This is an old revision of this page, as edited by Sandstein (talk | contribs) at 20:23, 1 February 2013 (Misplaced Pages:Articles for deletion/FDIC Enterprise Architecture Framework closed as keep). The present address (URL) is a permanent link to this revision, which may differ significantly from the current revision.
Revision as of 20:23, 1 February 2013 by Sandstein (talk | contribs) (Misplaced Pages:Articles for deletion/FDIC Enterprise Architecture Framework closed as keep)(diff) ← Previous revision | Latest revision (diff) | Newer revision → (diff)| This article needs to be updated. Please help update this article to reflect recent events or newly available information. (January 2013) |

FDIC Enterprise Architecture Framework is the Enterprise Architecture framework of the United States Federal Deposit Insurance Corporation (FDIC). A lot of the current article is about the Enterprise Architecture Framework developed around 2005, and currently anno 2011 out-of-date.
Overview
The FDIC's framework for implementing its Enterprise Architecture is based on Federal and industry best practices, including the Chief Information Officer (CIO) Council's Federal Enterprise Architecture Framework (FEAF) and the Zachman Framework for Enterprise Architecture. FDIC's framework has been tailored to emphasize security. The FDIC EA framework complies with the FEAF and highlights the importance of security to all other components of the architecture.
The FDIC EA framework includes five components. The first component, the Business Architecture, focuses on FDIC's business needs. The next three components, the Data Architecture, Applications Architecture, and Technical Infrastructure Architectures, focus on the technological capabilities that support the business and information needs. The final component, the Security Architecture, focuses on specific aspects of interest to the Corporation that span the enterprise and must be integral parts of all other architectures.
History
Historically, Federal agencies have managed IT investments autonomously. Until the new millennium, there has been little incentive for agencies to partner to effectively reuse IT investments, share IT knowledge, and explore joint solutions. Starting in the second half of the 1990 a collective, government-wide effort, supported by the Federal CIO Council, utilizing the Federal Enterprise Architecture (FEA), has been undertaken in an effort to yield significant improvements in the management and reuse of IT investments, while improving services to citizens, and facilitating business relationships internally and externally.
The Federal Deposit Insurance Corporation (FDIC) first realized the value of Enterprise Architecture in 1997, when two business executives had to reconcile data that had come from different systems for a high-profile report to the banking industry. The FDIC's first EA blueprint was published in December 2002.
In 2004 the FDIC received a 2004 Enterprise Architecture Excellence Award from the Zachman Institute for Framework Advancement (ZIFA) for its initiative to manage corporate data collaboratively.
EA framework topics
FDIC EA framework
The FDIC EA framework from 2005 included five components.
- Business Architecture : The Business Architecture describes the activities and processes performed by the Corporation to achieve its mission and to realize its vision and goals. Developing the Business Architecture is the first step in creating an Enterprise Architecture (EA) that links the Corporation's business needs to its Information Technology (IT) environment. Maximizing IT support for these requirements will optimize Corporate performance.
- Data Architecture : The Data Architecture describes the activities required to obtain and maintain data that supports the information needed by the Corporation’s major business areas. Data and information are different. Data is the foundation of information. Data is the raw material that is processed and refined to generate information. Information consists of a collection of related data that has been processed into a form that is meaningful to the recipient.
- Applications Architecture : The Applications Architecture describes the major types of applications that manage data to produce the information needed to support the activities of the Corporation. The Applications Architecture provides a framework that enables the migration from the current applications catalog and software development environment to the target integrated applications, development and engineering environments. The target architecture promotes the use of commercial and government off-the-shelf products, consolidating applications, where applicable, and the use of emerging technologies where appropriate.
- Technical Infrastructure Architecture : The IT infrastructure provides access to application systems and office automation tools used in performance of the business processes. The Corporation places high priority on maintaining a consistent, available, and reliable technical infrastructure. The Technical Architecture describes the underlying technology for the Corporation's business, data, and application processing. It includes the technologies used for communications, data storage, application processing, and computing platforms.
- Security Architecture : The Security Architecture establishes a framework for integrating safeguards into all layers of the FDIC's Enterprise Architecture. The security architecture uses a risk management and information assurance strategy that provides access control, confidentiality, integrity, and non-repudiation for the Corporation's information and systems.
Future IT development
The banking business model has become more complex, giving rise to financial instruments such as collateralized debt obligations (CDOs) and structured investment vehicles (SIVs) to manage risk. These instruments have created greater dependencies between the domestic and international financial markets. Financial institutions must, therefore, strike a balance between regulatory, legislative and banker concerns while appropriately managing risk.
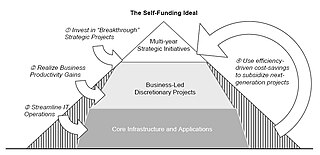
As cost savings are realized from a simplified IT environment and more efficient processes, the savings will be reinvested for IT improvements or accrue to the Corporation. This self-funding model is shown on the right.
Five-year technology roadmap
The technology roadmap outlines the major initiatives for standardizing the IT environment and increasing IT’s efficiency and effectiveness over the next five years. The initiatives were determined by various sources including business-side IT roadmaps, executive management planning meetings, client planning sessions, and client year-end reviews. The three major initiatives identified are enterprise architecture, security and privacy programs, and fiscal discipline.
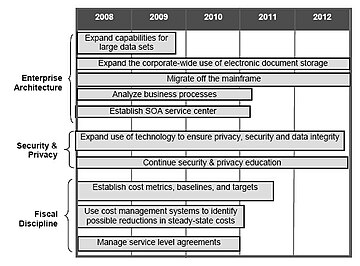
The enterprise architecture initiative will focus on simplifying the environment to ensure stable and economical performance for mission-critical applications. Simplifying the environment to decrease costs will include activities, such as decreasing the number of application systems and migrating applications off the mainframe. Efficiencies will also be gained by expanding capabilities for manipulating large data sets and storing traditional paper-based files electronically. The SOA service center will manage code (or services) for all development teams to discover and use, which will save time and costs in application development, testing and deployment.
The organization will continue to enhance IT security and privacy programs to address new and evolving risks by improving controls over sensitive data. In some cases, technology, such as scanning outgoing e-mail for sensitive information and encrypting removable storage devices, can mitigate potential risks. The other cornerstone of mitigating risk is educating employees of emerging security and privacy issues.
Lastly, in order to continue sound fiscal discipline and responsibility, the organization will establish IT baselines and metrics, study steady-state costs, manage service level agreements, and more judiciously choose new development projects. These three areas – enterprise architecture, security and privacy programs, and fiscal discipline – are shown below with the estimated time frames.
See also
References
- OIG (2005). Implementation of E-Government Principles. May 2005
- ^ Implementation of E-Government Principles AUDIT REPORT, Report No. 05-018, May 2005
- FDIC (2003). Information Technology Strategic Plan 2004–2007
- Gregg Kreizman, Cathleen E. Blanton (2005) "The FDIC Is Aligning IT to Business Through Enterprise Architecture" Gartner, Inc.
- FDIC Receives Technology Award
- ^ CIO Council (2008) Information Technology Strategic Plan 2008–2013, January 23, 2008.
Further reading
- Gartner (2005) The FDIC Is Aligning IT to Business Through Enterprise Architecture. Industrial research paper.
- Pallab Saha (2007). Handbook of Enterprise Systems Architecture in Practice. Chapter IX gives a detailed case study of the FDIC.
External links
- FDIC Homepage.