| This article needs additional citations for verification. Please help improve this article by adding citations to reliable sources. Unsourced material may be challenged and removed. Find sources: "Bibliography of cryptography" – news · newspapers · books · scholar · JSTOR (January 2017) (Learn how and when to remove this message) |
Books on cryptography have been published sporadically and with variable quality for a long time. This is despite the paradox that secrecy is of the essence in sending confidential messages – see Kerckhoffs' principle.
In contrast, the revolutions in cryptography and secure communications since the 1970s are covered in the available literature.
Early history
An early example of a book about cryptography was a Roman work, now lost and known only by references. Many early cryptographic works were esoteric, mystical, and/or reputation-promoting; cryptography being mysterious, there was much opportunity for such things. At least one work by Trithemius was banned by the Catholic Church and put on the Index Librorum Prohibitorum as being about black magic or witchcraft. Many writers claimed to have invented unbreakable ciphers. None were, though it sometimes took a long while to establish this.
In the 19th century, the general standard improved somewhat (e.g., works by Auguste Kerckhoffs, Friedrich Kasiski, and Étienne Bazeries). Colonel Parker Hitt and William Friedman in the early 20th century also wrote books on cryptography. These authors, and others, mostly abandoned any mystical or magical tone.
Open literature versus classified literature
With the invention of radio, much of military communications went wireless, allowing the possibility of enemy interception much more readily than tapping into a landline. This increased the need to protect communications. By the end of World War I, cryptography and its literature began to be officially limited. One exception was the 1931 book The American Black Chamber by Herbert Yardley, which gave some insight into American cryptologic success stories, including the Zimmermann telegram and the breaking of Japanese codes during the Washington Naval Conference.
List
Overview of cryptography
- Bertram, Linda A. / Dooble, Gunther van / et al. (Eds.): Nomenclatura: Encyclopedia of modern Cryptography and Internet Security - From AutoCrypt and Exponential Encryption to Zero-Knowledge-Proof Keys, 2019, ISBN 9783746066684.
- Piper, Fred and Sean Murphy, Cryptography : A Very Short Introduction ISBN 0-19-280315-8 This book outlines the major goals, uses, methods, and developments in cryptography.
Significant books
Significant books on cryptography include:
- Aumasson, Jean-Philippe (2017), Serious Cryptography: A Practical Introduction to Modern Encryption. No Starch Press, 2017, ISBN 9781593278267. Presents modern cryptography in a readable way, suitable for practitioners, software engineers, and others who want to learn practice-oriented cryptography. Each chapter includes a discussion of common implementation mistakes using real-world examples and details what could go wrong and how to avoid these pitfalls.
- Aumasson, Jean-Philippe (2021), Crypto Dictionary: 500 Tasty Tidbits for the Curious Cryptographer. No Starch Press, 2021, ISBN 9781718501409. Ultimate desktop dictionary with hundreds of definitions organized alphabetically for all things cryptographic. The book also includes discussions of the threat that quantum computing is posing to current cryptosystems and a nod to post-quantum algorithms, such as lattice-based cryptographic schemes.
- Bertram, Linda A. / Dooble, Gunther van: Transformation of Cryptography - Fundamental concepts of Encryption, Milestones, Mega-Trends and sustainable Change in regard to Secret Communications and its Nomenclatura, 2019, ISBN 978-3749450749.
- Candela, Rosario (1938). The Military Cipher of Commandant Bazeries. New York: Cardanus Press, This book detailed the cracking of a famous code from 1898 created by Commandant Bazeries, a brilliant French Army Cryptanalyst.
- Falconer, John (1685). Cryptomenysis Patefacta, or Art of Secret Information Disclosed Without a Key. One of the earliest English texts on cryptography.
- Ferguson, Niels, and Schneier, Bruce (2003). Practical Cryptography, Wiley, ISBN 0-471-22357-3. A cryptosystem design consideration primer. Covers both algorithms and protocols. This is an in-depth consideration of one cryptographic problem, including paths not taken and some reasons why. At the time of its publication, most of the material was not otherwise available in a single source. Some was not otherwise available at all. According to the authors, it is (in some sense) a follow-up to Applied Cryptography.
- Gaines, Helen Fouché (1939). Cryptanalysis, Dover, ISBN 0-486-20097-3. Considered one of the classic books on the subject, and includes many sample ciphertext for practice. It reflects public amateur practice as of the inter-War period. The book was compiled as one of the first projects of the American Cryptogram Association.
- Goldreich, Oded (2001 and 2004). Foundations of Cryptography. Cambridge University Press. Presents the theoretical foundations of cryptography in a detailed and comprehensive manner. A must-read for anyone interested in the theory of cryptography.
