A direct function (dfn, pronounced "dee fun") is an alternative way to define a function and operator (a higher-order function) in the programming language APL. A direct operator can also be called a dop (pronounced "dee op"). They were invented by John Scholes in 1996. They are a unique combination of array programming, higher-order function, and functional programming, and are a major distinguishing advance of early 21st century APL over prior versions.
A dfn is a sequence of possibly guarded expressions (or just a guard) between { and }, separated by ⋄ or new-lines, wherein ⍺ denotes the left argument and ⍵ the right, and ∇ denotes recursion (function self-reference). For example, the function PT tests whether each row of ⍵ is a Pythagorean triplet (by testing whether the sum of squares equals twice the square of the maximum).
PT← {(+/⍵*2)=2×(⌈/⍵)*2}
PT 3 4 5
1
x
4 5 3
3 11 6
5 13 12
17 16 8
11 12 4
17 15 8
PT x
1 0 1 0 0 1
The factorial function as a dfn:
fact← {0=⍵:1 ⋄ ⍵×∇ ⍵-1}
fact 5
120
fact¨ ⍳10 ⍝ fact applied to each element of 0 to 9
1 1 2 6 24 120 720 5040 40320 362880
Description
The rules for dfns are summarized by the following "reference card":
{⍺ function ⍵}
|
{⍺⍺ operator ⍵⍵}
|
: guard
|
⍺ left argument
|
⍺⍺ left operand
|
:: error-guard
|
⍵ right argument
|
⍵⍵ right operand
|
⍺← default left argument
|
∇ self-reference
|
∇∇ self-reference
|
s← shy result
|
A dfn is a sequence of possibly guarded expressions (or just a guard) between { and }, separated by ⋄ or new-lines.
expression guard: expression guard:
The expressions and/or guards are evaluated in sequence. A guard must evaluate to a 0 or 1; its associated expression is evaluated if the value is 1. A dfn terminates after the first unguarded expression which does not end in assignment, or after the first guarded expression whose guard evaluates to 1, or if there are no more expressions. The result of a dfn is that of the last evaluated expression. If that last evaluated expression ends in assignment, the result is "shy"—not automatically displayed in the session.
Names assigned in a dfn are local by default, with lexical scope.
⍺ denotes the left function argument and ⍵ the right; ⍺⍺ denotes the left operand and ⍵⍵ the right. If ⍵⍵ occurs in the definition, then the dfn is a dyadic operator; if only ⍺⍺ occurs but not ⍵⍵, then it is a monadic operator; if neither ⍺⍺ or ⍵⍵ occurs, then the dfn is a function.
The special syntax ⍺←expression is used to give a default value to the left argument if a dfn is called monadically, that is, called with no left argument. The ⍺←expression is not evaluated otherwise.
∇ denotes recursion or self-reference by the function, and ∇∇ denotes self-reference by the operator. Such denotation permits anonymous recursion.
Error trapping is provided through error-guards, errnums::expression. When an error is generated, the system searches dynamically through the calling functions for an error-guard that matches the error. If one is found, the execution environment is unwound to its state immediately prior to the error-guard's execution and the associated expression of the error-guard is evaluated as the result of the dfn.
Additional descriptions, explanations, and tutorials on dfns are available in the cited articles.
Examples
The examples here illustrate different aspects of dfns. Additional examples are found in the cited articles.
Default left argument
The function {⍺+0j1×⍵} adds ⍺ to 0j1 (i or ) times ⍵.
3 {⍺+0j1×⍵} 4
3J4
∘.{⍺+0j1×⍵}⍨ ¯2+⍳5
¯2J¯2 ¯2J¯1 ¯2 ¯2J1 ¯2J2
¯1J¯2 ¯1J¯1 ¯1 ¯1J1 ¯1J2
0J¯2 0J¯1 0 0J1 0J2
1J¯2 1J¯1 1 1J1 1J2
2J¯2 2J¯1 2 2J1 2J2
The significance of this function can be seen as follows:
Complex numbers can be constructed as ordered pairs of real numbers, similar to how integers can be constructed as ordered pairs of natural numbers and rational numbers as ordered pairs of integers. For complex numbers,
{⍺+0j1×⍵}plays the same role as-for integers and÷for rational numbers.
