 (29%) 20 (31%) 21 (32%) 20 (31%) Improved n/a 5 (33%) 11 (31%) 12 (26%) 12 (18%) 15 (23%) 34 (52%) 32 (49%) 19 (29%) Declined n/a 9 (60%) 17 (47%) 28 (60%) 36 (55%) 32 (49%) 14 (22%) 13 (20%) 26 (40%) No change n/a 1 (7%) 8 (22%) 7 (15%) 17 (26%) 18 (28%) 17 (26%) 20 (31%) 20 (31%)
The 2014 report assessed 65 countries and reported that 36 countries experienced a negative trajectory in Internet freedom since the previous year, with the most significant declines in Russia, Turkey and Ukraine. According to the report, few countries demonstrated any gains in Internet freedom, and the improvements that were recorded reflected less vigorous application of existing controls rather than new steps taken by governments to actively increase Internet freedom. The year's largest improvement was recorded in India, where restrictions to content and access were relaxed from what had been imposed in 2013 to stifle rioting in the northeastern states. Notable improvement was also recorded in Brazil, where lawmakers approved the bill Marco Civil da Internet, which contains significant provisions governing net neutrality and safeguarding privacy protection.
Reporters Without Borders (RSF)
RWB "Internet enemies" and "countries under surveillance" lists
In 2006, Reporters without Borders (Reporters sans frontières, RSF), a Paris-based international non-governmental organization that advocates freedom of the press, started publishing a list of "Enemies of the Internet". The organization classifies a country as an enemy of the internet because "all of these countries mark themselves out not just for their capacity to censor news and information online but also for their almost systematic repression of Internet users." In 2007 a second list of countries "Under Surveillance" (originally "Under Watch") was added.
Enemies of the Internet:
|
Current Countries Under Surveillance:
Past Countries Under Surveillance:
|
When the "Enemies of the Internet" list was introduced in 2006, it listed 13 countries. From 2006 to 2012 the number of countries listed fell to 10 and then rose to 12. The list was not updated in 2013. In 2014 the list grew to 19 with an increased emphasis on surveillance in addition to censorship. The list has not been updated since 2014.
When the "Countries under surveillance" list was introduced in 2008, it listed 10 countries. Between 2008 and 2012 the number of countries listed grew to 16 and then fell to 11. The number grew to 12 with the addition of Norway in 2020. The list was last updated in 2020.
RWB Special report on Internet Surveillance
On 12 March 2013, Reporters Without Borders published a Special report on Internet Surveillance. The report includes two new lists:
- a list of "State Enemies of the Internet", countries whose governments are involved in active, intrusive surveillance of news providers, resulting in grave violations of freedom of information and human rights; and
- a list of "Corporate Enemies of the Internet", companies that sell products that are liable to be used by governments to violate human rights and freedom of information.
The five "State Enemies of the Internet" named in March 2013 are: Bahrain, China, Iran, Syria, and Vietnam.
The five "Corporate Enemies of the Internet" named in March 2013 are: Amesys (France), Blue Coat Systems (U.S.), Gamma Group (UK and Germany), HackingTeam (Italy), and Trovicor (Germany).
V-Dem Digital Societies Project
The V-Dem Digital Societies Project measures a range of questions related to internet censorship, misinformation online, and internet shutdowns. This annual report includes 35 indicators assessing five areas: disinformation, digital media freedom, state regulation of digital media, polarization of online media, and online social cleavages. The data set uses V-Dem's methodology of aggregating surveys of experts from around the world. It has been updated each year starting in 2019, with data covering from 2000–2021. These ratings are more similar to other expert analyses like Freedom House than remotely sensed data from Access Now.
Access Now #KeepItOn
Access Now maintains an annual list of internet shutdowns, throttling, and blockages as part of the #KeepItOn project. These data track several features of shutdowns including their location, their duration, the particular services impacted, the government's justification for the shutdown, and actual reasons for the shutdown as reported by independent media. Unlike Freedom House or V-Dem, Access Now detects shutdowns using remote sensing and then confirms these instances with reports from civil society, government, in-country volunteers, or ISPs. These methods have been found to be less prone to false positives.
BBC World Service global public opinion poll
A poll of 27,973 adults in 26 countries, including 14,306 Internet users, was conducted for the BBC World Service by the international polling firm GlobeScan using telephone and in-person interviews between 30 November 2009 and 7 February 2010. GlobeScan Chairman Doug Miller felt, overall, that the poll showed that:
- Despite worries about privacy and fraud, people around the world see access to the internet as their fundamental right. They think the web is a force for good, and most don't want governments to regulate it.
Findings from the poll include:
- Nearly four in five (78%) Internet users felt that the Internet had brought them greater freedom.
- Most Internet users (53%) felt that "the internet should never be regulated by any level of government anywhere".
- Opinion was evenly split between Internet users who felt that "the internet is a safe place to express my opinions" (48%) and those who disagreed (49%). Users in Germany and France agreed the least, followed by users in a highly filtered country such as China, while users in Egypt, India and Kenya agreed more strongly.