- Katz, Jonathan and Lindell, Yehuda (2007 and 2014). Introduction to Modern Cryptography, CRC Press. Presents modern cryptography at a level appropriate for undergraduates, graduate students, or practitioners. Assumes mathematical maturity but presents all the necessary mathematical and computer science background.
- Konheim, Alan G. (1981). Cryptography: A Primer, John Wiley & Sons, ISBN 0-471-08132-9. Written by one of the IBM team who developed DES.
- Mao, Wenbo (2004). Modern Cryptography Theory and Practice ISBN 0-13-066943-1. An up-to-date book on cryptography. Touches on provable security, and written with students and practitioners in mind.
- Mel, H.X., and Baker, Doris (2001). Cryptography Decrypted, Addison Wesley ISBN 0-201-61647-5. This technical overview of basic cryptographic components (including extensive diagrams and graphics) explains the evolution of cryptography from the simplest concepts to some modern concepts. It details the basics of symmetric key, and asymmetric key ciphers, MACs, SSL, secure mail and IPsec. No math background is required, though there's some coverage of the mathematics underlying public key/private key crypto in the appendix.
- A. J. Menezes, P. C. van Oorschot, and S. A. Vanstone (1996) Handbook of Applied Cryptography ISBN 0-8493-8523-7. Equivalent to Applied Cryptography in many ways, but somewhat more mathematical. For the technically inclined. Covers few meta-cryptographic topics, such as crypto system design. This is currently (2004) regarded as the standard reference work in technical cryptography.
- Paar, Christof and Jan Pelzl (2009). Understanding Cryptography: A Textbook for Students and Practitioners, Springer, ISBN 978-3-642-04100-6. Very accessible introduction to applied cryptography which covers most schemes of practical relevance. The focus is on being a textbook, i.e., it has pedagogical approach, many problems and further reading sections. The main target audience are readers without a background in pure mathematics.
- Patterson, Wayne (1987). Mathematical Cryptology for Computer Scientists and Mathematicians, Rowman & Littlefield, ISBN 0-8476-7438-X
- Rosulek, Mike (2018). The Joy of Cryptography Presents modern cryptography at a level appropriate for undergraduates.
- Schneier, Bruce (1996). Applied Cryptography, 2 ed, Wiley, (ISBN 0-471-11709-9). Survey of mostly obsolete cryptography with some commentary on 1990s legal environment. Aimed at engineers without mathematical background, including source code for obsolete ciphers. Lacks guidance for choosing cryptographic components and combining them into protocols and engineered systems. Contemporaneously influential on a generation of engineers, hackers, and cryptographers. Supplanted by Cryptography Engineering.
- Smart, Nigel (2004). Cryptography: An introduction ISBN 0-07-709987-7. Similar in intent to Applied Cryptography but less comprehensive. Covers more modern material and is aimed at undergraduates covering topics such as number theory and group theory not generally covered in cryptography books.
- Stinson, Douglas (2005). Cryptography: Theory and Practice ISBN 1-58488-508-4. Covers topics in a textbook style but with more mathematical detail than is usual.
- Young, Adam L. and Moti Yung (2004). Malicious Cryptography: Exposing Cryptovirology, ISBN 0764568469, ISBN 9780764568466, John Wiley & Sons. Covers topics regarding use of cryptography as an attack tool in systems as was introduced in the 1990s: Kleptography which deals with hidden subversion of cryptosystems, and, more generally, Cryptovirology which predicted Ransomware in which cryptography is used as a tool to disable computing systems, in a way that is reversible only by the attacker, generally requiring ransom payment(s).
- Washington, Lawrence C. (2003). Elliptic Curves: Number Theory and Cryptography ISBN 1-58488-365-0. A book focusing on elliptic curves, beginning at an undergraduate level (at least for those who have had a course on abstract algebra), and progressing into much more advanced topics, even at the end touching on Andrew Wiles' proof of the Taniyama–Shimura conjecture which led to the proof of Fermat's Last Theorem.
- Welsh, Dominic (1988). Codes and Cryptography, Oxford University Press, A brief textbook intended for undergraduates. Some coverage of fundamental information theory. Requires some mathematical maturity; is well written, and otherwise accessible.
The Codebreakers
From the end of World War II until the early 1980s most aspects of modern cryptography were regarded as the special concern of governments and the military and were protected by custom and, in some cases, by statute. The most significant work to be published on cryptography in this period is undoubtedly David Kahn's The Codebreakers, which was published at a time (mid-1960s) when virtually no information on the modern practice of cryptography was available. Kahn has said that over ninety percent of its content was previously unpublished.
