A clandestine cell system is a method for organizing a group of people, such as resistance fighters, spies, mercenaries, organized crime members, or terrorists, to make it harder for police, military or other hostile groups to catch them. In a cell structure, each cell consists of a relatively small number of people, who know little to no information concerning organization assets (such as member identities) beyond their cell. This limits the harm that can be done to the organization as a whole by any individual cell member defecting, being a mole, being surveilled, or giving up information after being apprehended and interrogated.
The structure of a clandestine cell system can range from a strict hierarchy to an extremely distributed organization, depending on the group's ideology, its operational area, the communications technologies available, and the nature of the mission. Criminal organizations, undercover operations, and unconventional warfare units led by special forces may also use this sort of organizational structure.
Covert operations vs. clandestine operations
Covert and clandestine operations are not the same when it comes to tradecraft. The modern NATO definition of a covert operation says the identity of the sponsor is concealed, but in a clandestine operation the operation itself is concealed from the participants. Put differently, clandestine means "hidden", and covert means "deniable"—that is to say that the sponsor of a covert action is sufficiently removed from it that the sponsor can claim ignorance in the event the plot is discovered.
A sleeper cell refers to a cell, or isolated grouping of sleeper agents, that lies dormant until it receives orders or decides to act.
History
World War II French Resistance
In World War II, Operation Jedburgh teams were formed to lead unconventional warfare against German units by acts of sabotage and leading local resistance forces. They also acted as a liaison between Allied command and the resistance units. They were composed of two officers – one American or British, and the other a native to the area they would operate, preferably from the area into which they landed – and a third member who was a radio operator. They operated in France and the Netherlands and similar teams operated in South East Asia. On the night of the 5/6 June 1944, the first Operation Jedburgh teams parachuted into occupied France
Especially through the French member, they would contact trusted individuals in the area of operation, and ask them to recruit a team of trusted subordinates (a subcell). If the mission was sabotage, reconnaissance, or espionage, there was no need to meet in large units. If the team was to carry out direct action (often an unwise mission unless an appreciable number of the locals had military experience) it would be necessary to assemble into larger units for combat. Even then, the hideouts of the leadership were known only to subcell leaders. The legitimacy of the Jedburgh team came from its known affiliation with Allied powers, and it was a structure more appropriate for unconventional warfare than for truly clandestine operations.
National Front for the Liberation of South Vietnam

Also known as the Viet Cong, this organization grew from earlier anticolonial groups fighting the French and from anti-Japanese guerrillas during World War II.
Provisional Irish Republican Army
The modern Provisional Irish Republican Army (PIRA) has a history going back to Irish revolutionary forces in the early 20th century. Its doctrine and organization have changed over time, as political, technological, and cultural situations have changed in Ireland.
Officially, the PIRA was hierarchical, but as British security forces became more effective it changed to a semiautonomous model for its operational and for certain of its support cells (such as transportation, intelligence, cover, and security). Its leadership saw itself as guiding and as building consensus. The lowest-level cells, typically of 2–5 people, tended to be built from people with existing personal relationships. British counterinsurgents could understand the command structure, but not the workings of the operational cells.
The IRA had an extensive network of inactive or sleeper cells, so it could summon new ad hoc organizations for any specific operation.
Parallel organizations
The NLF (Viet Cong) and PIRA, as well as other movements, have chosen to have parallel political and military organizations. In the case of the NLF, except for some individuals with sanctuary in North Vietnam, people in the political organization could not be overt during the Vietnam War. After the war ended, surviving NLF officials held high office.
In the case of the PIRA, its political wing, Sinn Féin, became increasingly overt, and then a full participant in politics. Hamas and Hezbollah also have variants of overt political/social service and covert military wings.
The overt political/social–covert military split postponed the inflexibility of a completely secret organization and shortage of PMC/black-ops resources as well as redundancy. Once an active insurgency began, the secrecy could limit freedom of action, distort information about goals and ideals, and restrict communication within the insurgency. In such a split organization, public issues can be addressed overtly while military actions are kept covert and intelligence functions stay clandestine.
External support
Many cell systems receive support from outside the cell. This can include leaders, trainers, and supplies (such as the Jedburgh assistance to the French Resistance), or a safe haven for overt activities (such as the NLF spokesmen who could operate in Hanoi).