Moreover, analogous to that monadic -⍵ ⇔ 0-⍵ (negate) and monadic ÷⍵ ⇔ 1÷⍵ (reciprocal), a monadic definition of the function is useful, effected by specifying a default value of 0 for ⍺: if j←{⍺←0 ⋄ ⍺+0j1×⍵}, then j ⍵ ⇔ 0 j ⍵ ⇔ 0+0j1×⍵.
j←{⍺←0 ⋄ ⍺+0j1×⍵}
3 j 4 ¯5.6 7.89
3J4 3J¯5.6 3J7.89
j 4 ¯5.6 7.89
0J4 0J¯5.6 0J7.89
sin← 1∘○
cos← 2∘○
Euler← {(*j ⍵) = (cos ⍵) j (sin ⍵)}
Euler (¯0.5+?10⍴0) j (¯0.5+?10⍴0)
1 1 1 1 1 1 1 1 1 1
The last expression illustrates Euler's formula on ten random numbers with real and imaginary parts in the interval .
Single recursion
The ternary construction of the Cantor set starts with the interval and at each stage removes the middle third from each remaining subinterval:
The Cantor set of order ⍵ defined as a dfn:
Cantor← {0=⍵:,1 ⋄ ,1 0 1 ∘.∧ ∇ ⍵-1}
Cantor 0
1
Cantor 1
1 0 1
Cantor 2
1 0 1 0 0 0 1 0 1
Cantor 3
1 0 1 0 0 0 1 0 1 0 0 0 0 0 0 0 0 0 1 0 1 0 0 0 1 0 1
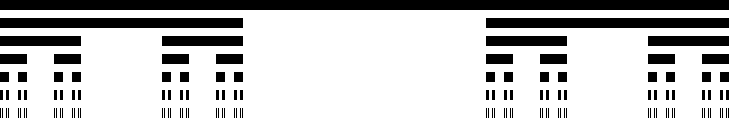
Cantor 0 to Cantor 6 depicted as black bars:
The function sieve ⍵ computes a bit vector of length ⍵ so that bit i (for 0≤i and i<⍵) is 1 if and only if i is a prime.
sieve←{
4≥⍵:⍵⍴0 0 1 1
r←⌊0.5*⍨n←⍵
p←2 3 5 7 11 13 17 19 23 29 31 37 41 43
p←(1+(n≤×⍀p)⍳1)↑p
b← 0@1 ⊃ {(m⍴⍵)>m⍴⍺↑1 ⊣ m←n⌊⍺×≢⍵}⌿ ⊖1,p
{r<q←b⍳1:b⊣b←1 ⋄ b←0 ⋄ ∇ ⍵,q}p
}
10 10 ⍴ sieve 100
0 0 1 1 0 1 0 1 0 0
0 1 0 1 0 0 0 1 0 1
0 0 0 1 0 0 0 0 0 1
0 1 0 0 0 0 0 1 0 0
0 1 0 1 0 0 0 1 0 0
0 0 0 1 0 0 0 0 0 1
0 1 0 0 0 0 0 1 0 0
0 1 0 1 0 0 0 0 0 1
0 0 0 1 0 0 0 0 0 1
0 0 0 0 0 0 0 1 0 0
b←sieve 1e9
≢b
1000000000
(10*⍳10) (+⌿↑)⍤0 1 ⊢b
0 4 25 168 1229 9592 78498 664579 5761455 50847534
The last sequence, the number of primes less than powers of 10, is an initial segment of OEIS: A006880. The last number, 50847534, is the number of primes less than . It is called Bertelsen's number, memorably described by MathWorld as "an erroneous name erroneously given the erroneous value of ".
sieve uses two different methods to mark composites with 0s, both effected using local anonymous dfns: The first uses the sieve of Eratosthenes on an initial mask of 1 and a prefix of the primes 2 3...43, using the insert operator ⌿ (right fold). (The length of the prefix obtains by comparison with the primorial function ×⍀p.) The second finds the smallest new prime q remaining in b (q←b⍳1), and sets to 0 bit q itself and bits at q times the numbers at remaining 1 bits in an initial segment of b (⍸b↑⍨⌈n÷q). This second dfn uses tail recursion.