- The aspects of the Internet that cause the most concern include: fraud (32%), violent and explicit content (27%), threats to privacy (20%), state censorship of content (6%), and the extent of corporate presence (3%).
- Almost four in five Internet users and non-users around the world felt that access to the Internet was a fundamental right (50% strongly agreed, 29% somewhat agreed, 9% somewhat disagreed, 6% strongly disagreed, and 6% gave no opinion). And while there is strong support for this right in all of the countries surveyed, it is surprising that the United States and Canada were among the top five countries where people most strongly disagreed that access to the Internet was a fundamental right of all people (13% in Japan, 11% in the U.S., 11% in Kenya, 11% in Pakistan, and 10% in Canada strongly disagree).
Internet Society's Global Internet User Survey
In July and August 2012, the Internet Society conducted online interviews of more than 10,000 Internet users in 20 countries. Some of the results relevant to Internet censorship are summarized below.
| Question | No. of Responses | Responses |
|---|---|---|
| Access to the Internet should be considered a basic human right. | 10,789 | 83% somewhat or strongly agree, 14% somewhat or strongly disagree, 3% don't know |
| Freedom of expression should be guaranteed on the Internet. | 10,789 | 86% somewhat or strongly agree, 11% somewhat or strongly disagree, 2% don't know |
| The Internet should be governed in some form to protect the community from harm. | 10,789 | 82% somewhat or strongly agree, 15% somewhat or strongly disagree, 3% don't know / not applicable |
| Censorship should exist in some form on the Internet. | 10,789 | 71% somewhat or strongly agree, 24% somewhat or strongly disagree, 5% don't know / not applicable |
| Each individual country has the right to govern the Internet the way they see fit. | 10,789 | 67% somewhat or strongly agree, 29% somewhat or strongly disagree, 4% don't know / not applicable |
| The Internet does more to help society than it does to hurt it. | 10,789 | 83% somewhat or strongly agree, 13% somewhat or strongly disagree, 4% don't know / not applicable |
| How often do you read the privacy policies of websites or services that you share personal information with? | 10,789 | 16% all the time, 31% most of the time, 41% sometimes, 12% never |
| When you are logged in to a service or application do you use privacy protections? | 10,789 | 27% all the time, 36% most of the time, 29% sometimes, 9% never |
| Do you use "anonymization" services, for example, the "anonymize" feature in your web browser, specialized software like Tor, third - party redirection services like duckduckgo.com? | 10,789 | 16% yes, 38% no, 43% don't know / not aware of these types of services, 3% would like to use them but I am not able to |
| Increased government control of the Internet would put limits on the content I can access. | 9,717 | 77% somewhat or strongly agree, 18% somewhat or strongly disagree, 4% don't know / not applicable |
| Increased government control of the Internet would limit my freedom of expression. | 9,717 | 74% somewhat or strongly agree, 23% somewhat or strongly disagree, 4% don't know / not applicable |
| Increased government control of the Internet would improve the content on the Internet. | 9,717 | 49% somewhat or strongly agree, 44% somewhat or strongly disagree, 7% don't know / not applicable |
| Increased government control of the Internet would make the Internet safe for everyone to use. | 9,717 | 58% somewhat or strongly agree, 35% somewhat or strongly disagree, 7% don't know / not applicable |
| Increased government control of the Internet would have no effect. | 9,717 | 31% somewhat or strongly agree, 56% somewhat or strongly disagree, 14% don't know / not applicable |
| To what degree would you accept increased control or monitoring of the Internet if you gained increased safety? | 10,789 | 61% a lot or somewhat, 23% not very much or not at all |
Transparency of filtering or blocking activities
Among the countries that filter or block online content, few openly admit to or fully disclose their filtering and blocking activities. States are frequently opaque and/or deceptive about the blocking of access to political information. For example:
- Saudi Arabia and the United Arab Emirates (UAE) are among the few states that publish detailed information about their filtering practices and display a notification to the user when attempting to access a blocked website. The websites that are blocked are mostly pornographic or considered un-Islamic.
- In contrast, countries such as China and Tunisia send users a false error indication. China blocks requests by users for a banned website at the router level and a connection error is returned, effectively preventing the user's IP address from making further HTTP requests for a varying time, which appears to the user as "time-out" error with no explanation. Tunisia has altered the block page functionality of SmartFilter, the commercial filtering software it uses, so that users attempting to access blocked websites receive a fake "File not found" error page.
- In Uzbekistan, users are frequently sent block pages stating that the website is blocked because of pornography, even when the page contains no pornography. Uzbeki ISPs may also redirect users' request for blocked websites to unrelated websites, or sites similar to the banned websites, but with different information.
Arab Spring
See also: Internet censorship in the Arab Spring, Internet in Egypt § 2011 Internet shutdown, and Free speech in the media during the Libyan civil war (2011)During the Arab Spring of 2011, media jihad (media struggle) was extensive. Internet and mobile technologies, particularly social networks such as Facebook and Twitter, played and are playing important new and unique roles in organizing and spreading the protests and making them visible to the rest of the world. An activist in Egypt tweeted, "we use Facebook to schedule the protests, Twitter to coordinate, and YouTube to tell the world".