External support need not be overt. Certain Shi'a groups in Iraq, for example, receive assistance from Iran, but this is not a public position of the government of Iran, and may even be limited to factions of that government. Early U.S. support to the Afghan Northern Alliance against the Taliban used clandestine operators from the CIA and United States Army Special Forces. As the latter conflict escalated, U.S. participation became overt.
Note that both unconventional warfare (guerrilla operations) and foreign internal defense (counterinsurgency) may be covert and use cellular organization.
In a covert counterinsurgency mission, only selected host nation leaders are aware of the foreign support organization. Under Operation White Star, for example, U.S. personnel gave covert counterinsurgency assistance to the Royal Lao Army starting in 1959, this became overt in 1961, and finally ceased operations in 1962.
Models of insurgency and associated cell characteristics
Different kinds of insurgency differ in where they place clandestine or covert cells. Also, when certain types of insurgency grow in power, they deemphasize the cell system. They may still use cells for leadership security, but if overt violence by organized units becomes significant, cells become less important. In Mao's three-stage doctrine, cells are still useful in Phase II to give cover to part-time guerillas, but as the insurgency creates full-time military units in Phase III, the main units become the focus, not the cells.
Different varieties of insurgency place their cells differently with respect to the existing government. The U.S. Army Field Manual FM3-07 distinguishes between varieties of insurgencies. Drawing on this work, Nyberg (a United States Marine Corps officer) describes four types of cell system (there is also a new type associated with transnational terrorist insurgencies):
- Traditional: The slowest to form, these are typically indigenous insurgencies that begin with limited goals. These are more secure than others, as they tend to form from people with preexisting social, cultural, or family ties. The insurgents resent a government that has failed to recognize tribal, racial, religious, or linguistic groups. They "perceive that the government has denied their rights and interests and work to establish or restore them. They seldom seek to overthrow the government or control the whole society; however, they frequently attempt to withdraw from government control through autonomy or semiautonomy." The Mujahideen in Afghanistan and the Kurdish revolt in Iraq are examples of this traditional pattern of insurgency. al-Qaeda generally operates in this mode, but if they become strong enough in a given area, they may change to the mass-oriented form (see below).
- Subversive: These are usually driven by an organization that contains at least some of the governing elite, some being sympathizers already in government, and others who penetrate the government. When they use violence, it has a specific purpose, such as coercing voters, intimidating officials, and disrupting and discrediting the government. Typically, there is a political arm (such as Sinn Féin or the National Liberation Front) that directs the military in planning carefully coordinated violence. "Employment of violence is designed to show the system to be incompetent and to provoke the government to an excessively violent response which further undermines its legitimacy." The Nazi rise to power, in the 1930s, is another example of subversion. Nazi members of parliament and street fighters were hardly clandestine, but the overall plan of the Nazi leadership to gain control of the nation was hidden. "A subversive insurgency is suited to a more permissive political environment which allows the insurgents to use both legal and illegal methods to accomplish their goals. Effective government resistance may convert this to a critical-cell model.
- Critical-cell: These come into play when the political climate becomes less permissive than one that allowed shadow cells. While other cell systems try to form intelligence cells within the government, this type sets up "shadow government" cells that can seize power once the status quo is overthrown. This model includes the classic coup d'etat, and often tries to minimize violence. Examples include the Sandinista takeover of an existing government weakened by external popular revolution, or the Gülen movement in Turkey. "Insurgents also seek to infiltrate the government's institutions, but their object is to destroy the system from within." Clandestine cells form inside the government. "The use of violence remains covert until the government is so weakened that the insurgency's superior organization seizes power, supported by the armed force. One variation of this pattern is when the insurgent leadership permits the popular revolution to destroy the existing government, then emerges to direct the formation of a new government. Another variation is seen in the Cuban revolution and is referred to as the foco (or Cuban model) insurgency. This model involves a single, armed cell which emerges in the midst of degenerating government legitimacy and becomes the nucleus around which mass popular support rallies. The insurgents use this support to establish control and erect new institutions."
- Mass-oriented: While the subversive and covert-cell systems work from within the government, the mass-oriented system builds a government completely outside the existing one, with the intention of replacing it. Such "insurgents patiently construct a base of passive and active political supporters, while simultaneously building a large armed element of guerrilla and regular forces. They plan a protracted campaign of increasing violence to destroy the government and its institutions from the outside. They have a well-developed ideology and carefully determine their objectives. They are highly organized and effectively use propaganda and guerrilla action to mobilize forces for a direct political and military challenge to the government." The revolution that produced the People's Republic of China, the American Revolution, and the Shining Path insurgency in Peru are examples of the mass-oriented model. Once established, this type of insurgency is extremely difficult to defeat because of its great depth of organization.