Tail recursion
Typically, the factorial function is define recursively (as above), but it can be coded to exploit tail recursion by using an accumulator left argument:
fac←{⍺←1 ⋄ ⍵=0:⍺ ⋄ (⍺×⍵) ∇ ⍵-1}
Similarly, the determinant of a square complex matrix using Gaussian elimination can be computed with tail recursion:
det←{ ⍝ determinant of a square complex matrix
⍺←1 ⍝ product of co-factor coefficients so far
0=≢⍵:⍺ ⍝ result for 0-by-0
(i j)←(⍴⍵)⊤⊃⍒|,⍵ ⍝ row and column index of the maximal element
k←⍳≢⍵
(⍺×⍵ׯ1*i+j) ∇ ⍵ - ⍵ ∘.× ⍵÷⍵
}
Multiple recursion
A partition of a non-negative integer is a vector of positive integers such that n = +⌿v, where the order in is not significant. For example, 2 2 and 2 1 1 are partitions of 4, and 2 1 1 and 1 2 1 and 1 1 2 are considered to be the same partition.
The partition function counts the number of partitions. The function is of interest in number theory, studied by Euler, Hardy, Ramanujan, Erdős, and others. The recurrence relation
derived from Euler's pentagonal number theorem. Written as a dfn:
pn ← {1≥⍵:0≤⍵ ⋄ -⌿+⌿∇¨rec ⍵}
rec ← {⍵ - (÷∘2 (×⍤1) ¯1 1 ∘.+ 3∘×) 1+⍳⌈0.5*⍨⍵×2÷3}
pn 10
42
pn¨ ⍳13 ⍝ OEIS A000041
1 1 2 3 5 7 11 15 22 30 42 56 77
The basis step 1≥⍵:0≤⍵ states that for 1≥⍵, the result of the function is 0≤⍵, 1 if ⍵ is 0 or 1 and 0 otherwise. The recursive step is highly multiply recursive. For example, pn 200 would result in the function being applied to each element of rec 200, which are:
rec 200 199 195 188 178 165 149 130 108 83 55 24 ¯10 198 193 185 174 160 143 123 100 74 45 13 ¯22
and pn 200 requires longer than the age of the universe to compute ( function calls to itself). The compute time can be reduced by memoization, here implemented as the direct operator (higher-order function) M:
M←{
f←⍺⍺
i←2+'⋄'⍳⍨t←2↓,⎕cr 'f'
⍎'{T←(1+⍵)⍴¯1 ⋄ ',(i↑t),'¯1≢T:⊃T ⋄ ⊃T←⊂',(i↓t),'⍵}⍵'
}
pn M 200
3.973E12
0 ⍕ pn M 200 ⍝ format to 0 decimal places
3972999029388
This value of pn M 200 agrees with that computed by Hardy and Ramanujan in 1918.
The memo operator M defines a variant of its operand function ⍺⍺ to use a cache T and then evaluates it. With the operand pn the variant is:
{T←(1+⍵)⍴¯1 ⋄ {1≥⍵:0≤⍵ ⋄ ¯1≢T:⊃T ⋄ ⊃T←⊂-⌿+⌿∇¨rec ⍵}⍵}
Direct operator (dop)
Quicksort on an array ⍵ works by choosing a "pivot" at random among its major cells, then catenating the sorted major cells which strictly precede the pivot, the major cells equal to the pivot, and the sorted major cells which strictly follow the pivot, as determined by a comparison function ⍺⍺. Defined as a direct operator (dop) Q:
Q←{1≥≢⍵:⍵ ⋄ (∇ ⍵⌿⍨0>s)⍪(⍵⌿⍨0=s)⍪∇ ⍵⌿⍨0<s←⍵ ⍺⍺ ⍵⌷⍨?≢⍵}
⍝ precedes ⍝ follows ⍝ equals
2 (×-) 8 8 (×-) 2 8 (×-) 8
¯1 1 0
x← 2 19 3 8 3 6 9 4 19 7 0 10 15 14
(×-) Q x
0 2 3 3 4 6 7 8 9 10 14 15 19 19
Q3 is a variant that catenates the three parts enclosed by the function ⊂ instead of the parts per se. The three parts generated at each recursive step are apparent in the structure of the final result. Applying the function derived from Q3 to the same argument multiple times gives different results because the pivots are chosen at random. In-order traversal of the results does yield the same sorted array.