This successful use of digital media in turn led to increased censorship including the complete loss of Internet access for periods of time in Egypt and Libya in 2011. In Syria, the Syrian Electronic Army (SEA), an organization that operates with at least tacit support of the government, claims responsibility for defacing or otherwise compromising scores of websites that it contends spread news hostile to the Syrian government. SEA disseminates denial of service (DoS) software designed to target media websites including those of Al Jazeera, BBC News, Syrian satellite broadcaster Orient TV, and Dubai-based Al Arabiya TV.
In response to the greater freedom of expression brought about by the Arab Spring revolutions in countries that were previously subject to very strict censorship, in March 2011, Reporters Without Borders moved Tunisia and Egypt from its "Internet enemies" list to its list of countries "under surveillance" and in 2012 dropped Libya from the list entirely. At the same time, there were warnings that Internet censorship might increase in other countries following the events of the Arab Spring. However, in 2013, Libyan communication company LTT blocked the pornographic websites. It even blocked the family-filtered videos of ordinary websites like Dailymotion.
Russian invasion of Ukraine
During the Russian invasion of Ukraine in 2022, Russia was reported to have blocked the internet websites Twitter and Facebook. Facebook was noted as being suspended due to an objection to its policy of reviewing news stories for authenticity where they were produced by Russian state-backed media before allowing them to be published on its platform. It was subject to a total ban whereas Twitter was suspended regionally. Reports have identified that VPN use has enabled people to circumvent the restrictions by installing software.
It been reported that the European Union would seek to censor Russian media outlets regarded as producing propaganda.
See also
|
Organizations and projects
|
Topics
|
References
- "What is Internet Censorship?". www.iplocation.net. Archived from the original on 1 May 2021. Retrieved 1 May 2021.
- The Editorial Board (15 October 2018). "There May Soon Be Three Internets. America's Won't Necessarily Be the Best. - A breakup of the web grants privacy, security and freedom to some, and not so much to others". The New York Times. Archived from the original on 9 July 2021. Retrieved 16 October 2018.
- ^ Schmidt, Eric E.; Cohen, Jared (11 March 2014). "The Future of Internet Freedom". The New York Times. Archived from the original on 12 December 2020. Retrieved 11 March 2014.
- Goldberg, Erica (2016). "Free Speech Consequentialism". Columbia Law Review. 116 (3): 687–694. JSTOR 43783393.
- ^ Marcello Mari. How Facebook's Tor service could encourage a more open web Archived 10 June 2016 at the Wayback Machine. The Guardian. Friday 5 December 2014.
- ^ Freedom of connection, freedom of expression: the changing legal and regulatory ecology shaping the Internet Archived 28 September 2011 at the Wayback Machine, Dutton, March 2003
- "First Nation in Cyberspace", Philip Elmer-Dewitt, Time, 6 December 1993, No.49
- "Cerf sees government control of Internet failing" Archived 3 November 2020 at the Wayback Machine, Pedro Fonseca, Reuters, 15 November 2006
- 2007 Circumvention Landscape Report: Methods, Uses, and Tools Archived 11 November 2011 at the Wayback Machine, Hal Roberts, Ethan Zuckerman, and John Palfrey, Beckman Center for Internet & Society at Harvard University, March 2009
- ^ Chadwick, Andrew (2009). Routledge handbook of Internet politics. Routledge international handbooks. Taylor and Francis. p. 332. ISBN 978-0-415-42914-6.
- ^ "Measuring Global Internet Filtering" Archived 9 August 2020 at the Wayback Machine, Robert Faris and Nart Villeneuve, in Access Denied: The Practice and Policy of Global Internet Filtering Archived 26 February 2009 at the Wayback Machine, Ronald Deibert, John Palfrey, Rafal Rohozinski, and Jonathan Zittrain, eds., MIT Press (Cambridge), 2008
- Lao Wai (21 October 2007). "I've Been Rivercrabbed!". An American in Beijing. Archived from the original on 11 August 2011. Retrieved 28 May 2011.
- ^ Jones, Ben; Feamster, Nick; Hall, Joseph; Adams, Stan; Aaron, Michael (23 August 2019). "A Survey of Worldwide Censorship Techniques". IETF. Archived from the original on 19 September 2020. Retrieved 30 September 2019.
- Hoffman, Chris (22 September 2016). "How the "Great Firewall of China" Works to Censor China's Internet". www.howtogeek.com. How to geek. Archived from the original on 15 August 2018. Retrieved 15 August 2018.
- For an example, see Misplaced Pages:Advice to users using Tor to bypass the Great Firewall
- Tom Espiner (4 July 2006). "Academics break the Great Firewall of China". ZDNet. Archived from the original on 8 October 2009. Retrieved 5 April 2015.
- Greenberg, Andy. "The Ingenious Way Iranians Are Using Satellite TV to Beam in Banned Internet". WIRED. Archived from the original on 8 November 2020. Retrieved 25 January 2018.