The book caused serious concern at the NSA despite its lack of coverage of specific modern cryptographic practice, so much so that after failing to prevent the book being published, NSA staff were informed to not even acknowledge the existence of the book if asked. In the US military, mere possession of a copy by cryptographic personnel was grounds for some considerable suspicion. Perhaps the single greatest importance of the book was the impact it had on the next generation of cryptographers. Whitfield Diffie has made comments in interviews about the effect it had on him.
Cryptographic environment/context or security
- Schneier, Bruce – Secrets and Lies, Wiley, ISBN 0-471-25311-1, a discussion of the context within which cryptography and cryptosystems work. Practical Cryptography also includes some contextual material in the discussion of crypto system design.
- Schneier, Bruce – Beyond Fear: Thinking Sensibly About Security in an Uncertain World, Wiley, ISBN 0-387-02620-7
- Anderson, Ross – Security Engineering, Wiley, ISBN 0-471-38922-6 (online version), advanced coverage of computer security issues, including cryptography. Covers much more than merely cryptography. Brief on most topics due to the breadth of coverage. Well written, especially compared to the usual standard.
- Edney, Jon and Arbaugh, William A – Real 802.11 Security: Wi-Fi Protected Access and 802.11i, Addison-Wesley, ISBN 0-321-13620-9, covers the use of cryptography in Wi-Fi networks. Includes details on Wi-Fi Protected Access (which is based on the IEEE 802.11i specification). The book is slightly out of date as it was written before IEEE 802.11i was finalized but much of the content is still useful for those who want to find out how encryption and authentication is done in a Wi-Fi network.
Declassified works
- Boak, David G. A History of U.S. Communications Security (Volumes I and II); the David G. Boak Lectures, National Security Agency (NSA), 1973, A frank, detailed, and often humorous series of lectures delivered to new NSA hires by a long time insider, largely declassified as of 2015.
- Callimahos, Lambros D. and Friedman, William F. Military Cryptanalytics. A (partly) declassified text intended as a training manual for NSA cryptanalysts.
- Friedman, William F., Six Lectures on Cryptology, National Cryptology School, U.S. National Security Agency, 1965, declassified 1977, 1984
- Friedman, William F. (October 14, 1940). "Preliminary Historical Report on the Solution of the Type "B" Machine" (PDF). Archived from the original (PDF) on April 4, 2013. (How the Japanese Purple cipher was broken, declassified 2001)
History of cryptography
- Bamford, James, The Puzzle Palace: A Report on America's Most Secret Agency (1982)(ISBN 0-14-006748-5), and the more recent Body of Secrets: Anatomy of the Ultra-Secret National Security Agency (2001). The first is one of a very few books about the US Government's NSA. The second is also about NSA but concentrates more on its history. There is some very interesting material in Body of Secrets about US attempts (the TICOM mission) to investigate German cryptographic efforts immediately as WW II wound down.
- Gustave Bertrand, Enigma ou la plus grande énigme de la guerre 1939–1945 (Enigma: the Greatest Enigma of the War of 1939–1945), Paris, 1973. The first public disclosure in the West of the breaking of Enigma, by the chief of French military cryptography prior to WW II. The first public disclosure anywhere was made in the first edition of Bitwa o tajemnice by the late Władysław Kozaczuk.
- James Gannon, Stealing Secrets, Telling Lies: How Spies and Codebreakers Helped Shape the Twentieth Century, Washington, D.C., Brassey's, 2001: an overview of major 20th-century episodes in cryptology and espionage, particularly strong regarding the misappropriation of credit for conspicuous achievements.
- Kahn, David – The Codebreakers (1967) (ISBN 0-684-83130-9) A single-volume source for cryptographic history, at least for events up to the mid-'60s (i.e., to just before DES and the public release of asymmetric key cryptography). The added chapter on more recent developments (in the most recent edition) is quite thin. Kahn has written other books and articles on cryptography, and on cryptographic history. They are very highly regarded.
- Kozaczuk, Władysław, Enigma: How the German Machine Cipher Was Broken, and How It Was Read by the Allies in World War II, edited and translated by Christopher Kasparek, Frederick, MD, 1984: a history of cryptological efforts against Enigma, concentrating on the contributions of Polish mathematicians Marian Rejewski, Jerzy Różycki and Henryk Zygalski; of particular interest to specialists will be several technical appendices by Rejewski.
- Levy, Steven – Crypto: How the Code Rebels Beat the Government—Saving Privacy in the Digital Age (2001) (ISBN 0-14-024432-8): a journalistic overview of the development of public cryptographic techniques and the US regulatory context for cryptography. This is an account of a major policy conflict.