Q3←{1≥≢⍵:⍵ ⋄ (⊂∇ ⍵⌿⍨0>s)⍪(⊂⍵⌿⍨0=s)⍪⊂∇ ⍵⌿⍨0<s←⍵ ⍺⍺ ⍵⌷⍨?≢⍵}
(×-) Q3 x
┌────────────────────────────────────────────┬─────┬┐
│┌──────────────┬─┬─────────────────────────┐│19 19││
││┌──────┬───┬─┐│6│┌──────┬─┬──────────────┐││ ││
│││┌┬─┬─┐│3 3│4││ ││┌┬─┬─┐│9│┌┬──┬────────┐│││ ││
│││││0│2││ │ ││ ││││7│8││ │││10│┌──┬──┬┐││││ ││
│││└┴─┴─┘│ │ ││ ││└┴─┴─┘│ │││ ││14│15││││││ ││
││└──────┴───┴─┘│ ││ │ │││ │└──┴──┴┘││││ ││
││ │ ││ │ │└┴──┴────────┘│││ ││
││ │ │└──────┴─┴──────────────┘││ ││
│└──────────────┴─┴─────────────────────────┘│ ││
└────────────────────────────────────────────┴─────┴┘
(×-) Q3 x
┌───────────────────────────┬─┬─────────────────────────────┐
│┌┬─┬──────────────────────┐│7│┌────────────────────┬─────┬┐│
│││0│┌┬─┬─────────────────┐││ ││┌──────┬──┬────────┐│19 19│││
│││ │││2│┌────────────┬─┬┐│││ │││┌┬─┬─┐│10│┌──┬──┬┐││ │││
│││ │││ ││┌───────┬─┬┐│6│││││ │││││8│9││ ││14│15││││ │││
│││ │││ │││┌┬───┬┐│4│││ │││││ │││└┴─┴─┘│ │└──┴──┴┘││ │││
│││ │││ │││││3 3│││ │││ │││││ ││└──────┴──┴────────┘│ │││
│││ │││ │││└┴───┴┘│ │││ │││││ │└────────────────────┴─────┴┘│
│││ │││ ││└───────┴─┴┘│ │││││ │ │
│││ │││ │└────────────┴─┴┘│││ │ │
│││ │└┴─┴─────────────────┘││ │ │
│└┴─┴──────────────────────┘│ │ │
└───────────────────────────┴─┴─────────────────────────────┘
The above formulation is not new; see for example Figure 3.7 of the classic The Design and Analysis of Computer Algorithms. However, unlike the pidgin ALGOL program in Figure 3.7, Q is executable, and the partial order used in the sorting is an operand, the (×-) the examples above.
Dfns with operators and trains
Dfns, especially anonymous dfns, work well with operators and trains. The following snippet solves a "Programming Pearls" puzzle: given a dictionary of English words, here represented as the character matrix a, find all sets of anagrams.
a {⍵}⍤1 ⊢a ({⍵}⍤1 {⊂⍵}⌸ ⊢) a
pats apst ┌────┬────┬────┐
spat apst │pats│teas│star│
teas aest │spat│sate│ │
sate aest │taps│etas│ │
taps apst │past│seat│ │
etas aest │ │eats│ │
past apst │ │tase│ │
seat aest │ │east│ │
eats aest │ │seta│ │
tase aest └────┴────┴────┘
star arst
east aest
seta aest
The algorithm works by sorting the rows individually ({⍵}⍤1 ⊢a), and these sorted rows are used as keys ("signature" in the Programming Pearls description) to the key operator ⌸ to group the rows of the matrix. The expression on the right is a train, a syntactic form employed by APL to achieve tacit programming. Here, it is an isolated sequence of three functions such that (f g h) ⍵ ⇔ (f ⍵) g (h ⍵), whence the expression on the right is equivalent to ({⍵}⍤1 ⊢a) {⊂⍵}⌸ a.
Lexical scope
When an inner (nested) dfn refers to a name, it is sought by looking outward through enclosing dfns rather than down the call stack. This regime is said to employ lexical scope instead of APL's usual dynamic scope. The distinction becomes apparent only if a call is made to a function defined at an outer level. For the more usual inward calls, the two regimes are indistinguishable.