- Google excluding controversial sites Archived 23 November 2020 at the Wayback Machine, Declan McCullagh, CNET News, 23 October 2002, 8:55 pm PDT. Retrieved 22 April 2007 00:40 UTC
- "The Emergence of Open and Organized Pro-Government Cyber Attacks in the Middle East: The Case of the Syrian Electronic Army" Archived 14 May 2020 at the Wayback Machine, Helmi Noman, OpenNet Initiative, May 2011
- "India blocks Yahoo! Groups" Archived 17 September 2018 at the Wayback Machine, Andrew Orlowski, The Register, 24 September 2003
- ^ Chadwick, Andrew (2009). Routledge handbook of Internet politics. Routledge international handbooks. Taylor and Francis. pp. 330–331. ISBN 978-0-415-42914-6.
- "Political Repression 2.0" Archived 12 November 2020 at the Wayback Machine, Evgeny Morzov, Op-Ed Contributor to the New York Times, 1 September 2011
- Glanville, Jo (17 November 2008). "The big business of net censorship". The Guardian. London. Archived from the original on 28 January 2013. Retrieved 11 December 2016.
- "Internet content filtering" Archived 17 December 2013 at the Wayback Machine, Netsweeper, Inc. web site. Retrieved 1 September 2011
- ^ "West Censoring East: The Use of Western Technologies by Middle East Censors, 2010–2011" Archived 18 September 2018 at the Wayback Machine, Helmi Noman and Jillian C. York, OpenNet Initiative, March 2011
- "BAD TRAFFIC: Sandvine's PacketLogic Devices Used to Deploy Government Spyware in Turkey and Redirect Egyptian Users to Affiliate Ads?". The Citizen Lab. 9 March 2018. Archived from the original on 10 December 2020. Retrieved 10 May 2018.
- ^ The Enemies of the Internet Special Edition : Surveillance Archived 31 August 2013 at the Wayback Machine, Reporters Without Borders, 12 March 2013
- "The Great Firewall of China". National Council for the Social Studies. 27 May 2016. Archived from the original on 29 March 2020. Retrieved 29 March 2020.
- Somini Sengupta (2 September 2011). "Group Says It Has New Evidence of Cisco's Misdeeds in China". The New York Times. Archived from the original on 12 November 2020.
- Chadwick, Andrew (2009). Routledge handbook of Internet politics. Routledge international handbooks. Taylor and Francis. pp. 323–324. ISBN 978-0-415-42914-6.
- "R.I. ACLU releases report on "troubling" internet censorship in public libraries" (Press release). ACLU. 18 April 2005. Archived from the original on 5 December 2008. The Rhode Island affiliate, American Civil Liberties Union (April 2005). Reader's block: Internet censorship in Rhode Island public libraries (PDF) (Report). Archived from the original (PDF) on 6 September 2005.
- Sutton, Maira; Timm, Trevor (7 November 2011). "This Week in Internet Censorship Egypt Imprisons Alaa, Other Pro-democracy Bloggers". Electronic Frontier Foundation. Archived from the original on 12 August 2020. Retrieved 27 March 2012.
- China: Controls tighten as Internet activism grows Archived 25 September 2020 at the Wayback Machine "Cisco Systems, Microsoft, Nortel Networks, Websense and Sun Microsystems", citing Amnesty International: People's Republic of China: State Control of the Internet in China, ASA, 17/007/2002, November 2002.
- "In Mexico, Social Media Become a Battleground in the Drug War" Archived 11 October 2012 at the Wayback Machine, J. David Goodman, The Lede, The New York Times, 15 September 2011
- ^ Provision of information in this fashion is in keeping with principles of freedom of expression, as long as it is done transparently and does not overwhelm alternative sources of information.
- "China's growing army of paid internet commentators" Archived 13 October 2011 at the Wayback Machine, Sarah Cook and Maggie Shum, Freedom House, 11 October 2011
- Farrell, Michael B (22 March 2010). "Google Ends Internet Censorship, Dares China to Make Next Move". link.galegroup.com. The Christian Science Monitor. Archived from the original on 17 January 2023. Retrieved 15 November 2018.
- ^ Reynolds, Glenn Harlan (18 August 2018). "When Digital Platforms Become Censors". The Wall Street Journal. Archived from the original on 30 March 2019.
- Chappell, Bill; Tsioulcas, Anastasia (6 August 2018). "YouTube, Apple and Facebook Ban Infowars, Which Decries 'Mega Purge'". NPR. Archived from the original on 3 May 2019. Retrieved 2 September 2018.