Classic models for cell system operations
The examples here will use CIA cryptonyms as a naming convention used to identify members of the cell system. Cryptonyms begin with a two-letter country or subject name (e.g., AL), followed by more letters so as to form an arbitrary word, such as "BERRY", "BEN", and "BEATLE" in the example below.
Operations under official cover
Station BERRY operates, on behalf of country B, in target country BE. The station has three case officers and several support officers. Case officer BETTY supervises the local agents BEN and BEATLE. Case officer BESSIE supervises BENSON and BEAGLE.

Some recruits, due to the sensitivity of their position or their personalities not being appropriate for cell leadership, might not enter cells but be run as singletons, perhaps by other than the recruiting case officer. In this example, asset BARD is a different sort of highly sensitive singleton, who is a joint asset of the country B, and the country identified by prefix AR. ARNOLD is a case officer from the country AR embassy, who knows only the case officer BERTRAM and the security officer BEST. ARNOLD does not know the station chief of BERRY or any of its other personnel. Other than BELL and BEST, the Station personnel only know BERTRAM as someone authorized to be in the Station, and who is known for his piano playing at embassy parties. He is covered as Cultural Attache, in a country that has very few pianos. Only the personnel involved with BARD know that ARNOLD is other than another friendly diplomat.
In contrast, BESSIE and BETTY know one another, and procedures exist for their taking over each other's assets in the event one of the two is disabled.
Some recruits, however, would be qualified to recruit their own subcell, as BEATLE has done. BETTY knows the identity of BEATLE-1 and BEATLE-2, since he or she had them checked by headquarters counterintelligence before they were recruited.
Clandestine presence
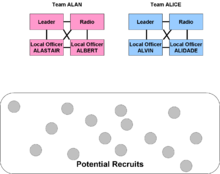
The diagram in this section shows that two teams, ALAN and ALICE, have successfully entered an area of operation, the country coded AL, but are only aware of a pool of potential recruits, and have not yet actually recruited anyone. They communicate with one another only through headquarters, so compromise of one team will not affect the other.
Assume that in team ALAN, ALASTAIR is one of the officers with local contacts, and might recruit two cell leaders: ALPINE and ALTITUDE. The other local officer in the team, ALBERT, recruits ALLOVER. When ALPINE recruited two subcell members, they would be referred to as ALPINE-1 and ALPINE-2.
ALPINE and ALTITUDE only know how to reach ALASTAIR, but they are aware of at least some of other team members' identities should ALASTAIR be unavailable, and they would accept a message from ALBERT. Most often, the identity (and location) of the radio operator may not be shared. ALPINE and ALTITUDE, however, do not know one another. They do not know any of the members of team ALICE.
The legitimacy of the subcell structure came from the recruitment process, originally by the case officer and then by the cell leaders. The cell leader might propose subcell member names to the case officer, so the case officer could have headquarters run a background check on the potential recruit before bringing them into the subcell. In principle, however, the subcell members would know ALPINE, and sometimes the other members of the ALPINE cell if they needed to work together; if ALPINE-1 and ALPINE-2 had independent assignments, they might not know each other. ALPINE-1 and ALPINE-2 certainly would not know ALASTAIR or anyone in the ALTITUDE or ALLOVER cells.
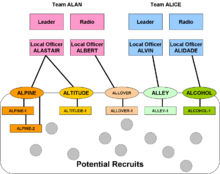
As the networks grow, a subcell leader might create her or his own cell, so ALPINE-2 might become the leader of the ALIMONY cell.
Fault-tolerant cellular structures
Modern communications theory has introduced methods to increase fault tolerance in cell organizations. Game theory and graph theory have been applied to the study of optimal covert network design.
In the past, if cell members only knew the cell leader, and the leader was neutralized, the cell was cut off from the rest of the organization. But if a traditional cell had independent communications with the foreign support organization, headquarters might be able to arrange its reconnection. Another method is to have impersonal communications as "side links" between cells, such as a pair of dead drops, one for Team ALAN to leave "lost contact" messages to be retrieved by Team ALICE, and another dead drop for Team ALICE to leave messages for Team ALAN.