For example, in the following function which, the variable ty is defined both in which itself and in the inner function f1. When f1 calls outward to f2 and f2 refers to ty, it finds the outer one (with value 'lexical') rather than the one defined in f1 (with value 'dynamic'):
which←{
ty←'lexical'
f1←{ty←'dynamic' ⋄ f2 ⍵}
f2←{ty,⍵}
f1 ⍵
}
which ' scope'
lexical scope
Error-guard
The following function illustrates use of error guards:
plus←{
tx←'catch all' ⋄ 0::tx
tx←'domain' ⋄ 11::tx
tx←'length' ⋄ 5::tx
⍺+⍵
}
2 plus 3 ⍝ no errors
5
2 3 4 5 plus 'three' ⍝ argument lengths don't match
length
2 3 4 5 plus 'four' ⍝ can't add characters
domain
2 3 plus 3 4⍴5 ⍝ can't add vector to matrix
catch all
In APL, error number 5 is "length error"; error number 11 is "domain error"; and error number 0 is a "catch all" for error numbers 1 to 999.
The example shows the unwinding of the local environment before an error-guard's expression is evaluated. The local name tx is set to describe the purview of its following error-guard. When an error occurs, the environment is unwound to expose tx's statically correct value.
Dfns versus tradfns
Since direct functions are dfns, APL functions defined in the traditional manner are referred to as tradfns, pronounced "trad funs". Here, dfns and tradfns are compared by consideration of the function sieve: On the left is a dfn (as defined above); in the middle is a tradfn using control structures; on the right is a tradfn using gotos (→) and line labels.
sieve←{
4≥⍵:⍵⍴0 0 1 1
r←⌊0.5*⍨n←⍵
p←2 3 5 7 11 13 17 19 23 29 31 37 41 43
p←(1+(n≤×⍀p)⍳1)↑p
b← 0@1 ⊃ {(m⍴⍵)>m⍴⍺↑1 ⊣ m←n⌊⍺×≢⍵}⌿ ⊖1,p
{r<q←b⍳1:b⊣b←1 ⋄ b←0 ⋄ ∇ ⍵,q}p
}
|
∇ b←sieve1 n;i;m;p;q;r :If 4≥n ⋄ b←n⍴0 0 1 1 ⋄ :Return ⋄ :EndIf r←⌊0.5*⍨n p←2 3 5 7 11 13 17 19 23 29 31 37 41 43 p←(1+(n≤×⍀p)⍳1)↑p b←1 :For q :In p ⋄ b←(m⍴b)>m⍴q↑1 ⊣ m←n⌊q×≢b ⋄ :EndFor b←0 :While r≥q←b⍳1 ⋄ b←0 ⋄ p⍪←q ⋄ :EndWhile b←1 ∇ |
∇ b←sieve2 n;i;m;p;q;r →L10 ⍴⍨ 4<n ⋄ b←n⍴0 0 1 1 ⋄ →0 L10: r←⌊0.5*⍨n p←2 3 5 7 11 13 17 19 23 29 31 37 41 43 p←(1+(n≤×\p)⍳1)↑p i←0 ⋄ b←1 L20: b←(m⍴b)>m⍴p↑1 ⊣ m←n⌊p×≢b →L20 ⍴⍨ (≢p)>i←1+i b←0 L30: →L40 ⍴⍨ r<q←b⍳1 ⋄ b←0 ⋄ p⍪←q ⋄ →L30 L40: b←1 ∇ |
- A dfn can be anonymous; a tradfn must be named.
- A dfn is named by assignment (
←); a tradfn is named by embedding the name in the representation of the function and applying⎕fx(a system function) to that representation. - A dfn is handier than a tradfn as an operand (see preceding items: a tradfn must be named; a tradfn is named by embedding ...).
- Names assigned in a dfn are local by default; names assigned in a tradfn are global unless specified in a locals list.
- Locals in a dfn have lexical scope; locals in a tradfn have dynamic scope, visible in called functions unless shadowed by their locals list.
- The arguments of a dfn are named
⍺and⍵and the operands of a dop are named⍺⍺and⍵⍵; the arguments and operands of a tradfn can have any name, specified on its leading line. - The result (if any) of a dfn is unnamed; the result (if any) of a tradfn is named in its header.
- A default value for ⍺ is specified more neatly than for the left argument of a tradfn.
- Recursion in a dfn is effected by invoking
∇or∇∇or its name; recursion in a tradfn is effected by invoking its name. - Flow control in a dfn is effected by guards and function calls; that in a tradfn is by control structures and
→(goto) and line labels. - Evaluating an expression in a dfn not ending in assignment causes return from the dfn; evaluating a line in a tradfn not ending in assignment or goto displays the result of the line.