- "Statement of Rights and Responsibilities" Archived 26 December 2018 at the Wayback Machine, Facebook, 26 April 2011. Retrieved 18 August 2011
- "Google Terms of Service" Archived 15 December 2020 at the Wayback Machine, Policies & Principles, Google, Inc.. Retrieved 1 April 2012
- "Why does Google remove sites from the Google index?" Archived 6 May 2007 at the Wayback Machine, Google Webmaster Tools Help. Retrieved 22 April 2007 00:43 UTC
- "Terms of Service" Archived 15 December 2020 at the Wayback Machine, Twitter, 1 June 2011. Retrieved 18 August 2011
- "Terms of Service" Archived 26 December 2016 at the Wayback Machine, YouTube, 9 June 2010. Retrieved 18 August 2011
- West, Andrew Granville; Lee, Insup (October 2011). "What Misplaced Pages deletes: Characterizing dangerous collaborative content". Proceedings of the 7th International Symposium on Wikis and Open Collaboration. pp. 25–28. doi:10.1145/2038558.2038563. ISBN 978-1-4503-0909-7. S2CID 10396423.
- Jemielniak, Dariusz (2014). Common Knowledge?: An Ethnography of Misplaced Pages. Stanford University Press.
- "Yahoo! Terms of Service" Archived 18 July 2014 at the Wayback Machine, Yahoo!, 24 November 2008. Retrieved 18 August 2011
- Roberts, H., Zuckerman, E., & Palfrey, J. (2009, March). 2007 Circumvention Landscape Report: Methods, Uses, and Tools (Rep.). Retrieved 18 March 2016, from The Berkman Center for Internet & Society at Harvard University.
- "Risks" Archived 8 September 2011 at the Wayback Machine, Internet censorship wiki. Retrieved 2 September 2011
- "U.S. Underwrites Internet Detour Around Censors" Archived 11 November 2020 at the Wayback Machine, James Glanz and John Markoff, The New York Times, 12 June 2011
- Dahir, Abdi Latif (28 March 2017). "Reeling from an internet shutdown, startups in Cameroon have created an "internet refugee camp"". Quartz Africa. Archived from the original on 12 November 2020. Retrieved 30 January 2020.
- Ritzen, Yarno (26 January 2018). "Cameroon internet shutdowns cost Anglophones millions". Al Jazeera. Archived from the original on 22 September 2020. Retrieved 30 January 2020.
- Connolly, Amanda (27 January 2016). "Medium stands by journalists as Malaysia blocks the site". The Next Web. Archived from the original on 29 November 2020. Retrieved 26 April 2020.
- Zittrain, Jonathan; Faris, Robert; Noman, Helmi; Clark, Justin; Tilton, Casey; Morrison-Westphal, Ryan (June 2017). "The Shifting Landscape of Global Internet Censorship" (PDF). Dash.Harvard.Edu. Archived (PDF) from the original on 6 December 2018. Retrieved 25 April 2020.
- "Encrypting SNI: Fixing One of the Core Internet Bugs". The Cloudflare Blog. 24 September 2018. Archived from the original on 12 December 2020. Retrieved 22 August 2020.
- Oku, Kazuho; Wood, Christopher; Rescorla, Eric; Sullivan, Nick (June 2020). "Encrypted Server Name Indication for TLS 1.3". IETF. Archived from the original on 16 July 2020. Retrieved 22 August 2020.
- "Blog censorship gains support". CNET. Archived from the original on 29 May 2012. Retrieved 5 April 2015.
- "Far Eastern Economic Review | China's Guerrilla War for the Web". 25 February 2009. Archived from the original on 25 February 2009. Retrieved 25 April 2020.
- ^ "Which Countries Censor the Internet?". Time Magazine. 23 November 2015. p. 36. Archived from the original on 12 November 2015. Retrieved 5 August 2023.
- "Latest Stories From News.Com.Au". Archived from the original on 11 December 2008. Retrieved 8 December 2007.
- Russia Bans the Misplaced Pages of Drugs Archived 11 November 2020 at the Wayback Machine The Fix 2013-02-28
- "Why Malware Filtering Is Necessary in the Web Gateway". Gartner. 26 August 2008. Archived from the original on 18 October 2017. Retrieved 14 April 2012.
- "Collateral Blocking: Filtering by South Korean Government of Pro-North Korean Websites" Archived 9 December 2020 at the Wayback Machine, OpenNet Initiative: Bulletin 009, 31 January 2005
- "Federal authorities take on Anonymous hackers" Archived 9 December 2020 at the Wayback Machine, Associated Press in the Washington Post, 12 September 2011
- Rick Falkvinge (9 July 2011). "The Copyright Lobby Absolutely Loves Child Pornography". TorrentFreak. Archived from the original on 9 December 2020. Retrieved 26 July 2012.
- "YouTube Blocked in...Thailand". Mashable. 11 March 2007. Archived from the original on 9 August 2020. Retrieved 5 April 2015.
- "China struggles to tame microblogging masses" Archived 4 November 2017 at the Wayback Machine, Agence France-Presse (AFP) in The Independent, 8 September 2011
- "Sex, Social Mores, and Keyword Filtering: Microsoft Bing in the "Arabian Countries Archived 13 December 2020 at the Wayback Machine", Helmi Noman, OpenNet Initiative, March 2010
- "Google Search & Cache Filtering Behind China's Great Firewall" Archived 8 August 2020 at the Wayback Machine, OpenNet Initiative: Bulletin 006, 3 September 2004
- "Empirical Analysis of Google SafeSearch" Archived 4 March 2013 at the Wayback Machine, Benjamin Edelman, Berkman Center for Internet & Society, Harvard Law School, 13 April 2003
- "China blocking Google". BBC News. 2 September 2002. Archived from the original on 11 December 2020. Retrieved 5 May 2010.