- Singh, Simon, The Code Book (ISBN 1-85702-889-9): an anecdotal introduction to the history of cryptography. Covers more recent material than does even the revised edition of Kahn's The Codebreakers. Clearly written and quite readable. The included cryptanalytic contest has been won and the prize awarded, but the cyphertexts are still worth attempting.
- Bauer, F L, Decrypted Secrets, This book is unusual. It is both a history of cryptography, and a discussion of mathematical topics related to cryptography. In his review, David Kahn said he thought it the best book he'd read on the subject. It is essentially two books, in more or less alternating chapters. Originally in German, and the translation shows it in places. Some surprising content, e.g., in the discussion of President Edgar Hoover's Secretary of State, Henry Stimson.
- Budiansky, Stephen, Battle of Wits: a one-volume history of cryptography in WW II. It is well written, well researched, and responsible. Technical material (e.g., a description of the cryptanalysis of Enigma) is limited, but clearly presented.
- Budiansky, Stephen, Code Warriors: NSA's Codebreakers and the Secret Intelligence War Against the Soviet Union (Knopf, 2016). (ISBN 0385352662): A sweeping, in-depth history of NSA, whose famous “cult of silence” has left the agency shrouded in mystery for decades.
- Prados, John – Combined Fleet Decoded, An account of cryptography in the Pacific Theatre of World War II with special emphasis on the Japanese side. Reflects extensive research in Japanese sources and recently available US material. Contains material not previously accessible or unavailable.
- Marks, Leo, Between Silk and Cyanide: a Codemaker's Story, 1941–1945, (HarperCollins, 1998). (ISBN 0-684-86780-X). A humorous but informative account of code-making and -breaking in Britain's WWII Special Operations Executive.
- Mundy, Liza, Code Girls, (Hachette Books, 2017) (ISBN 978-0-316-35253-6) An account of some of the thousands of women recruited for U.S. cryptologic work before and during World War II, including top analysts such as Elizebeth Smith Friedman and Agnes Meyer Driscoll, lesser known but outstanding contributors like Genevieve Grotjan Feinstein and Ann Zeilinger Caracristi, and many others, and how the women made a strategic difference in the war.
- Yardley, Herbert, The American Black Chamber (ISBN 0-345-29867-5), a classic 1931 account of American code-breaking during and after World War I; and Chinese Black Chamber: An Adventure in Espionage (ISBN 0-395-34648-7), about Yardley's work with the Chinese government in the years just before World War II. Yardley has an enduring reputation for embellishment, and some of the material in these books is less than reliable. The American Black Chamber was written after the New York operation Yardley ran was shut down by Secretary of State Henry L. Stimson and the US Army, on the grounds that "gentlemen don't read each other's mail".
Historic works
- Abu Yusuf Yaqub ibn Ishaq al-Sabbah Al-Kindi, (A Manuscript on Deciphering Cryptographic Messages), 9th century included first known explanation of frequency analysis cryptanalysis
- Michel de Nostredame, (16th century prophet famed since 1555 for prognostications), known widely for his "Les Propheties" sets of quatrains composed from four languages into a ciphertext, deciphered in a series called "Rise to Consciousness" (Deschausses, M., Outskirts Press, Denver, CO, Nov 2008).
- Roger Bacon (English friar and polymath), Epistle on the secret Works of Art and Nullity of Magic, 13th century, possibly the first European work on cryptography since Classical times, written in Latin and not widely available then or now
- Johannes Trithemius, Steganographia ("Hidden Writing"), written ca. 1499; pub 1606, banned by the Catholic Church 1609 as alleged discussion of magic, see Polygraphiae (below).
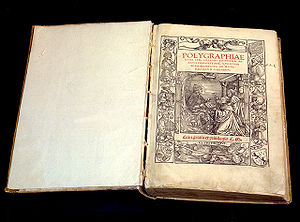
- Johannes Trithemius, Polygraphiae Libri Sex ("Six Books on Polygraphy"), 1518, first printed book on cryptography (thought to really be about magic by some observers at the time)
- Giovan Battista Bellaso, La cifra del. Sig. Giovan Battista Bellaso, 1553, first pub of the cypher widely misattributed to Vigenère.
- Giambattista della Porta, De Furtivis Literarum Notis ("On concealed characters in writing"), 1563.
- Blaise de Vigenère, Traicte de Chiffres, 1585.