These links, to be used only on losing contact, do not guarantee a contact. When a team finds a message in its emergency drop, it might do no more than send an alert message to headquarters. Headquarters might determine, through SIGINT or other sources, that the enemy had captured the leadership and the entire team, and order the other team not to attempt contact. If headquarters can have reasonable confidence that there is a communications failure or partial compromise, it might send a new contact to the survivors.
When the cut-off team has electronic communications, such as the Internet, it has a much better chance of eluding surveillance and getting emergency instructions than by using a dead drop that can be under physical surveillance.
Non-traditional models, exemplified by al-Qaeda
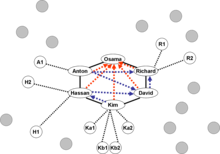
If the al-Qaeda Training Manual is authentic, it demonstrates that Eastern cell structures may differ from the Western mode. Al-Qaeda's minimal core leadership group can be viewed as a ring or chain network, with each leader/node heading their own particular hierarchy.
Such networks function by having their sub-networks provide information and other forms of support (the 'many-to-one' model), while the core group supplies 'truth' and decisions/directions (the 'one-to-many' model). Trust and personal relationships are an essential part of the Al-Qaeda network (a limiting factor, even while it provides enhanced security). Cell members are trained as 'replaceable' units and 'vetting' of members occurs during the training period under the observation of the core group.
Cells of this structure are built outwards, from an internal leadership core. Superficially, this might be likened to a Western cell structure that emanates from a headquarters, but the Western centrality is bureaucratic, while structures in other non-Western cultures build on close personal relationships, often built over years, perhaps involving family or other in-group linkages. Such in-groups are thus extremely hard to infiltrate. Still, it may be possible for an in-group to be compromised through COMINT or, in rare cases, by compromising a member.
The core group is a ring, superimposed on an inner hub-and-spoke structure of ideological authority. Each member of the core forms another hub and spoke system, the spokes leading to infrastructure cells under the supervision of the core group member, and possibly to operational groups that the headquarters supports. In an organization like this, there is a point at which the operational cell becomes autonomous of the core. Members surviving the operation may rejoin at various points.

Osama bin Laden, in this model, had the responsibility of commanding the organization and being the spokesman on propaganda messages distributed by the propaganda cell. The other members of the core each command one or more infrastructure cells.
While the tight coupling enhances security, it can limit flexibility and the ability to scale the organization. The in-group values that tie the cell together initially, shared cultural and ideological values, are not sufficient to create additional loyalty to a bureaucratic process.
"Members of the core group are under what could be termed 'positive control'—long relationships and similar mindsets make 'control' not so much of an issue, but there are distinct roles, and position (structural, financial, spiritual) determines authority, thus making the core group a hierarchy topologically."
In the illustration of the core shown here, each member knows how to reach two other members, and also knows the member(s) he or she considers her or his ideological superior. Solid lines show basic communication, dotted red arrows show the first level of ideological respect, and dotted blue arrows show a second level of ideological respect.
If Osama, the most respected, died, the core would reconstitute itself. While different members each have an individual ideological guide, and these are not the same for all members, the core would reconstitute itself with (in our example) Richard as most respected.
Assume there are no losses, and Osama can be reached directly only by members of the core group. Members of outer cells and support systems might know him only as "the Commander", or, as in the actual case of al-Qaeda, Osama bin Laden's face is recognizable worldwide, but only a few people knew where he was or even how to contact him.
Infrastructure cells
Any clandestine or covert service, especially a non-national one, needs a variety of technical and administrative functions, such as:
- Recruitment/training
- Forged documents/counterfeit currency
- Finance/Fundraising
- Communications
- Transportation/Logistics
- Safehouses
- Reconnaissance/Counter-surveillance
- Operational planning
- Arms and ammunition
- Psychological operations
A national intelligence service has a support organization to deal with services like finance, logistics, facilities (e.g., safehouses), information technology, communications, training, weapons and explosives, medical services, etc. Transportation alone is a huge function, including the need to buy tickets without drawing suspicion, and, where appropriate, using private vehicles. Finance includes the need to transfer money without coming to the attention of financial security organizations.
Some of these functions, such as finance, are far harder to operate in remote areas (like the FATA of Pakistan) than in cities with large numbers of official and unofficial financial institutions and the communications to support them. If the financial office is distant from the remote headquarters, there is a need for couriers, who must be trusted to some extent, but who may not know the contents of their messages or the actual identity of the sender and/or receiver. The couriers, depending on the balance among type and size of message, security, and technology available, may memorize messages, carry audio or video recordings, or hand-carry computer media.