- Julia Powles (15 May 2014). "What we can salvage from 'right to be forgotten' ruling". Wired.co.uk. Archived from the original on 16 May 2014. Retrieved 16 May 2014.
- Solon, Olivia (13 May 2014). "People have the right to be forgotten, rules EU court". Wired.co.uk. Conde Nast Digital. Archived from the original on 14 May 2014. Retrieved 13 May 2014.
- "EU court backs 'right to be forgotten' in Google case". BBC News. 13 May 2014. Archived from the original on 25 November 2020. Retrieved 13 May 2014.
- "EU court rules Google must tweak search results in test of "right to be forgotten"". CBS News. 13 May 2014. Archived from the original on 3 December 2019. Retrieved 13 May 2014.
- "Removal of Google personal information could become work intensive". Europe News.Net. Archived from the original on 21 October 2014. Retrieved 2 June 2014.
- "Index blasts EU court ruling on "right to be forgotten"". indexoncensorship.org. 13 May 2014. Archived from the original on 19 September 2020. Retrieved 5 April 2015.
- ^ Roberts, Margaret E. (2020). "Resilience to Online Censorship". Annual Review of Political Science. 23: 401–419. doi:10.1146/annurev-polisci-050718-032837.
- "Introduction" (PDF). Archived from the original (PDF) on 29 June 2012. Retrieved 14 September 2011., Jonathan Zittrain and John Palfrey, in Access Denied: The Practice and Policy of Global Internet Filtering Archived 26 February 2009 at the Wayback Machine, Ronald Deibert, John Palfrey, Rafal Rohozinski, and Jonathan Zittrain, eds., MIT Press (Cambridge), 2008
- "Internet Filtering: The Politics and Mechanisms of Control" Archived 19 September 2020 at the Wayback Machine, Jonathan Zittrain and John Palfrey, in Access Denied: The Practice and Policy of Global Internet Filtering Archived 26 February 2009 at the Wayback Machine, Ronald Deibert, John Palfrey, Rafal Rohozinski, and Jonathan Zittrain, eds., MIT Press (Cambridge), 2008
- "Internet Censorship in China". The New York Times. 28 December 2012. Archived from the original on 4 March 2016. Retrieved 9 March 2013.
- Human Rights Watch (22 January 2012). World Report 2012: China. Archived from the original on 11 March 2013. Retrieved 9 March 2013.
- G. King; et al. (22 August 2014). "Reverse-engineering censorship in China: Randomized experimentation and participant observation". Science. 345 (6199): 891. doi:10.1126/science.1251722. PMID 25146296. S2CID 5398090. Archived from the original on 24 August 2020. Retrieved 11 July 2019.
- "WTO could challenge Internet censorship". Newsletter on Intellectual Freedom. 59 (1). Chicago: American Library Association: 6. January 2010. ProQuest 217137198.
- Kelion, Leo (24 September 2019). "Google wins landmark right to be forgotten case". BBC. Archived from the original on 1 December 2020. Retrieved 3 October 2019.
- Satariano, Adam (3 October 2019). "Facebook Can Be Forced to Delete Content, E.U.'s Top Court Rules". The New York Times. Archived from the original on 3 October 2019. Retrieved 3 October 2019.
- ^ Cowie, James. "Egypt Leaves the Internet". Renesys. Archived from the original on 29 January 2011. Retrieved 28 January 2011.
- ^ Kirk, Jeremy (28 January 2011). "With Wired Internet Locked, Egypt Looks to the Sky". IDG News/PC World. Archived from the original on 30 January 2011. Retrieved 28 January 2011.
- "Pulling the Plug: A Technical Review of the Internet Shutdown in Burma". opennet.net. Archived from the original on 15 November 2020. Retrieved 5 April 2015.
- ^ "Journalists confined to their hotels, Internet disconnected". Reporters Without Borders. Archived from the original on 4 March 2016. Retrieved 21 March 2011.
- Skinner, Helena (22 November 2019). "How did Iran's government pull the plug on the Internet?". euronews. Archived from the original on 27 November 2019. Retrieved 9 November 2020.
- "Sudan's Internet Outage". NPR.org. Archived from the original on 8 August 2020. Retrieved 30 July 2019.
- "Sudan internet shows signs of recovery after month-long shutdown". 9 July 2019. Archived from the original on 14 October 2020. Retrieved 30 July 2019.
- "Ethiopia partially restores internet access days after blackout following reported Amhara coup attempt". 27 June 2019. Archived from the original on 14 October 2020. Retrieved 30 July 2019.
- "Post-election internet shutdown in Mauritania following widespread mobile disruptions". 25 June 2019. Archived from the original on 19 November 2020. Retrieved 30 July 2019.