- A dfn returns on evaluating an expression not ending in assignment, on evaluating a guarded expression, or after the last expression; a tradfn returns on
→(goto) line 0 or a non-existing line, or on evaluating a:Returncontrol structure, or after the last line. - The simpler flow control in a dfn makes it easier to detect and implement tail recursion than in a tradfn.
- A dfn may call a tradfn and vice versa; a dfn may be defined in a tradfn, and vice versa.
History
Kenneth E. Iverson, the inventor of APL, was dissatisfied with the way user functions (tradfns) were defined. In 1974, he devised "formal function definition" or "direct definition" for use in exposition. A direct definition has two or four parts, separated by colons:
name : expression name : expression0 : proposition : expression1
Within a direct definition, ⍺ denotes the left argument and ⍵ the right argument. In the first instance, the result of expression is the result of the function; in the second instance, the result of the function is that of expression0 if proposition evaluates to 0, or expression1 if it evaluates to 1. Assignments within a direct definition are dynamically local. Examples of using direct definition are found in the 1979 Turing Award Lecture and in books and application papers.
Direct definition was too limited for use in larger systems. The ideas were further developed by multiple authors in multiple works but the results were unwieldy. Of these, the "alternative APL function definition" of Bunda in 1987 came closest to current facilities, but is flawed in conflicts with existing symbols and in error handling which would have caused practical difficulties, and was never implemented. The main distillates from the different proposals were that (a) the function being defined is anonymous, with subsequent naming (if required) being effected by assignment; (b) the function is denoted by a symbol and thereby enables anonymous recursion.
In 1996, John Scholes of Dyalog Limited invented direct functions (dfns). The ideas originated in 1989 when he read a special issue of The Computer Journal on functional programming. He then proceeded to study functional programming and became strongly motivated ("sick with desire", like Yeats) to bring these ideas to APL. He initially operated in stealth because he was concerned the changes might be judged too radical and an unnecessary complication of the language; other observers say that he operated in stealth because Dyalog colleagues were not so enamored and thought he was wasting his time and causing trouble for people. Dfns were first presented in the Dyalog Vendor Forum at the APL '96 Conference and released in Dyalog APL in early 1997. Acceptance and recognition were slow in coming. As late as 2008, in Dyalog at 25, a publication celebrating the 25th anniversary of Dyalog Limited, dfns were barely mentioned (mentioned twice as "dynamic functions" and without elaboration). As of 2019, dfns are implemented in Dyalog APL, NARS2000, and ngn/apl. They also play a key role in efforts to exploit the computing abilities of a graphics processing unit (GPU).
References
- ^ Scholes, John (October 1996). "Direct Functions in Dyalog APL" (PDF). Vector. 13 (2). Retrieved 16 September 2019.
- Scholes, John (1998–2019), Direct Functions Reference Card, retrieved 26 September 2019
- Scholes, John (April 2001). "D: A Functional Subset of Dyalog APL". Vector. 17 (4). Retrieved 21 September 2019.
- Scholes, John (13 September 2009). Introduction to D-functions: 1 of 2 (video). Dyalog '09 User Conference. Retrieved 21 September 2019.
- Scholes, John (13 September 2009). Introduction to D-functions: 2 of 2 (video). Dyalog '09 User Conference. Retrieved 21 September 2019.
- ^ Scholes, John (31 October 2018). Dfns—Past, Present and Future (video). Dyalog '18 User Meeting. Retrieved 21 September 2019.
- ^ Scholes, John (31 October 2018), Dfns—Past, Present and Future (text) (PDF), Dyalog '18 User Meeting, retrieved 21 September 2019
- Scholes, John (1998–2019), Direct Functions Workspace, retrieved 2019-09-15
- ^ Hui, Roger; Kromberg, Morten (June 2020). "APL Since 1978". Proceedings of the ACM on Programming Languages. 4 (HOPL): 1–108. doi:10.1145/3386319. S2CID 218517570.