These cells are socially embedded (less so than the core group, however), structurally embedded, functionally embedded (they are specialized into a domain), and knowledge base-specific (there does not seem to be a great deal of cross-training or lateral mobility in the organization). Such cells are probably subjected to a mixture of both positive and negative control ('do this, do these sorts of things, don't do that').
| Member | Infrastructure commanded |
|---|---|
| Richard | Finance |
| Anton | Military training/operations 1 |
| Hassan | Military training/operations 2 |
| David | Transportation |
| Kim | Communications and propaganda |
The leader of a military cell is responsible for training its members, and, when an operation is scheduled, selecting the operational commander, giving her or him the basic objective and arranging whatever support is needed, and then releasing her or him from tight control to execute the meeting. Military leaders might have direct, possibly one-way, communications with their cells, or they might have to give Kim the messages to be transmitted, by means that Anton and Hassan have no need to know.
Note that Anton does not have a direct connection to Kim. Under normal circumstances, he sacrifices efficiency for security, by passing communications requests through Hassan. The security structure also means that Hassan does not know the members of Anton's cells, and Kim may know only ways to communicate with them but not their identity.
Kim operates two systems of cells, one for secure communications and one for propaganda. To send out a propaganda message, Osama must pass it to Kim. If Kim were compromised, the core group might have significant problems with any sort of outside communications.
Terrorist networks do not match cleanly to other cell systems that regularly report to a headquarters. The apparent al-Qaeda methodology, of letting operational cells decide on their final dates and means of attack, exhibits an operational pattern, but not a periodicity that could easily be used for an indications checklist appropriate for a warning center. Such lists depend on seeing a local pattern to give a specific warning.
Note that Hassan has two subordinates that have not yet established operational cells. These subordinates can be considered sleepers, but not necessarily with a sleeper cell.
Operational cells
For each mission, one or more operational cells are created. If al-Qaeda uses its typical modus operandi of multiple concurrent attacks, there may be an operational cell for each target location. Some operations may need support cells in the operational area. For example, it may be more secure to have a local cell build bombs, which will be delivered by cells coming from outside the area.
Operational cells are not created, but instead 'seeded' utilizing individuals spotted or that request assistance (both groups are 'vetted' by being trained under the observation of the core group, which dramatically restricts the opportunity for passing off walk-ins under false flag). Categorization of operational cells appears to be by capabilities, region, and then task/operation. Operational cells are composed of members whose worldview has been firmly tested—necessary to front-load, because such cells are dispersed back to their own local control (or negative control—proscribed behavior—with positive control only coming in the form of contact for synchronization or support).
U.S. special operations forces sometimes wait for presidential authorization to make an attack, or even to move to staging areas. A country would have to face the consequences of an inappropriate attack, so it may tend to be overcautious, whereas a terror network might merely shrug at the world being upset. Assuming that the al-Qaeda operational technique is not to use positive control, their operations may be more random, but also more unpredictable for counterterror forces. If their cells need constant control, there are communications links that might be detected by SIGINT, and if their command can be disrupted, the field units could not function. Since there is fairly little downside for terrorists to attack out of synchronization with other activities, the lack of positive control becomes a strength of their approach to cell organization.

Operational cells need to have continuous internal communication; there is a commander, who may be in touch with infrastructure cells or, less likely from a security standpoint, with the core group.
Al-Qaeda's approach differs from that of earlier terrorist organizations:
- Cells are redundant and distributed, making them difficult to "roll up"
- Cells are coordinated, not under "command smf control"—this autonomy and local control makes them flexible and enhances security
- Trust internally to the cell provide redundancy of potential command (a failure of Palestinian operations in the past), as well as a shared knowledge base (which may mean, over time, that cross-training emerges inside a cell, providing redundancy of most critical skills and knowledge).
Indirect support networks
In the above graphic, note the indirect support network controlled by Richard's subcell.
"While Al-Qaeda has elements of the organization designed to support the structure, but such elements are insufficient in meeting the needs of such an organization, and for security reasons there would be redundant and secondary-/tertiary-networks that are unaware of their connection to Al-Qaeda. These networks, primarily related to fundraising and financial activities, as well as technology providers, are in a 'use' relationship with Al-Qaeda—managed through cut-outs or individuals that do not inform them of the nature of activities, and that may have a cover pretext sufficient to deflect questions or inquiry."