- ^ "Government that have shut down the Internet in 2019". 26 June 2019. Archived from the original on 1 November 2020. Retrieved 30 July 2019.
- "Internet Shutdowns in India". internetshutdowns.in. Archived from the original on 16 November 2021. Retrieved 30 July 2019.
- Krishna Mohan, Vaishnavi (30 January 2021). "Internet Shutdowns in India: From Kashmir to Haryana". Global Views 360. Archived from the original on 31 January 2021. Retrieved 30 January 2021.
- "Iraq shuts down internet to prevent cheating in national science exams". 26 June 2019. Archived from the original on 27 October 2020. Retrieved 30 July 2019.
- "Internet being restored in Iran after week-long shutdown". NetBlocks. 23 November 2019. Archived from the original on 28 November 2019. Retrieved 10 December 2019.
- ^ Ivana Kottasová and Sara Mazloumsaki (19 November 2019). "What makes Iran's internet blackout different". CNN. Archived from the original on 21 November 2019. Retrieved 9 November 2020.
- "Iran shuts down country's internet in the wake of fuel protests". TechCrunch. 17 November 2019. Archived from the original on 25 November 2020. Retrieved 9 November 2020.
- Mihalcik, Carrie. "Iran's internet has been shut down for days amid protests". CNET. Archived from the original on 26 November 2019. Retrieved 9 November 2020.
- "2010 Country Reports on Human Rights Practices", Bureau of Democracy, Human Rights, and Labor, U.S. Department of State, 8 April 2011
- Due to legal concerns the OpenNet Initiative does not check for filtering of child pornography and because their classifications focus on technical filtering, they do not include other types of censorship.
- ^ "Freedom on the Net 2018" (PDF). Freedom House. November 2018. Archived from the original (PDF) on 1 November 2018. Retrieved 1 November 2018.
- ^ Freedom on the Net 2009 Archived 26 March 2018 at the Wayback Machine, Freedom House, accessed 16 April 2012
- ^ Freedom on the Net 2011 Archived 16 June 2018 at the Wayback Machine, Freedom House, accessed 15 April 2012
- ^ Freedom on the Net 2012 Archived 12 April 2019 at the Wayback Machine, Freedom House, accessed 24 September 2012
- ^ Freedom on the Net 2013 Archived 22 April 2018 at the Wayback Machine, Freedom House, 3 October 2013. Retrieved 12 October 2013.
- ^ "Freedom on the Net 2014" (PDF). Freedom House. Archived (PDF) from the original on 12 April 2019. Retrieved 14 December 2014.
- ^ "Freedom on the Net 2015" (PDF). Freedom House. October 2015. Archived (PDF) from the original on 11 April 2019. Retrieved 27 December 2015.
- ^ "Freedom on the Net 2016" (PDF). Freedom House. October 2016. Archived (PDF) from the original on 12 April 2019. Retrieved 25 March 2018.
- ^ "Freedom on the Net 2017" (PDF). Freedom House. October 2017. Archived from the original (PDF) on 12 April 2019. Retrieved 25 March 2018.
- List of the 13 Internet enemies Reporters Without Borders (Paris), 11 July 2006, .
- "Internet enemies", Reporters Without Borders (Paris), 12 March 2009, Archived 16 March 2009 at the Wayback Machine.
- Web 2.0 versus Control 2.0. Reporters Without Borders (Paris), 18 March 2010, Archived 14 March 2010 at the Wayback Machine.
- ^ Internet Enemies Archived 2012-03-23 at the Wayback Machine, Reporters Without Borders (Paris), 12 March 2012
- "Internet Enemies", Enemies of the Internet 2014: Entities at the heart of censorship and surveillance, Reporters Without Borders (Paris), 11 March 2014. Archived 12 March 2014 at the Wayback Machine. Retrieved 24 June 2014.
- Mechkova, V., Daniel P., Brigitte S.,&Steven W. (2020). Digital Society Project Dataset v2.Varieties of Democracy (V-Dem) Project http://digitalsocietyproject.org/ Archived 19 May 2021 at the Wayback Machine
- ^ Mechkova, Valeriya; Pemstein, Daniel; Seim, Brigitte; Wilson, Steven (2021). Digital Society Survey Codebook (PDF). Digital Society Project. Archived (PDF) from the original on 27 May 2021. Retrieved 27 May 2021.
- ^ Fletcher, Terry; Hayes-Birchler, Andria (30 July 2020). Comparing Measures of Internet Censorship: Analyzing the Tradeoffs between Expert Analysis and Remote Measurement. Data for Policy 2020, 15-17 September 2020. doi:10.5281/zenodo.3967398. S2CID 244992072. Archived from the original on 27 May 2021. Retrieved 27 May 2021.
- Taye, B. (2020). Targeted, Cut Off, and Left in the DarkThe #KeepItOn Report on internet shutdowns in 2019. Access Now. https://www.accessnow.org/keepiton/
- Taye, Berhan (2021). "Shattered Dreams and Lost Opportunities" (PDF). Access Now. Archived (PDF) from the original on 2 June 2021. Retrieved 27 May 2021.