- ^ Hui, Roger (27 November 2016), A History of APL in 50 Functions, retrieved 17 September 2019
- ^ Hui, Roger (18 July 2016), APL Exercises, retrieved 24 September 2019
- Weisstein, Eric W., Bertelsen's Number, MathWorld, A Wolfram Web Resource, retrieved 26 September 2019
- Scholes, John (1998–2019), "Factorial", DFNS Workspace, retrieved 20 September 2019
- Scholes, John (1998–2019), "Determinant", DFNS Workspace, retrieved 20 September 2019
- Weisstein, Eric W., Partition Function P, equation 11, MathWorld, A Wolfram Web Resource, retrieved 3 October 2019
- Hardy, G.H.; Ramanujan, S. (1918), "Asymptotic Formulæ in Combinatory Analysis" (PDF), Proceedings of the London Mathematical Society, 17 (2), retrieved 24 December 2019
- Aho, A.V.; Hopcroft, J.E.; Ullman, J.D. (1974), The Design and Analysis of Computer Algorithms, Addison-Wesley
- Bentley, Jon (August 1983). "Programming Pearls". Communications of the ACM. 26 (8 and 9).
- ^ Dyalog (15 August 2019). Dyalog Programming Reference Guide, version 17.1, Dfns & Dops, pp. 133-147 (PDF). Dyalog Ltd. Retrieved 30 September 2019.
- Iverson, Kenneth E. (1974), "Chapter 10, Formal Function Definition", Elementary Functions, IBM Corporation, retrieved 18 September 2019
- Iverson, Kenneth E. (August 1980). "Notation as a Tool of Thought". Communications of the ACM. 23 (8): 444–465. doi:10.1145/358896.358899. Retrieved 8 April 2016.
- Iverson, Kenneth E. (1976). Elementary Analysis. APL Press.
- Orth, D.L. (1976). Calculus in a New Key. APL Press.
- Hui, Roger (May 1987). "Some Uses of { and }". APL 87 Conference Proceedings. Retrieved 15 April 2016.
- McDonnell, E.E. (May 1987), "Life: Nasty, Brutish, and Short", APL 87 Conference Proceedings, retrieved 6 October 2019
- Iverson, Kenneth E. (26 April 1978), "Operators and Functions", Research Report Number #RC7091, IBM Corporation, retrieved 2019-09-19
- Iverson, Kenneth E.; Wooster, Peter (September 1981). "A Function Definition Operator". APL81 Conference Proceedings, APL Quote Quad. 12 (1).
- Cheney, Carl M. (March 1981), APL*Plus Nested Array System Reference Manual (PDF), STSC, Inc., retrieved 18 September 2019
- Iverson, Kenneth E. (6 January 1983), Rationalized APL, I. P. Sharp Associates, retrieved 2019-09-19
- Iverson, Kenneth E. (September 1987). "A Dictionary of APL". APL Quote Quad. 18 (1): 5–40. doi:10.1145/36983.36984. S2CID 18301178. Retrieved 19 September 2019.
- ^ Bunda, John (May 1987). "APL Function Definition Notation". APL87 Conference Proceedings, APL Quote Quad. 17 (4).
- Hui, Roger; et al. (July 1990). "APL\?". Conference proceedings on APL 90: For the future. Vol. 20. pp. 192–200. doi:10.1145/97808.97845. ISBN 089791371X. S2CID 235453656. Retrieved 2019-09-10.
- Wadler, Philip L.; et al. (1 January 1989). "Special Issue on Functional Programming". The Computer Journal. 32 (2).
- Dyalog (September 2008). "Dyalog at 25" (PDF). Vector. Retrieved 2019-09-20.
- Smith, Bob (2006–2019), NARS2000, retrieved 18 September 2019
- Nickolov, Nick (September 2013). "Compiling APL to JavaScript". Vector. 26 (1). Retrieved 19 September 2019.
- Hsu, Aaron (2019). A Data Parallel Compiler Hosted on a GPU (PDF) (Ph.D. thesis). Indiana University. Retrieved 25 December 2019.
External links
- Official website, Dyalog
| APL programming | |||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Features |  | ||||||||||||
| Implementations |
| ||||||||||||
| Community |
| ||||||||||||
| |||||||||||||
 ) times
) times  .
.



 . It is called Bertelsen's number, memorably described by
. It is called Bertelsen's number, memorably described by  ".
".
 is a vector
is a vector  of positive integers such that
of positive integers such that  counts the number of partitions. The function is of interest in
counts the number of partitions. The function is of interest in 
 function calls to itself). The compute time can be reduced by
function calls to itself). The compute time can be reduced by