A possible countermeasure
In 2002, U.S. News & World Report said that American intelligence was beginning to acquire intelligence on al-Qaeda indicating that "nce thought nearly impossible to penetrate, al-Qaeda is proving no tougher a target than the KGB or the Mafia—closed societies that took the U.S. government years to get inside. 'We're getting names, the different camps they trained at, the hierarchy, the infighting,' says an intelligence official. 'It's very promising.'" The report also said that the collected data has allowed the recruiting of informants.
Writing in the U.S. Army journal Military Review, David W. Pendall suggested that a "catch-and-release program for suspected operatives might create reluctance or distrust in such suspects and prevent them from further acts or, perhaps more important, create distrust in the cell leaders of these individuals in the future." The author noted the press release describing Ramzi bin al-Shibh's cooperation with the United States is "sure to prevent reentry into a terrorist cell as a trusted member and most likely limits the further trust and assignments of close cell associates still at large. The captor would determine when to name names and when to remain silent." Indeed, once intelligence learns the name and characteristics of an at-large adversary, as well as some sensitive information that would plausibly be known to him, a news release could be issued to talk about his cooperation. Such a method could not be used too often, but, used carefully, could disturb the critical trust networks. The greatest uncertainty might be associated with throwing doubt onto a key member of an operational cell that has gone autonomous.
See also
References
- Hall, Roger (1964). You're Stepping on my Cloak and Dagger. Bantam Books.
- Hogan, David W. (1992). "Chapter 3: Special Operations in the European Theater". U.S. Army Special Operations in World War II. Washington, D.C.: United States Army Center of Military History. CMH Pub 70-42. Archived from the original on 23 August 2020. Retrieved 12 July 2010.
- Pike, Douglas (1970). Viet Cong: Organization and Technique of the National Liberation Front of South Vietnam. MIT Press.
- Leahy, Kevin C. (2005). "The Impact of Technology on the Command, Control, and Organizational Structure of Insurgent Groups" (PDF). Archived from the original (PDF) on 30 May 2008.
- Irish Republican Army. "The Green Book". Archived from the original on 30 May 2008. Retrieved 4 December 2007.
- US Department of the Army (December 2006). "FM 3–24: Counterinsurgency" (PDF).
- Mao, Zedong (1967). On Protracted War. Foreign Language Press, Beijing.
- US Department of the Army (20 February 2003). "FM 3-07 (formerly FM 100-20): Stability Operations and Support Operations". Archived from the original on 27 June 2007. Retrieved 2 February 2008.
- Nyberg, Eric N. (1991). "Insurgency: The Unsolved Mystery". US Marine Corps University Command and Staff College.
{{cite journal}}: Cite journal requires|journal=(help) - Luttwak, Edward (1968). Coup d'etat: A Practical Handbook. Harvard University Press.
- Guevara, Ernesto "Che" (1961). On Guerilla Warfare. Praeger.
- Lindelauf, R.H.A. et al. 2009. "The influence of secrecy on the communication structure of covert networks" Social Networks 31: 126
- "al-Qaeda training manual" (PDF). US Southern District Court, US New York City Attorney's Office, entered as evidence in Africa embassy bombings.
- ^ Decision Support Systems, Inc. (31 December 2001). "Hunting the Sleepers: Tracking al-Qaida's Covert Operatives" (PDF). Archived from the original (PDF) on 28 November 2007.
- US Central Intelligence Agency. "Support to Mission: Who We Are". Archived from the original on 12 June 2007. Retrieved 19 November 2007.
- Fellman, Philip Vos; Wright, Roxana. "Modeling Terrorist Networks – Complex Systems at the Mid-Range" (PDF). Archived from the original (PDF) on 8 July 2007.
- Kaplan, David E. (22 September 2002). "Run and Gun: Al Qaeda arrests and intelligence hauls bring new energy to the war on terrorism". U.S. News & World Report.
- Pendall, David W. (January–February 2004). "Effects-Based Operations and the Exercise of National Power". Military Review. United States Army Combined Arms Center. Archived from the original on 30 March 2008. Retrieved 4 July 2019. Find the article by going through the Military Review directories
| Intelligence management | |||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Collection |
| ||||||||||||||
| Analysis | |||||||||||||||
| Dissemination | |||||||||||||||
| Terrorism | ||
|---|---|---|
| Main articles |  | |
| By ideology | ||
| Types and tactics | ||
| State involvement | ||
| Organisation | ||
| Historical | ||
| Lists | ||
| Memorials and museums | ||
| By country | ||