- ^ Access Now (2021). "STOP Methodology" (PDF). Access Now. Archived (PDF) from the original on 17 January 2023. Retrieved 27 May 2021.
- For the BBC poll Internet users are those who used the Internet within the previous six months.
- ^ "BBC Internet Poll: Detailed Findings" Archived 1 June 2013 at the Wayback Machine, BBC World Service, 8 March 2010
- "Internet access is 'a fundamental right'" Archived 7 January 2012 at the Wayback Machine, BBC News, 8 March 2010
- "Global Internet User Survey 2012" Archived 14 March 2013 at the Wayback Machine, Internet Society, 20 November 2012
- Note: Responses may not add up to 100% due to rounding in the original report.
- Chadwick, Andrew (2009). Routledge handbook of Internet politics. Routledge international handbooks. Taylor and Francis. p. 331. ISBN 978-0-415-42914-6.
- "The Arab Spring's Cascading Effects" Archived 27 February 2011 at the Wayback Machine, Philip N. Howard, Miller-McCune, 23 February 2011
- "Middle East Political Protest And Internet Traffic Report: February 12–20, 2011" Archived 25 February 2011 at the Wayback Machine, Craig Labovitz, Arbor Networks
- Dainotti; et al. (2011). "Analysis of Country-wide Internet Outages Caused by Censorship" (PDF). ACM. Archived (PDF) from the original on 17 June 2012. Retrieved 14 April 2012.
- "Syrian Electronic Army: Disruptive Attacks and Hyped Targets" Archived 20 July 2018 at the Wayback Machine, OpenNet Initiative, 25 June 2011
- "Countries under surveillance: Egypt" Archived 4 March 2016 at the Wayback Machine, Reporters Without Borders, March 2011
- "Censorship fallout from the Arab Spring?" Archived 26 January 2012 at the Wayback Machine, Juliette Terzieff, The Future 500, 29 June 2011
- "Insight: Social media – a political tool for good or evil?" Archived 6 November 2011 at the Wayback Machine, Peter Apps, Reuters Canada, 28 September 2011
- "LTT Blocks Pornographic Websites". 13 September 2013. Archived from the original on 11 August 2017. Retrieved 10 August 2017.
- Shishkina, Alisa (November 2018). "Internet Censorship in Arab Countries: Religious and Moral Aspects". Religions. 9 (11): 358. doi:10.3390/rel9110358.
- "Ukraine invasion: Russia restricts social media access". BBC News. 26 February 2022. Archived from the original on 2 March 2022. Retrieved 26 February 2022.
Sources
 This article incorporates licensed material from the OpenNet Initiative web site.
This article incorporates licensed material from the OpenNet Initiative web site.
Further reading
- King Gary, Pan, Jennifer, & Robert, Margaret. (2013). "How Censorship in China Allows Government Criticism but Silences Collective Expression." American Political Science Review, 107(2), 326–343.
External links
![]() Media related to Internet censorship at Wikimedia Commons
Media related to Internet censorship at Wikimedia Commons
- Censorship Wikia, an anti-censorship site that catalogs past and present censored works, using verifiable sources, and a forum to discuss organizing against and circumventing censorship.
- "Index on Censorship", website of Index on Censorship, a London-based organization and magazine that promotes freedom of expression.
- Internet censorship wiki (Archived 2017-06-07 at the Wayback Machine) provided information about different methods of access filtering and ways to bypass them.
- "Online Survival Kit", We Fight Censorship project of Reporters Without Borders.
- "Media Freedom Internet Cookbook" by the OSCE Representative on Freedom of the Media, Vienna, 2004.
- How to Bypass Internet Censorship, also known by the titles: Bypassing Internet Censorship or Circumvention Tools, a FLOSS Manual, 10 March 2011, 240 pp.
| Censorship and websites | |
|---|---|
| Censorship of | |
| Censorship by | |
| Websites blocked in | |
| Media manipulation | |
|---|---|
| Context | |
| Activism | |
| Advertising | |
| Censorship and Media regulation | |
| Hoaxing | |
| Marketing | |
| News media | |
| Political campaigning | |
| Propaganda | |
| Psychological warfare | |
| Public relations | |
| Sales | |
| Related | |
| Internet censorship circumvention technologies | |||||||
|---|---|---|---|---|---|---|---|
| Background |
| ||||||
| Principles |
| ||||||
| Anti-censorship software |
| ||||||
| Anonymity |
| ||||||
| Physical circumvention methods | |||||||
| Relevant organizations | |||||||
| Reference | |||||||
| Italics indicates that maintenance of the tool has been discontinued. | |||||||
-
 Creative Commons Attribution 3.0 Unported license, see the lower right corner of pages at the OpenNet Initiative web site Archived 25 September 2018 at the Wayback Machine
Creative Commons Attribution 3.0 Unported license, see the lower right corner of pages at the OpenNet Initiative web site Archived 25 September 2018 at the Wayback Machine