- Gustavus Selenus, Cryptomenytics, 1624, (modern era English trans by J W H Walden)
- John Wilkins, Mercury, 1647, earliest printed book in English about cryptography
- Johann Ludwig Klüber, Kryptographik Lehrbuch der Geheimschreibekunst ("Cryptology: Instruction Book on the Art of Secret Writing"), 1809.
- Friedrich Kasiski, Die Geheimschriften und die Dechiffrierkunst ("Secret writing and the Art of Deciphering"), pub 1863, contained the first public description of a technique for cryptanalyzing polyalphabetic cyphers.
- Etienne Bazeries, Les Chiffres secrets dévoilés ("Secret ciphers unveiled") about 1900.
- Émile Victor Théodore Myszkowski, Cryptographie indéchiffrable: basée sur de nouvelles combinaisons rationelles ("Unbreakable cryptography"), published 1902.
- William F. Friedman and others, the Riverbank Publications, a series of pamphlets written during and after World War I that are considered seminal to modern cryptanalysis, including no. 22 on the Index of Coincidence.
Fiction
- Neal Stephenson – Cryptonomicon (1999) (ISBN 0-06-051280-6) The adventures of some World War II codebreakers and their modern-day progeny.
- Edgar Allan Poe – "The Gold-Bug" (1843) An eccentric man discovers an ancient parchment which contains a cryptogram which, when solved, leads to the discovery of buried treasure. Includes a lengthy discourse on a method of solving a simple cypher.
- Sir Arthur Conan Doyle – The Dancing Men. Holmes becomes involved in a case which features messages left lying around. They are written in a substitution cypher, which Holmes promptly discerns. Solving the cypher leads to solving the case.
- Ken Follett – The Key to Rebecca (1980), World War II spy novel whose plot revolves around the heroes' efforts to cryptanalyze a book cipher with time running out.
- Clifford B. Hicks – Alvin's Secret Code (1963), a children's novel which introduces some basics of cryptography and cryptanalysis.
- Robert Harris – Enigma (1995) (ISBN 0-09-999200-0) Novel partly set in Britain's World War II codebreaking centre at Bletchley Park.
- Ari Juels – Tetraktys (2009) (ISBN 0-9822837-0-9) Pits a classicist turned cryptographer against an ancient Pythagorean cult. Written by RSA Labs chief scientist.
- Dan Brown - Digital Fortress (1998), a thriller takes a plunge into the NSA's cryptology wing giving the readers a modern and technology oriented view of the codebreaking in vogue.
- Max Hernandez - Thieves Emporium (2013), a novel that examines how the world will change if cryptography makes fully bi-directional anonymous communications possible. A technically accurate document, it shows the effects of crypto from the citizen's standpoint rather than the NSA.
- Barry Eisler, Fault Line (2009) ISBN 978-0-345-50508-8. A thriller about a race to nab software (of the cryptovirology type) which is capable of shutting down cyberspace.
References
- Ellison, Katherine E. (2016). A cultural history of early modern English cryptography manuals. Abingdon, Oxon: Taylor & Francis. p. 58. ISBN 9781315458205.
- "Introduction to Modern Cryptography".
- Landau, Susan (2004). "Review of Handbook of Applied Cryptography by A. J. Menezes, P. C. Oorschot, and S. A. Vanstone and 9 other books by various authors" (PDF). Bull. Amer. Math. Soc. (N.S.). 41 (3): 357–367. doi:10.1090/s0273-0979-04-01011-0.
- Viega, John (2009-01-12). "The Cult of Schneier". O'Reilly Media. Archived from the original on 2009-01-16.
- Schneier, Bruce (2009-09-03). ""The Cult of Schneier"". Schneier on Security. Retrieved 2022-08-24.
- Ptacek, Thomas (2013-07-22). "Applied Cryptography Engineering". sockpuppet.org. Retrieved 2022-08-24.
- Kahn, David (1967). The Codebreakers: The Story of Secret Writing. New York: The Macmillan Company. ISBN 978-0-684-83130-5. OCLC 59019141
- The Codebreakers: The Story of Secret Writing by David Kahn, internal CIA book review by Roger Pineau, ca.1967, released to public 1996
- Cohen, Eliot A.; Kahn, David (1997). "The Codebreakers: The Comprehensive History of Secret Communication from Ancient Times to the Internet". Foreign Affairs. 76 (3): 129. doi:10.2307/20048054. ISSN 0015-7120. JSTOR 20048054.
- Singh, Simon. "Book review of The Codebreakers".
External links
- Listing and reviews for a large number of books in cryptography
- A long list of works of fiction where the use of cryptology is a significant plot element. The list is in English.
- List of where cryptography features in literature — list is presented in German. It draws on the English list above.